Microsoft's Legal Takedown
How Court Orders Crush Phishing Networks Explained Simply
How a Court Order Became the Ultimate Cybersecurity Weapon Against the RedVeds Threat
In This Deep Dive:
- Executive Summary: The Day Microsoft Fought Back
- Anatomy of an Attack: How RedVeds Phishing Lures Worked
- MITRE ATT&CK Mapping: The Hacker's Playbook Exposed
- The Legal Weapon: Step-by-Step Takedown Process
- Red Team vs. Blue Team: Perspectives on Disruption
- Common Mistakes & Best Practices for Organizations
- Implementation Framework: Building Legal Readiness
- Frequently Asked Questions
- Key Takeaways & Call to Action
Executive Summary: The Day Microsoft Fought Back
In January 2026, cybersecurity defense entered a new era. Microsoft didn't just patch a vulnerability or block IP addresses, they went to court. This landmark action against the RedVeds phishing campaign represents a powerful shift in how corporations can legally dismantle cybercriminal infrastructure from the ground up.
The phishing campaign disruption targeted a network that created hundreds of deceptive lookalike domains impersonating major brands like Microsoft, Zoom, and US government agencies. The threat actors used these domains to launch credential harvesting attacks, tricking thousands of users into surrendering their login details, which could then be used for identity theft, ransomware deployment, or corporate espionage.
This post breaks down not only the technical mechanics of the attack but, more importantly, the innovative legal and technical strategy Microsoft employed to achieve a complete disruption. For cybersecurity beginners and professionals alike, it's a case study in modern, multi-pronged defense.
Anatomy of an Attack: How the RedVeds Phishing Lures Worked
To understand the brilliance of the defense, we must first understand the offense. The RedVeds operation was not a simple, one-off phishing email. It was a sophisticated, persistent campaign designed for scale and evasion.
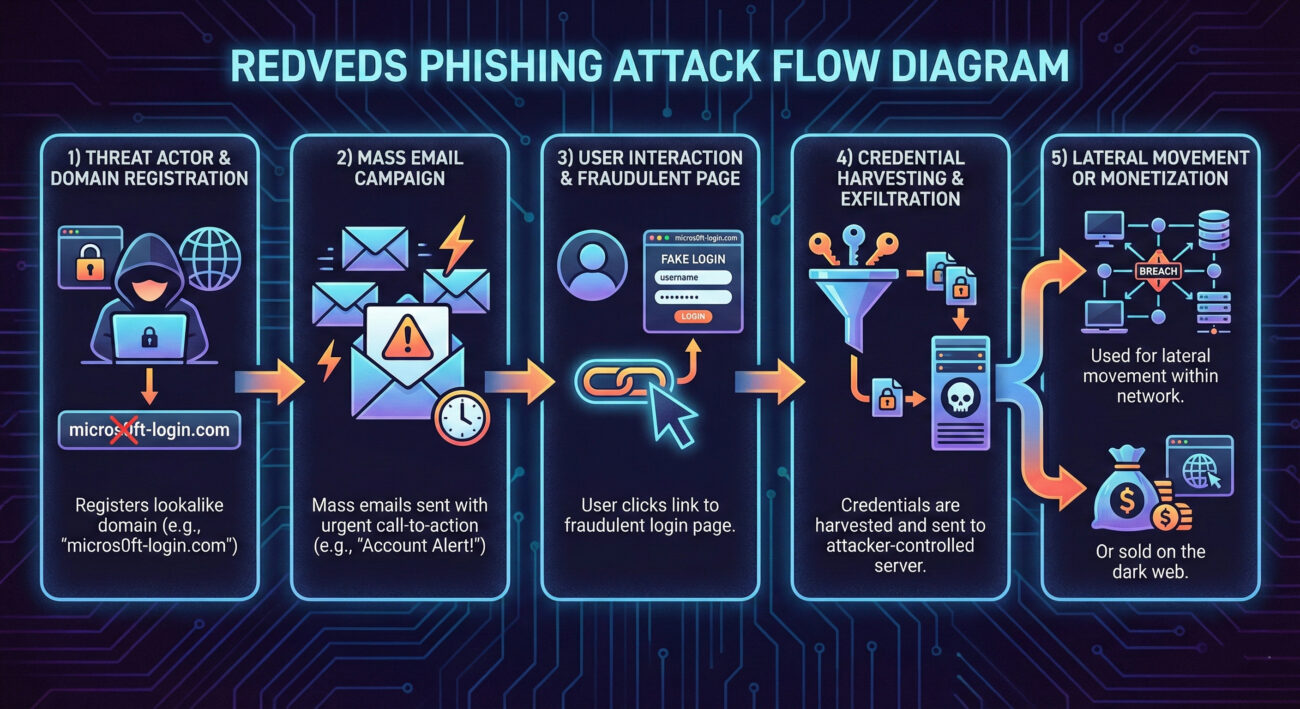
The Technical Hook: Lookalike Domains and Social Engineering
The core of the attack was domain impersonation. The attackers registered domains that closely resembled legitimate ones, using techniques like:
- Character Substitution: Replacing 'o' with '0', 'm' with 'rn' (e.g., micr0soft.online).
- Extra Words/Dashes: Adding words like "secure", "login", or "verify" (e.g., microsoft-verify-portal.com).
- Different Top-Level Domains (TLDs): Using .us, .net, .co instead of .com.
Victims would receive emails designed to create urgency: "Your account will be suspended," "Unusual login attempt detected," or "Action required on your invoice." The link, of course, pointed to the fraudulent lookalike domain hosting a perfect replica of a Microsoft, Zoom, or government login page. Any credentials entered were instantly sent to the threat actors.
MITRE ATT&CK Mapping: The Hacker's Playbook Exposed
Frameworks like MITRE ATT&CK help defenders understand adversary behavior in a structured way. The RedVeds campaign was a textbook example of several techniques.
| MITRE ATT&CK Tactic | Specific Technique (ID) | How RedVeds Used It |
|---|---|---|
| Resource Development | Acquire Infrastructure: Domains (T1583.001) | Registered hundreds of lookalike domains to host phishing pages. |
| Initial Access | Phishing: Spearphishing Link (T1566.002) | Sent targeted emails with links to fraudulent login pages to harvest credentials. |
| Credential Access | Credentials from Web Browsers (T1555.003) | Directly harvested credentials via fake web forms (phishing pages). |
| Defense Evasion | Domain Masquerading (T1036.006) | Used lookalike domains to appear legitimate and bypass user scrutiny. |
By mapping the attack, defenders can build detections. For example, detecting new domain registrations similar to your corporate domain (T1583.001) or internal alerts for emails containing links to domains with character substitutions (T1566.002, T1036.006).
The Legal Weapon: A Step-by-Step Guide to Campaign Disruption
This is where the case gets groundbreaking. Microsoft moved beyond technical blocks to a legal counteroffensive. Here’s how they achieved the phishing campaign disruption.
Step 1: Investigation & Attribution
Microsoft's Digital Crimes Unit (DCU) first investigated the campaign, tracing the infrastructure (domains, servers, hosting providers). They gathered evidence linking the domains to malicious activity, demonstrating they were created for the sole purpose of fraud and trademark infringement.
Step 2: Obtaining a Court Order
Microsoft filed a lawsuit in the U.S. District Court for the Eastern District of Virginia. They presented their evidence and requested a temporary restraining order (TRO) and transfer order. The court granted it, giving Microsoft legal authority to take control of the malicious domains.
Step 3: Seizing Control of the Domains
With the court order in hand, Microsoft worked with domain registrars worldwide. The order compelled the registrars to transfer control of the identified malicious domains to Microsoft. This is the core of the legal disruption.
Step 4: Neutralizing the Threat
Once Microsoft controlled the domains, they could defang them. Instead of pointing to phishing pages, the domains now redirected to a "safe sinkhole", a server controlled by Microsoft that either displayed a warning message or simply timed out. This broke the attack chain completely.
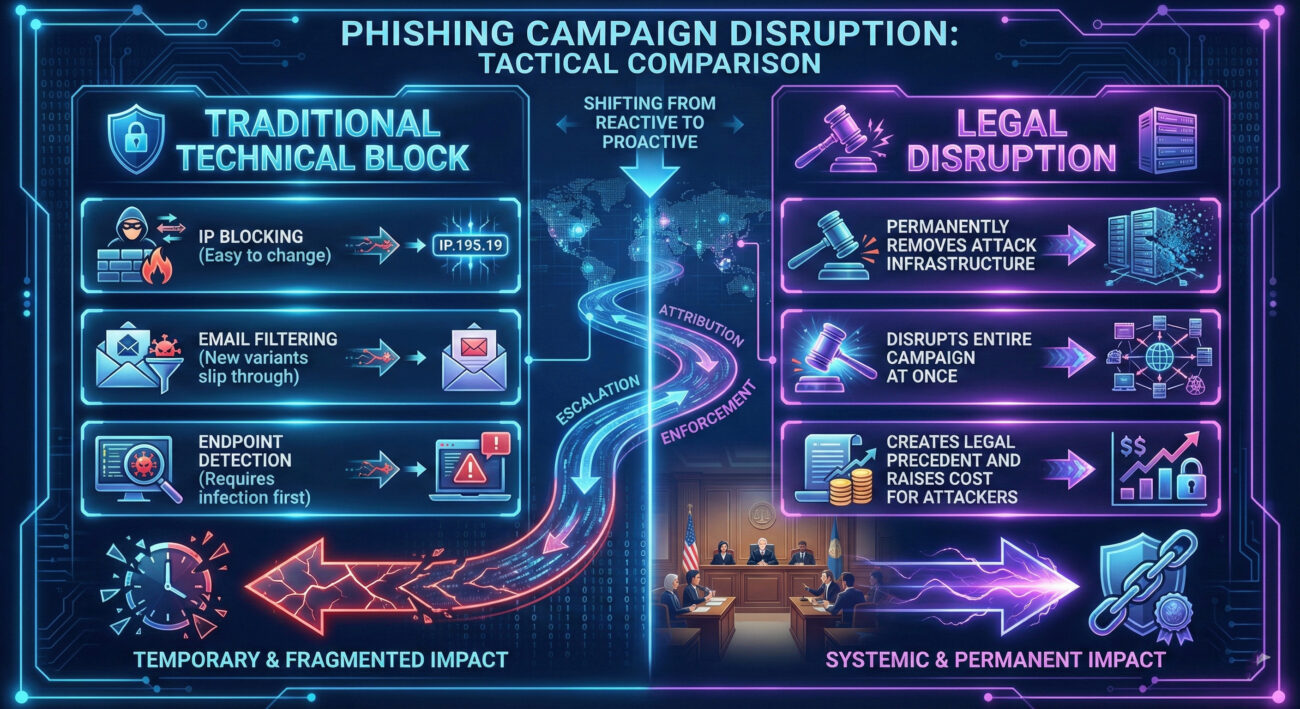
Red Team vs. Blue Team: Perspectives on Disruption
This event is a fascinating study from both adversarial and defensive viewpoints.
The Red Team (Threat Actor) View
Impact: A catastrophic operational failure. Their primary infrastructure, the domains, was permanently seized, not just blocked. This means:
- Financial Loss: Investment in registering domains is lost.
- Operational Reset: Must find new registrars, register new domains (which can be tracked), and rebuild phishing kits.
- Increased Risk: Legal attention raises their profile; evidence gathered could aid in attribution.
Adaptation: Future campaigns may use more decentralized infrastructure, bulletproof hosting, or faster domain rotation to make legal action harder.
The Blue Team (Defender) View
Opportunity: A powerful new tool in the arsenal. Legal action offers a more permanent and scalable solution than whack-a-mole technical blocking.
- Proactive Defense: Can dismantle campaigns before they reach peak effectiveness.
- Strategic Deterrence: Raises the cost and risk for adversaries, potentially discouraging some actors.
- Collaboration Model: Sets a precedent for public-private partnership (corporations + courts) in cyber defense.
Challenge: Requires significant legal resources, evidence collection, and is typically only available to large organizations with clear trademark claims.
Common Mistakes & Best Practices for Organizational Defense
While not every company can replicate Microsoft's legal action, all can learn from the principles and shore up defenses.
Common Mistakes (What to Avoid)
- Relying Solely on Email Filters: Assuming your secure email gateway will catch everything. New domains and sophisticated lures often bypass filters initially.
- No Domain Monitoring: Failing to monitor for lookalike domains registering in real-time. This is a critical early warning signal.
- Weak Authentication: Allowing password-only access to critical systems, making stolen credentials immediately useful to attackers.
- Poor User Training: Training that is annual, generic, and doesn't teach users how to inspect URLs and identify subtle domain spoofs.
Best Practices (What to Implement)
- Enforce Phishing-Resistant MFA: Implement Multi-Factor Authentication (MFA) using FIDO2 security keys or authenticator apps. This makes stolen passwords worthless.
- Implement Domain Monitoring Services: Use services (like DNS sinkholing, threat intel feeds) or scripts to alert when domains similar to yours are registered. Resources like ICANN's data can be a starting point.
- Adopt a Zero-Trust Mindset: Never trust, always verify. Assume a breach can happen and segment networks, enforce least-privilege access, and log all access attempts.
- Conduct Regular Phishing Simulations: Use realistic simulations based on current threats (like lookalike domains) to train and test users. Measure click rates and provide immediate feedback.
- Have an Incident Response Plan for Credential Theft: Know exactly what to do if credentials are phished: force password reset, revoke sessions, investigate for lateral movement.
Implementation Framework: Building Legal & Technical Readiness
For organizations inspired by this phishing campaign disruption, here is a practical framework to build similar resilience.
- Technical Foundation: Harden your environment. Deploy DMARC, DKIM, and SPF to make email spoofing harder. Enforce MFA universally. Use endpoint detection and response (EDR) tools.
- Threat Intelligence: Subscribe to feeds that provide data on newly registered malicious domains and phishing kits. The CISA Alerts are a great free resource.
- Legal Preparedness: Work with your legal team to understand the prerequisites for taking legal action. This often requires strong evidence logs, clear trademark ownership, and a relationship with law enforcement or a dedicated digital crimes unit.
- Partnership Building: Establish relationships with your domain registrars, hosting providers, and computer emergency response teams (CERTs). In a crisis, knowing who to contact is half the battle.
- Continuous Improvement: Treat every security incident as a learning opportunity. Update your playbooks, refine your detection rules, and retrain your teams.
Frequently Asked Questions
Q: Can a small or medium-sized business (SMB) use this legal takedown strategy?
A: Directly replicating it is challenging due to cost and resource requirements. However, SMBs can report malicious domains to their hosting provider, registrar, and authorities like the FBI's Internet Crime Complaint Center (IC3). The key takeaway is to secure your own environment with MFA and user training.
Q: Why don't we see legal takedowns for every phishing campaign?
A: The process requires identifiable infrastructure (often hidden by threat actors), jurisdiction over that infrastructure, and substantial evidence gathering. It's most effective against large, persistent campaigns using impersonation of clear trademarks, like Microsoft's.
Q: What's the single most effective thing I can do to prevent phishing success?
A: Without a doubt, implement phishing-resistant Multi-Factor Authentication (MFA). If a user enters their password on a fake site, the attacker still cannot access the account without the second factor. NIST guidelines provide excellent standards for authentication.
Key Takeaways & Call to Action
The Microsoft vs. RedVeds case is more than a news story; it's a blueprint for the future of cyber defense:
- Legal action is a potent tool for large-scale disruption. It removes attacker infrastructure permanently, raising their costs.
- Defense must be layered. Combine technical controls (MFA, filters), human training, and strategic partnerships (legal, industry).
- Understand the adversary's playbook (MITRE ATT&CK) to build better detections and anticipate their next move.
- The goal is to break the attack chain. Whether by blocking an email, training a user, or seizing a domain, every layer adds friction for the attacker.
Your Call to Action
This Week: Check your organization's MFA enrollment rate. Aim for 100% on all critical systems (email, VPN, cloud apps). If you're an individual, enable MFA on your personal email and banking accounts.
This Month: Conduct a phishing simulation focused on lookalike domains. Use the results to tailor a 10-minute training session for your team or colleagues.
This Quarter: Initiate a conversation between your security and legal teams. Discuss what evidence would be needed to pursue action against a persistent threat and begin building those logging capabilities.
For continued learning, follow threat intelligence from sources like The Hacker News, Krebs on Security, and official advisories from CISA/US-CERT.
Cybersecurity is a continuous journey, not a destination. Stay vigilant, stay informed, and build defenses that are as adaptable as the threats they face.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































