DLL Side-Loading Attack
Decoding the c-ares Exploit & Building Ironclad Defenses Explained Simply
Table of Contents
- Executive Summary: The Stealthy Hijack
- What is DLL Side-Loading? The Wolf in Sheep's Clothing
- The c-ares Case Study: A Real-World Weaponization
- How the Attack Works: A Step-by-Step Breakdown
- MITRE ATT&CK Mapping: The Adversary's Playbook
- Red Team vs. Blue Team: Attack & Defense Perspectives
- Common Mistakes & Best Practices
- Defense Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways
In the ever-evolving landscape of cybersecurity, attackers continuously refine their tradecraft, seeking the path of least resistance. One of the most persistent and effective techniques involves abusing trusted Windows mechanisms to bypass security controls. The recent exploitation of the popular c-ares DNS library via a DLL side-loading attack is a textbook example of this threat. This post will dissect this attack vector, explain its mechanics in beginner-friendly terms, and provide actionable defense strategies.
Executive Summary: The Stealthy Hijack
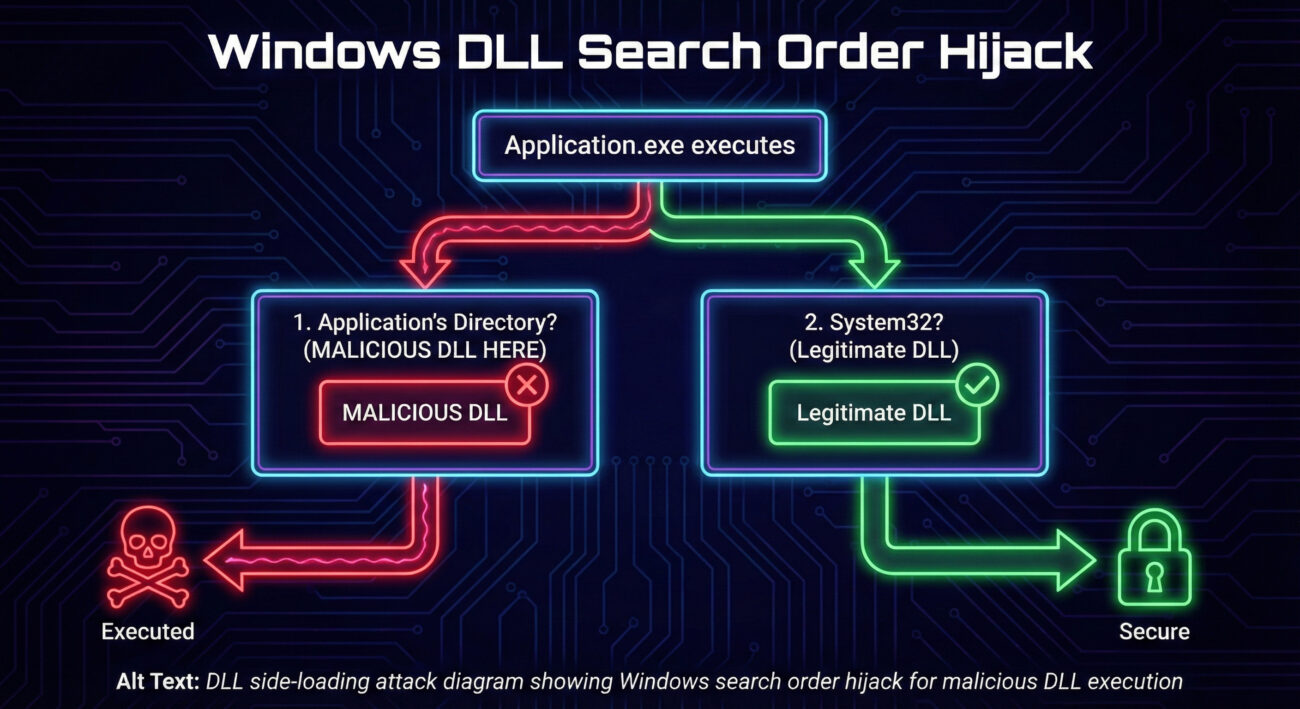
DLL side-loading is a hacker technique where a malicious Dynamic Link Library (DLL) is placed in a location where a legitimate, trusted application will load it instead of the intended, safe DLL. The recent campaign targeting the c-ares (C library for asynchronous DNS requests) software package perfectly illustrates this. Attackers bundled a malicious DLL named cyber.dll with the legitimate ares_init.exe tool. When executed, the legitimate executable, following standard Windows DLL search order, loads the malicious DLL, granting the attacker code execution within the context of a trusted process. This attack evades signature-based detection and leverages the trust associated with signed, legitimate software.
What is DLL Side-Loading? The Wolf in Sheep's Clothing
Imagine a trusted company van (legitimate.exe) that always picks up its driver (legitimate.dll) from a specific parking spot (System32 folder). A malicious actor learns this route and places an imposter driver (malicious.dll) in a parking spot closer to the van's starting point (the application's own folder). The van, simply following its standard "look for the driver" procedure, picks up the imposter first. That's DLL side-loading.
Technically, when a Windows application needs a DLL, it searches for it in a specific order (the DLL Search Order). The default order typically is:
- The directory from which the application loaded.
- The system directory (
C:\Windows\System32). - The 16-bit system directory.
- The Windows directory.
- The current directory.
- The directories listed in the PATH environment variable.
The vulnerability arises when an application tries to load a DLL by name (e.g., cyber.dll) without specifying its full, safe path. If an attacker can place their malicious version of cyber.dll in a higher-priority search location (like the application's folder), it gets loaded instead of the legitimate one from System32.
The c-ares Case Study: A Real-World Weaponization
The c-ares library includes a command-line tool, ares_init.exe, designed for testing and initialization. This tool depends on a DLL. Threat actors created a malware package containing:
- The legitimate, signed
ares_init.exebinary. - A malicious
cyber.dllfile, crafted to be loaded by the executable. - Other payload or deployment scripts.
The attack likely spreads through phishing emails, malicious downloads, or compromised websites. When a user runs ares_init.exe (or is tricked into running it), the process follows the DLL search order. Since cyber.dll sits right beside the EXE in the same folder, it's loaded first. The malicious DLL's code then executes, potentially deploying a backdoor, stealing data, or downloading additional malware, all under the guise of a legitimate c-ares process.
How the Attack Works: A Step-by-Step Breakdown
Step 1: Delivery & Execution
The attacker delivers a ZIP archive or installer containing the legitimate ares_init.exe and the malicious cyber.dll. The user is socially engineered into extracting and running the EXE file.
Step 2: The DLL Search
Upon execution, ares_init.exe requests to load a necessary DLL module. It calls a standard Windows API (like LoadLibrary) for a DLL named "cyber.dll" (or similar).
Step 3: Search Order Hijack
Windows begins its search. It first checks the directory where ares_init.exe lives. It finds the attacker-placed cyber.dll there and stops searching. The legitimate version in System32 is never reached.
Step 4: Malicious Code Execution
Windows loads the malicious cyber.dll into the memory space of ares_init.exe. The DLL's entry point function (DllMain) executes. This function contains the attacker's code, which now runs with the same privileges as the launched process.
Step 5: Persistence & Payload
The malicious DLL code can now perform its objectives: establish persistence, exfiltrate data, connect to a command-and-control (C2) server, or deploy a second-stage payload. All activity appears under the legitimate c-ares process name.
MITRE ATT&CK Mapping: The Adversary's Playbook
This attack maps clearly to the MITRE ATT&CK framework, a globally accessible knowledge base of adversary tactics and techniques.
| Tactic | Technique ID & Name | How It Applies to c-ares DLL Side-Loading |
|---|---|---|
| Defense Evasion | T1574.002 - Hijack Execution Flow: DLL Side-Loading | The core technique. Uses a legitimate executable to load a malicious DLL, evading application allowlisting and signature-based detection. |
| Execution | T1204.002 - User Execution: Malicious File | Relies on the user executing the delivered ares_init.exe file, often via social engineering. |
| Persistence | T1574.002 (also applies here) | The malicious DLL can be configured to execute its code every time the legitimate host executable is run, creating a persistence mechanism. |
| Privilege Escalation | T1574.002 | If the host executable (ares_init.exe) is run with higher privileges (e.g., by an admin), the malicious DLL code also executes with those elevated privileges. |
Red Team vs. Blue Team: Attack & Defense Perspectives
Red Team (Attack) Perspective
For a red teamer simulating an adversary, DLL side-loading is a prized technique.
- Objective: Gain stealthy, persistent execution that blends in with normal software.
- Tooling: Use tools like sRDI to convert shellcode into a position-independent DLL, or craft custom DLLs with frameworks.
- Target Selection: Identify software commonly deployed in the target environment that has a known DLL side-loading condition (missing DLL, weak directory permissions). Tools like LOLBAS can be a resource.
- Delivery: Package the legitimate EXE and malicious DLL together. Use phishing, compromised shared drives, or supply chain attacks for delivery.
- Advantage: Executes within a signed, trusted process, often bypassing Application Control policies like WDAC or AppLocker if they allow the legitimate parent binary.
Blue Team (Defense) Perspective
Defenders must focus on disrupting the attack chain and detecting the anomaly.
- Detection: Monitor for processes loading DLLs from unusual locations. An executable in
C:\Program Files loading a DLL from a user's Downloads folder is a major red flag. Use Sysmon (Event ID 7: Image loaded) and SIEM correlation.
- Hardening: Implement Microsoft's recommended DLL search order hardening via the
CWDIllegalInDllSearch registry key or the SetDefaultDllDirectories() API call for custom applications.
- Application Control: Deploy Windows Defender Application Control (WDAC) or AppLocker in allowlist mode, but ensure rules are precise. A rule allowing
ares_init.exe from any location is dangerous.
- Privilege Management: Enforce the principle of least privilege. Users should not run with administrative rights for daily tasks, limiting the impact of a successful side-load.
- Asset Management: Know your software inventory. Unexpected instances of tools like
ares_init.exe on workstations should be investigated.
Common Mistakes & Best Practices
Common Defensive Mistakes
- Relying solely on antivirus signatures. This attack uses a legitimate signed binary, making static file scanning ineffective.
- Overly permissive application allowlisting rules. Allowing all versions of an executable from any path.
- Ignoring DLL load events in logs. Not collecting or alerting on Sysmon Event ID 7 or similar telemetry.
- Granting users excessive permissions. Allowing standard users to write to program directories or install software globally.
- Not understanding the DLL search order. A fundamental gap in knowledge for Windows administrators.
Essential Best Practices
- Implement DLL search order hardening. Configure the
CWDIllegalInDllSearch registry value to 0xFFFFFFFF to prevent loading from the current working directory. (Microsoft Documentation)
- Deploy advanced application control. Use WDAC with policy rules that specify allowed publishers and file paths. Sign your own internal software.
- Enable and tune advanced logging. Deploy Sysmon with a robust configuration focusing on DLL loads, process creation, and file writes. Forward logs to a SIEM.
- Adopt the principle of least privilege (PoLP). Use standard user accounts for daily work. Implement Just-Enough-Administration (JEA) for IT tasks.
- Conduct regular user awareness training. Teach users about the dangers of running unknown executables, especially from email or downloads.
- Use managed installers and software restriction paths. Configure AppLocker to only allow execution from
%PROGRAMFILES%, %WINDIR%, etc.
Defense Implementation Framework
Red Team (Attack) Perspective
For a red teamer simulating an adversary, DLL side-loading is a prized technique.
- Objective: Gain stealthy, persistent execution that blends in with normal software.
- Tooling: Use tools like sRDI to convert shellcode into a position-independent DLL, or craft custom DLLs with frameworks.
- Target Selection: Identify software commonly deployed in the target environment that has a known DLL side-loading condition (missing DLL, weak directory permissions). Tools like LOLBAS can be a resource.
- Delivery: Package the legitimate EXE and malicious DLL together. Use phishing, compromised shared drives, or supply chain attacks for delivery.
- Advantage: Executes within a signed, trusted process, often bypassing Application Control policies like WDAC or AppLocker if they allow the legitimate parent binary.
Blue Team (Defense) Perspective
Defenders must focus on disrupting the attack chain and detecting the anomaly.
- Detection: Monitor for processes loading DLLs from unusual locations. An executable in
C:\Program Filesloading a DLL from a user'sDownloadsfolder is a major red flag. Use Sysmon (Event ID 7: Image loaded) and SIEM correlation. - Hardening: Implement Microsoft's recommended DLL search order hardening via the
CWDIllegalInDllSearchregistry key or theSetDefaultDllDirectories()API call for custom applications. - Application Control: Deploy Windows Defender Application Control (WDAC) or AppLocker in allowlist mode, but ensure rules are precise. A rule allowing
ares_init.exefrom any location is dangerous. - Privilege Management: Enforce the principle of least privilege. Users should not run with administrative rights for daily tasks, limiting the impact of a successful side-load.
- Asset Management: Know your software inventory. Unexpected instances of tools like
ares_init.exeon workstations should be investigated.
Common Defensive Mistakes
- Relying solely on antivirus signatures. This attack uses a legitimate signed binary, making static file scanning ineffective.
- Overly permissive application allowlisting rules. Allowing all versions of an executable from any path.
- Ignoring DLL load events in logs. Not collecting or alerting on Sysmon Event ID 7 or similar telemetry.
- Granting users excessive permissions. Allowing standard users to write to program directories or install software globally.
- Not understanding the DLL search order. A fundamental gap in knowledge for Windows administrators.
Essential Best Practices
- Implement DLL search order hardening. Configure the
CWDIllegalInDllSearchregistry value to0xFFFFFFFFto prevent loading from the current working directory. (Microsoft Documentation) - Deploy advanced application control. Use WDAC with policy rules that specify allowed publishers and file paths. Sign your own internal software.
- Enable and tune advanced logging. Deploy Sysmon with a robust configuration focusing on DLL loads, process creation, and file writes. Forward logs to a SIEM.
- Adopt the principle of least privilege (PoLP). Use standard user accounts for daily work. Implement Just-Enough-Administration (JEA) for IT tasks.
- Conduct regular user awareness training. Teach users about the dangers of running unknown executables, especially from email or downloads.
- Use managed installers and software restriction paths. Configure AppLocker to only allow execution from
%PROGRAMFILES%,%WINDIR%, etc.
Defense Implementation Framework
Build your defense in layers, following this actionable framework:
| Layer | Action | Tool/Technique |
|---|---|---|
| 1. Policy & Hardening | Harden the DLL Search Order across the enterprise. | Group Policy: Computer Configuration -> Administrative Templates -> MS Security Guide -> Configure DLL search order. |
| 2. Prevention | Restrict unauthorized code execution. | Deploy Windows Defender Application Control (WDAC) with a deny-by-default policy, incrementally allowing trusted software. (WDAC Guide) |
| 3. Detection | Monitor for anomalous DLL loads. | Sysmon Configuration (SwiftOnSecurity's config is a great start) alerting on DLL loads where ImageLoaded path is not in System32, SysWOW64, or approved application directories. |
| 4. Response | Have a playbook for suspected side-loading incidents. | Playbook steps: 1. Isolate host. 2. Capture memory & disk artifacts (MFT, prefetch, the suspicious DLL/EXE). 3. Analyze DLL metadata, imports, and behavior in sandbox. 4. Hunt for other occurrences using file hash (DLL/EXE) and parent process criteria. |
| 5. Awareness | Reduce the human attack surface. | Regular, engaging training on identifying phishing lures and the risks of executing unknown programs. Simulated phishing campaigns. |
Frequently Asked Questions (FAQ)
Q: Is DLL side-loading a vulnerability in Windows itself?
A: Not exactly. It's an exploitation of a documented Windows feature (the DLL search order). The vulnerability often lies in application design (not specifying full DLL paths) or in environmental configurations (permissive file permissions). Microsoft provides features to harden against it.
Q: Can antivirus software stop this attack?
A: Traditional signature-based AV may struggle because the host executable is legitimate. Modern Endpoint Detection and Response (EDR) solutions are better suited as they can detect the suspicious behavior (e.g., a process loading a DLL from a temp folder) using behavioral analytics.
Q: How can developers prevent their applications from being used in such attacks?
A: Developers should:
- Use absolute paths or
SetDefaultDllDirectories(LOAD_LIBRARY_SEARCH_SYSTEM32) API to restrict DLL loading to secure directories.
- Digitally sign all application binaries and DLLs.
- Use manifests to specify dependent assemblies.
- Follow secure coding practices for the Windows API.
Q: Is this related to "DLL Hijacking" or "DLL Injection"?
A: DLL Side-Loading and DLL Hijacking are often used interchangeably to describe this search order abuse. DLL Injection is a different technique where code is forcibly inserted into a running process's memory space, often requiring higher privileges or different APIs.
Key Takeaways
- DLL side-loading is a pervasive defense evasion technique that abuses Windows DLL search order to run malicious code under the cover of legitimate, trusted processes.
- The c-ares exploit is a real-world example where attackers paired
ares_init.exe with a malicious cyber.dll, demonstrating the practicality of this method.
- MITRE ATT&CK T1574.002 formally defines this technique under the "Hijack Execution Flow" tactic.
- Defense requires a multi-layered approach: system hardening (DLL search order), advanced application control (WDAC/AppLocker), robust logging (Sysmon/SIEM), and user training.
- Detection hinges on behavioral analysis. Look for processes loading DLLs from unusual, writable locations like user directories or temporary folders.
- Understanding this attack is fundamental for both red teams testing defenses and blue teams building them.
Ready to Fortify Your Defenses?
DLL side-loading is just one piece of the complex threat puzzle. To build a truly resilient security posture, continuous learning is key.
Next Steps:
- Test your environment: Use a safe, controlled lab to simulate a DLL side-loading attack and validate your detection capabilities. Always ensure you have explicit permission.
- Review your logging: Check if you are collecting Sysmon Event ID 7 (Image loaded) and if your SOC can create alerts for suspicious load events.
- Audit application controls: Review your WDAC or AppLocker policies. Are they in allowlist mode? Do they restrict execution to trusted paths only?
Share this knowledge with your team, and start implementing these secure practices today. The cost of prevention is always lower than the cost of a breach.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
A: Not exactly. It's an exploitation of a documented Windows feature (the DLL search order). The vulnerability often lies in application design (not specifying full DLL paths) or in environmental configurations (permissive file permissions). Microsoft provides features to harden against it.
A: Traditional signature-based AV may struggle because the host executable is legitimate. Modern Endpoint Detection and Response (EDR) solutions are better suited as they can detect the suspicious behavior (e.g., a process loading a DLL from a temp folder) using behavioral analytics.
A: Developers should:
- Use absolute paths or
SetDefaultDllDirectories(LOAD_LIBRARY_SEARCH_SYSTEM32)API to restrict DLL loading to secure directories. - Digitally sign all application binaries and DLLs.
- Use manifests to specify dependent assemblies.
- Follow secure coding practices for the Windows API.
A: DLL Side-Loading and DLL Hijacking are often used interchangeably to describe this search order abuse. DLL Injection is a different technique where code is forcibly inserted into a running process's memory space, often requiring higher privileges or different APIs.
- DLL side-loading is a pervasive defense evasion technique that abuses Windows DLL search order to run malicious code under the cover of legitimate, trusted processes.
- The c-ares exploit is a real-world example where attackers paired
ares_init.exewith a maliciouscyber.dll, demonstrating the practicality of this method. - MITRE ATT&CK T1574.002 formally defines this technique under the "Hijack Execution Flow" tactic.
- Defense requires a multi-layered approach: system hardening (DLL search order), advanced application control (WDAC/AppLocker), robust logging (Sysmon/SIEM), and user training.
- Detection hinges on behavioral analysis. Look for processes loading DLLs from unusual, writable locations like user directories or temporary folders.
- Understanding this attack is fundamental for both red teams testing defenses and blue teams building them.
Ready to Fortify Your Defenses?
DLL side-loading is just one piece of the complex threat puzzle. To build a truly resilient security posture, continuous learning is key.
Next Steps:
- Test your environment: Use a safe, controlled lab to simulate a DLL side-loading attack and validate your detection capabilities. Always ensure you have explicit permission.
- Review your logging: Check if you are collecting Sysmon Event ID 7 (Image loaded) and if your SOC can create alerts for suspicious load events.
- Audit application controls: Review your WDAC or AppLocker policies. Are they in allowlist mode? Do they restrict execution to trusted paths only?
Share this knowledge with your team, and start implementing these secure practices today. The cost of prevention is always lower than the cost of a breach.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































