Third-Party Apps Data Exposure
The Silent 64% Threat and How to Stop It Explained Simply
Imagine your website as a high-security office building. You control the front door, but what about the dozens of delivery people, maintenance workers, and consultants who come in every day? New 2026 research reveals a shocking reality: 64% of these digital “third-party visitors”, applications like analytics tools and social media pixels, are accessing sensitive data inside your organization without a legitimate reason. This represents a 25% year-over-year increase and creates a massive, often invisible, attack surface.
This guide breaks down this critical third-party application security threat. We’ll move beyond the alarming statistics to explain exactly how this data exposure happens, map it to real-world adversary techniques like MITRE ATT&CK T1190, and provide a clear, actionable framework for defenders to regain control. Whether you're a security leader, a developer, or just starting in cybersecurity, understanding this risk is the first step toward building a more secure digital environment.
Table of Contents
- Executive Summary: The State of Third-Party Risk
- A Real-World Scenario: From Marketing Pixel to Data Breach
- Technical Breakdown: How Unjustified Access Happens
- Mapping to MITRE ATT&CK: Understanding the Adversary's Playbook
- Red Team vs. Blue Team: Perspectives on the Threat
- Step-by-Step Guide to Securing Your Third-Party Ecosystem
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Your Security Roadmap Starts Now
Executive Summary: The State of Third-Party Risk
The digital supply chain is under siege. A comprehensive 12-month study of 4,700 leading websites exposes a severe and growing governance failure. The core finding is that nearly two-thirds (64%) of all third-party applications have access to sensitive user data, like payment details, credentials, or personal information, without any clear business need for it.
This "unjustified access" crisis is accelerating, up from 51% just one year prior. Major contributors include ubiquitous tools like Google Tag Manager (implicated in 8% of violations), Shopify apps (5%), and the Facebook Pixel (4%). The sectors hit hardest are often those with budget constraints: government sites saw malicious activity spike from 2% to 12.9%, and 1 in 7 education sites now show signs of active compromise.
Perhaps the most telling statistic is the awareness-action gap. While 81% of security leaders identify web-based attacks as a top priority, only 39% have actually deployed solutions to manage third-party risk. This 42-point gap is the reason the problem is getting worse, not better. The following table summarizes the stark contrast between high-performing organizations and the average, highlighting that effective security is a matter of process, not just budget.
| Security Benchmark | Top-Performing Organizations | Average Organization | Key Insight |
|---|---|---|---|
| Number of Third-Party Apps | ≤ 8 | 15 - 25 | Quantity directly increases attack surface. |
| Unjustified Data Access | Rigorously blocked | 64% of apps have it | A governance failure, not a technical one. |
| Primary Risk Owner | Unified IT/Security oversight | 43% driven by Marketing alone | Departmental silos create risk. |
| Response to Compromise Signals | Automated monitoring & alerts | Reliance on basic WAFs (24% of orgs) | Reactive tools miss supply chain attacks. |
A Real-World Scenario: From Marketing Pixel to Data Breach
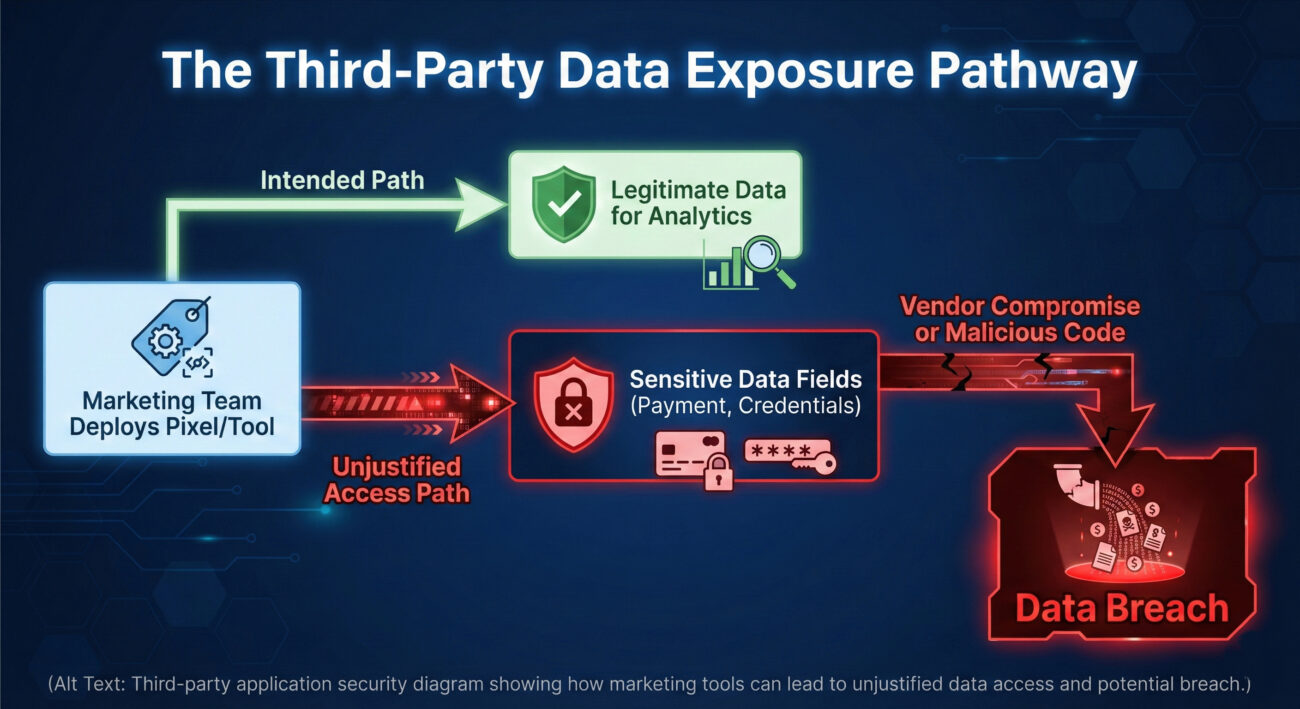
Let's translate the statistics into a narrative. Consider "SecureBuy," a fictional mid-sized e-commerce retailer. The marketing team wants to optimize ad campaigns and installs the Facebook Pixel using Google Tag Manager. To ensure they track all possible conversions, they grant the pixel "Full DOM Access" and enable "Automatic Advanced Matching." This means the script can read everything a user types on any page it's loaded on, not just the intended product views.
Months later, a threat actor exploits a vulnerability in a different, smaller analytics tool also used on SecureBuy's site. Using this foothold (a technique known as software supply chain compromise), they inject malicious JavaScript into the payment page. Because the Facebook Pixel is already there with broad permissions, the malicious code finds it easy to exfiltrate the credit card details users enter, camouflaging the traffic as normal pixel activity. SecureBuy's basic Web Application Firewall (WAF) never triggers an alert because the request originates from a "trusted" third-party domain.
The result? A data breach affecting thousands of customers, traced back not to a direct hack of SecureBuy, but to the weak governance around a marketing tool's excessive permissions. This scenario, mirrored in the real-world Polyfill.io attack, illustrates why controlling third-party application security is non-negotiable.
Technical Breakdown: How Unjustified Access Happens
Understanding the mechanics is key to defense. Unjustified access isn't typically a bug; it's a misconfiguration stemming from a lack of "least privilege" principles. Here are the primary technical causes:
1. Over-Permissioning via Tag Managers
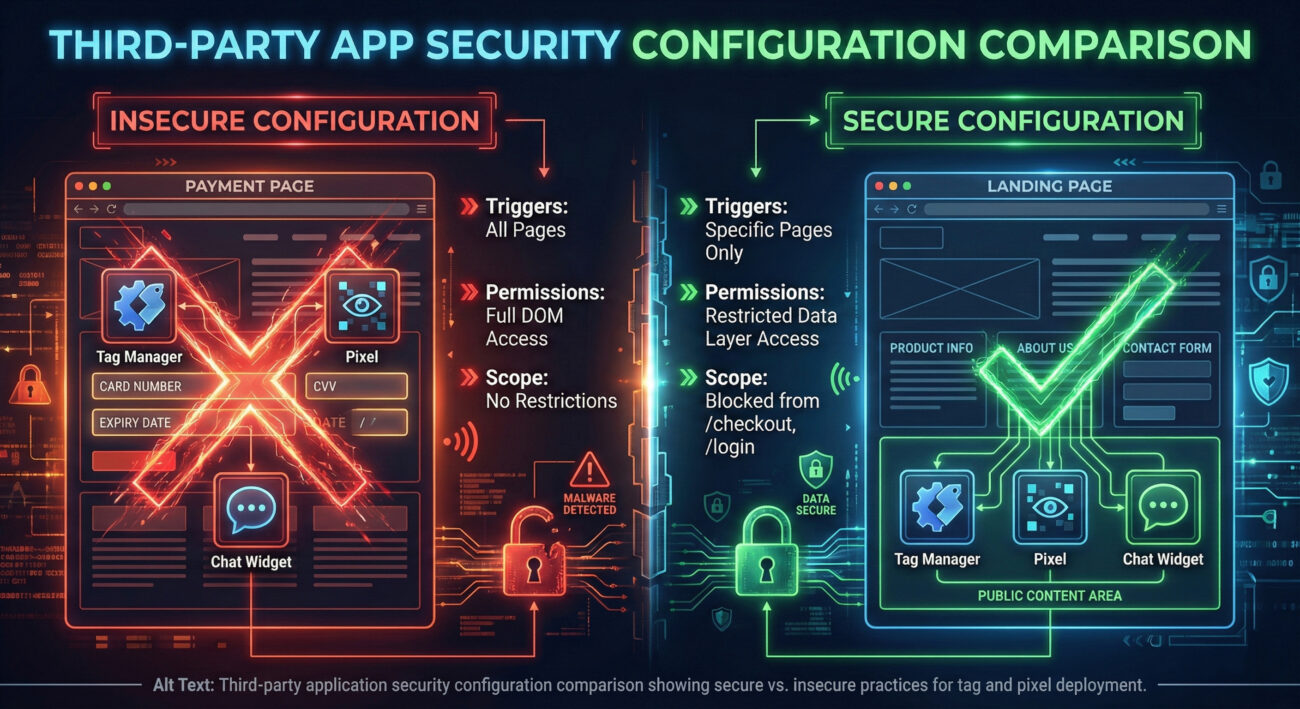
Tools like Google Tag Manager are powerful but dangerous when ungoverned. A common mistake is deploying a tag with a trigger of "All Pages" or granting it permission to read the entire Document Object Model (DOM). This allows a simple analytics script to silently harvest data from sensitive forms.
2. "Automatic Advanced Matching" & Data Scraping
Features like Facebook Pixel's "Automatic Advanced Matching" are designed to improve ad targeting by hashing user data like email. When improperly scoped, these features actively scan input fields across the entire site, including password and credit card fields, creating a rich data harvest for a potential attacker.
3. Shadow IT and Lack of Runtime Context
Marketing or sales teams often deploy tools directly, without IT review. These "shadow" applications are never assessed for the specific data they access at runtime. A chatbot widget on a homepage doesn't need to run on the payment confirmation page, yet it often does by default, gaining access to full transaction details.
Mapping to MITRE ATT&CK: Understanding the Adversary's Playbook
Framing this threat within the MITRE ATT&CK framework helps security professionals understand, communicate, and defend against it systematically. The unjustified access problem enables several key tactics and techniques.
Primary Tactic: Initial Access (TA0001)
- Technique T1190 - Exploit Public-Facing Application: A compromised third-party script (like the malicious Polyfill.io script) is delivered to the victim's browser via the trusted website. The victim's application (the website) is exploiting the trust relationship with the user to deliver the malware. The "public-facing application" in this case is the third-party vendor's service, which has been compromised.
Supporting Tactic: Collection (TA0009)
- Technique T1056.001 - Input Capture: Keylogging: When an over-permissioned third-party script runs on a login or payment page, it can capture keystrokes and input field values directly. This turns a marketing tool into an unwitting keylogger.
- Technique T1119 - Automated Collection: Scripts with "Automatic Advanced Matching" are designed to automatically scan and collect data from forms, aligning perfectly with this automated collection technique.
Supporting Tactic: Exfiltration (TA0010)
- Technique T1041 - Exfiltration Over C2 Channel: Stolen data is sent to an adversary-controlled server. This traffic can be disguised as legitimate beaconing to the third-party's domain (e.g., facebook.com, google-analytics.com), making it extremely difficult to detect without specialized runtime monitoring.
By understanding these mappings, blue teams can better prioritize controls like strict Content Security Policies (CSP), subresource integrity (SRI), and continuous third-party script monitoring to disrupt these adversary workflows.
Red Team vs. Blue Team: Perspectives on the Threat
The Red Team (Adversary) View
Objective: Steal sensitive data or credentials with minimal detection.
- Target Identification: Scan for websites using known over-permissioned tools (e.g., Facebook Pixel with default settings). Tools like BuiltWith or manual inspection make this easy.
- Initial Access: Instead of attacking the target directly, look for vulnerabilities in the third-party application's supply chain. A smaller, less-secure vendor is the perfect weak link.
- Execution & Collection: Once the third-party script is compromised, it runs with the trust of the main website. It can manipulate the DOM, hook into event listeners, and capture all data entered by users, bypassing most traditional perimeter defenses.
- Advantage: The attack originates from a whitelisted, trusted domain. Logs on the target server show nothing anomalous, as the malicious code runs entirely in the user's browser.
The Blue Team (Defender) View
Objective: Prevent data exfiltration and detect compromised third-party assets.
- Prevention: Implement a strict governance process. No third-party script is deployed without security review, least-privilege scoping, and SRI tags. Use Content Security Policies (CSP) to restrict allowed script sources and data destinations.
- Detection: Deploy specialized runtime application security monitoring tools that can detect when a script accesses sensitive form fields (e.g., `input[type="password"]`, `[data-credit-card]`). Monitor for abnormal network calls to third-party domains.
- Response: Have an automated kill-switch. If a script is found to be malicious or overreaching, it must be possible to immediately block it at the CDN, tag manager, or firewall level without waiting for a developer deployment.
- Challenge: Overcoming organizational silos. The blueprint requires close collaboration with Marketing, Product, and Development teams to enforce policies without hindering business agility.
Step-by-Step Guide to Securing Your Third-Party Ecosystem
This practical framework is designed to close the 42-point awareness-action gap. You don't need to do everything at once; start with Step 1.
Step 1: Conduct a Comprehensive Audit & Inventory
Action: Shine a light on what's already running. Use browser developer tools, network monitors, or dedicated tools like Blacksmith or Snyk to catalog every third-party script, pixel, library, and widget on your key pages (homepage, login, checkout).
Deliverable: A living inventory spreadsheet with: Script Name, Provider, Purpose/Justification, Pages Where It Loads, Data It Accesses, and Owner (Dept.).
Step 2: Apply the "Principle of Least Privilege"
Action: For each item in your inventory, ruthlessly scope its permissions.
- In Tag Managers (GTM): Change triggers from "All Pages" to specific page paths (e.g., `Page URL contains `/blog/`). Explicitly block scripts from `/checkout`, `/login`, `/account`.
- For Pixels: Disable features like "Automatic Advanced Matching." Configure them to only fire on specific, non-sensitive events.
- Technical Enforcement: Implement Subresource Integrity (SRI) hashes for critical libraries to ensure they haven't been tampered with.
Step 3: Implement Runtime Monitoring and Defense
Action: Deploy tools that provide visibility into what scripts are doing in real-time. This is your last line of defense.
- Monitor for Sensitive Data Access: Use tools that can alert you when any script interacts with password fields, credit card inputs, or personal data.
- Harden with CSP: Develop and deploy a strong Content Security Policy. Start in report-only mode (`Content-Security-Policy-Report-Only`) to monitor potential breakages, then enforce. Resources from MDN Web Docs are invaluable here.
- Plan for Incidents: Have a documented playbook for immediately disabling a compromised third-party script.
Step 4: Bridge the Organizational Divide
Action: Create a formal cross-functional governance board. This should include Security, IT, Legal/Compliance, Marketing, and Product.
Process: Establish a mandatory security review for any new third-party tool request. The requesting team must provide a business justification and a data privacy impact assessment. The security team evaluates the vendor's security posture and defines the technical guardrails (scoping, CSP rules).
Common Mistakes & Best Practices
❌ Common Mistakes
- Default Allow-All Policies: Deploying scripts globally "just in case" they're needed.
- Shadow Deployments: Allowing business units to embed scripts directly into pages or tag managers without review.
- Over-Reliance on WAFs: Assuming a WAF can catch malicious data exfiltration via trusted third-party domains.
- Ignoring Dormant Scripts: Leaving scripts active that haven't transmitted data in 90+ days, which are perfect targets for takeover.
- Trusting Vendor Security Claims Blindly: Not performing due diligence on the security practices of your third-party providers.
✅ Best Practices
- Implement a Formal Procurement Process: Every new third-party tool must pass a security and privacy review.
- Enforce Least Privilege by Default: Scope every script to the minimum pages and data it needs to function.
- Deploy Runtime Protection: Use specialized tools for third-party application security monitoring that go beyond static analysis.
- Adopt a Zero-Trust Mindset: Treat every external script as potentially malicious and segment your site accordingly.
- Foster Cross-Departmental Collaboration: Regular meetings between Security and Marketing to align on goals and risks are crucial.
Frequently Asked Questions (FAQ)
Q: We're a small team with no budget for fancy tools. What's the single most effective thing we can do?
A: Start with a manual audit and inventory (Step 1). This cost-free action alone will reveal shocking exposures. Then, spend an afternoon in your Google Tag Manager or equivalent, and remove global triggers from scripts that don't need them. These two actions can eliminate a huge portion of your risk immediately.
Q: Isn't this the vendor's responsibility to secure their own scripts?
A: It's a shared responsibility. The vendor is responsible for the security of their infrastructure and code. You are responsible for what data you choose to expose to that vendor's script on your website. Applying least-privilege scoping is your duty under data protection laws like GDPR and CCPA.
Q: How is this different from a typical software supply chain attack (like Log4j)?
A: It's a subset focused on the client-side. Traditional supply chain attacks (e.g., compromising an open-source library) affect server-side code. Client-side third-party application security risks involve scripts that run in your users' browsers. They are harder to detect with traditional tools and directly lead to data theft from your customers.
Q: Can a strong Content Security Policy (CSP) solve this?
A: A CSP is a critical and highly effective layer of defense, but not a silver bullet. It can prevent unauthorized scripts from loading and block unauthorized data exfiltration destinations. However, it cannot fully control what an authorized script (like a whitelisted Facebook Pixel) does once it loads. CSP must be combined with least-privilege scoping and runtime monitoring.
Key Takeaways
- The 64% Statistic is a Governance Failure: The explosive growth in unjustified data access is not a technical mystery. It results from a lack of process, cross-departmental collaboration, and the application of least-privilege principles.
- Marketing Tools Are the Primary Attack Vector: Nearly half of all risk exposure is driven by Marketing departments deploying tools without security oversight. Bridging this organizational divide is non-negotiable.
- Traditional Security Tools Are Blind: WAFs and network firewalls cannot see or stop data theft orchestrated by a trusted, whitelisted third-party script running in the browser. You need dedicated client-side runtime monitoring.
- Adversaries Follow a Clear Playbook (MITRE ATT&CK): Threat actors exploit these weaknesses using established techniques like T1190 and T1056.001. Defenders must build controls that disrupt these specific techniques.
- Action Beats Awareness: An 81% awareness rate coupled with a 39% action rate is a formula for continued breaches. Start with a simple audit and inventory today to begin closing your own personal risk gap.
Call to Action: Your Security Roadmap Starts Now
The research is clear, the threat is growing, and the adversary's playbook is well-documented. The time for passive concern is over. You have the knowledge and the framework to act.
Your mission, should you choose to accept it:
- This Week: Open your browser's Developer Console (F12) on your site's login and checkout pages. Take a screenshot of the "Network" tab showing all the third-party requests. Share it with your security or engineering lead and start the conversation.
- This Month: Lead or request a formal cross-departmental meeting (Security, IT, Marketing) to present the findings of this article and the linked research. Propose the adoption of the 4-Step Guide outlined above.
- This Quarter: Implement at least Step 1 (Full Inventory) and Step 2 (Least Privilege Scoping) for your top 5 most critical user journeys.
For a deeper dive into the data, including full sector breakdowns and a list of high-risk applications, you can download the original 43-page report that inspired this analysis. Continue your education with trusted resources like the OWASP Top Ten for web risks and the MITRE ATT&CK® Framework for adversary behavior.
The security of your users' data now depends as much on your digital supply chain as on your own code. Take control of it today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































