AWS CodeBuild Misconfiguration
A Critical Guide for Cloud Security Explained Simply
Table of Contents
- Executive Summary: The Cloud's Silent Alarm
- Understanding AWS CodeBuild & The Misconfiguration
- The Attacker's Playbook: MITRE ATT&CK Mapping
- Real-World Scenario: How a Simple Mistake Leads to a Catastrophic Breach
- Step-by-Step Guide: Finding & Fixing the Misconfiguration
- Common Mistakes & Best Practices
- Red Team vs. Blue Team Perspective
- Implementation Framework: Proactive Defense
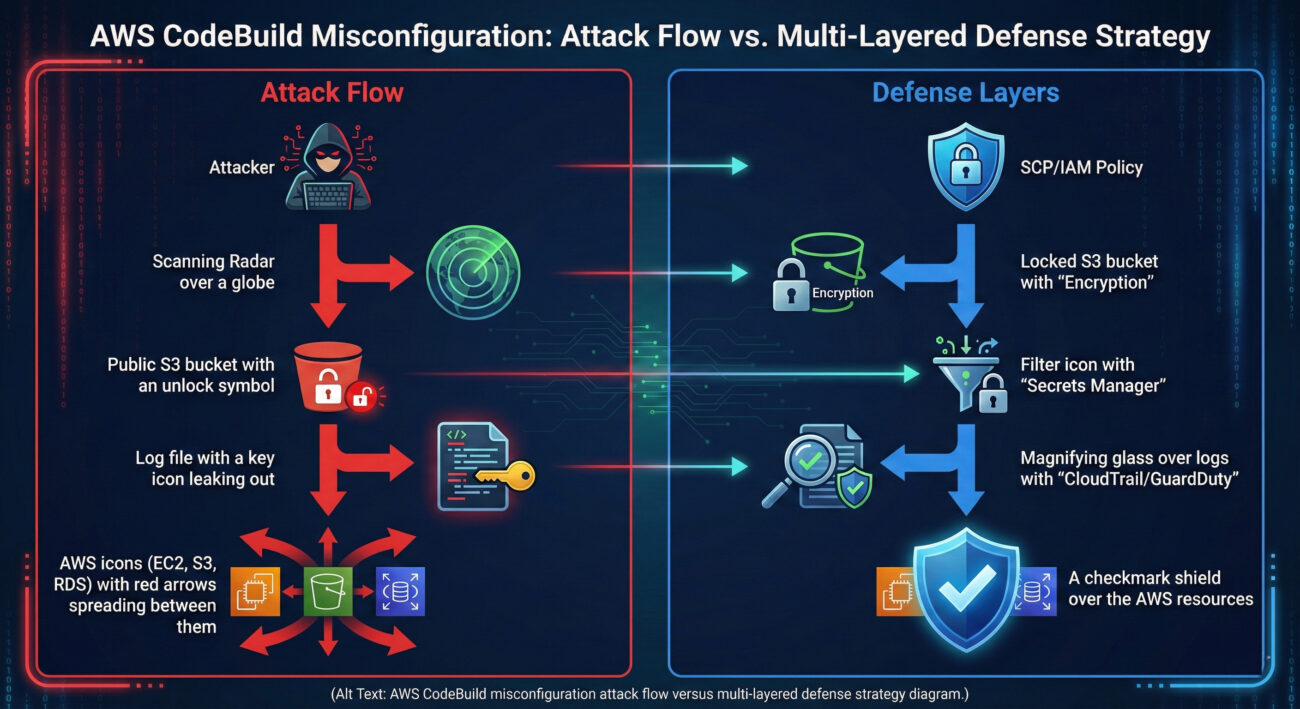
- Visual Breakdown: Attack Flow & Defense Layers
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call-to-Action: Secure Your Pipeline Today
Executive Summary: The Cloud's Silent Alarm
In the high-speed world of DevOps, the AWS CodeBuild service is a cornerstone for continuous integration and delivery (CI/CD). However, a pervasive and often overlooked misconfiguration can transform this powerful tool into a critical vulnerability, silently exposing sensitive credentials like AWS IAM keys, API tokens, and SSH keys to the public internet. This isn't a theoretical flaw; it's a real-world attack vector actively exploited by threat actors scanning for improperly secured build logs.
This guide deconstructs the AWS CodeBuild misconfiguration, explaining not just the "how" but also the "why" behind the risk. We'll map the exploitation to the MITRE ATT&CK framework, provide a tactical walkthrough for both attackers and defenders, and arm you with a concrete framework to audit and secure your own environments. Understanding this vulnerability is the first step in preventing a devastating cloud breach.
Understanding AWS CodeBuild & The Misconfiguration
AWS CodeBuild is a fully managed build service that compiles source code, runs tests, and produces software packages. For each build, it generates detailed logs. By default, these logs are stored in an S3 bucket or CloudWatch Logs. The misconfiguration occurs when these logs are made publicly accessible.
The Root Cause: Public Logs in S3/CloudWatch
If the S3 bucket storing logs has a permissive bucket policy (like Principal: "*" with Action: "s3:GetObject"), or if CloudWatch Logs are not encrypted and are exposed, the build logs become a treasure trove. What's in these logs? Often, everything the build process had access to:
- AWS IAM Role Temporary Credentials (via AWS CodeBuild's default behavior).
- Secrets passed as environment variables (e.g.,
DATABASE_PASSWORD). - API Keys for third-party services (GitHub, Slack, etc.).
- Source Code and build artifacts, potentially containing hardcoded secrets.
The critical oversight is assuming that build logs are private by default. In AWS, security is a shared responsibility; the platform provides the tools, but you must configure them correctly.
The Attacker's Playbook: MITRE ATT&CK Mapping
This AWS CodeBuild misconfiguration is not an isolated issue but part of a broader attack chain. Here’s how it maps to the MITRE ATT&CK for Cloud framework:
| MITRE ATT&CK Tactic | Technique (ID) | How It Applies to CodeBuild Misconfiguration |
|---|---|---|
| Reconnaissance | TA0043: Cloud Infrastructure Discovery | Attackers use automated tools to scan for publicly accessible S3 buckets and CloudWatch Logs associated with CodeBuild. |
| Credential Access | T1552.001: Unsecured Credentials in Cloud Storage | The exposed build logs are a form of unsecured cloud storage containing IAM credentials, API keys, and other secrets. |
| Initial Access | T1078.004: Valid Accounts - Cloud Accounts | Stolen IAM credentials from logs are used to gain initial access to the AWS cloud environment. |
| Persistence & Lateral Movement | T1136.003: Create Cloud Account & T1550.002: Pass the Hash (Cloud) | With initial access, attackers create backdoor IAM users, assume other roles, and move laterally across resources. |
This mapping highlights that the misconfiguration is a critical enabler for multiple stages of a cloud-focused attack, turning a simple logging mistake into a full-scale compromise.
Real-World Scenario: How a Simple Mistake Leads to a Catastrophic Breach
Imagine a development team at "StartupXYZ" is in a rush to deploy a new feature. They configure a new CodeBuild project and let it use the default log settings, unaware that the associated S3 bucket was created with a broad, public-read policy by an old Terraform script.
Step 1: The Build Runs
The CodeBuild project pulls code from GitHub, which requires a GitHub Personal Access Token (PAT) stored as a plaintext environment variable GH_TOKEN. It also deploys to AWS, using an IAM Role attached to the build project.
Step 2: Logs Are Written
The build log captures the entire process. While the token itself might not be echoed, the IAM role's temporary credentials (AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY, AWS_SESSION_TOKEN) are often logged by AWS CLI or SDK calls during the build.
Step 3: The Attacker Discovers
An attacker, running a routine scan for misconfigured *.s3.amazonaws.com buckets, stumbles upon the log bucket. They browse to a recent log file and use simple grep commands to extract credentials.
Step 4: Full Environment Compromise
Using the stolen IAM credentials, the attacker authenticates to the AWS account. They now have the permissions of the build role, which is often overly permissive (e.g., AdministratorAccess or broad write permissions to EC2, S3, and RDS). A data breach or crypto-mining campaign begins.
Step-by-Step Guide: Finding & Fixing the Misconfiguration
Part A: Detection & Audit
You must proactively hunt for this vulnerability. Here’s a methodical approach:
Step 1: Identify All CodeBuild Projects
Use the AWS CLI or Console to list all projects. Note their log configuration (S3 bucket or CloudWatch Logs group).
Step 2: Audit S3 Bucket Policies
For projects logging to S3, retrieve and analyze the bucket policy for public access.
Step 3: Audit CloudWatch Log Groups
Check if any CloudWatch Logs are publicly accessible via resource-based policies.
Step 4: Simulate External Access
Use a tool like S3Scanner or a simple curl command from an external network to attempt anonymous access to a log file URL.
Part B: Remediation & Hardening
Step 1: Immediately Restrict Log Access
Apply the principle of least privilege. For S3, block public access and update the bucket policy to only allow access from specific IAM roles or VPC Endpoints.
Step 2: Enable Encryption at Rest
Ensure all S3 buckets and CloudWatch Log Groups use AWS KMS keys (SSE-KMS) for encryption. This adds a layer of protection even if access controls fail.
Step 3: Scrub Secrets from Logs
Prevent secrets from being logged in the first place. Use AWS Secrets Manager or Parameter Store, and reference them in env as secretsManager type. Never echo secrets in build commands.
Step 4: Implement Continuous Monitoring
Use AWS Config with conformance packs, or tools like Prowler, to continuously check for public S3 buckets and overly permissive log configurations. Set up CloudWatch Alerts for anomalous access patterns.
Common Mistakes & Best Practices
Common Mistakes (The "Don'ts")
- Assuming Defaults are Secure: Using the default S3 bucket creation settings which historically allowed public access.
- Hardcoding Secrets in buildspec.yml: Storing API keys and passwords directly in the build specification file.
- Over-Permissive IAM Roles for CodeBuild: Attaching the
AdministratorAccess policy to a build project "for convenience".
- Neglecting Log Encryption: Storing sensitive logs without Server-Side Encryption (SSE) enabled.
- Lack of Regular Audits: Never reviewing S3 bucket policies or CloudWatch Logs permissions post-creation.
Best Practices (The "Dos")
- Enforce Least Privilege IAM Roles: Create custom IAM roles for CodeBuild with only the permissions needed for the specific build job.
- Leverage AWS Secrets Manager/Parameter Store: Always fetch secrets dynamically at runtime. Never log them.
- Enable S3 Block Public Access & Bucket Policies: Apply account-wide S3 Block Public Access settings and craft restrictive bucket policies.
- Mandate Encryption: Enforce KMS encryption for all S3 buckets and CloudWatch Log Groups via Service Control Policies (SCPs).
- Automate Security Scanning: Integrate secret scanning tools like TruffleHog into your pipeline to catch leaked credentials before they reach logs.
Red Team vs. Blue Team Perspective
Red Team (Attackers)
Objective: Discover and exploit publicly accessible CodeBuild logs to gain initial foothold and escalate privileges.
- Reconnaissance: Use tools like S3Scanner,
awscli (if some read access exists), or even simple Google dorks (site:s3.amazonaws.com "CodeBuild" "log").
- Credential Harvesting: Write scripts to parse thousands of log files, searching for patterns of AWS keys, GitHub tokens, and other secrets.
- Lateral Movement: Upon obtaining credentials, immediately use them to call
sts:GetCallerIdentity to confirm access, then enumerate resources using tools like enumerate-iam or Pacu.
- Persistence: Create backdoor IAM users, install crypto-miners on EC2 instances, or exfiltrate data from RDS and S3.
Blue Team (Defenders)
Objective: Prevent credential leakage, detect unauthorized access attempts, and respond to incidents.
- Prevention: Implement the hardening steps above. Use Infrastructure as Code (IaC) scanning with Checkov or tfsec to catch misconfigurations before deployment.
- Detection: Monitor CloudTrail logs for
GetObject calls from unexpected IP addresses or anonymous principals on your log buckets. Set up Amazon GuardDuty to detect credential exfiltration.
- Response: Have an incident response plan for compromised IAM credentials. This includes steps to revoke the credentials, identify affected resources, and rotate all potentially exposed secrets.
- Education: Continuously train developers and DevOps engineers on secure CI/CD practices and the dangers of misconfigurations.
Implementation Framework: Proactive Defense
Common Mistakes (The "Don'ts")
- Assuming Defaults are Secure: Using the default S3 bucket creation settings which historically allowed public access.
- Hardcoding Secrets in buildspec.yml: Storing API keys and passwords directly in the build specification file.
- Over-Permissive IAM Roles for CodeBuild: Attaching the
AdministratorAccesspolicy to a build project "for convenience". - Neglecting Log Encryption: Storing sensitive logs without Server-Side Encryption (SSE) enabled.
- Lack of Regular Audits: Never reviewing S3 bucket policies or CloudWatch Logs permissions post-creation.
Best Practices (The "Dos")
- Enforce Least Privilege IAM Roles: Create custom IAM roles for CodeBuild with only the permissions needed for the specific build job.
- Leverage AWS Secrets Manager/Parameter Store: Always fetch secrets dynamically at runtime. Never log them.
- Enable S3 Block Public Access & Bucket Policies: Apply account-wide S3 Block Public Access settings and craft restrictive bucket policies.
- Mandate Encryption: Enforce KMS encryption for all S3 buckets and CloudWatch Log Groups via Service Control Policies (SCPs).
- Automate Security Scanning: Integrate secret scanning tools like TruffleHog into your pipeline to catch leaked credentials before they reach logs.
Red Team (Attackers)
Objective: Discover and exploit publicly accessible CodeBuild logs to gain initial foothold and escalate privileges.
- Reconnaissance: Use tools like S3Scanner,
awscli(if some read access exists), or even simple Google dorks (site:s3.amazonaws.com "CodeBuild" "log"). - Credential Harvesting: Write scripts to parse thousands of log files, searching for patterns of AWS keys, GitHub tokens, and other secrets.
- Lateral Movement: Upon obtaining credentials, immediately use them to call
sts:GetCallerIdentityto confirm access, then enumerate resources using tools like enumerate-iam or Pacu. - Persistence: Create backdoor IAM users, install crypto-miners on EC2 instances, or exfiltrate data from RDS and S3.
Blue Team (Defenders)
Objective: Prevent credential leakage, detect unauthorized access attempts, and respond to incidents.
- Prevention: Implement the hardening steps above. Use Infrastructure as Code (IaC) scanning with Checkov or tfsec to catch misconfigurations before deployment.
- Detection: Monitor CloudTrail logs for
GetObjectcalls from unexpected IP addresses or anonymous principals on your log buckets. Set up Amazon GuardDuty to detect credential exfiltration. - Response: Have an incident response plan for compromised IAM credentials. This includes steps to revoke the credentials, identify affected resources, and rotate all potentially exposed secrets.
- Education: Continuously train developers and DevOps engineers on secure CI/CD practices and the dangers of misconfigurations.
Implementation Framework: Proactive Defense
Move beyond one-time fixes. Implement this layered framework for ongoing security:
- Policy as Code (PaC): Define and enforce security policies using AWS Service Control Policies (SCPs) and IAM Policies. For example, an SCP can deny the creation of S3 buckets without encryption or block S3 bucket policies that contain
Principal: "*". - Automated Guardrails: Integrate security scans into your CI/CD pipeline itself. Use AWS CodeBuild's built-in support for running security linters, or break the build if a secret is detected in the source code.
- Unified Observability: Centralize logs (CloudTrail, S3 access logs, CloudWatch) into a security information and event management (SIEM) system like Amazon Security Lake, Splunk, or a similar tool for correlation and advanced threat detection.
- Regular Attack Simulation: Conduct periodic Red Team exercises targeting your own CI/CD pipeline to validate controls and uncover blind spots.
Visual Breakdown: Attack Flow & Defense Layers
Frequently Asked Questions (FAQ)
Q: If my S3 bucket is private but my CloudWatch Logs are public, is that still a risk?
A: Absolutely yes. The attack vector is any publicly accessible log store. You must audit both S3 and CloudWatch Logs configurations.
Q: I use AWS CodePipeline with CodeBuild. Does this affect me?
A: Yes, if CodeBuild is a stage in your pipeline. The logging configuration is set at the CodeBuild project level, regardless of whether it's invoked manually or via CodePipeline.
Q: Are temporary IAM role credentials from CodeBuild really that dangerous?
A: Extremely. These credentials are short-lived but often have very high privileges during their validity period (typically one hour). An attacker can use them to cause immense damage or establish persistent access within that window.
Q: What's the single most important action I should take right now?
A: Enable S3 Block Public Access at the account level and audit all existing CodeBuild project log destinations. This provides a critical safety net.
Key Takeaways
- The misconfiguration is common and dangerous: Publicly accessible AWS CodeBuild logs are a low-hanging fruit for attackers leading directly to cloud account takeover.
- It maps to critical MITRE ATT&CK Tactics: Specifically aiding in Reconnaissance (TA0043) and Credential Access (T1552.001).
- Prevention is a multi-layered effort: Combine restrictive IAM roles, proper secrets management, enforced encryption, and automated scanning.
- Detection is possible: Leverage CloudTrail, GuardDuty, and access logging to monitor for unauthorized attempts to access your build logs.
- Security is continuous: Regular audits, automated policy enforcement, and team education are non-negotiable for maintaining a secure CI/CD pipeline.
Call-to-Action: Secure Your Pipeline Today
Don't let your build logs be the weakest link. Start your remediation journey now:
- Schedule a 1-hour audit this week for all your AWS CodeBuild projects.
- Implement Account Guardrails: Turn on S3 Block Public Access and create an SCP to deny the creation of non-encrypted log resources.
- Educate Your Team: Share this article with your DevOps and development teams to raise awareness.
For further learning, explore these essential resources:
- AWS Official Documentation: Monitoring CodeBuild Logs
- MITRE ATT&CK: T1552.001 - Unsecured Credentials in Cloud Storage
- Git-Secrets Tool by AWS Labs (Prevent committing secrets to Git)
- In-Depth Blog: AWS CodeBuild Security Best Practices
Your cloud security starts with a single, informed action. Take it now.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































