Critical WordPress Plugin Vulnerability
10k+ Sites Exposed Full Analysis & Fix
A critical security flaw has been discovered in the popular Modular Data Science Plugin for WordPress, putting over 10,000 websites at immediate risk of a complete takeover. Designated as CVE-2025-53079, this vulnerability carries a maximum CVSS score of 9.8, placing it firmly in the "critical" category. This blog post provides a comprehensive, beginner-friendly analysis of this WordPress plugin vulnerability, explaining exactly how the attack works, its real-world implications, and the definitive steps you must take to secure your site.
Table of Contents
- Executive Summary: The Gravity of CVE-2025-53079
- Vulnerability Deep Dive: How the Exploit Works
- Mapping to MITRE ATT&CK: The Attacker's Playbook
- Red Team View: How Attackers Exploit This Flaw
- Blue Team View: Detection, Defense, and Mitigation
- Step-by-Step Guide: Patching & Securing Your WordPress Site
- Common Mistakes & Best Practices for Plugin Security
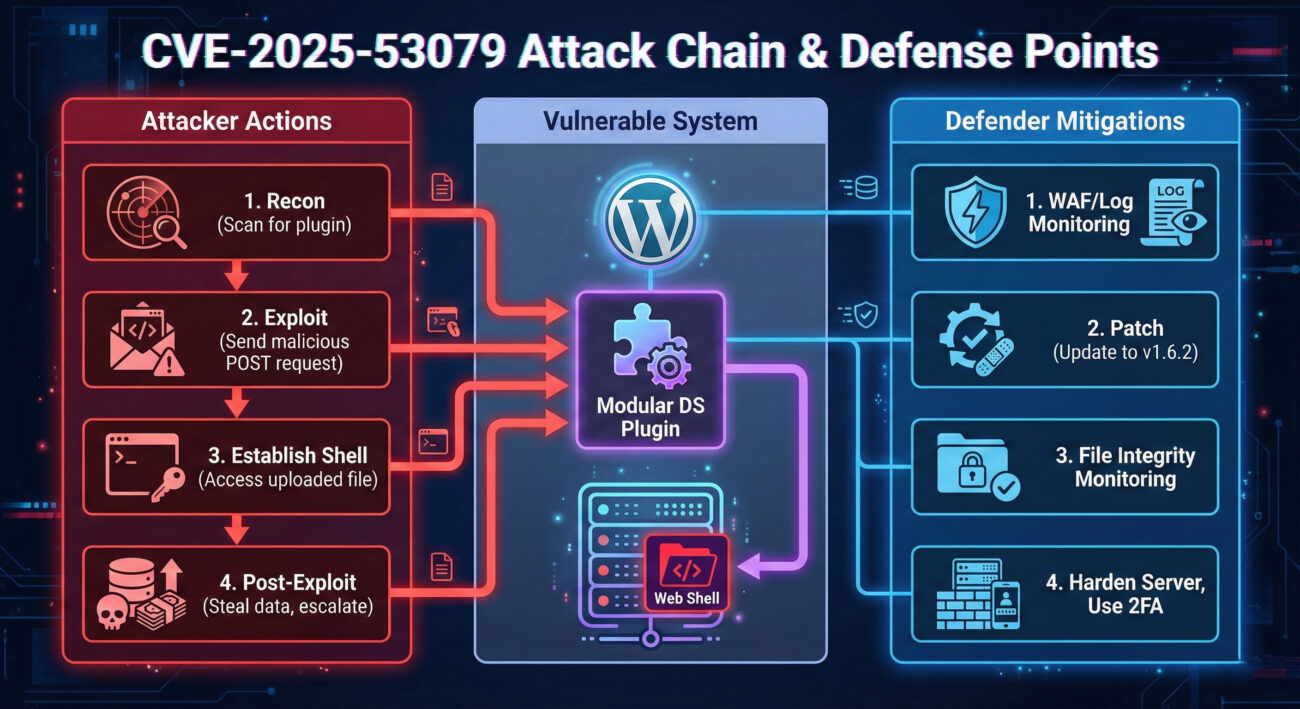
- Visual Breakdown: Attack Flow & Defense Matrix
- Frequently Asked Questions (FAQ)
- Key Takeaways & Immediate Actions
Executive Summary: The Gravity of CVE-2025-53079
The Modular Data Science Plugin was designed to add data visualization and analysis capabilities to WordPress. However, a severe oversight in its code created a gaping security hole. The vulnerability resides in the plugin's file upload handler, specifically in the /includes/admin/upload.php file (or similar endpoint).
In essence, the plugin failed to implement proper authentication and file type validation for a function meant to upload data files. This allowed any visitor to your website, completely unauthenticated, to upload arbitrary files, including malicious PHP shells, directly to the server.
Impact: Successful exploitation leads to Remote Code Execution (RCE). An attacker can gain full control over the affected WordPress site, enabling them to:
- Deface the website.
- Steal sensitive user data and database information.
- Install backdoors for persistent access.
- Use the server as part of a botnet or to launch attacks against other systems.
- Encrypt files for ransom (ransomware).
The vulnerability is "wormable", meaning it could be used to automate attacks across thousands of sites. A Proof-of-Concept (PoC) exploit code has been publicly released, making it trivial for even low-skilled threat actors to weaponize it.
Vulnerability Deep Dive: How the Exploit Works
Let's break down the technical mechanics of this WordPress plugin vulnerability without the overwhelming jargon.
The Flawed Code Pathway
WordPress plugins often create custom endpoints (URLs) to handle specific tasks. This plugin created an endpoint accessible via a POST request, likely similar to:
POST /wp-content/plugins/modular-data-science/includes/admin/upload.phpThe intended purpose was for administrators to upload data files (like CSV). The critical failures were:
- Missing Authentication Check: The script did not verify if the user making the request was logged in as an administrator, or logged in at all.
- Missing Authorization Check: It did not check if the user had the proper permissions ('manage_options' capability in WordPress) to perform this action.
- Insufficient File Validation: It either performed no check on the uploaded file's extension/content or used a weak check that could be easily bypassed.
This trifecta of failures is a classic recipe for disaster. An attacker could simply craft an HTTP request with a malicious file and send it directly to this public URL.
The Attack Sequence
Here’s a simplified step-by-step of the exploit:
Step 1: Reconnaissance
The attacker scans a target WordPress site to identify if the vulnerable Modular Data Science Plugin (versions < 1.6.2) is installed. This can be done using public tools.
Step 2: Crafting the Payload
The attacker creates a simple PHP web shell file. A common example is a one-liner that executes system commands passed via a GET parameter:
<?php system($_GET['cmd']); ?>This file is saved as something like shell.php.
Step 3: Unauthenticated File Upload
Using a tool like curl or a simple script, the attacker sends a POST request to the vulnerable upload.php endpoint, with the malicious PHP file attached.
curl -X POST -F "[email protected]" https://target-site.com/wp-content/plugins/modular-data-science/includes/admin/upload.phpThe server, lacking any checks, accepts the file and saves it to a publicly accessible directory within the plugin (e.g., /wp-content/uploads/mds/).
Step 4: Remote Code Execution
The attacker now navigates to the uploaded file: https://target-site.com/wp-content/uploads/mds/shell.php?cmd=whoami. The server executes the PHP code, running the whoami command and returning the result (e.g., www-data) to the attacker's browser. Full server control is achieved.
Mapping to MITRE ATT&CK: The Attacker's Playbook
Understanding this vulnerability within the MITRE ATT&CK framework helps defenders recognize the tactics, techniques, and procedures (TTPs) used.
| Tactic | Technique (ID) | How It Applies to This Vulnerability |
|---|---|---|
| Initial Access | T1190: Exploit Public-Facing Application | The attacker exploits the unauthenticated file upload feature in a public WordPress plugin. |
| Execution | T1059: Command and Scripting Interpreter | By uploading a PHP web shell, the attacker can execute arbitrary system commands on the web server. |
| Persistence | T1505: Server Software Component | The uploaded web shell becomes a persistent backdoor within the web server's file system. |
| Defense Evasion | T1221: Template Injection / File Upload Bypass | The technique involves bypassing weak file upload restrictions to place malicious code. |
This mapping shows that the exploit isn't an isolated incident but part of a standard attack chain. Blue teams can use these identifiers to search for related activity in logs.
Red Team View: How Attackers Exploit This Flaw
A Red Team simulates real-world adversaries to test defenses. Here's how they would approach this WordPress plugin vulnerability.
🔴 Attacker's Objectives & Methods
- Objective 1 - Initial Compromise: Use automated scanners (e.g., WPScan) to mass-find WordPress sites with the vulnerable plugin version. The public PoC is integrated into tools, making exploitation automated and widespread.
- Objective 2 - Establish Foothold: Upload a robust, obfuscated web shell instead of a simple one-liner. This provides a stable, hidden command-and-control (C2) interface.
- Objective 3 - Privilege Escalation: Use the initial shell (running as the web user, e.g., 'www-data') to probe the server for misconfigurations, weak sudo rights, or kernel vulnerabilities to gain root access.
- Objective 4 - Lateral Movement/Data Theft: Dump the WordPress
wp-config.phpfile to steal database credentials. Exfiltrate the entire database containing user info, passwords (hashed), and sensitive post data. - Objective 5 - Covering Tracks: Modify or delete WordPress and server access logs to remove evidence of the file upload and subsequent malicious requests.
🔵 Defender's Counter-Strategy (Detection)
How a Blue Team would detect these Red Team activities:
- Detect Scanning: Monitor web server logs for an unusual surge in requests to plugin-specific directories (
/wp-content/plugins/modular-data-science/) from single IPs. - Detect Exploit Attempt: Use a Web Application Firewall (WAF) with rules to block POST requests containing PHP files to unusual upload paths. Look for POST requests to the known vulnerable endpoint.
- Detect Web Shell: Employ file integrity monitoring (FIM) on the
wp-content/uploads/and plugin directories to alert on new PHP file creation. Use server-side antivirus/clamAV to scan for known shell signatures. - Detect Post-Exploitation: Monitor for suspicious child processes spawned by the web server (e.g.,
/bin/sh -c whoami). Alert on database export commands or large outbound data transfers from the web server.
Blue Team View: Detection, Defense, and Mitigation
For defenders, the priority is immediate action to eliminate the risk and prepare for future vulnerabilities.
Immediate Containment & Eradication
- Check for Compromise: Immediately scan your
wp-content/uploads/and all plugin directories for recently added, suspicious PHP files (especially in the Modular Data Science plugin folder). Look for files with names likeshell.php,cmd.php,wp-config.php.bak, etc. - Update Immediately: The only complete fix is to update the Modular Data Science Plugin to version 1.6.2 or higher. This patch adds the necessary authentication and file validation checks.
- If Update Isn't Possible: Disable or completely delete the plugin from your site immediately. The functionality loss is far less critical than a site compromise.
Long-Term Defense Strategy
- Implement a Web Application Firewall (WAF): A WAF can block exploit attempts in real-time. Cloud-based WAFs like Cloudflare or Sucuri offer rules specifically for such plugin vulnerabilities.
- Enable File Integrity Monitoring: Use security plugins like Wordfence or server-level tools like Tripwire to get alerts on unauthorized file changes.
- Principle of Least Privilege: Ensure your WordPress file permissions are correct. Directories should be 755, files 644. The web user should have minimal write access outside of necessary uploads directories.
- Regular Security Audits: Regularly audit your installed plugins. Remove unused ones. Only install plugins from reputable sources with a history of timely updates.
Step-by-Step Guide: Patching & Securing Your WordPress Site
Follow this actionable guide to address this specific vulnerability and harden your overall WordPress security posture.
Step 1: Verify Plugin Installation
Log into your WordPress admin dashboard. Navigate to Plugins -> Installed Plugins. Look for "Modular Data Science" or "MDS". If it's not there, you are not directly vulnerable to CVE-2025-53079, but the following steps are still good practice.
Step 2: Immediate Update or Removal
If the plugin is installed:
a. Check the version number listed next to it.
b. If it's below 1.6.2, you should see an "Update Available" notice. Click "Update Now" immediately.
c. If no update is available or you cannot update, you must deactivate and delete the plugin. Click "Deactivate" and then "Delete".
Step 3: Scan for Compromise
Install a reputable security scanner like Wordfence or Sucuri. Run a full malware and file integrity scan. This will identify if any web shells were uploaded before you patched the hole.
Step 4: Implement a WAF
Sign up for a WAF service. This acts as a protective shield. For example, Cloudflare's free plan includes basic WAF rules. Point your site's DNS to Cloudflare to activate it. Configure rules to block SQL injection and file upload exploits.
Step 5: Harden WordPress
a. Change all passwords: Admin, database, and hosting account.
b. Enable Two-Factor Authentication (2FA): Use a plugin like Wordfence or Google Authenticator to add 2FA for all admin users.
c. Limit Login Attempts: Install a plugin to prevent brute-force attacks.
d. Disable File Editing: Add define('DISALLOW_FILE_EDIT', true); to your wp-config.php file to prevent code editing from the admin panel.
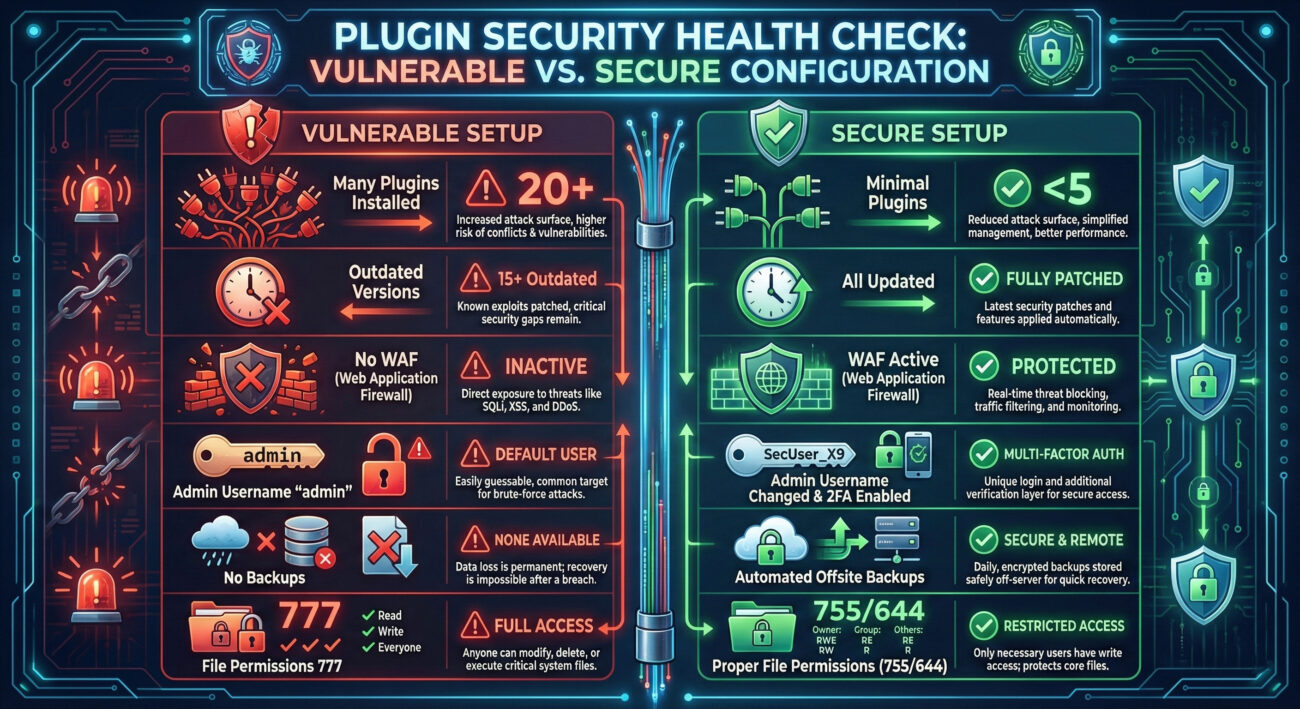
Common Mistakes & Best Practices for Plugin Security
This incident highlights widespread security pitfalls. Let's contrast what went wrong with what should be done.
❌ Common Security Mistakes
- Assuming Plugins Are Secure: Blindly trusting third-party code without vetting.
- Ignoring Update Notifications: Postponing critical security updates for days or weeks.
- Using Nulled or Pirated Plugins: These often contain backdoors and malware, and never receive security patches.
- Installing Unnecessary Plugins: Each plugin adds to your site's "attack surface".
- Lacking a Backup Strategy: Having no recent, clean backup makes recovery from a breach painful and costly.
✅ Essential Best Practices
- Practice Principle of Least Privilege: Plugins and users should have only the minimum permissions needed.
- Implement a Patch Management Schedule: Test and apply updates for core, plugins, and themes within 24-48 hours of release, especially for critical fixes.
- Source Plugins Wisely: Only use plugins from the official WordPress.org repository or highly reputable commercial developers.
- Conduct Regular Audits: Quarterly, review all installed plugins. Deactivate and delete anything not in active use.
- Maintain Automated, Offsite Backups: Use a reliable service like BlogVault, UpdraftPlus, or your host's tool. Ensure backups are stored separately from your hosting account.
Visual Breakdown: Attack Flow & Defense Matrix
Frequently Asked Questions (FAQ)
Q1: I deleted the plugin a while ago. Am I still at risk?
A: If you completely deleted the plugin files before any attack occurred, the vulnerability is gone. However, you should still scan for any backdoors that might have been uploaded before deletion. The act of deleting a compromised plugin does not remove already-dropped malicious files.
Q2: Is my website hosted on WordPress.com affected?
A: No. Managed WordPress hosting services like WordPress.com (not to be confused with self-hosted WordPress.org sites) manage plugin installations and security at the platform level. They typically do not allow the installation of such vulnerable third-party plugins or quickly patch them globally.
Q3: What if I need the old version of the plugin for compatibility?
A: Running a vulnerable version is never an option. The risk of a complete site takeover far outweighs any functionality loss. You must either:
- Update the plugin and find an alternative way to achieve the needed compatibility.
- Find a different, secure plugin that provides similar features.
- Commission a developer to create a custom, secure solution.
Q4: How can developers avoid creating such vulnerabilities?
A: Developers must follow WordPress coding standards and security best practices:
- Always use nonces and capability checks (
current_user_can()) for all admin/ajax endpoints. - Use WordPress built-in file upload functions (
wp_handle_upload()) which perform security checks. - Validate and sanitize all user input, including file extensions and MIME types.
- Store uploaded files outside the web root if possible, or at least in directories with
.htaccessrules preventing PHP execution.
Q5: Where can I get official information about this CVE?
A: Always refer to primary sources:
- Official CVE Record for CVE-2025-53079
- WordPress Plugin Repository Changelog
- National Vulnerability Database: NVD Entry
Key Takeaways & Immediate Actions
The WordPress plugin vulnerability CVE-2025-53079 is a stark reminder that third-party code is a primary attack vector. Here’s what you must remember and do right now:
- Patch Immediately: If you use the Modular Data Science Plugin, update it to version 1.6.2+ without delay.
- Assume Breach, Scan Thoroughly: After patching, run a full security scan to rule out prior compromise.
- Layered Defense is Key: No single tool is enough. Combine timely updates, a WAF, file monitoring, and strong access controls (2FA).
- Your Plugins Are Your Risk: Audit them regularly. Less is more. Choose quality over quantity.
- Backup Religiously: A clean, recent backup is your ultimate recovery tool after a security breach.
Call-to-Action: Secure Your Digital Perimeter Today
Don't wait for a compromise to happen. Proactive security is the only effective defense.
- Block an hour on your calendar today. Use it to log into all your WordPress sites and follow the Step-by-Step Guide above.
- Bookmark critical resources: The Wordfence Threat Intelligence blog and the CVE website for ongoing awareness.
- Share this knowledge. Forward this analysis to your colleagues, clients, or community. Collective awareness raises the security baseline for everyone.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































