SOC Modernization
Stop These 4 Outdated Habits Crushing Your Cyber Defenses Explained Simply
Table of Contents
- Executive Summary: The Modern SOC Imperative
- Habit 1: The SIEM-as-a-Panic-Button Mentality
- Habit 2: Treating All Alerts as Equally Critical
- Habit 3: The "Island" Approach to Threat Intelligence
- Habit 4: Manual, Human-Centric Response Playbooks
- Real-World Scenario: A Phishing Campaign Unveiled
- Common Mistakes & Best Practices
- Red Team vs. Blue Team: The Duality of Modern Threats
- Implementation Framework: Your 90-Day SOC Modernization Plan
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action
Executive Summary: The Modern SOC Imperative
In the relentless arms race of cybersecurity, your Security Operations Center (SOC) is the frontline command. Yet, many SOCs are fighting today's advanced persistent threats with yesterday's playbooks, trapped by outdated SOC habits that create exhaustion, not excellence. This post deconstructs the four most corrosive legacy practices, from SIEM misuse to manual response, and provides a clear, actionable roadmap for SOC modernization. We'll map these habits to specific MITRE ATT&CK techniques they fail to catch, and detail how modernizing your approach is the only way to build a proactive, resilient defense.
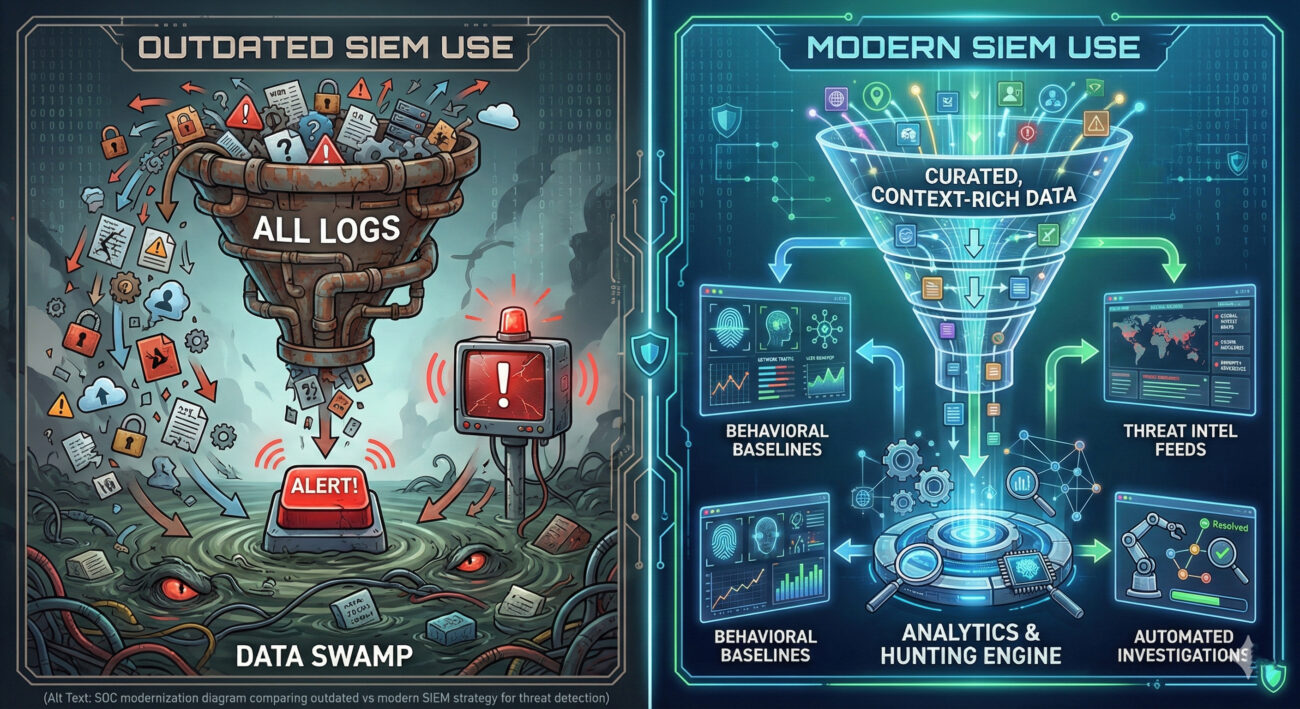
Habit 1: The SIEM-as-a-Panic-Button Mentality
Treating your Security Information and Event Management (SIEM) system as a glorified log collector and alert siren is the foundational failure. The outdated habit is: "Collect everything, hope to find something during an incident." This creates data swamps, skyrockets costs, and buries critical signals in noise.
The Technical Breakdown & MITRE ATT&CK Gap
A threat actor employs living-off-the-land techniques, like using built-in Windows tools (e.g., PowerShell for T1059.001: Command and Scripting Interpreter) or legitimate admin tools. A bloated, untuned SIEM may log these events but won't correlate them into a suspicious sequence (e.g., PowerShell execution followed by network discovery T1046: Network Service Discovery and lateral movement T1021: Remote Services). Without proactive threat hunting queries and behavioral analytics, this attack chain remains invisible until it's too late.
Habit 2: Treating All Alerts as Equally Critical
The "alert flood" is the primary symptom of a sick SOC. The outdated habit is: "Prioritize alerts based solely on static, pre-defined severity (High, Medium, Low)." This ignores context, is this "High" alert on a public-facing server or an isolated test machine? Analysts burn out on false positives, creating alert fatigue where real breaches are missed.
Contextual Prioritization: The Modern Fix
Modern SOCs implement Risk-Based Alerting (RBA). An alert's priority is dynamically calculated using:
- Asset Criticality: Is the target a domain controller or a user's laptop?
- User Sensitivity: Does the account have admin privileges?
- Threat Intelligence Context: Is the source IP on a known malware distribution list?
- Behavioral Anomaly Score: How unusual is this activity for the user/asset?
This approach directly counters techniques like T1078: Valid Accounts, where an attacker uses stolen credentials. A login from a new country might be "Medium," but if it's for a finance department user accessing the SharePoint server containing sensitive data, RBA escalates it to "Critical."
Habit 3: The "Island" Approach to Threat Intelligence
Subscribing to Threat Intelligence Feeds (TI Feeds) and dumping them into a separate portal analysts rarely check is a wasted investment. The outdated habit is: "Threat intel is a separate team's responsibility, not integrated into daily operations."
This leaves the SOC blind to the latest attacker Tactics, Techniques, and Procedures (TTPs). For example, if a feed reports a new Cobalt Strike command-and-control (C2) server IP, but that indicator isn't automatically added to your SIEM's blocklists or detection rules, you remain vulnerable.
Mapping to MITRE ATT&CK & Integration
Effective intelligence is integrated and actionable. It should fuel:
| MITRE ATT&CK Technique | Outdated SOC Approach | Modern, Intel-Integrated Approach |
|---|---|---|
| T1588.002: Obtain Capabilities - Tool (e.g., Mimikatz) | Read about the tool in a weekly intel report. | SIEM automatically hunts for process names, hash values, or network signatures associated with the tool, triggering proactive alerts. |
| T1190: Exploit Public-Facing Application | Generic "port scan" or "exploit attempt" alerts. | EDR/XDR tools are updated with behavioral patterns matching exploits for the specific vulnerabilities mentioned in intel briefs. |
Habit 4: Manual, Human-Centric Response Playbooks
When an alert fires, if the first step is "Analyst manually opens 5 tools to investigate," you've already lost precious time. The outdated habit is: "Incident response is a purely manual, analyst-driven process." This slows Mean Time to Respond (MTTR) to a crawl, allowing attackers to deepen their foothold.
Automation & Orchestration: The Force Multiplier
Security Orchestration, Automation, and Response (SOAR) platforms are not optional. They secure by executing pre-defined playbooks in seconds. For a "phishing email reported" alert, an automated playbook can:
Step 1: Enrichment
Automatically query the email's sender IP, domain, and attachment hash against internal logs and external threat intel APIs.
Step 2: Containment
If indicators are malicious, automatically quarantine the email from all user inboxes, block the sender domain at the email gateway, and isolate the endpoint if it clicked the link.
Step 3: Eradication & Recovery
Initiate a scan on affected endpoints, reset the password of the user who interacted with the phish (if credentials were entered), and create a ticket for post-incident review.
This automation directly counters fast-moving techniques like T1566: Phishing and its sub-techniques.
Real-World Scenario: A Phishing Campaign Unveiled
Let's see how these outdated habits fail and how SOC modernization succeeds against a multi-stage attack.
Attack Chain: Spear Phishing (T1566.002) → User executes macro (T1204.002) → Downloads Cobalt Strike beacon (T1588.002) → Lateral Movement via PsExec (T1021.002) → Data exfiltration (T1048).
- Outdated SOC: SIEM floods with macro-enabled email alerts (Habit 2). No integration with endpoint data means the beacon download is missed (Habit 1 & 3). Manual investigation starts hours later, after data is already gone (Habit 4).
- Modern SOC: Integrated email security flags the spear phish with high confidence. The EDR (Endpoint Detection and Response) tool, sharing context with the SIEM, detects the unusual child process (beacon) spawned from Word. A SOAR playbook automatically isolates the endpoint, hunts for related network connections (finding lateral movement attempts), and blocks C2 IPs from threat intel feeds. Analysts are presented with a consolidated, high-fidelity incident within minutes.
Common Mistakes & Best Practices
Common Mistakes (X)
- Logging everything without a data retention and relevance strategy.
- Chasing every alert, leading to analyst burnout and high turnover.
- Treating threat intelligence as a "nice-to-have" report instead of an operational feed.
- Fearing automation due to "false positive" concerns, preferring slow manual control.
- Not training analysts on MITRE ATT&CK to understand adversary behavior.
Best Practices (✓)
- Implement log curation: Define clear use cases first, then collect only the data needed.
- Adopt Risk-Based Alerting to focus human attention on true business risks.
- Automatically ingest and integrate Threat Intel Indicators (IOCs & TTPs) into detection and blocking tools.
- Start with low-risk, high-volume automation (e.g., ticket creation, IOC enrichment) and expand.
- Use MITRE ATT&CK as a common language for planning detection, conducting hunts, and writing reports.
Red Team vs. Blue Team: The Duality of Modern Threats
Red Team (Threat Actor) View
They love outdated SOCs. Their strategy exploits these habits directly:
- Against Habit 1 & 2: Use slow, low-signature techniques (Living off the Land) to avoid generating "High" severity alerts, knowing analysts are drowning in noise.
- Against Habit 3: Use newly registered domains or temporary infrastructure, knowing it will take time for intel to be published and manually added to blocklists.
- Against Habit 4: Rely on the time gap between detection and manual response to achieve their objectives (data theft, ransomware deployment).
Their goal is to remain in the "detection gap" created by legacy processes.
Blue Team (Defender) View
The modern Blue Team flips the script through SOC modernization:
- Countering Red Team: Use behavioral analytics and hunting to find anomalies that don't trigger traditional alerts, closing the detection gap.
- Operationalizing Intel: Automate the ingestion and application of IOCs/TTPs, shrinking the adversary's window of opportunity.
- Leveraging Automation: Use SOAR to respond at machine speed, containing threats before they can spread, effectively "moving faster than the attacker."
The goal shifts from reactive alert triage to proactive threat disruption.
Implementation Framework: Your 90-Day SOC Modernization Plan
Phase 1: Foundation (Days 1-30)
- Conduct a Tool & Process Audit: Document all data sources, alert rules, and manual workflows.
- Define Top 5 Use Cases: Align with business risk (e.g., ransomware, data exfiltration, account compromise).
- Begin Log Curation: For each use case, identify the critical logs needed and stop collecting irrelevant data.
- External Resource: Study the SANS PICERL Framework for incident handling structure.
Phase 2: Integration & Tuning (Days 31-60)
- Implement Risk-Based Alerting: Work with IT to tag asset criticality. Start weighting alerts.
- Connect One Threat Intel Feed: Choose a reputable feed (e.g., AlienVault OTX) and automate IOC ingestion into your SIEM/firewall.
- Build Your First SOAR Playbook: Automate the response to a simple, high-volume alert like "Malicious Hash Detected."
Phase 3: Advanced Operations (Days 61-90)
- Initi-ate Proactive Threat Hunts: Use MITRE ATT&CK (reference the official MITRE ATT&CK website) to guide weekly hunts for specific techniques relevant to your industry.
- Measure & Refine: Track new KPIs: Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), Alert Triage Rate, and Automation Execution Count.
- Foster a Learning Culture: Use Atomic Red Team to safely test your new detections in a lab environment.
Frequently Asked Questions (FAQ)
Q: Isn't collecting all logs the safest option for forensics?
A: While comprehensive data is ideal, unfiltered collection is impractical and costly. The key is strategic collection. Define your investigative requirements (compliance, key systems) and ensure you collect and retain those logs at a higher fidelity. Use cheaper, longer-term storage for less critical logs.
Q: We're a small team with a limited budget. Can we still modernize?
A> Absolutely. SOC modernization is about process first, tools second. Start by tuning your existing SIEM (reduce noise), implementing free threat intel sources (like AlienVault OTX), and using built-in automation features in your current tools. Prioritize changes that reduce workload, like creating dashboards and standard operating procedures (SOPs).
Q: How does MITRE ATT&CK practically help my daily SOC work?
A: It provides a structured knowledge base of adversary behavior. Use it to:
- Gap Analysis: Map your current detections to ATT&CK techniques to see where you're blind.
- Hunt Planning: "Today, we will hunt for T1053.005 - Scheduled Task" provides clear focus.
- Incident Reporting: Describe an incident as "T1566.001 -> T1204.002 -> T1573" for clear, universal communication.
Key Takeaways
- Outdated SOC habits create preventable risk by fostering alert fatigue, slowing response, and missing sophisticated attacks.
- Modernization starts with curating data and implementing Risk-Based Alerting to empower, not overwhelm, your analysts.
- Threat intelligence must be operationalized and integrated into tools, not stored in isolated reports.
- Automation (SOAR) is non-negotiable for achieving the speed required to disrupt modern adversaries.
- Use the MITRE ATT&CK framework as your common language for planning detection, conducting hunts, and measuring coverage.
Call to Action
Your SOC doesn't have to be a victim of its own processes. Start your modernization journey today.
Pick ONE of the four habits outlined above that resonates most with your team's pain points. In your next meeting, discuss one concrete step from our 90-day plan to address it. The path from a reactive, overwhelmed SOC to a proactive, resilient security command center begins with a single, deliberate action.
For further learning, explore the CISA Cybersecurity Performance Goals (CPGs) for foundational practices.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































