The Unseen Danger of Abandoned Accounts
The Silent Cyber Threat You Must Eliminate Now Explained Simply
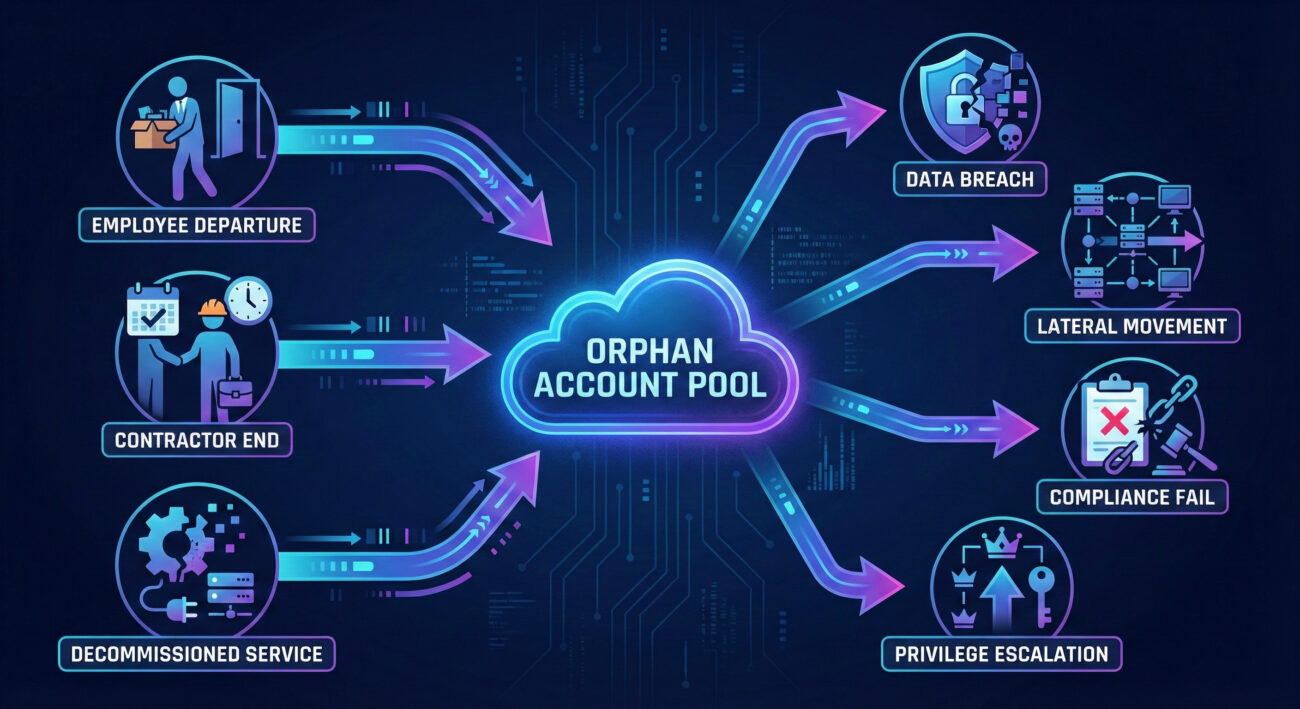
In the sprawling digital landscape of a modern organization, user accounts are created for employees, contractors, and service bots. But what happens when the person leaves, the project ends, or the contractor's role is complete? Too often, the associated accounts are forgotten, left active, unmonitored, and unmanaged. These are orphan accounts, and they represent one of the most pervasive and underestimated security risks in cybersecurity today.
Imagine leaving a spare key to your office under the doormat after an employee quits. A threat actor finds that key. That's the essence of an orphan account. This guide will demystify this hidden danger, explain exactly how attackers exploit them using recognized MITRE ATT&CK techniques, and provide you with a clear, actionable framework to find and neutralize these threats.
Table of Contents
- What Are Orphan Accounts? More Than Just Forgotten Logins
- Why Are Orphan Accounts a Critical Security Risk?
- The MITRE ATT&CK Connection: Mapping the Threat
- Real-World Attack Scenario: From Orphan Account to Full Breach
- Step-by-Step: How Attackers Exploit Orphan Accounts
- Red Team vs. Blue Team: Perspectives on Orphan Accounts
- Common Mistakes & Best Practices
- Implementation Framework: The 5-Step Orphan Account Cleanup
- Visual Breakdown: The Lifecycle of an Orphan Account Attack
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Secure Your Environment Now
What Are Orphan Accounts? More Than Just Forgotten Logins
An orphan account (sometimes called a "ghost" or "dangling" account) is any user credential that remains active within a system after its legitimate owner no longer requires access. The "owner" could be a departed employee, a contractor whose project concluded, a temporary staff member, or even a service account for decommissioned software.
These accounts are "orphaned" because they lack an active, responsible user to monitor their activity or update their security settings. They are often created with standard, sometimes privileged, access and then fall off the IT department's radar during offboarding processes.
Common Causes of Orphan Accounts:
- Incomplete Offboarding: HR notifies IT that an employee has left, but IT only disables the primary Active Directory account, missing secondary accounts in GitHub, Salesforce, AWS, or the VPN.
- Contractor & Vendor Churn: Short-term contractors are given access that is never revoked after their contract ends.
- Silent Service Accounts: Accounts created to run automated tasks or for application integrations. When the service is retired, the account remains.
- Mergers & Acquisitions: Integrating systems from another company can lead to duplicate or obsolete accounts that are overlooked.
- Lack of Centralized Inventory: No single source of truth exists for all user accounts across all platforms (cloud, on-prem, SaaS).
Why Are Orphan Accounts a Critical Security Risk?
Orphan accounts are not just clutter; they are active, credentialed backdoors. Their danger is multifaceted:
- No User Monitoring: Since no legitimate user is logging in, any activity on the account is, by definition, suspicious, but there's often no one to notice. This makes them perfect for stealthy, long-term attacks.
- Outdated Security Posture: These accounts rarely have Multi-Factor Authentication (MFA) enabled and often use old, potentially compromised, or easily guessable passwords.
- Privilege Creep: Over time, the original user may have accumulated access rights. An orphaned account retains all these privileges, potentially giving an attacker access to sensitive data and critical systems.
- Compliance Nightmare: Regulations like GDPR, HIPAA, and SOC 2 require strict access control. Orphan accounts are a direct violation, leading to failed audits and hefty fines.
The MITRE ATT&CK Connection: Mapping the Threat
The exploitation of orphan accounts maps directly to several key tactics and techniques in the MITRE ATT&CK framework, a globally recognized knowledge base of adversary tactics. Understanding this mapping helps defenders speak a common language and prioritize defenses.
| MITRE ATT&CK Tactic | Relevant Technique | How Orphan Accounts Are Used |
|---|---|---|
| Initial Access (TA0001) | T1078 - Valid Accounts | Orphan accounts are the quintessential valid account. Attackers use credential stuffing, password spraying, or leaked passwords to gain initial access, bypassing perimeter defenses because the credentials are legitimate. |
| Persistence (TA0003) | T1098 - Account Manipulation T1136 - Create Account |
Once in, attackers use the orphan account to create new backdoor accounts or modify existing ones (like resetting passwords or adding SSH keys) to maintain access even if the orphan account is eventually discovered. |
| Privilege Escalation (TA0004) | T1078.002 - Domain Accounts | If the orphan account already has elevated privileges (e.g., a forgotten admin account), it provides immediate escalation. If not, attackers use it to perform lateral movement to find more powerful accounts. |
| Lateral Movement (TA0008) | T1021 - Remote Services T1550 - Use Alternate Authentication Material |
Using the orphan account's credentials, attackers move laterally across the network, accessing file shares, internal wikis, or other systems to expand their foothold. |
By framing the orphan account risk within MITRE ATT&CK, security teams can proactively hunt for indicators of these techniques in their logs and align their defenses with industry best practices.
Real-World Attack Scenario: From Orphan Account to Full Breach
Let's follow a hypothetical but all-too-plausible scenario, "Project Ghost Access," to see how a threat actor leverages an orphan account.
Phase 1: Discovery & Initial Access
A hacker acquires a list of employee emails from a past data breach of a major corporation, "TechGlobal." They perform password spraying (T1110) against TechGlobal's VPN login portal. One set of credentials ([email protected] / Winter2023!) works. John Smith was a contractor who left 8 months ago, but his VPN account was never disabled.
Phase 2: Establishing Persistence & Reconnaissance
From the VPN, the attacker accesses the internal network. They find the orphan account has basic network share access. Using it, they locate internal IT documentation and discover a privileged service account named svc_backup_legacy used for an old backup system. The password is stored in plaintext in a shared file. This is another orphan account for a decommissioned service.
Phase 3: Privilege Escalation & Lateral Movement
The attacker uses the svc_backup_legacy credentials (T1078) to log into a domain server. This account has local admin rights on several key servers. Using Mimikatz or similar tools (T1003), they dump credentials from server memory, capturing the hash of a Domain Administrator account.
Phase 4: Impact & Exfiltration
With Domain Admin privileges, the attacker can now access any system, encrypt files for ransomware, or quietly exfiltrate sensitive intellectual property and customer data over several weeks, all originating from forgotten, unmonitored accounts.
Step-by-Step: How Attackers Exploit Orphan Accounts
Here is a technical breakdown of the common attack flow, useful for understanding the adversary's perspective.
Step 1: Reconnaissance & Credential Harvesting
Attackers scour LinkedIn, past breach databases (like HaveIBeenPwned), or even corporate websites to find names of former employees/contractors. They then compile username lists (e.g., firstname.lastname, flastname).
Step 2: Password Spraying & Credential Stuffing
Using tools like Hydra or SprayingToolkit, they attempt a few common passwords (CompanyName123, SeasonYear!) across many usernames to avoid lockouts. They also try credentials leaked from other breaches, banking on password reuse.
Simplified Example of a Password Spraying Command:
Explanation: This command tries the password 'Spring2024!' for every user in 'userlist.txt' against a VPN login form, waiting 30 seconds between attempts on each host (-W) to avoid triggering alarms.
Step 3: Initial Foothold & Network Discovery
Upon successful login, the attacker uses basic commands to map the network from within:
net view /domain
net use \\\\target-pc\\c$
# Linux/General - Check permissions and linked systems
id
ssh svc_backup@internal-server
Red Team vs. Blue Team: Perspectives on Orphan Accounts
Red Team (Attackers) View
Threat actors see orphan accounts as low-hanging fruit and a primary entry vector.
- Primary Target: Former contractor and service accounts, as they are less likely to be monitored.
- Method: Automated scanning with tools like BloodHound to find these accounts and their associated privileges automatically.
- Objective: Use them as a quiet, legitimate-looking launchpad for deeper network penetration and persistence.
- Advantage: Activity often blends in or goes entirely unnoticed due to lack of baseline behavior for the account.
Blue Team (Defenders) View
Defenders must treat orphan account management as a fundamental hygiene task.
- Primary Challenge: Gaining complete visibility across all systems (AD, cloud IAM, SaaS apps) to identify dormant accounts.
- Method: Implementing automated identity lifecycle management and regular access reviews.
- Objective: Reduce the attack surface to as few valid, active accounts as possible.
- Key Tactic: Hunting for logon events from accounts belonging to users marked as "terminated" in the HR system.
Common Mistakes & Best Practices
❌ Common Mistakes Organizations Make
- Manual Offboarding: Relying on checklists that humans can miss, leading to accounts slipping through the cracks.
- Ignoring Cloud & SaaS: Only managing on-premise Active Directory while neglecting accounts in AWS, Azure AD, Google Workspace, GitHub, etc.
- No Regular Audits: Never reviewing account logs or conducting formal access reviews.
- Weak Service Account Management: Using shared, powerful service accounts with non-expiring passwords and no ownership.
- Over-Permissioning: Granting excessive privileges "just in case," which then become embedded in orphan accounts.
✅ Best Practices for Defense
- Automate Identity Lifecycle Management: Integrate HR systems with IT provisioning (e.g., using SCIM) to automatically disable all accounts upon termination.
- Enforce Multi-Factor Authentication (MFA): Mandate MFA on ALL user accounts. While not a silver bullet, it significantly raises the bar for credential-based attacks.
- Implement Just-In-Time (JIT) Access: For privileged tasks, use PAM solutions that grant elevated access only when needed and for a limited time.
- Conduct Regular Access Reviews: Quarterly or semi-annual reviews where managers must certify their team members' access is still required.
- Use Strong Password Policies & Credential Managers: Enforce long, complex passwords or passphrases and discourage password reuse with enterprise password managers.
- Centralize Logging & Monitoring: Aggregate logs from all systems to detect logins from terminated-user accounts or from unusual locations.
Implementation Framework: The 5-Step Orphan Account Cleanup
Ready to act? Follow this structured framework to eliminate orphan accounts from your environment.
Step 1: Discovery & Inventory (The "Find" Phase)
You can't secure what you don't know exists. Use native tools and scripts to compile a list of all accounts.
- Active Directory: Use PowerShell:
Get-ADUser -Filter * -Properties LastLogonDate | Where-Object {$_.LastLogonDate -lt (Get-Date).AddDays(-90)}to find stale accounts. - AWS IAM: Use the CLI:
aws iam generate-credential-reportand analyze for unused access keys or old passwords. - Google Workspace/Microsoft 365: Use admin consoles to audit last sign-in activity.
- Consider tools like Tenable Nessus or Qualys for comprehensive asset and vulnerability discovery.
Step 2: Attribution & Validation (The "Verify" Phase)
Cross-reference your account list with authoritative sources.
- Match accounts against your HRIS (Human Resources Information System) active employee list.
- For service accounts, identify the application owner or team responsible.
- Flag any account without a clear, active owner for immediate review.
Step 3: Triage & Action (The "Fix" Phase)
Take action based on the account type and risk.
| Account Type | Recommended Action |
|---|---|
| Confirmed former employee/contractor | Disable immediately, then schedule for deletion after a retention period (e.g., 30-90 days). |
| Unknown/Unvalidated user account | Disable and investigate. If no owner claims it, delete. |
| Legacy service account | Assess if the service is still running. If not, disable. If yes, document ownership and rotate credentials. |
| Privileged orphan account | HIGH PRIORITY. Disable immediately. Conduct a forensic review of its recent activity logs. |
Step 4: Process Implementation (The "Prevent" Phase)
Establish automated guardrails to prevent future orphan accounts.
- Formalize an Identity and Access Management (IAM) Policy.
- Set up automated de-provisioning workflows between HR and IT.
- Implement a Privileged Access Management (PAM) solution for high-risk accounts.
- Enforce a periodic recertification process for all accounts, at least annually.
Step 5: Monitoring & Alerting (The "Sustain" Phase)
Continuously monitor for signs of orphan account misuse.
- Create SIEM alerts for logon attempts from accounts marked as "terminated."
- Monitor for impossible travel (logins from different countries in a short time).
- Regularly re-run the discovery scripts (Step 1) as part of a quarterly security audit.
Visual Breakdown: The Lifecycle of an Orphan Account Attack

Frequently Asked Questions (FAQ)
Q: What's the difference between an orphan account and a dormant account?
A: A dormant account belongs to a current user who hasn't logged in for a long time (e.g., someone on extended leave). An orphan account has no active owner (the user is gone). Dormant accounts can become orphaned if not managed properly.
Q: How often should we audit for orphan accounts?
A: At a minimum, quarterly. However, the best practice is to have continuous monitoring via automated tools that flag accounts inactive for 45-90 days and immediately disable accounts upon HR termination feed updates.
Q: Are service accounts considered orphan accounts?
A: They can be. If a service account is tied to a decommissioned application and has no documented owner, it is an orphan. Service accounts require even stricter management due to their often-high privileges.
Q: What's the first tool a small team should use to find orphan accounts?
A: Start with native, free tools. Use PowerShell for AD and the built-in access review features in your cloud provider (Azure AD Access Reviews, AWS IAM Access Analyzer). For a more unified view, consider open-source IAM tools or affordable SaaS solutions like Okta or Auth0 for smaller organizations.
Key Takeaways
- Orphan accounts are valid, active backdoors. They are not theoretical risks but primary attack vectors mapped to MITRE ATT&CK techniques like Valid Accounts (T1078).
- Automation is non-negotiable. Manual offboarding processes will fail. Integrate HR and IT systems to automate de-provisioning.
- Visibility is the first step to defense. You must inventory all accounts across all systems (on-prem, cloud, SaaS) before you can secure them.
- MFA and Least Privilege are critical mitigations. Enforcing Multi-Factor Authentication and granting only necessary access limits the blast radius if an orphan account is compromised.
- Continuous monitoring trumps periodic audits. Set up alerts for logins from terminated users to catch breaches in real-time.
Call to Action: Secure Your Environment Now
Don't let forgotten accounts be your downfall.
This week, take these three immediate actions:
- Run a stale account report in your primary directory (Active Directory, Azure AD, etc.).
- Pick one critical SaaS application (like GitHub, Salesforce, or your cloud console) and audit its user list against current employees.
- Schedule a 30-minute meeting with IT and HR to discuss automating the first step of the offboarding process.
For further learning, explore these essential resources:
MITRE ATT&CK: Valid Accounts (T1078) | CISA Identity and Access Management Guidance | NIST Cybersecurity Framework
Share this guide with your team to build collective awareness against the hidden risk of orphan accounts.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































