Cloudflare Patches ACME Bug That Permitted WAF Bypass
How Cloudflare's Bug Threatens SSL/TLS Security Explained Simply
In January 2026, cybersecurity researchers discovered a critical vulnerability in Cloudflare's implementation of the ACME (Automated Certificate Management Environment) protocol that could have allowed attackers to obtain valid SSL/TLS certificates for domains they didn't own. This bug, while promptly patched, revealed fundamental flaws in certificate validation logic that threaten the foundation of web security. The ACME protocol vulnerability highlights how even trusted security providers can inadvertently introduce critical weaknesses into the global internet infrastructure.
Table of Contents
- Executive Summary: The Gravity of the ACME Validation Bug
- What is the ACME Protocol and Why Does It Matter?
- Technical Deep Dive: How the ACME Validation Bug Worked
- Real-World Attack Scenario: Exploiting the Flaw
- MITRE ATT&CK Framework Mapping
- Step-by-Step: How an Attacker Could Exploit This Vulnerability
- Common Mistakes & Best Practices in Certificate Validation
- Red Team vs Blue Team Perspectives
- Implementation Framework: Protecting Your Organization
- Frequently Asked Questions
- Key Takeaways
- Call to Action
Executive Summary: The Gravity of the ACME Validation Bug
The ACME protocol vulnerability discovered in Cloudflare's systems represents a significant threat to internet security. SSL/TLS certificates form the backbone of secure web communications, establishing trust between websites and users. When a flaw allows unauthorized entities to obtain these certificates, the entire trust model collapses.
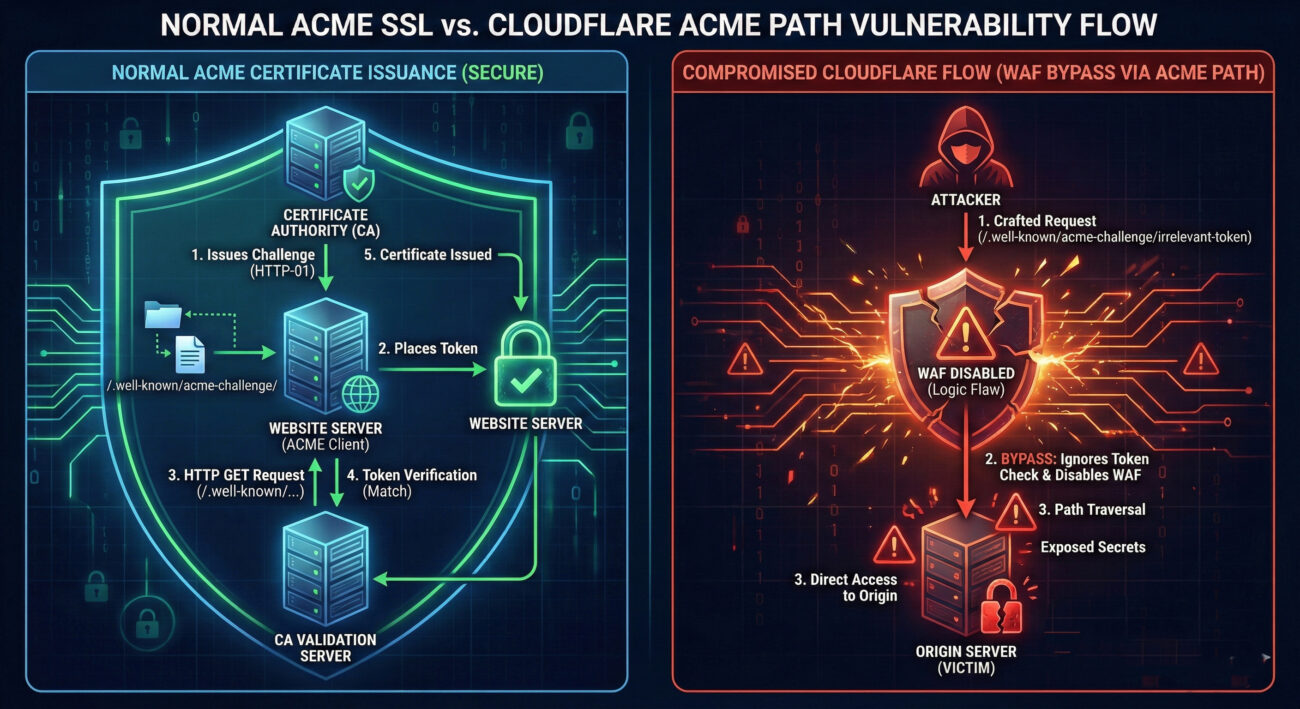
Cloudflare's implementation contained a logic flaw during domain validation where the system would incorrectly validate ownership if certain edge cases occurred in the validation process. This could have enabled attackers to trick the system into issuing certificates for domains they didn't control, potentially enabling sophisticated phishing attacks, man-in-the-middle attacks, and widespread trust erosion.
What is the ACME Protocol and Why Does It Matter?
ACME (Automated Certificate Management Environment) is the protocol that powers Let's Encrypt and other certificate authorities to automatically issue SSL/TLS certificates. It automates domain validation, certificate issuance, and renewal through a standardized API. The protocol has been revolutionary in enabling widespread HTTPS adoption by making certificates free and easy to obtain.
The Standard ACME Validation Flow
- Request: A client requests a certificate for a domain
- Challenge: The CA issues a validation challenge to prove domain ownership
- Response: The client responds to the challenge (HTTP-01, DNS-01, or TLS-ALPN-01)
- Verification: The CA verifies the challenge response
- Issuance: If verification succeeds, the CA issues the certificate
Cloudflare manages millions of certificates through its automated systems, making any vulnerability in their ACME implementation particularly dangerous due to the scale of their infrastructure.
Technical Deep Dive: How the ACME Validation Bug Worked
The specific ACME protocol vulnerability involved a race condition and improper state handling in Cloudflare's validation logic. When multiple certificate requests occurred simultaneously for related domains, the validation system could incorrectly associate successful validations with pending requests that hadn't been properly validated.
Simplified Pseudo-Code of the Vulnerable Logic
// VULNERABLE IMPLEMENTATION (Simplified)
function processValidation(requestId, domain, challengeToken) {
// Race condition could occur here between validation start and completion
validationCache[domain] = {status: 'pending', requestId: requestId};
// Challenge verification happens here
if (verifyChallenge(domain, challengeToken)) {
// BUG: The system incorrectly updates ALL pending requests for this domain
// rather than only the specific requestId that passed validation
updateAllPendingRequests(domain, 'validated'); // VULNERABLE LINE
}
}
The core issue was that the system used domain-based caching without proper request isolation. When a validation succeeded for one request, it could mark all pending validations for that domain as successful, regardless of whether those specific requests had completed their challenges.
Technical Components Involved
| Component | Role in Vulnerability | Impact |
|---|---|---|
| Validation Cache | Stored validation state by domain instead of by request ID | Allowed state bleed between requests |
| Race Condition Window | Multiple requests could be processed simultaneously | Created timing opportunity for exploitation |
| State Management | Inadequate isolation between validation sessions | Enabled cross-request contamination |
Real-World Attack Scenario: Exploiting the Flaw
Imagine an attacker targeting a financial institution's online portal. The attacker could have:
Step 1: Reconnaissance
The attacker identifies target domains and determines they use Cloudflare for certificate management.
Step 2: Simultaneous Request Flood
The attacker sends multiple certificate requests for variations of the target domain (subdomains, similar spellings) at nearly the same time.
Step 3: Strategic Validation
The attacker only completes the validation challenge for one legitimate domain they control, but due to the race condition, Cloudflare's system could mark ALL pending requests as validated.
Step 4: Certificate Issuance
Cloudflare issues valid certificates for domains the attacker doesn't own, enabling them to create convincing phishing sites or intercept traffic.
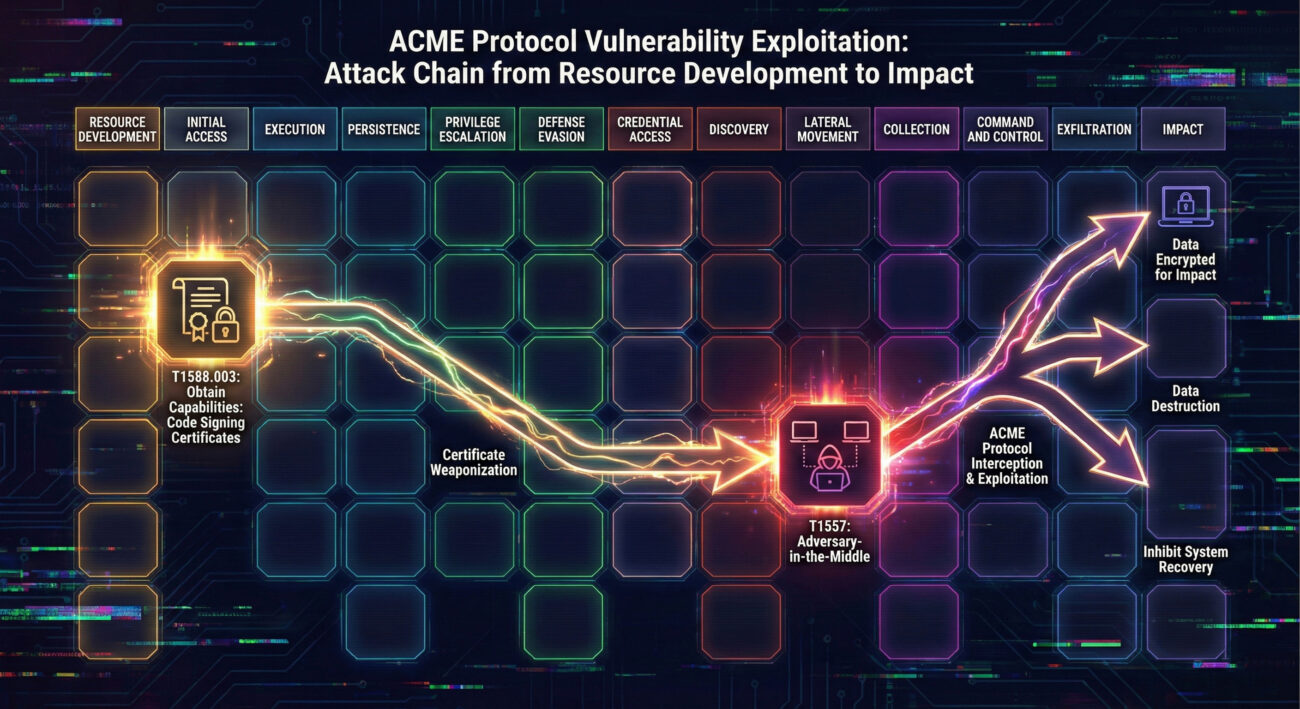
MITRE ATT&CK Framework Mapping
This ACME protocol vulnerability maps to several MITRE ATT&CK techniques, highlighting its sophistication and potential impact:
| Tactic | Technique | Description | Relevance |
|---|---|---|---|
| Initial Access | T1588.003: Obtain Digital Certificates | Adversaries obtain SSL/TLS certificates that can be used during targeting | Direct exploitation - obtaining fraudulent certificates |
| Resource Development | T1587.001: Domains | Adversaries acquire domains that can be used during targeting | Related to obtaining certificates for malicious domains |
| Credential Access | T1557: Man-in-the-Middle | Adversaries position themselves between two communicating parties | Fraudulent certificates enable MITM attacks |
| Impact | T1539: Steal Web Session Cookie | Adversaries steal web session cookies to gain access to web applications | Valid certificates make session hijacking more effective |
Step-by-Step: How an Attacker Could Exploit This Vulnerability
Step 1: Infrastructure Setup
The attacker sets up automated tools to interact with Cloudflare's ACME endpoint, preparing for rapid request submission.
Step 2: Target Identification
Research identifies high-value targets and their domain structures, noting which use Cloudflare's certificate services.
Step 3: Concurrent Request Engineering
Using multiple threads or processes, the attacker submits certificate requests for:
- Legitimate subdomains they control (for validation)
- Target domains they don't control (to benefit from the bug)
- Variations like www.target.com, login.target.com, secure.target.com
Step 4: Precision Timing Attack
The attacker times the validation response for their controlled domain to coincide with the processing window for all pending requests, exploiting the race condition.
Step 5: Certificate Harvesting
Successful exploitation yields valid certificates for unauthorized domains, which can be deployed for malicious purposes.
Common Mistakes & Best Practices in Certificate Validation
Common Implementation Mistakes
- Shared State Without Isolation: Using global or domain-level state without request context separation
- Inadequate Race Condition Protection: Failing to implement proper locking mechanisms for concurrent operations
- Overly Broad Cache Invalidation: Invalidating or updating cache entries too broadly rather than specifically
- Insufficient Request Tracing: Lacking detailed audit trails for validation attempts and outcomes
- Assumption of Linear Processing: Designing systems that assume requests will be processed sequentially rather than concurrently
Security Best Practices
- Request-Specific State Management: Isolate validation state per request using unique identifiers
- Implement Proper Locking: Use mutexes or distributed locks for critical validation sections
- Comprehensive Audit Logging: Log all validation attempts with timestamps, request IDs, and outcomes
- Regular Security Reviews: Conduct thorough code reviews specifically looking for race conditions and state management issues
- Implement Rate Limiting: Add request throttling to prevent flooding attacks
- Use Certificate Transparency Logs: Monitor CT logs for suspicious certificate issuance
- Adopt Zero-Trust Principles: Validate each request independently without relying on cached trust decisions
Red Team vs Blue Team Perspectives
Red Team: Attack Perspective
From an attacker's viewpoint, this vulnerability presented a golden opportunity:
- High Impact, Low Visibility: Obtaining legitimate certificates provides trusted access without triggering most security controls
- Perfect for Advanced Phishing: Certificates for legitimate-looking domains enable highly convincing phishing campaigns
- Ideal for Supply Chain Attacks: Compromise certificates for software update domains to distribute malware
- Excellent Persistence Mechanism: Valid certificates can enable long-term man-in-the-middle positions
- Testing Methodology: Red teams should now include ACME implementation testing in their infrastructure assessments
Blue Team: Defense Perspective
For defenders, this incident highlights critical monitoring gaps:
- Enhanced Certificate Monitoring: Implement continuous monitoring of Certificate Transparency logs for your domains
- Anomaly Detection: Create alerts for unusual certificate issuance patterns or unexpected certificate authorities
- DNSSEC Implementation: Use DNSSEC to protect DNS records from manipulation that could facilitate certificate fraud
- CAA Record Configuration: Properly configure Certificate Authority Authorization (CAA) DNS records to restrict which CAs can issue certificates for your domains
- Internal CA Consideration: For internal systems, consider using an internal CA rather than public certificates for critical infrastructure
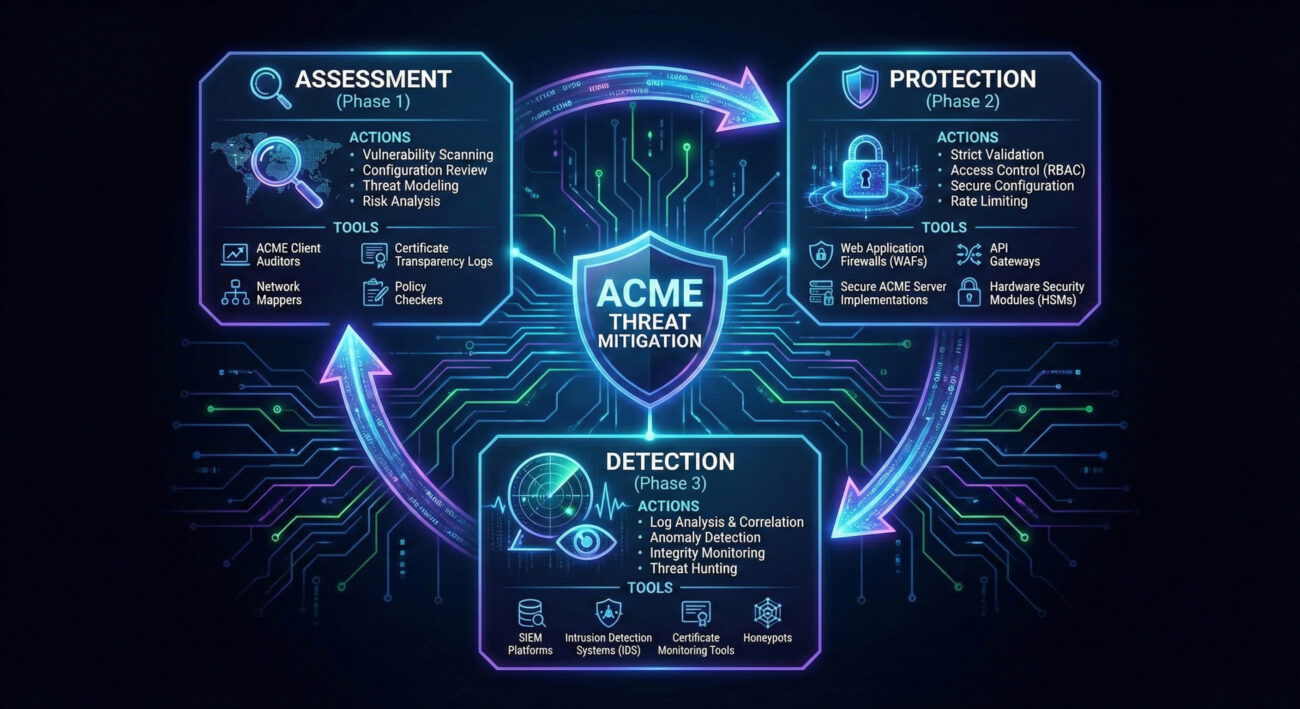
Implementation Framework: Protecting Your Organization
Phase 1: Assessment & Visibility
- Certificate Inventory: Document all SSL/TLS certificates across your organization
- ACME Dependency Mapping: Identify which systems use automated certificate management
- Vulnerability Assessment: Review certificate issuance processes for similar logic flaws
Phase 2: Protection & Prevention
- CAA Record Implementation: Configure DNS to restrict authorized certificate authorities
- Certificate Pinning: Implement HTTP Public Key Pinning (HPKP) for critical domains (with caution for maintainability)
- Monitoring Automation: Set up automated CT log monitoring using tools like Certificate Transparency Monitor
Phase 3: Detection & Response
- Anomaly Detection Rules: Create SIEM rules for unexpected certificate issuances
- Incident Response Playbook: Develop specific procedures for certificate compromise scenarios
- Revocation Procedures: Establish fast-track certificate revocation processes
Frequently Asked Questions
Cloudflare stated there was no evidence of active exploitation before the fix was deployed. However, the nature of such vulnerabilities means it's difficult to be certain, as sophisticated attackers might not leave detectable traces.
If Cloudflare has patched the vulnerability in their systems, certificates issued after the patch should be safe. However, organizations with extreme security requirements might consider reissuing certificates as a precautionary measure.
Use Certificate Transparency search tools like crt.sh or Google's Transparency Report to monitor certificate issuance for your domains.
The specific bug was in Cloudflare's implementation. However, all ACME implementations should be reviewed for similar logic flaws, as the protocol itself doesn't prevent such implementation errors.
The 2020 Let's Encrypt CAA bug involved incorrect validation of Certificate Authority Authorization records. This Cloudflare bug involved race conditions in validation state management. Both highlight different aspects of certificate validation that can fail.
Key Takeaways
1. Trust Requires Verification: Even trusted security providers can introduce critical vulnerabilities. Implement defense-in-depth rather than blind trust in any single vendor.
2. Automation Introduces New Risks: While ACME automates certificate management, it also creates new attack surfaces. Automated systems require rigorous security testing, especially for race conditions.
3. Certificate Transparency is Essential: CT logs provide crucial visibility into certificate issuance. Regular monitoring can detect unauthorized certificates early.
4. State Management is Critical: The vulnerability stemmed from improper state handling. Security-critical systems must implement robust, isolated state management with proper concurrency controls.
5. Comprehensive Security Reviews Matter: This bug survived standard testing but was caught through security reviews. Regular, thorough security assessments of critical infrastructure are non-negotiable.
Call to Action
Ready to Strengthen Your Certificate Security?
Don't wait for a certificate-related breach to impact your organization. Take proactive steps today:
Immediate Actions (Next 24 Hours):
- Check your domains on crt.sh for unexpected certificates
- Verify your CAA DNS records are properly configured
- Review which certificate authorities are authorized for your domains
Strategic Actions (Next 30 Days):
- Implement automated CT log monitoring
- Conduct a security review of your certificate management processes
- Develop incident response procedures for certificate compromise scenarios
For further reading on certificate security best practices, explore these resources:
Stay vigilant, stay informed, and remember: in cybersecurity, trust must be continuously earned and verified.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































