Complete Mid-Market Threat Lifecycle Protection: A Beginner’s Blueprint to Outsmart Attackers
- Executive Summary: The Mid-Market Security Balancing Act
- Real-World Scenario: When EDR Becomes a Burden
- Mapping the Threat Lifecycle to MITRE ATT&CK®
- Step-by-Step: Implementing Unified Threat Lifecycle Protection
- Common Mistakes & Best Practices
- Red Team vs. Blue Team View
- Implementation Framework for Mid-Market
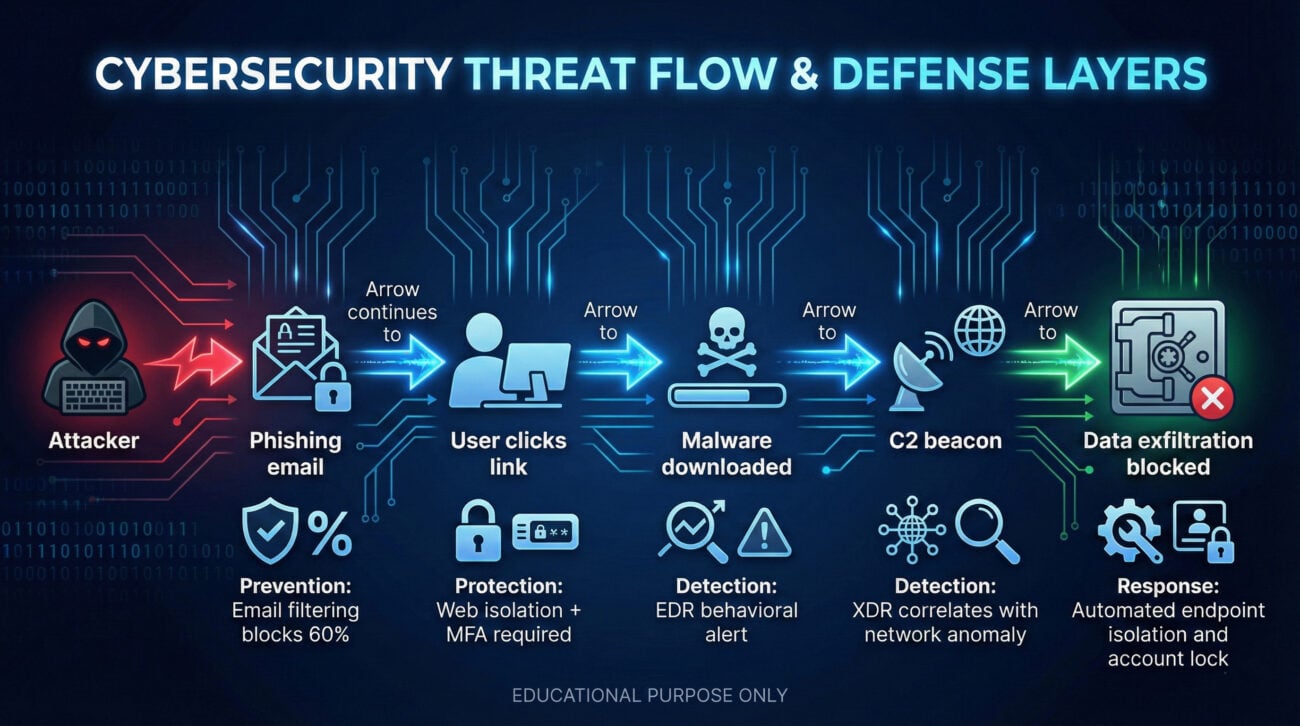
- Visual Breakdown: Threat Lifecycle in Action
- FAQ: Mid-Market Threat Lifecycle Protection
- Key Takeaways
- Call to Action
📌 Executive Summary: The Mid-Market Security Balancing Act
For mid-market organizations, cybersecurity is a constant tug-of-war. You need enterprise-grade defense, but you have lean teams and tighter budgets. The old model, buying point tools for prevention, detection, and response, often creates complexity that actually increases risk. This guide introduces mid-market threat lifecycle protection: an integrated approach that covers the entire attack chain, from initial reconnaissance to remediation. By understanding frameworks like MITRE ATT&CK and leveraging modern platforms (XDR, MDR), even small security teams can achieve robust defense without drowning in alerts. Let's transform security from a cost center into a business enabler.
Mid-market threat lifecycle protection isn't about buying more; it's about using smarter. We'll explore how to unify prevention, protection, detection, and response, exactly what the original article from The Hacker News highlighted, but with a fresh, beginner-focused lens.
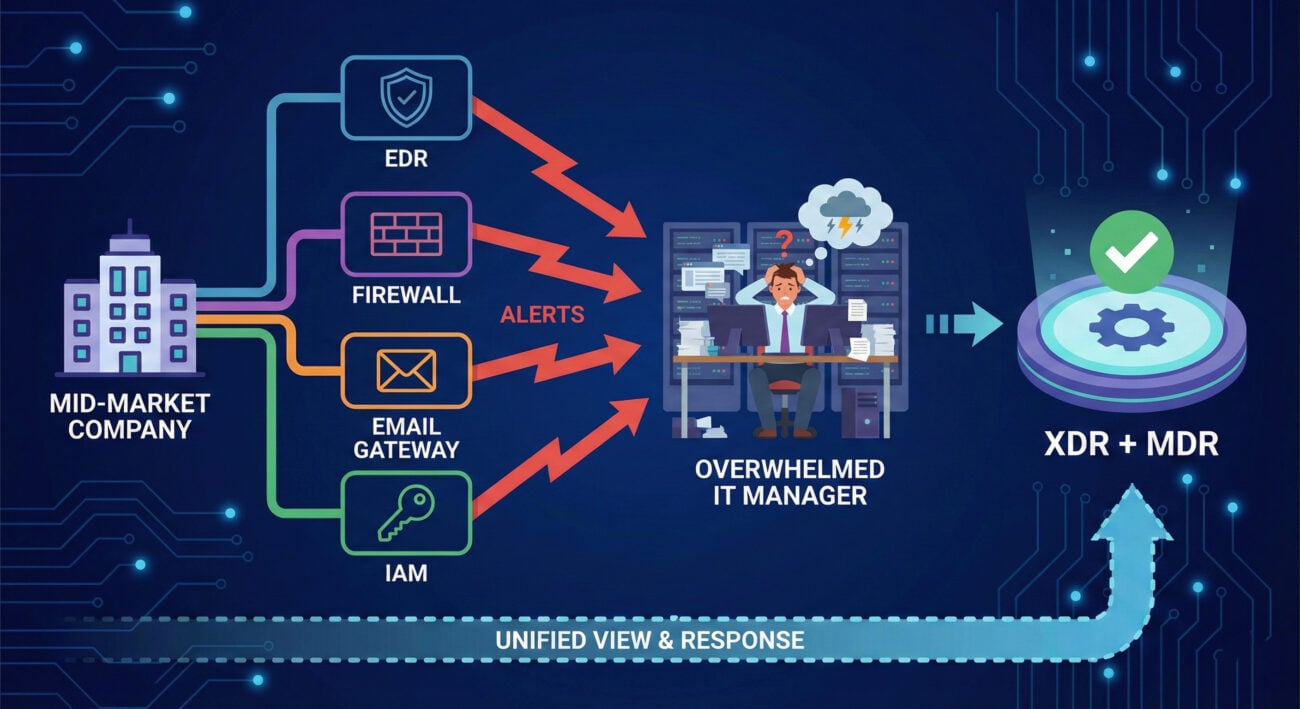
🏢 Real-World Scenario: When EDR Becomes a Burden
Meet NexGen Manufacturing, a 600-employee mid-market company. They have a lean IT team of four, plus one part-time security analyst. They invested in a top-tier EDR (Endpoint Detection and Response) solution because a breach at a competitor scared leadership. But six months later, they're overwhelmed.
- Alert fatigue: The EDR generates 200+ alerts daily. Most are false positives, but the team lacks time to tune them.
- Isolated tools: Firewall logs, email security, and EDR don't talk to each other. The team manually correlates data using spreadsheets.
- Reactive mode: They spend 80% of their time fighting fires, no time for proactive threat hunting or improvements.
This scenario is painfully common. The original article noted that EDR was designed for enterprises with dedicated SOC teams. Mid-market needs a different approach: mid-market threat lifecycle protection that consolidates capabilities and adds external support.
🔬 Mapping the Threat Lifecycle to MITRE ATT&CK®
To truly secure the complete threat lifecycle, you must understand the adversary's playbook. MITRE ATT&CK® is a knowledge base of real-world tactics and techniques. Let's map each phase of the threat lifecycle to specific ATT&CK stages and show how integrated protection disrupts them.
| Threat Lifecycle Phase | MITRE ATT&CK Tactics | Example Techniques | How Mid-Market Protection Helps |
|---|---|---|---|
| Prevention | Reconnaissance, Resource Development | Gather victim info (T1590), Develop capabilities (T1587) | External attack surface management, email filtering, MFA to block initial access |
| Protection | Initial Access, Execution | Phishing (T1566), Drive-by compromise (T1189) | Next-gen AV, application control, patch management – stops known malware |
| Detection | Persistence, Privilege Escalation, Defense Evasion | Registry run keys (T1547.001), Process injection (T1055) | XDR correlation across endpoints, network, identity; behavioral analytics |
| Response | Collection, Command and Control, Exfiltration | Data staged (T1074), C2 via web (T1071.001) | Automated isolation, incident response runbooks, MDR hunting |
By aligning your defenses with ATT&CK, you ensure no gap is left open. The table above is a starting point for building your mid-market threat lifecycle protection program.
📋 Step-by-Step: Implementing Unified Threat Lifecycle Protection
Moving from disjointed tools to a unified platform doesn't happen overnight. Follow these steps to evolve your security posture.
Step 1: Assess Your Current Coverage Gaps
Inventory all security tools and map them to the threat lifecycle phases. Where are you blind? For example, you might have endpoint detection but no cloud workload protection. Use MITRE ATT&CK to identify missing techniques.
Step 2: Choose a Consolidated Platform (XDR)
Select a vendor that provides integrated endpoint, network, email, and identity protection. Platforms like Bitdefender GravityZone (mentioned in the original article) unify prevention, detection, and response. Ensure it offers extended detection and response (XDR) to correlate signals.
Step 3: Augment with Managed Detection and Response (MDR)
Even with a great platform, your team may be too small for 24/7 monitoring. MDR services provide human analysts who hunt for threats and respond on your behalf. This closes the "specialist gap."
Step 4: Create Feedback Loops
Use insights from detection/response to improve prevention. If you see repeated phishing attempts, update your email filters and train employees. This creates a continuous improvement cycle.
⚠️ Common Mistakes & Best Practices
❌ Common Mistakes
- Relying solely on prevention – Attackers will eventually get in. Without detection/response, dwell time increases.
- Buying tools without integration – Five best-of-breed tools that don't share data create silos and alert storms.
- Ignoring insider threats – Not monitoring for compromised credentials or malicious insiders leaves a huge gap.
- Underfunding training – Your team is the last line of defense; if they can't use the tools, you're wasting money.
✅ Best Practices
- Adopt an XDR mindset – Correlate data across endpoints, networks, and clouds to catch multi-stage attacks.
- Outsource 24/7 monitoring (MDR) – Extend your team with experts; it's often cheaper than hiring internally.
- Use MITRE ATT&CK as a common language – It bridges communication between technical and non-technical stakeholders.
- Regularly test your defenses – Run tabletop exercises and purple team engagements to validate coverage.
⚔️ Red Team vs. Blue Team View
Understanding both perspectives helps you build resilient defenses. Here's how each side approaches the threat lifecycle.
🔴 Red Team (Adversary)
- Goal: Achieve objective (data theft, ransomware) with minimal detection.
- Tactics: Exploit unpatched vulnerabilities, use phishing, blend in with normal traffic.
- Loves: Tool silos, misconfigured alerts, and overworked defenders.
- Attack chain: Recon → Initial access → Persistence → Lateral movement → Exfiltration.
🔵 Blue Team (Defender)
- Goal: Reduce attack surface, detect early, respond fast.
- Strategy: Prevent what you can, detect what you can't, and have a response plan.
- Loves: Integrated telemetry, automated containment, threat intelligence.
- Defense lifecycle: Harden → Monitor → Hunt → Respond → Recover → Harden again.
Effective mid-market threat lifecycle protection makes the red team's job harder by removing silos and enabling blue team efficiency.
🏗️ Implementation Framework for Mid-Market
A phased approach prevents overwhelm. Use this framework to roll out complete lifecycle protection over 12–18 months.
| Phase | Timeline | Key Activities | Success Metric |
|---|---|---|---|
| Phase 1: Foundation | Months 1-3 | Asset inventory, enforce MFA, patch critical vulnerabilities, deploy EDR with basic configuration. | Reduction in unpatched critical CVEs by 80% |
| Phase 2: Consolidation | Months 4-9 | Replace point products with XDR platform, integrate email & network telemetry, enable automated responses for common alerts. | Alert volume down by 50% (due to correlation) |
| Phase 3: Augment & Optimize | Months 10-12 | Onboard MDR service, conduct purple team exercise, tune detection rules based on findings, implement threat hunting. | Mean time to respond (MTTR) < 1 hour |
❓ FAQ: Mid-Market Threat Lifecycle Protection
No, when properly implemented, XDR breaks down silos. It's about correlated detection across multiple security layers. For mid-market, it's a game-changer because it reduces the number of consoles and manual work.
MDR typically costs a fraction of a full-time employee (often $2,000–$5,000/month). A security analyst in the US costs $90k–$120k/year plus benefits. MDR gives you a whole team for less than one salary.
Think of ATT&CK as a map of attacker behavior. You don't need to memorize it; use it to check your coverage. For example, if you have no visibility into "privilege escalation," you know where to improve.
Yes, many modern platforms can ingest data from existing tools via APIs. The key is to have a central data lake and correlation engine (the XDR platform).
Start with free resources: implement MFA on all accounts, enable automatic updates, and use open-source tools like Wazuh for basic SIEM. Then build a business case for a consolidated platform.
🔑 Key Takeaways
- Mid-market threat lifecycle protection requires integrating prevention, protection, detection, and response, not just buying more tools.
- Use the MITRE ATT&CK framework to identify blind spots and speak a common language.
- Platforms with XDR capabilities reduce complexity by correlating data across endpoints, networks, and identities.
- MDR services are a cost-effective way to add 24/7 expertise and close the skills gap.
- Start with a phased approach: assess, consolidate, augment, and continuously improve.
🚀 Ready to Transform Your Security?
You don't have to figure it out alone. Begin your journey toward mid-market threat lifecycle protection today:
- 📘 Download our free Mid-Market Security Maturity Model (internal link placeholder).
- 🔍 Schedule a gap analysis workshop with our experts.
- 🛡️ Explore vendor solutions like Bitdefender GravityZone or Microsoft 365 Defender.
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































