CISA Flags Critical SolarWinds Web Help Desk RCE Bug Under Active Attack – KEV Alert
📋 Table of Contents
- Executive Summary
- Background: SolarWinds Web Help Desk & CISA KEV
- Technical Deep Dive: Deserialization RCE
- MITRE ATT&CK Mapping
- Real-World Attack Scenario
- Red Team vs. Blue Team View
- Step-by-Step Mitigation Guide
- Common Mistakes & Best Practices
- Other KEV Additions
- Frequently Asked Questions
- Key Takeaways
🚨 Executive Summary
On February 4, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a critical vulnerability affecting SolarWinds Web Help Desk to its Known Exploited Vulnerabilities (KEV) catalog. The flaw, identified as CVE-2025-40551, is an untrusted data deserialization issue that allows unauthenticated remote code execution (RCE). This means attackers can take full control of affected servers without a username or password. CISA confirmed the vulnerability is being actively exploited in the wild.
Federal agencies must patch by February 6, 2026. All organizations using SolarWinds Web Help Desk should treat this as a top priority. This post explains the vulnerability, maps it to MITRE ATT&CK, and provides clear steps to secure your environment.
🔍 Background: SolarWinds Web Help Desk & CISA KEV
SolarWinds Web Help Desk is a popular IT ticketing and asset management solution used by thousands of organizations. The newly added vulnerability (CVE-2025-40551) carries a CVSS score of 9.8 (Critical). It resides in the software's deserialization mechanism, where untrusted data is processed without proper validation. This allows an attacker to send a specially crafted object that, when deserialized, executes arbitrary code on the server.
Alongside this, SolarWinds released fixes for six other flaws in WHD version 2026.1, including four additional critical RCEs (CVE-2025-40552, CVE-2025-40553, CVE-2025-40554). CISA also added three unrelated vulnerabilities to the KEV catalog: two in Sangoma FreePBX and one in GitLab. All are actively exploited or have known exploitation history.
⚙️ Technical Deep Dive: Deserialization RCE
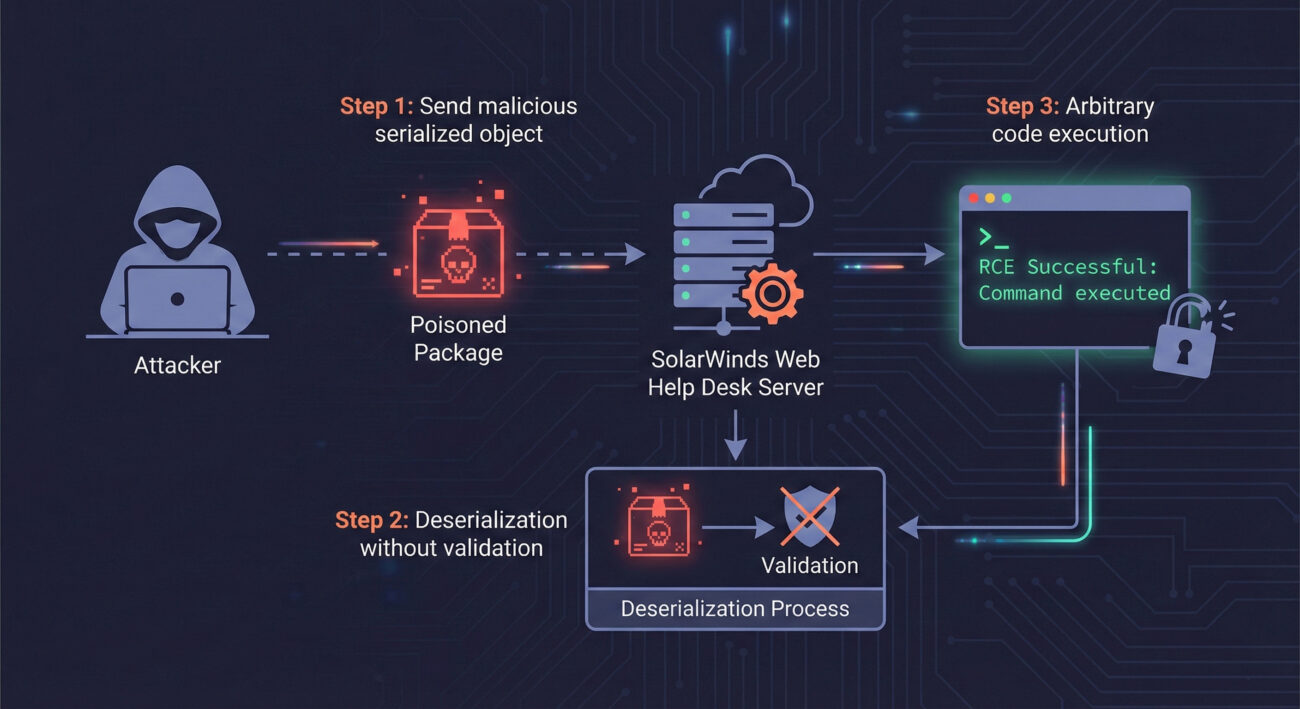
Deserialization is the process of converting a stream of bytes back into an object. When an application deserializes data from an untrusted source without proper safeguards, attackers can manipulate the object to alter application behavior. In the case of CVE-2025-40551, the SolarWinds Web Help Desk Java-based backend fails to validate serialized objects before reconstruction.
An attacker can send a malicious serialized object, perhaps via an HTTP request to a vulnerable endpoint, that, when deserialized, triggers execution of arbitrary commands. Because the flaw is pre-authentication, no login is required. Successful exploitation gives the attacker the same privileges as the Web Help Desk service account, often leading to full server compromise.
Vulnerability Details at a Glance
| CVE ID | CVSS | Type | Component |
|---|---|---|---|
| CVE-2025-40551 | 9.8 | Deserialization RCE | Web Help Desk Core |
| CVE-2025-40552 | 9.8 | Deserialization RCE | Web Help Desk Core |
| CVE-2025-40553 | 9.8 | Deserialization RCE | Web Help Desk Core |
| CVE-2025-40554 | 9.8 | Deserialization RCE | Web Help Desk Core |
| CVE-2025-40536 | 8.1 | Improper Access Control | Web Help Desk |
| CVE-2025-40537 | 7.5 | Information Disclosure | Web Help Desk |
🎯 MITRE ATT&CK Mapping
Understanding how this attack fits into the MITRE framework helps defenders build better detections. Below are the relevant tactics and techniques:
| Tactic | Technique ID | Technique Name | Context |
|---|---|---|---|
| Initial Access | T1190 | Exploit Public-Facing Application | Attacker exploits the Web Help Desk RCE via network |
| Execution | T1203 | Exploitation for Client Execution | Deserialization leads to code execution on server |
| Persistence | T1505 | Server Software Component | Attacker may install web shell or backdoor |
| Command and Control | T1059 | Command and Scripting Interpreter | Using system shell for post-exploitation |
Defenders should monitor for unusual deserialization activity, especially from unauthenticated sources, and unexpected process launches from the Web Help Desk service account.
🌐 Real-World Attack Scenario
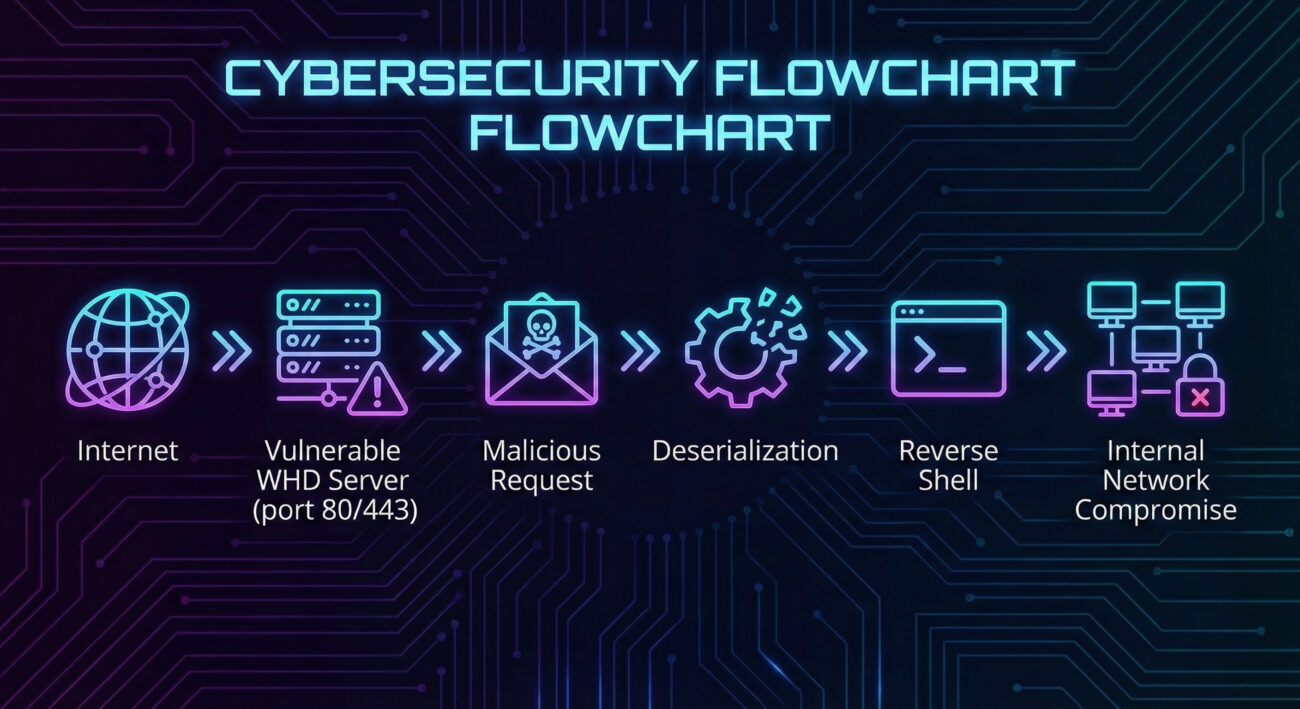
While specific attack campaigns exploiting CVE-2025-40551 are not yet public, we can construct a realistic scenario based on similar deserialization attacks (e.g., Log4Shell, WebLogic).
Scenario: Compromise of IT Service Desk
An attacker scans the internet for exposed SolarWinds Web Help Desk instances. They identify a server running a vulnerable version. Using a publicly available exploit or custom payload, they send a malicious serialized Java object to a specific endpoint (e.g., /helpdesk/Upload). The server deserializes the object, executing the attacker's code, which opens a reverse shell. The attacker now has a foothold inside the network, potentially moving laterally to more sensitive systems.
🛡️ Red Team vs. Blue Team View
🔴 Red Team (Attacker)
- Scan for WHD instances using Shodan/Censys.
- Use Metasploit or custom Java deserialization tools to deliver payload.
- Bypass basic WAF rules with encoded/obfuscated serialized objects.
- After RCE, dump credentials, install persistence (e.g., web shell).
- Move laterally using stolen tickets or service accounts.
🔵 Blue Team (Defender)
- Patch immediately to version 2026.1 or later.
- Monitor for anomalous deserialization exceptions in logs.
- Deploy RASP (Runtime Application Self-Protection) to detect object injection.
- Restrict outbound connections from WHD servers.
- Harden network segmentation: place WHD behind VPN/zero-trust.
🛠️ Step-by-Step Mitigation Guide
Step 1: Identify Affected Versions
Check your SolarWinds Web Help Desk version. Versions prior to 2026.1 are vulnerable. Log in to the admin console and look under "About" or use the command line.
Step 2: Download the Patch
Visit the SolarWinds Security Advisory page and download the latest version (2026.1). Ensure you get the correct build for your environment.
Step 3: Backup & Apply Update
Before applying, back up your database and configuration files. Run the installer as administrator and follow the prompts. The update will restart services.
Step 4: Verify Patching
After installation, confirm the version number. Also, test core functionality to ensure no regression. Check for any indicators of compromise (unexpected files, new accounts).
Step 5: Monitor for Exploitation Attempts
Even after patching, monitor logs for deserialization-related errors or unusual outbound connections. Use a SIEM to alert on suspicious patterns.
❌ Common Mistakes & ✅ Best Practices
Common Mistakes (Avoid These)
- Assuming the vulnerability doesn't affect you because your server is internal.
- Delaying patching due to change management processes.
- Relying solely on a WAF to block deserialization attacks (they can be bypassed).
- Not checking for signs of prior compromise before patching.
Best Practices (Implement These)
- Patch within 48 hours for critical KEV-listed flaws.
- Use application allowlisting to prevent unauthorized code execution.
- Segment IT service management tools from critical assets.
- Enable detailed logging and send logs to a SIEM.
- Conduct regular vulnerability scans and prioritize KEV entries.
📌 Other KEV Additions You Should Know
CISA also added three other vulnerabilities to the KEV catalog alongside the SolarWinds issue. Federal agencies must patch these by February 24, 2026.
| CVE | Product | Type | Notes |
|---|---|---|---|
| CVE-2019-19006 | Sangoma FreePBX | Improper Authentication | Exploited since 2020 in INJ3CTOR3 campaign |
| CVE-2025-64328 | Sangoma FreePBX | OS Command Injection | Leads to web shell (EncystPHP) deployment |
| CVE-2021-39935 | GitLab CE/EE | SSRF | Actively exploited in 2025, allows internal scans |
For a complete list, visit the CISA KEV Catalog.
❓ Frequently Asked Questions
Q: What is the CISA KEV catalog?
A: It's a list of vulnerabilities that have been confirmed as actively exploited in the wild. Federal agencies must patch these by a deadline, and private sector is strongly urged to do so.
Q: Do I need to worry if I use SolarWinds Web Help Desk cloud version?
A: SolarWinds typically manages patching for cloud offerings. Verify with your provider that they have applied the update. If self-hosted, you must patch.
Q: Can a WAF stop this attack?
A: A WAF might detect some exploit attempts, but deserialization attacks can be obfuscated. Patching is the only reliable mitigation.
Q: How do I check if I've been compromised?
A: Look for unexpected processes, outbound connections from the WHD server, new files in web directories, and unauthorized administrator accounts. Use an EDR tool for deeper investigation.
Q: What's the deadline for federal agencies?
A: For CVE-2025-40551, the deadline is February 6, 2026. For the other three, February 24, 2026.
🔑 Key Takeaways
- CISA added a critical SolarWinds Web Help Desk RCE vulnerability (CVE-2025-40551) to the KEV catalog due to active exploitation.
- The flaw is an unauthenticated deserialization issue allowing full server compromise.
- Update to WHD version 2026.1 immediately; federal agencies must comply by Feb 6, 2026.
- Three other vulnerabilities in FreePBX and GitLab were also added.
- Defenders should monitor for deserialization attempts and apply patches as the primary fix.
🚀 Stay Ahead of Threats
Subscribe to our newsletter for the latest cybersecurity insights and KEV updates. Share this post with your team to ensure everyone understands the urgency.
📧 Join our mailing list | 🔗 Related: Understanding Deserialization Attacks | Internal: KEV Catalog Guide
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































