Clearance Levels
The Powerful Threat Every Beginner Must Stop Explained Simply
📋 Table of Contents
- Introduction: The Digital Security Hierarchy
- Why Clearance Levels Matter in Cybersecurity Today
- Key Terms & Concepts Explained
- Real-World Scenario: From Entry to Top Secret
- How to Navigate Security Clearance Requirements
- Common Mistakes & Best Practices
- Threat Hunter's Eye: The Adversarial Perspective
- Red Team vs Blue Team View of Clearance Systems
- Conclusion & Key Takeaways
Introduction: The Digital Security Hierarchy
Have you ever wondered how governments protect their most sensitive information from cyber attacks and espionage? Or why some IT professionals can access certain systems while others cannot? The answer lies in one of cybersecurity's most fundamental concepts: clearance levels.
Clearance levels are a hierarchical system of security classifications that determine who can access what information. Think of it like a corporate building: the lobby is open to everyone (public information), certain offices require employee badges (confidential), and the executive suite needs special authorization (top secret). In cybersecurity, these "digital badges" protect everything from military secrets to personal citizen data.
Analogy Time: Imagine your social media privacy settings as a simple clearance system. "Public" posts are like unclassified information. "Friends only" represents confidential level. "Custom lists" with specific people resemble secret clearance. And "Only me" is your personal top-secret compartment!
In this comprehensive guide, you'll learn: the 5 main government clearance levels, how investigations work, why this system is crucial for national security, and how understanding clearance can advance your cybersecurity career.
Why Clearance Levels Matter in Cybersecurity Today
In our interconnected digital world, clearance levels serve as the foundation of trust in government and corporate security systems. According to the Office of the Director of National Intelligence, over 4 million Americans hold security clearances, protecting trillions of dollars worth of intellectual property and state secrets.
The importance of proper clearance level management became painfully clear during incidents like the 2020 SolarWinds breach, where hackers potentially accessed systems containing sensitive government data. Proper clearance protocols act as digital gatekeepers, ensuring that only vetted individuals can access specific information tiers.
For cybersecurity professionals, understanding clearance isn't just about government jobs. Major corporations like Microsoft, Amazon AWS, and Google Cloud have adopted similar tiered access models for their cloud services and internal data. The National Institute of Standards and Technology (NIST) framework explicitly recommends implementing "least privilege access" principles, the core philosophy behind clearance systems.
Every day, clearance levels prevent thousands of potential security breaches by creating structured barriers between different sensitivity levels of information. They're not just bureaucratic red tape, they're essential digital defenses.
Key Terms & Concepts Explained
Before diving deeper, let's clarify essential terminology. This table breaks down the core concepts in simple language.
| Term | Simple Definition | Everyday Analogy |
|---|---|---|
| Security Clearance | Official permission to access classified information after background investigation | Like getting a driver's license, proves you're qualified and vetted to operate vehicles (access data) |
| Need-to-Know | Principle that clearance alone isn't enough; you must also require the information for your job | Having a master key to a building (clearance) but only opening doors relevant to your work duties |
| Background Investigation | Comprehensive check of your personal, professional, and financial history | Extreme version of a landlord checking your rental history, credit, and references |
| Least Privilege | Security principle granting only minimum access necessary to perform job functions | Hotel staff: housekeepers access rooms but not financial systems; managers access both but not other hotels |
| Compartmentalization | Isolating sensitive information into separate "compartments" with unique access requirements | Bank vault with separate boxes, having access to the vault doesn't grant access to individual boxes |
Real-World Scenario: From Entry to Top Secret
Meet Alex Chen, a recent cybersecurity graduate hired as an IT specialist at a defense contractor. Alex's journey through the clearance process illustrates how these systems work in practice.
Alex starts with a Public Trust position, handling non-sensitive systems. After six months of excellent performance, their company sponsors them for Secret clearance to work on a new government contract. The process begins with SF-86 paperwork, a 127-page form detailing Alex's entire life history for the past 10 years.

The investigation takes 8 months. Investigators interview Alex's neighbors, former colleagues, and even travel to verify foreign contacts (Alex studied abroad in college). Finally, clearance is granted with a caveat: Alex can access Secret materials but only those related to specific projects (need-to-know).
Two years later, Alex is promoted to a cyber defense team requiring Top Secret/Sensitive Compartmented Information (TS/SCI) clearance. This triggers a more intensive investigation including polygraph examination. The timeline below shows Alex's clearance journey:
| Time/Stage | What Happened | Impact on Security |
|---|---|---|
| Month 0-6 | Public Trust position, basic access controls | Protected non-sensitive systems only |
| Month 7-14 | Secret clearance application and investigation | Secured access to military project data |
| Month 15-30 | Secret clearance active, regular monitoring | Prevented potential insider threats through continuous evaluation |
| Month 31-40 | TS/SCI application, enhanced investigation | Encrypted access to intelligence community systems |
| Ongoing | Periodic reinvestigations every 5 years | Maintains verified trust despite life changes |
How to Navigate Security Clearance Requirements
Whether you're pursuing a government cybersecurity career or just want to understand these systems, here's your step-by-step guide to security clearances.
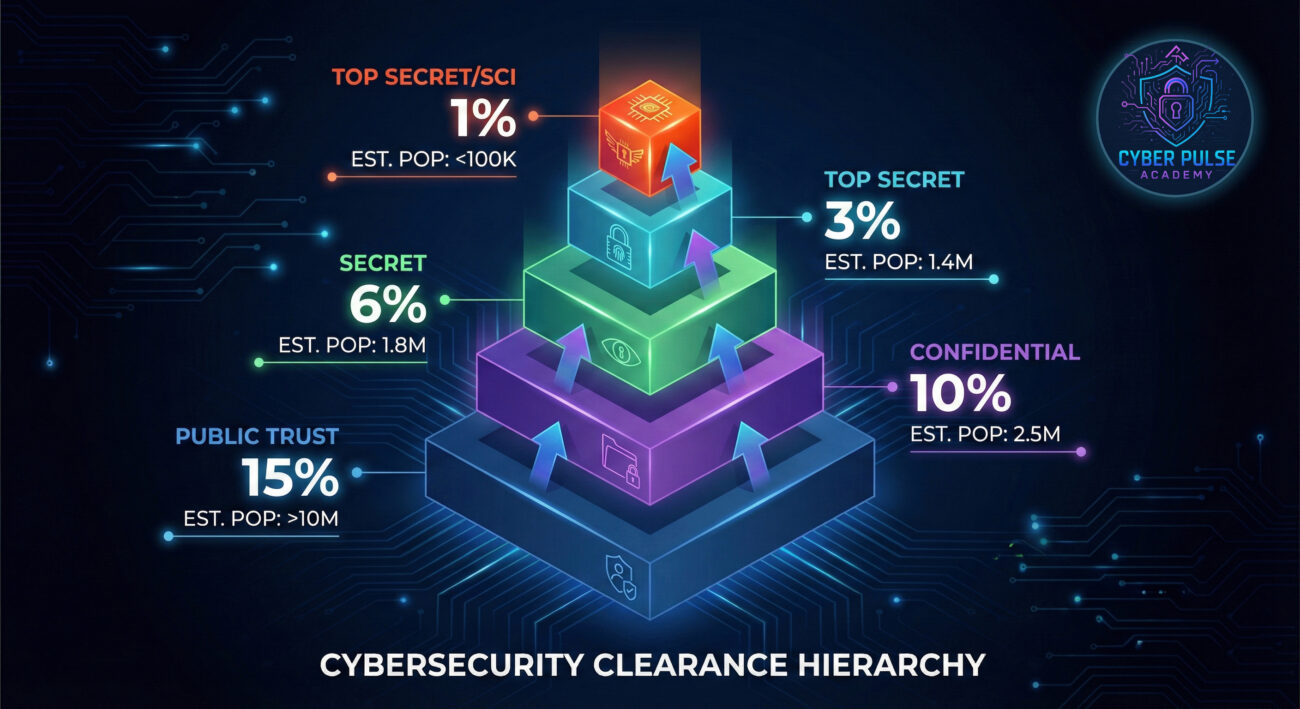
Step 1: Understand the Clearance Pyramid
Recognize that clearances build upon each other like a pyramid:
- Base: Public Trust/Position of Trust (minimal investigation)
- Tier 1: Confidential (damage to national security if disclosed)
- Tier 2: Secret (serious damage to national security)
- Tier 3: Top Secret (exceptionally grave damage)
- Peak: TS/SCI with polygraph (compartmentalized intelligence)
Most cybersecurity professionals start at Secret level for defense contracting roles.
Step 2: Get Sponsored for Clearance
You cannot apply for clearance yourself, you need employer sponsorship:
- Seek positions with "clearance eligible" or "must obtain clearance" requirements
- Consider interim clearances for immediate start while full investigation continues
- Government contractors often sponsor clearances for qualified candidates
Check our guide on cybersecurity career paths for sponsorship opportunities.
Step 3: Complete the SF-86 Form Thoroughly
This extensive form is your first major hurdle:
- Be meticulously honest, omissions are worse than minor issues
- Document all foreign contacts, travels, and financial issues
- Gather addresses, employment history, and references from past 10 years
Even small discrepancies can delay your investigation for months.
Step 4: Prepare for the Background Investigation
Investigators will verify everything on your SF-86:
- Notify references that they may be contacted
- Prepare for interviews about your character and reliability
- For higher clearances: prepare for financial reviews and polygraphs
The Defense Counterintelligence and Security Agency (DCSA) conducts most investigations.
Step 5: Maintain Your Clearance Actively
Clearance isn't permanent, it requires ongoing maintenance:
- Report foreign travel, significant financial changes, or legal issues immediately
- Complete annual security training without fail
- Prepare for periodic reinvestigation every 5-10 years
Learn about security awareness best practices to maintain compliance.

Common Mistakes & Best Practices
❌ Mistakes to Avoid
- Omitting information on SF-86 forms, thinking "they won't find out"
- Failing to report foreign contacts or travels after clearance is granted
- Discussing classified information in unsecured environments (even vaguely)
- Ignoring financial troubles that create vulnerability to exploitation
- Assuming clearance is permanent without continuous compliance
✅ Best Practices
- Practice absolute honesty throughout the process, integrity is paramount
- Implement strong password and MFA for all systems (learn more in our MFA guide)
- Regularly update your security reporting as life circumstances change
- Maintain encrypted storage for any work-related materials
- Develop a "need-to-know" mindset, don't access information unnecessarily
Threat Hunter's Eye: The Adversarial Perspective
From an attacker's viewpoint, clearance levels represent both barriers and potential targets. Here's how adversaries think about these systems:
Attack Path: A sophisticated threat actor doesn't always attack the most secure system directly. Instead, they might target someone with lower clearance who has access paths to higher systems, like compromising a secretary with Secret clearance who handles scheduling for Top Secret meetings. Through phishing or social engineering, they gain foothold in the network, then move laterally, exploiting trust relationships between systems of different classification levels.
Defender's Counter-Move: Security teams implement air-gapping (physical separation) between classification levels and strict data loss prevention (DLP) controls. They monitor for "hopping" attempts between security zones and enforce multi-factor authentication that changes between compartments. The key mindset: assume clearance boundaries will be tested daily, and monitor not just for breaches, but for suspicious access patterns across classification lines.
Red Team vs Blue Team View of Clearance Systems
From the Attacker's Eyes
"Clearance levels are organizational patterns that reveal what information is valuable. The higher the clearance required, the more sensitive the data. We look for weak links in the chain, personnel with high clearance but poor security habits, or systems where classification boundaries aren't strictly enforced. Our goal is to find paths from lower classification zones to higher ones, often through legitimate accounts that have been compromised. The clearance hierarchy itself becomes a map telling us where to focus our efforts."
From the Defender's Eyes
"Clearance levels implement the principle of least privilege at scale. Our job is to ensure these digital boundaries are secure, monitored, and respected. We care about proper implementation: ensuring someone with Secret clearance can't accidentally (or intentionally) access Top Secret materials. We implement encryption, logging, and behavioral analytics to detect when clearance boundaries are tested. For us, the system isn't just about keeping secrets, it's about maintaining trust through verifiable access controls."
Conclusion & Key Takeaways
Understanding clearance levels is fundamental to cybersecurity, whether you work in government, defense contracting, or corporate security. These hierarchical systems represent one of the most sophisticated approaches to information protection ever developed.
Key Takeaways:
- Clearance levels (Public, Confidential, Secret, Top Secret, TS/SCI) create structured access to sensitive information
- The system combines thorough vetting (background investigations) with ongoing monitoring and need-to-know principles
- For cybersecurity careers, clearance can be a valuable asset, opening doors to specialized roles in defense and intelligence
- Both attackers and defenders study clearance systems, one to bypass them, the other to strengthen these digital boundaries
As digital threats evolve, so do clearance level systems. Continuous vetting, behavioral analytics, and advanced authentication methods are making these systems more dynamic and responsive. Whether you're pursuing clearance or just securing your own organization's data, the principles behind these systems, least privilege, need-to-know, and verified trust, are universally applicable in cybersecurity.
💬 Call to Action
Have questions about security clearances or cybersecurity career paths? Share your thoughts in the comments below! For more beginner-friendly cybersecurity guides, explore our Beginner's Resource Library or download our free Cybersecurity Career Checklist.
Remember: In cybersecurity, understanding how to protect information is just as important as understanding the information itself. Stay curious, stay secure!


















































