Critical Privilege Boundary Bypass in Cisco ISE
Patch This Vulnerability Now Explained Simply
A recent disclosure by Cisco has spotlighted a critical concept in enterprise security: the privilege boundary. Tracked as CVE-2026-20029, this vulnerability in Cisco's Identity Services Engine (ISE) isn't just another bug; it's a textbook case of a privilege boundary bypass. This flaw allowed an authenticated administrator, a supposedly trusted user, to step beyond their intended permissions and read sensitive files on the underlying operating system. In this deep dive, we'll unpack how this XML parsing vulnerability works, map it to the MITRE ATT&CK framework, and provide a clear, actionable guide for both Red and Blue Teams. Understanding this privilege boundary bypass is essential for anyone responsible for securing network access control systems.
Table of Contents
- Executive Summary: The Core of the Vulnerability
- Vulnerability Deep Dive: How the Bypass Works
- A Real-World Attack Scenario
- Mapping to MITRE ATT&CK
- Red Team vs. Blue Team Perspective
- Step-by-Step Patching and Mitigation Guide
- Common Mistakes & Best Practices
- Proactive Defense Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways and Action Items
Executive Summary: The Core of the Privilege Boundary Bypass
Cisco ISE is a cornerstone of network security, acting as a policy enforcement point for network access control. It decides who and what can connect to a corporate network. The vulnerability, CVE-2026-20029 (CVSS 4.9), resides in the licensing feature of ISE and its Passive Identity Connector (ISE-PIC).
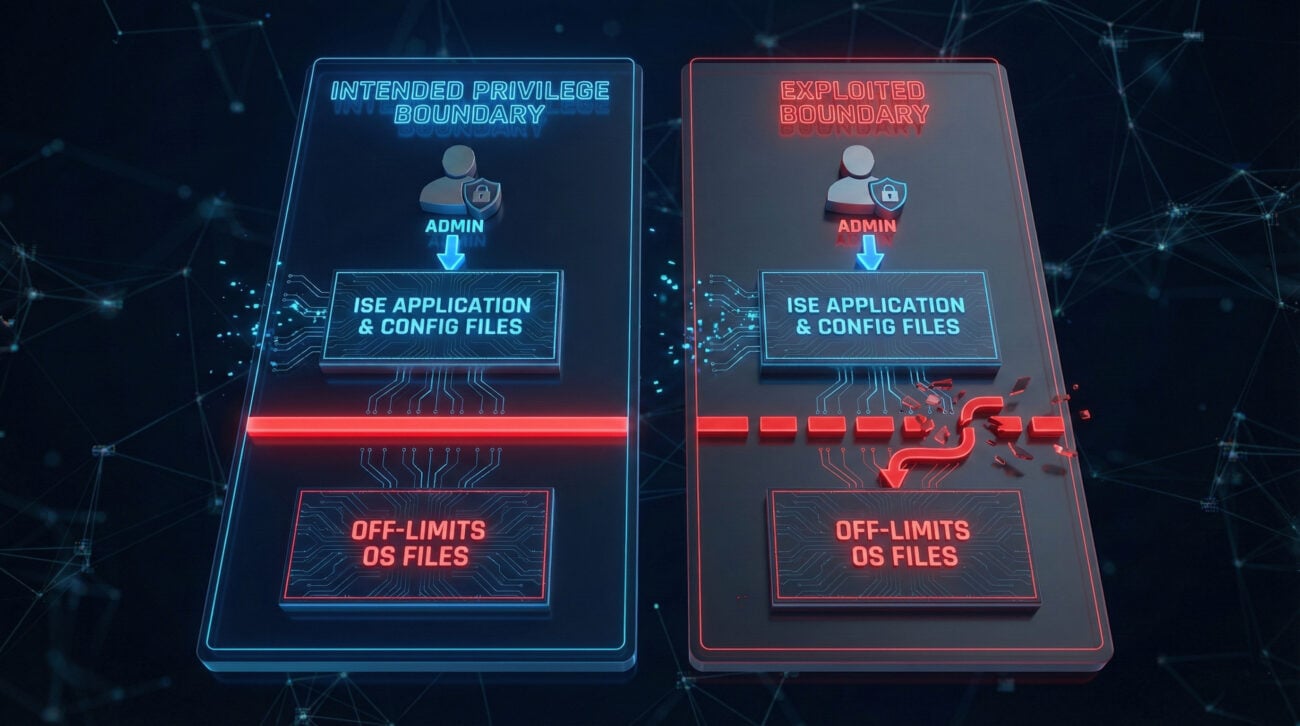
The flaw is an improper XML parsing issue within the web-based management interface. In simple terms, the system fails to properly validate and sanitize XML files uploaded via the admin panel. While exploitation requires valid administrative credentials, the critical failure is a broken privilege boundary. Even an administrator's access should be confined to the ISE application's data and configuration. This vulnerability allows them to break out of that "application sandbox" and perform arbitrary file reads on the host OS.
Think of it like this: A building manager has a master key (admin creds) for all apartment doors (ISE functions). However, due to a flaw in the security system (XML bug), using that key on a specific lock (upload feature) also secretly unlocks the secure basement (OS files) that should never be accessible with that key. Cisco has released patches, and a public Proof-of-Concept (PoC) exploit exists, making prompt patching non-negotiable.
Vulnerability Deep Dive: How the Privilege Boundary Bypass Works
To defend against a threat, you must first understand its mechanics. Let's break down the technical sequence of this attack.
The Faulty XML Parsing Engine
The licensing feature in Cisco ISE's web interface accepts uploads, likely for license files or related data. These files are processed by an XML parser. A properly secure parser would:
- Validate the structure of the XML.
- Sanitize or block any references to external resources or file paths.
- Confine the read/write operations to a predefined, safe directory.
The vulnerable parser fails to properly handle certain XML constructs, likely XML External Entities (XXE) or path traversal sequences embedded within tags or attributes. When a malicious actor uploads a specially crafted XML file, the parser is tricked into interpreting part of the file's content as a directive to read a file from the local filesystem.
Technical Breakdown of the Exploit
An attacker with admin access would follow this technical path:
Step 1: Crafting the Malicious Payload
The attacker creates an XML file that appears to be a legitimate license or data file for upload. Inside this file, they embed a path traversal payload. For example, instead of pointing to a license value, a parameter might be crafted to reference a sensitive system file.
<?xml version="1.0" encoding="UTF-8"?>
<licenseData>
<feature name="Premium_Support">true</feature>
<!-- Malicious payload attempting to read the /etc/passwd file -->
<signature path="../../../etc/passwd">SpoofedSignatureValue</signature>
</licenseData>
Step 2: Bypassing the Application Context
The attacker logs into the ISE admin web interface and navigates to the license or file upload section. They upload the crafted XML file. The vulnerable parser reads the `path` attribute but does not confine the file access to the intended upload directory. The `../../../` sequence successfully traverses out of the application's web root.
Step 3: Accessing Off-Limits Data
The parser, following the malicious path, reads the contents of the target file (e.g., `/etc/passwd`, `/etc/shadow`, configuration files with database passwords, or SSH keys). This content is then typically reflected back in the web interface's response, perhaps in an error message, a confirmation dialog, or a parsed output field, allowing the attacker to view it.
The impact is severe: credentials, system configurations, and other secrets stored on the OS become exfiltrated. This data can be used for lateral movement, persistence, or further exploitation.
A Real-World Attack Scenario: From Breach to Dominion
Let's contextualize this vulnerability in a plausible attack chain against a large enterprise.
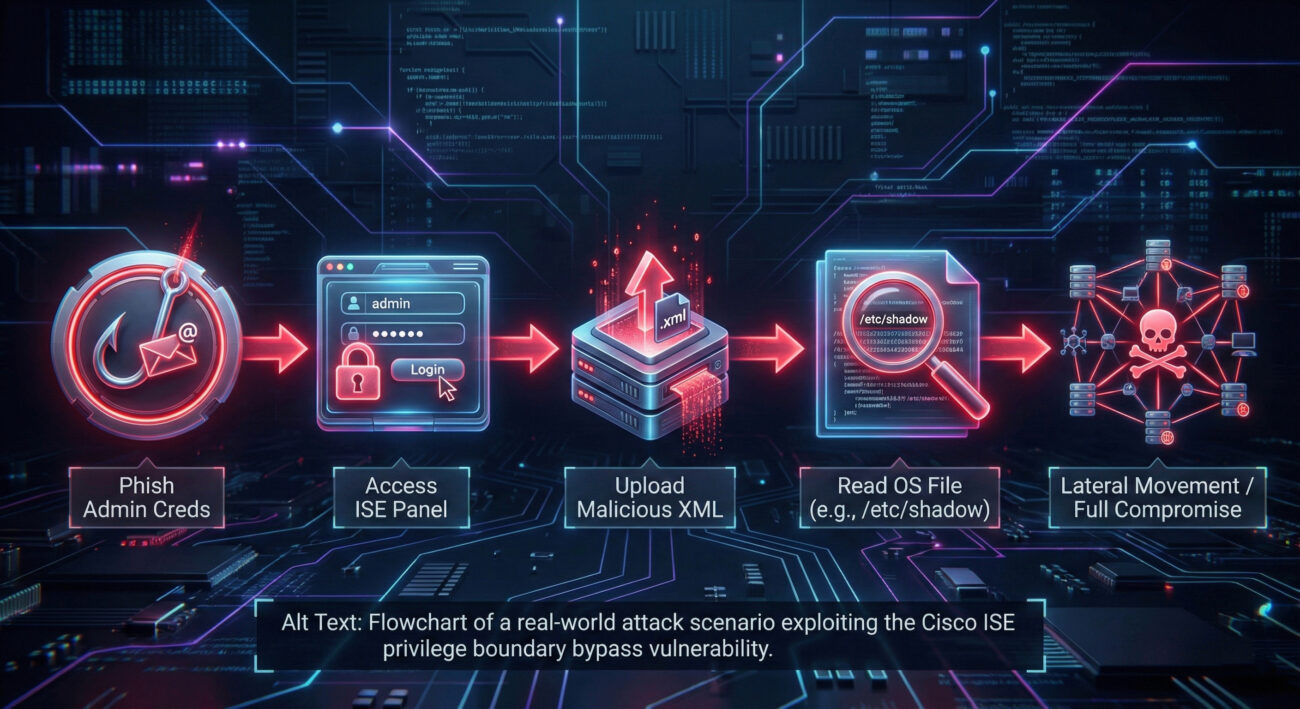
Act 1: Initial Foothold. An attacker phishes a network engineer, stealing their credentials for the internal IT portal. These credentials are tried against various systems, including the Cisco ISE admin panel, and gain access.
Act 2: Discovery and Exploitation. Inside the ISE panel, the attacker explores functionalities. Knowing about CVE-2026-20029 (from the public PoC), they craft and upload a malicious XML file via the licensing page, requesting the contents of `/root/.ssh/id_rsa` (the private SSH key of the root user).
Act 3: Privilege Escalation and Persistence. The ISE server returns the private key data. The attacker now has SSH access to the underlying Linux host with root privileges. From this powerful position, they can deploy backdoors, pivot to other network segments, or disrupt network access policies managed by ISE itself, causing widespread network outage or creating hidden access for other malicious actors.
Mapping the Attack: MITRE ATT&CK Framework
Framing this vulnerability within MITRE ATT&CK helps defenders understand its role in a broader attack campaign and identify detection opportunities.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How CVE-2026-20029 is Utilized | Detection & Mitigation Focus |
|---|---|---|---|
| Privilege Escalation | T1078.004: Valid Accounts: Cloud Accounts | While it uses a valid admin account, the flaw escalates privileges from application admin to OS-level access, breaking the intended boundary. | Monitor for anomalous file read activities by the ISE application process (e.g., reading /etc/shadow). |
| Defense Evasion | T1222: File and Directory Permissions Modification | By abusing a legitimate function (file upload), the attacker evades defenses that might only monitor for obvious malicious binaries or scripts. | Application allowlisting and monitoring for unexpected child processes spawned by the ISE service. |
| Credential Access | T1003.008: OS Credential Dumping: /etc/passwd and /etc/shadow | The direct outcome of the arbitrary file read is often the dumping of OS credentials from these critical files. | File integrity monitoring (FIM) on /etc/passwd and /etc/shadow for read attempts from non-system processes. |
| Discovery | T1083: File and Directory Discovery | The attacker can use the vulnerability to discover sensitive files and map the filesystem of the ISE server. | Correlate multiple "file not found" errors from the ISE app followed by a successful read of a sensitive file. |
Red Team vs. Blue Team Perspective
This vulnerability presents unique challenges and opportunities for both attackers and defenders.
The Red Team (Attack) View
Why It's Appealing:
- Stealth: Uses a legitimate admin portal and a normal-looking function (file upload), creating minimal network noise.
- High Reward: Direct path to root/system-level secrets from a mid-level privileged account.
- Pivoting Potential: Compromising the ISE server, a central network control node, offers unparalleled access to reconfigure network policies for further attacks.
Exploitation Strategy: A Red Team would first need to obtain admin credentials (via phishing, password spraying, or finding them in exposed configs). Post-exploitation, they would use the PoC to exfiltrate SSH keys or password hashes, then use that data to move laterally, ensuring persistence even if the ISE vulnerability is later patched.
The Blue Team (Defense) View
Primary Challenges:
- Detection Difficulty: The activity originates from a legitimate admin IP and user account, performing an allowed action.
- Blind Spots: Many monitoring tools focus on the network perimeter or endpoints, not on file read activities of a specific application server.
- Urgency: With a public PoC, the window to patch before widespread exploitation attempts is extremely short.
Defense Strategy: Immediate priority is patching. Second, hunt for indicators: look for logs of XML file uploads to the ISE licensing service around the time of anomalous admin logins. Implement Multi-Factor Authentication (MFA) on all admin accounts to negate the stolen credential vector. Deploy Host-Based Intrusion Detection Systems (HIDS) on the ISE server to alert on processes reading sensitive OS files.
Step-by-Step Patching and Mitigation Guide
Cisco has released patches for affected versions. There are no workarounds; patching is the only complete solution.
| Your Cisco ISE/ISE-PIC Release | Action Required | Patch / Fixed Release | Critical Notes |
|---|---|---|---|
| Earlier than 3.2 | Migrate to a fixed, supported release. | 3.2 Patch 8 or later (e.g., 3.3, 3.4) | Older releases cannot be patched. A major version upgrade is mandatory and requires careful planning. |
| Release 3.2 | Apply the specific patch. | 3.2 Patch 8 | Ensure you are on the base 3.2 release before applying this patch. |
| Release 3.3 | Apply the specific patch. | 3.3 Patch 8 | |
| Release 3.4 | Apply the specific patch. | 3.4 Patch 4 | |
| Release 3.5 | No action needed. | Not vulnerable. | Ensure you are on the latest patch for other security issues. |
Patching Procedure Checklist
Step 1: Pre-Patch Preparation
1. Identify Version: Log into each ISE node and run `show version` in the CLI.
2. Backup: Take a full configuration and database backup using the ISE admin GUI.
3. Review Dependencies: Check Cisco's release notes for the target patch for any other requirements or known issues.
4. Schedule Maintenance: Plan for an outage window, as patches often require a reboot.
Step 2: Download and Apply
1. Download: Obtain the correct patch file from the Cisco Software Download Center.
2. Transfer: Upload the patch file to the ISE primary Administration Node via GUI (System > Maintenance > Patch Management) or SCP.
3. Install: In the Patch Management screen, select the uploaded file and click "Install." The process will replicate to secondary nodes in a multi-node deployment.
4. Reboot: Allow the system to reboot as prompted.
Step 3: Post-Patch Validation
1. Verify Version: Confirm the new patch version is active (`show version`).
2. Functional Test: Test core ISE functions: admin login, policy execution, endpoint authentications.
3. Monitor Logs: Closely review application and system logs for any errors following the patch.
Common Mistakes & Best Practices
🚫 Common Mistakes That Increase Risk
- Deferring Patches: Treating "medium" severity (CVSS 4.9) as non-urgent. A public PoC elevates any vulnerability to critical status.
- Over-Privileged Admins: Having many users with full administrative privileges on ISE, increasing the attack surface for credential theft.
- Lack of Isolation: Running the ISE application on a server that also hosts other critical services, allowing a compromise to spread easily.
- Missing Backups: Attempting a major version upgrade or patch without a verified, recent backup of both config and runtime data.
✅ Best Practices for a Secure Posture
- Immediate Patching Cadence: Establish a policy to apply security patches for critical infrastructure like ISE within 72 hours of release, especially with a known PoC.
- Strict Principle of Least Privilege: Create granular admin roles in ISE. Does every admin need the "Super Admin" role to manage licenses? Restrict upload capabilities.
- Enforce Multi-Factor Authentication (MFA): Implement MFA for all administrative access to ISE. This is a single most effective measure to prevent the initial credential-based access required for this exploit.
- Comprehensive Monitoring: Extend your SIEM coverage to ingest ISE application logs. Create alerts for "file upload" events in the licensing module or for the ISE process accessing known sensitive OS files.
- Regular External Assessments: Include your network access control systems in annual penetration tests or Red Team exercises to find misconfigurations and vulnerabilities before attackers do.
Proactive Defense: A 5-Layer Implementation Framework
Move beyond reactive patching. Use this framework to build resilience against privilege boundary bypasses in all critical applications.
Layer 1: Asset & Vulnerability Management
Action: Maintain a real-time inventory of all network infrastructure software (like ISE) with versions. Subscribe to vendor security advisories (e.g., Cisco Security Advisories). Integrate this with a vulnerability scanner that can authenticate and check versions.
Layer 2: Access Hardening
Action: For every admin interface, enforce MFA. Implement role-based access control (RBAC). Use a privileged access management (PAM) solution to vault credentials and manage sessions. All admin access should be from dedicated, hardened jump hosts.
Layer 3: Host & Application Hardening
Action: Harden the OS hosting ISE (disable unnecessary services, use a dedicated service account). Run the application with the minimum required privileges. Implement File Integrity Monitoring (FIM) on critical OS and application files.
Layer 4: Detective Controls
Action: Deploy an EDR/XDR agent on the ISE server. Configure your SIEM (like Splunk or Elastic) with custom rules to detect anomalous behavior from the ISE application process, such as spawning shells or reading /etc/shadow. For deep packet inspection, ensure tools like Snort 3 are also patched (related to CVE-2026-20026/20027).
Layer 5: Incident Response Readiness
Action: Have a dedicated playbook for "Compromise of Network Access Control System." This should include steps for isolation, credential rotation, forensic data collection from ISE, and communication plans. Regularly conduct tabletop exercises for this scenario.
Frequently Asked Questions (FAQ)
Q1: The CVSS score is only 4.9 (Medium). Why is this such a big deal?
A: CVSS is a starting point, not the whole story. The "medium" score often reflects the requirement for admin credentials. However, the public availability of a working Proof-of-Concept (PoC) exploit dramatically increases the risk. It means the barrier to exploitation is now very low for any attacker who obtains those credentials. The impact, full system compromise, is severe, making this a high-priority issue in practice.
Q2: We use ISE in a multi-node deployment. Do we need to patch every node?
A: Yes. When you install the patch on the primary Administration Node, the process should automatically replicate and apply it to all secondary nodes (Policy Service Nodes, Monitoring Nodes) in the deployment. It is critical to verify the patch was successfully applied on all nodes by checking the version on each one post-installation.
Q3: Are there any indicators of compromise (IoCs) we can hunt for?
A: Yes. Look for these logs and activities:
- ISE Application Logs: Unexplained XML file upload events or errors in the licensing service logs.
- OS-Level Logs: The ISE application process (e.g., `ise-process`) reading files like `/etc/passwd`, `/etc/shadow`, or SSH keys in `/root/.ssh/`.
- Network Logs: Outbound connections from the ISE server to unexpected external IPs shortly after an admin login and file upload event.
Q4: This requires admin access. Wouldn't an admin already have full control?
A: This is the core lesson of the privilege boundary. No, an application administrator should not have full control over the host operating system. This is a fundamental security design principle called separation of duties. The ISE admin manages network access policies. The system administrator manages the OS. Allowing one role to silently usurp the other's permissions is a critical design flaw that enables massive lateral movement.
Key Takeaways and Action Items
The CVE-2026-20029 vulnerability is more than a bug; it's a case study in failed security boundaries. Here is your immediate action plan:
- Patch Immediately: If you run Cisco ISE/ISE-PIC versions 3.2, 3.3, or 3.4, apply the specified patches (3.2P8, 3.3P8, 3.4P4) now. Versions before 3.2 require a migration plan.
- Audit Admin Access: Review all accounts with administrative privileges on your ISE deployment. Implement the principle of least privilege and enforce MFA without delay.
- Hunt for IoCs: Use the indicators mentioned in the FAQ to search your logs for any signs of prior exploitation.
- Adopt the Framework: Use the 5-layer defense framework to assess and strengthen the security posture of all your critical infrastructure applications, not just ISE.
- Educate Your Team: Share this analysis with your network and security teams. Understanding "the why" behind a patch creates a more security-conscious culture.
Staying ahead of threats requires continuous learning. For the latest vulnerabilities and in-depth technical analyses, consider following resources like the CISA Known Exploited Vulnerabilities Catalog, the MITRE ATT&CK® Knowledge Base, and the NIST National Vulnerability Database.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































