CISA Retires Emergency Directives
A Victory for Proactive Cybersecurity Explained Simply
In a significant move signaling a shift in the national cybersecurity posture, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) recently announced the retirement of ten emergency directives issued between 2019 and 2024. This CISA emergency directives retirement is not a rollback of security but a landmark achievement, it represents the successful institutionalization of urgent, reactive patches into enduring, proactive defense frameworks. For cybersecurity professionals and beginners alike, this event offers a masterclass in effective vulnerability management and the evolution from crisis response to strategic resilience. This blog post will decode the technical and strategic implications of this milestone, linking the retired directives to real-world attacks and the MITRE ATT&CK framework, and provide actionable lessons for organizations of all sizes.
Table of Contents
- The Big Picture: Why Retiring Directives is a Win
- A Timeline of Threats: What These Directives Stopped
- The Attacker's View: MITRE ATT&CK Tactics Behind the Alerts
- Common Mistakes & Best Practices for Vulnerability Management
- Red Team vs. Blue Team: Perspectives on the Retirement
- Your Implementation Framework: Building a Proactive Defense
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
The Big Picture: Why Retiring Directives is a Win
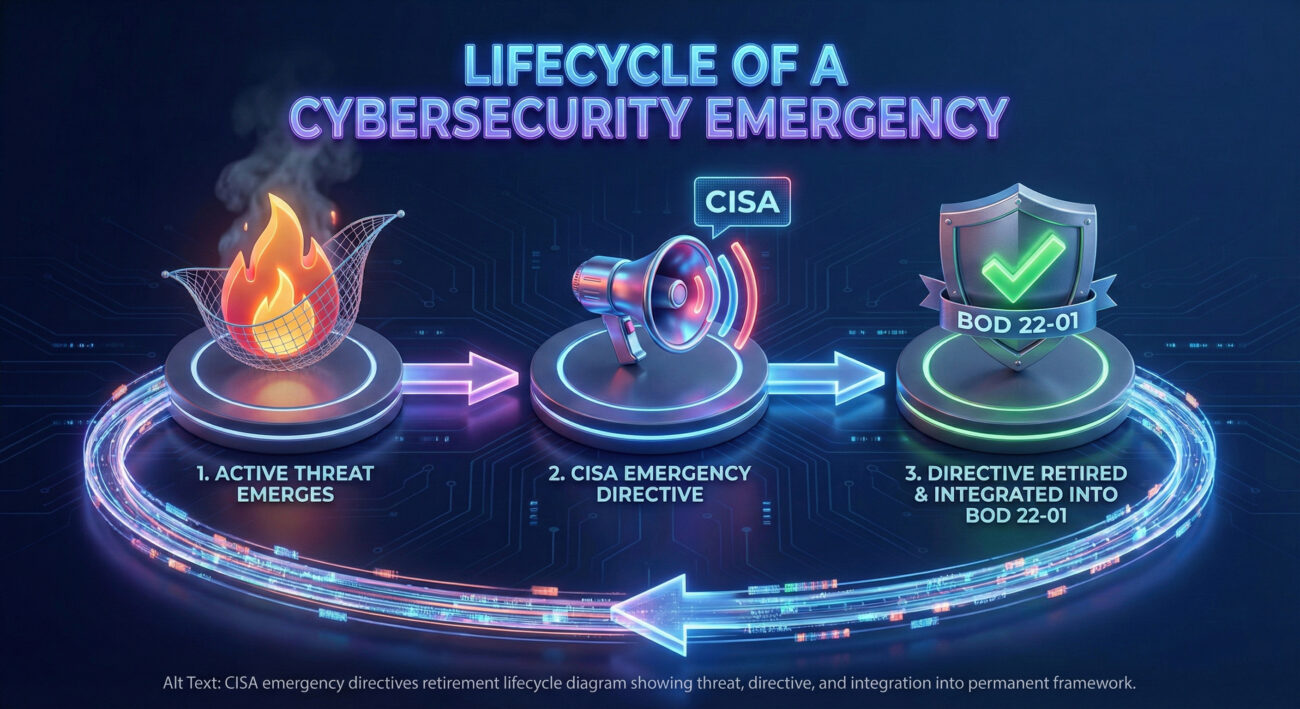
An Emergency Directive (ED) is CISA's "break glass in case of fire" tool. It mandates immediate action for Federal Civilian Executive Branch (FCEB) agencies to mitigate an active, unacceptable threat. Think of it as a nationwide emergency alert for a specific, critical cybersecurity vulnerability being exploited. The retirement of ten such directives means the fires have been put out, the root causes addressed, and the lessons learned baked into the standard operating procedure.
CISA stated these actions are now enforced through the more permanent Binding Operational Directive (BOD) 22-01, which maintains the Known Exploited Vulnerabilities (KEV) catalog. This transition is crucial. It moves urgent, one-off fixes into a structured, continuous, and predictable process for managing known threats. For defenders, this is evidence that a reactive security posture is maturing into a proactive, intelligence-driven one.
A Timeline of Threats: What These Directives Stopped
While CISA's announcement didn't list all ten retired EDs, historical data points to major campaigns they countered. These directives were often responses to widespread exploitation of critical vulnerabilities in foundational technologies.
For example, ED 19-01 (2019) addressed critical vulnerabilities in Domain Name System (DNS) infrastructure. An attack on DNS is like tampering with the phonebook of the internet, it can redirect users from legitimate sites to malicious ones for credential theft or malware deployment without their knowledge. Another, ED 21-02, focused on on-premises Microsoft Exchange Server vulnerabilities (like ProxyLogon) which were being exploited by state-sponsored actors to gain persistent, deep access to email systems for espionage.
| Emergency Directive (Sample) | Vulnerability / Threat Targeted | Potential Consequence if Unpatched |
|---|---|---|
| ED 19-01 | DNS Infrastructure Vulnerabilities | Traffic hijacking, broad user compromise, data theft. |
| ED 20-02 / 20-03 | Pulse Secure VPN & Citrix ADC Flaws | Remote network access for hackers, lateral movement, ransomware deployment. |
| ED 21-02 / 21-03 | Microsoft Exchange Server (ProxyLogon) | Full server control, email exfiltration, persistent backdoor for espionage. |
| ED 22-03 / 23-03 | VMware & Atlassian Confluence Flaws | Access to virtualization management and collaboration tools, massive data breach. |
The Attacker's View: MITRE ATT&CK Tactics Behind the Alerts
To understand the significance of the CISA emergency directives retirement, we must view the original threats through the lens of the adversary. The MITRE ATT&CK framework categorizes the techniques threat actors use. The retired directives primarily countered techniques in the initial stages of a attack chain.
How the Exploits Worked (Technical Perspective)
Let's take ED 21-02 (Microsoft Exchange ProxyLogon) as a case study. This was not one bug but a chain of vulnerabilities (CVE-2021-26855, 26857, 26858, 27065). At its core, it allowed an attacker to bypass authentication and execute code as the powerful SYSTEM user on the server. Here's a simplified view of the attack flow:
Step 1: Initial Access (MITRE Tactic: Initial Access)
The attacker sends a specially crafted HTTP request to the vulnerable Exchange server's web front-end (Outlook Web Access). The server incorrectly authenticates this request, granting access.
Step 2: Privilege Escalation & Execution (Tactic: Privilege Escalation, Execution)
Using the gained access, the attacker uploads a malicious web shell (a small piece of code) to a writable directory on the server. This web shell executes commands with the high privileges of the underlying system.
Step 3: Persistence & Impact (Tactic: Persistence, Impact)
The web shell provides a permanent backdoor. The attacker can now steal all emails, install ransomware, or use the compromised server as a foothold to attack other systems inside the network.
This sequence maps directly to MITRE ATT&CK techniques like Exploit Public-Facing Application (T1190), Web Shell (T1505.003), and Account Manipulation (T1098). CISA's directive forced a mass patch and cleanup operation, directly disrupting the Initial Access and Persistence tactics for a wide range of adversaries.
Common Mistakes & Best Practices for Vulnerability Management
The retirement of these directives highlights both past failures and current best practices. Organizations often fall into traps that make them vulnerable to the exact threats CISA had to address nationally.
Common Mistakes (What Led to the Emergencies)
- Ignoring "Known" Threats: De-prioritizing the patching of vulnerabilities that have public proof-of-concept code or are listed in CISA's KEV catalog, assuming they won't be targeted.
- Misplaced Focus: Investing heavily in advanced "unknown threat" detection while neglecting basic hygiene like timely updates for internet-facing systems (VPNs, email servers, CMS).
- Complex Patch Delays: Allowing patching cycles to stretch for weeks or months due to testing complexity or fear of downtime, leaving critical windows of exposure wide open.
- Lack of Asset Visibility: Not maintaining an accurate inventory of all internet-facing assets. You can't secure or patch what you don't know exists.
Best Practices (The Lessons Institutionalized)
- Prioritize by Threat, Not Just Severity: Use the CISA KEV Catalog as your primary patch priority list. A "Critical" CVSS 10 flaw with no active exploitation is less urgent than a "High" CVSS 7 flaw being used in real attacks.
- Implement a Compressed Patch Cycle: For critical infrastructure and internet-facing systems, establish a policy to apply patches for known exploited vulnerabilities within 48-72 hours. Automation is key.
- Adopt a Zero-Trust Mindset: Assume breach. Segment networks, enforce strict access controls, and use multi-factor authentication (MFA) everywhere, especially on admin accounts and remote access services.
- Continuous Monitoring & Validation: Don't just patch; verify. Use vulnerability scanners and threat intelligence feeds to continuously confirm your defenses are holding against known tactics.
Red Team vs. Blue Team: Perspectives on the Retirement
The Red Team (Adversary) View
"The CISA emergency directives retirement is a signal to adapt. Our favorite 'low-hanging fruit', unpatched Exchange servers, vulnerable VPN appliances, are becoming harder to find in the federal space because the directive forced a massive cleanup. This raises the cost of entry for broad campaigns.
Our focus shifts to:
- Newer Vulnerabilities: Targeting flaws disclosed after the directive era, in software not widely covered by such mandates.
- Supply Chain & Third-Party Access: Exploiting weaker security in vendor software or partner organizations that connect to hardened federal networks.
- Social Engineering: Doubling down on phishing to bypass technical controls, as human error remains a constant.
The retirement doesn't mean we've lost; it means we must be more sophisticated, precise, and patient."
The Blue Team (Defender) View
"This retirement is a major validation of our work. It shows that systemic, mandated action on known vulnerabilities works. It has literally removed entire classes of easy attacks from the adversary's playbook against federal systems.
Our takeaways and new focus are:
- Sustainable Processes Over Heroics: The goal is to build processes (like automated patching tied to the KEV) that prevent emergencies, not just respond to them heroically.
- Threat Intelligence is Non-Negotiable: Subscribing to and acting on feeds like CISA's alerts is the single most effective way to prioritize work.
- Extend the Framework: We must now apply the same rigorous 'known vulnerability' management principles that succeeded federally to our own state, local, and private sector partners.
This is a win, but vigilance is eternal. We're moving from fighting fires to strengthening the fireproofing of the entire building."
Your Implementation Framework: Building a Proactive Defense
Inspired by the success behind the CISA emergency directives retirement, here is a step-by-step framework any organization can adopt to mature its own vulnerability management program.
Step 1: Foundational Asset & Vulnerability Inventory
You cannot defend what you cannot see. Use tools to discover all assets (hardware, software, cloud instances) on your network, especially those facing the internet. Continuously scan them for vulnerabilities to create a live inventory.
Step 2: Integrate Threat Intelligence for Prioritization
Connect your vulnerability scanner to a threat intelligence feed. The highest priority must be vulnerabilities tagged as "Actively Exploited" in CISA's KEV catalog or by other reputable sources. This moves you from patching based on theoretical severity to patching based on actual risk.
Step 3: Establish & Enforce Compressed SLAs
Define and enforce strict Service Level Agreements (SLAs) for patching:
Critical/Actively Exploited: Patch within 48-72 hours.
High Severity: Patch within 2 weeks.
All others: Patch within a standard monthly cycle.
Step 4: Automate and Validate
Automate patch deployment where possible, especially for common, high-volume software. After patching, re-scan the asset to validate the fix was applied correctly and the vulnerability is closed. This closes the loop.
Step 5: Adopt a "Secure by Design" Posture
Look beyond patching. Work with procurement and development teams to prioritize purchasing and building software with security features (like MFA and logging) enabled by default. This is the long-term vision CISA advocates to prevent future emergencies.
Frequently Asked Questions (FAQ)
Q: Does the retirement mean these vulnerabilities are no longer dangerous?
A: Absolutely not. The vulnerabilities are still technically present in the code. Their "retirement" means the mandated, emergency-level response is over because the federal enterprise has largely implemented the required patches and mitigations. Any organization that has not patched these old flaws remains extremely vulnerable.
Q: As a small business, do CISA's directives apply to me?
A: While not legally binding for you, they are the most critical guidance you can follow. The threats targeted nation-state actors going after federal agencies. If you use the same technology (Microsoft Windows, VMware, Cisco VPNs), you are on the same attack surface. Adversaries will test these exploits against every organization. Treat CISA's KEV catalog as your mandatory patching list.
Q: What's the difference between an Emergency Directive (ED) and a Binding Operational Directive (BOD)?
A: An ED is an urgent, time-bound order for an imminent threat. It's like a fire alarm. A BOD is a standing, ongoing requirement to maintain a certain security baseline, like BOD 22-01 which requires agencies to patch vulnerabilities on the KEV catalog on a defined timeline. It's like a building's ongoing fire code. The retirement of EDs into BODs shows a transition from crisis to compliance.
Q: How can I stay updated on new threats like these?
A: Subscribe to CISA's Alerts and Announcements. Follow reputable cybersecurity news sources like Krebs on Security or SecurityWeek. For technical details on vulnerabilities, the NIST National Vulnerability Database (NVD) is the primary source.
Key Takeaways & Call to Action
The CISA emergency directives retirement is a defining moment in cybersecurity. It proves that coordinated, forceful action on known vulnerabilities is the most effective way to disrupt adversaries and raise national cyber resilience. The transition from reactive EDs to the proactive BOD 22-01 framework is a model every organization should emulate.

Your Action Plan Starts Today:
- Bookmark and Review Weekly: Make the CISA Known Exploited Vulnerabilities Catalog your homepage for patch management.
- Conduct a Gap Assessment: Do you have an accurate asset inventory? What is your current SLA for patching critical bugs? Find your biggest gap from the framework above.
- Start Small, Build Momentum: Pick one internet-facing system group (e.g., all your firewalls or web servers) and commit to patching any KEV-listed flaw on it within 7 days. Use that success to justify a broader program.
Become a Proactive Defender
The era of waiting for an emergency directive is over. The strategy is clear: know your assets, prioritize by active threat, patch ruthlessly, and build secure foundations. By learning from the success behind this CISA emergency directives retirement, you can transform your organization's cybersecurity from a cost center focused on breach response into a strategic advantage built on resilience and confidence.
Start by reviewing your systems against the KEV catalog today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































