VMware ESXi VM Escape Exploit Exposed
Defend Your Virtual Fortress Now Explained Simply
In December 2025, cybersecurity defenders intercepted a chillingly sophisticated attack that targeted the very foundation of modern cloud infrastructure: the VMware ESXi hypervisor. This wasn't a simple malware infection; it was a surgical breach designed to shatter the fundamental security promise of virtualization, isolation. By chaining together three previously unknown zero-day vulnerabilities, threat actors linked to Chinese-speaking regions demonstrated a capability to escape from within a confined virtual machine (VM) and seize full control of the host server. This VMware ESXi VM escape exploit represents a worst-case scenario for data center and cloud security, granting attackers the keys to the entire virtual kingdom. This guide breaks down this complex attack, explains the technical wizardry behind it, and provides a clear blueprint for defense.
Table of Contents
- Executive Summary: The Hypervisor Under Siege
- The Attack Scenario: A Step-by-Step Breakdown
- Vulnerability Deep Dive: The Three Zero-Day Flaws
- Anatomy of the Exploit: Step-by-Step Attack Flow
- Mapping to MITRE ATT&CK: The Adversary's Playbook
- Red Team vs. Blue Team Perspectives
- Common Mistakes & Best Practices for Defense
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
1. Executive Summary: The Hypervisor Under Siege
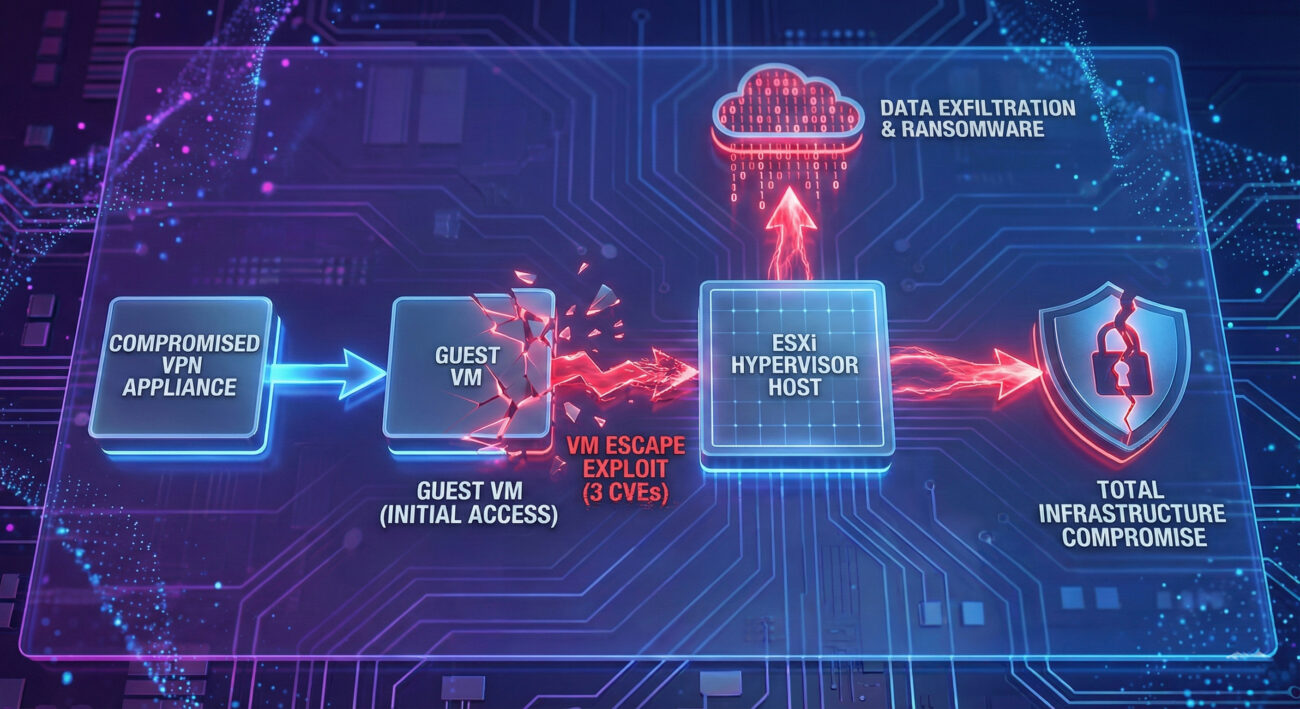
In late 2025, security analysts at Huntress uncovered a targeted intrusion with one ultimate goal: to achieve a full virtual machine escape on VMware ESXi platforms. The attackers first compromised a network's perimeter via a SonicWall VPN appliance. Once inside, they deployed a custom-built exploit toolkit, codenamed "MAESTRO," which weaponized three critical VMware ESXi vulnerabilities (CVE-2025-22224, CVE-2025-22225, CVE-2025-22226).
The sophistication was staggering. Evidence suggested the exploit was developed as a zero-day over a year before VMware's public disclosure in March 2025. The toolkit's internal use of Simplified Chinese strings and its precision pointed to a well-resourced, state-linked actor. The attack chain involved memory leaks, kernel driver manipulation, and ultimately the execution of a stealthy backdoor (VSOCKpuppet) that communicated over a virtual socket channel, rendering it invisible to standard network monitoring. This VMware ESXi VM escape exploit is a masterclass in offensive security, turning the hypervisor from a defender's fortress into an attacker's playground.
2. The Attack Scenario: A Real-World Use Case
Imagine a mid-sized financial services firm that relies on a private VMware cloud to host its customer portal, transaction databases, and internal applications. Their security team has rightly focused on protecting the individual VMs with anti-virus and intrusion detection systems. The network perimeter is guarded by a SonicWall VPN for remote employee access.
An advanced persistent threat (APT) group, after some reconnaissance, discovers an unpatched vulnerability in the specific SonicWall VPN model the firm uses. They gain an initial foothold, not into a critical server, but into a low-privilege virtual machine used for general employee workloads. From this seemingly insignificant beachhead, they deploy the MAESTRO toolkit. Within minutes, the exploit executes, the VM's walls vanish, and the attackers now have code running directly on the ESXi hypervisor with the highest privileges.
From here, the impact is catastrophic: they can create, delete, or snapshot any VM (including the domain controllers and SQL servers), intercept all traffic flowing between VMs, and install persistent backdoors at a layer below the operating system. They could silently exfiltrate data for months or deploy ransomware that encrypts every virtual disk file (.vmdk) at the storage level, making restoration from backup nearly impossible. This scenario underscores why a VMware ESXi VM escape exploit is a game-ending event in cybersecurity.
3. Vulnerability Deep Dive: The Three Zero-Day Flaws
The potency of this attack came from chaining three specific vulnerabilities in VMware's ESXi, Workstation, Fusion, and Cloud Foundation products. Broadcom disclosed them as zero-days in March 2025, and CISA immediately added them to its Known Exploited Vulnerabilities (KEV) catalog.
| CVE Identifier | CVSS Score | Technical Description | Role in the Exploit Chain |
|---|---|---|---|
| CVE-2025-22224 | 9.3 (Critical) | An out-of-bounds read vulnerability in the Host-Guest File System (HGFS). Allows an attacker with admin privileges in the guest VM to leak memory contents from the VMX process on the host. | Information Gathering: Used to leak critical memory addresses from the VMX process, which are essential for the next stages to work. It's the "reconnaissance" step of the exploit. |
| CVE-2025-22226 | 7.1 (High) | A heap-based buffer overflow vulnerability in the Virtual Machine Communication Interface (VMCI). Allows an attacker to corrupt memory in the host's VMX process. | Memory Corruption: Provides the initial ability to write and corrupt memory in the target VMX process, setting the stage for code execution. |
| CVE-2025-22225 | 8.2 (High) | An arbitrary write vulnerability in the VMCI. Allows an attacker to write data to arbitrary locations in the VMX process memory. | Sandbox Escape & Code Execution: The final blow. This flaw is exploited to overwrite a critical function pointer in VMX memory, redirecting execution to the attacker's shellcode and completing the escape from the VM sandbox. |
Individually, these flaws are dangerous. Together, they form a devastating chain: Leak information to understand the target's memory layout (CVE-2025-22224), use that knowledge to corrupt memory precisely (CVE-2025-22226), and finally hijack the program's execution flow to run your own code on the host (CVE-2025-22225). This trifecta is what enables the full VMware ESXi VM escape exploit.
4. Anatomy of the Exploit: Step-by-Step Attack Flow
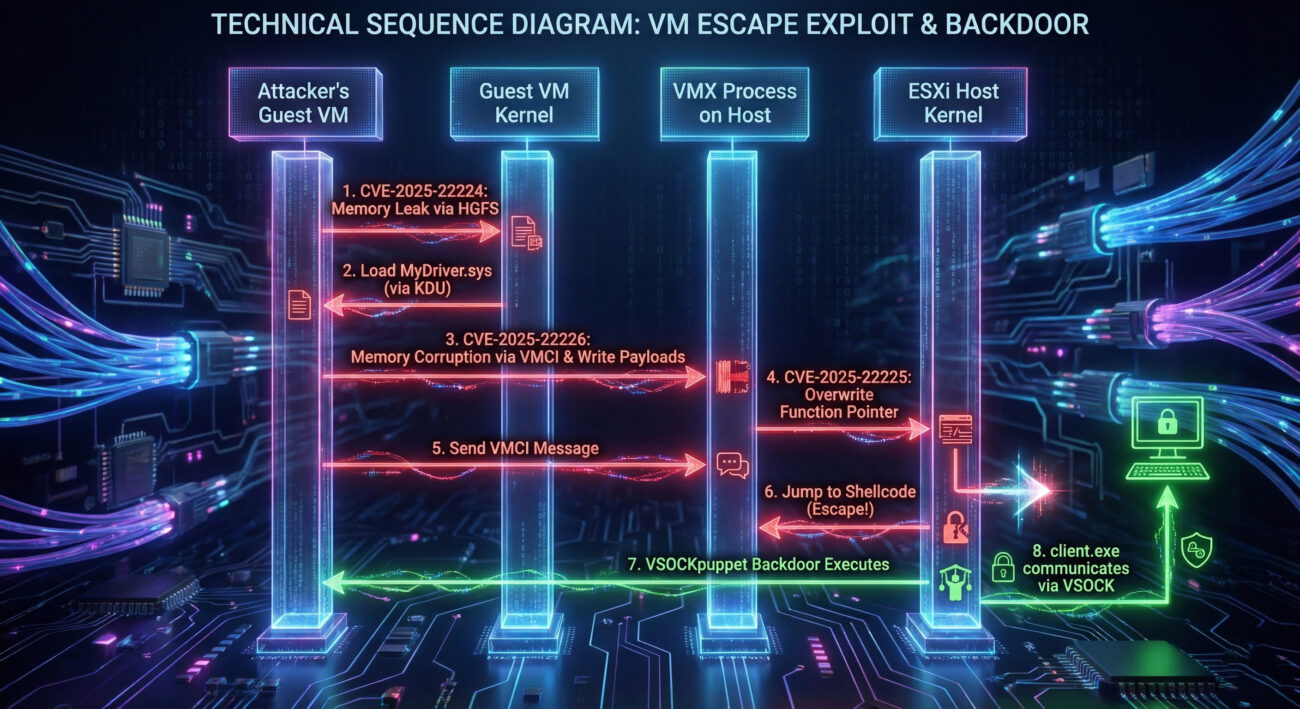
Let's walk through the exact sequence of events as executed by the MAESTRO toolkit. This demonstrates the precision required for a successful hypervisor breach.
Step 1: Initial Deployment & Reconnaissance
The attacker, already inside a Windows guest VM, executes exploit.exe (MAESTRO). The first action is reconnaissance. It uses the HGFS vulnerability (CVE-2025-22224) to leak memory from the host's VMX process. This leak reveals the exact ESXi version and, crucially, the memory addresses of key structures needed for the next steps. Simultaneously, it uses devcon.exe to disable the guest's VMCI drivers, preventing interference.
Step 2: Kernel Driver Exploitation
The toolkit then loads an unsigned kernel driver, MyDriver.sys, into the guest VM's kernel memory using a tool called Kernel Driver Utility (KDU). This driver is the workhorse. It now operates with high privileges inside the guest and triggers the VMCI buffer overflow (CVE-2025-22226). This corruption allows the attacker to write three payloads directly into the VMX process's memory on the host:
- Stage 1 Shellcode: Prepares the environment for the escape.
- Stage 2 Shellcode: Establishes a foothold on the ESXi host.
- VSOCKpuppet Backdoor: A persistent 64-bit ELF binary that listens on virtual socket port 10000.
Step 3: The Pointer Overwrite & Escape
This is the critical escape moment. The exploit leverages the arbitrary write flaw (CVE-2025-22225). It overwrites a function pointer inside the VMX process memory, replacing it with the address of the Stage 1 shellcode it just planted. It then sends a VMCI message to the host. When the VMX process handles this message, it follows the corrupted pointer and jumps to the attacker's shellcode instead of its legitimate code. The sandbox is now broken.
Step 4: Backdoor Communication & Control
With the VSOCKpuppet backdoor running on the ESXi host, the attacker uses a separate component, client.exe (GetShell Plugin), from any guest VM on the compromised host. This client communicates with the backdoor over the VSOCK channel (port 10000), a pathway invisible to physical network cards. The attacker can now execute shell commands on the hypervisor, upload/download files, and maintain persistent, stealthy control.
5. Mapping to MITRE ATT&CK: The Adversary's Playbook
Framing this attack within the MITRE ATT&CK framework helps defenders understand the tactics, techniques, and procedures (TTPs) used and where to look for detection opportunities.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It Was Applied in This Attack |
|---|---|---|
| Initial Access | T1190 • Exploit Public-Facing Application | The initial compromise of the SonicWall VPN appliance provided the first entry point into the network. |
| Execution | T1203 • Exploitation for Client Execution | The MAESTRO toolkit (exploit.exe) was executed on a guest VM to trigger the vulnerability chain. |
| Privilege Escalation | T1068 • Exploitation for Privilege Escalation | The core of the VMware ESXi VM escape exploit: chaining three CVEs to escalate from guest VM user privileges to hypervisor kernel-level privileges. |
| T1547.012 • Boot or Logon Autostart Execution: Kernel Modules and Extensions | Loading the malicious MyDriver.sys kernel driver via KDU to gain elevated execution within the guest. |
|
| Defense Evasion | T1622 • Debugger Evasion / T1036 • Masquerading | Disabling VMCI drivers temporarily to avoid detection/crashes; using an unsigned driver; VSOCK communication bypasses network monitoring. |
| Command and Control | T1573 • Encrypted Channel & T1095 • Non-Application Layer Protocol | The VSOCKpuppet backdoor used the VSOCK protocol (a non-IP, host-guest channel) for stealthy C2, bypassing traditional firewall/IDS. |
For detailed information on these techniques, refer to the official MITRE ATT&CK page for Exploitation for Privilege Escalation (T1068).
6. Red Team vs. Blue Team Perspectives
Red Team View: The Attacker's Advantage
For a red teamer or threat actor, this exploit is a golden ticket. The attack surface is the hypervisor, a high-value, foundational target often assumed to be secure by virtue of isolation.
- Stealth is Paramount: Using VSOCK for C2 is brilliant. It operates below the traditional network stack, making packet capture and netflow analysis useless. Detection requires host-based scrutiny of the hypervisor's process list and virtual device connections.
- Persistence vs. Stealth Trade-off: The toolkit reportedly prioritized stealth. Instead of making permanent changes to hypervisor disk files (which are easier to detect with file integrity monitoring), it operated in memory, potentially losing access on a host reboot but leaving minimal forensic traces.
- Exploitation as a Service: The presence of a README file suggests this toolkit is designed for operators who may not be the original developers. This points to a private, high-end market for such capabilities, where the exploit is the product.
Blue Team View: The Defender's Challenge
For defenders, this is a sobering reminder that perimeter and VM-level security are insufficient. The blue team's focus must shift "left and down", earlier in the kill chain and deeper into the infrastructure stack.
- Detection Blind Spot: The primary challenge is visibility. Blue teams need tools that can monitor hypervisor process behavior (e.g., unusual VMX process memory writes, new ELF binaries executing on ESXi) and virtual network anomalies (VSOCK connections).
- Patch Urgency is Absolute: The moment Broadcom released patches (March 2025) and CISA added these CVEs to its KEV catalog, applying them became the #1 priority. This case proves that advanced actors will have exploits ready for public zero-days on day one.
- Layered Defense (Defense in Depth): Relying on virtualization isolation is a weak single point of failure. Defenders must implement strong network segmentation, strict identity management for hypervisor access, and dedicated runtime protection for ESXi hosts themselves.
7. Common Mistakes & Best Practices for Defense
Learning from this incident, here are critical errors to avoid and proactive measures to implement.
Common Mistakes to Avoid
- Treating the Hypervisor as a "Set-and-Forget" Asset: Neglecting regular patching, hardening, and specific monitoring of ESXi hosts leaves the entire virtual environment vulnerable to a VMware ESXi VM escape exploit.
- Over-Reliance on VM-Level Security: Assuming that securing the guest operating systems (with endpoint protection) is enough. If the hypervisor is compromised, all VMs are compromised, regardless of their internal security.
- Ignoring Peripheral Devices: Overlooking the security of edge devices like VPN appliances, which are common and effective initial access vectors for advanced attackers.
- Lack of Hypervisor-Specific Backups: Not having tested, isolated backups of the ESXi host configuration and VM disk files stored offline. A hypervisor-level ransomware attack can encrypt all attached datastores.
Best Practices to Implement Now
- Hypervisor Hardening & Immediate Patching: Follow VMware's security hardening guide rigorously. Most critically, apply all security patches immediately, especially for CVEs listed in CISA's KEV catalog. For the vulnerabilities discussed here, ensure you are running ESXi versions with the fixes for CVE-2025-22224, -22225, and -22226. Check the official VMware Security Advisory VMSA-2025-0004.
- Implement Dedicated Hypervisor Security: Deploy security solutions designed specifically for VMware environments, such as VMware vSphere Trust Authority or third-party tools that provide runtime integrity monitoring, anomaly detection, and malware scanning for ESXi hosts.
- Network Segmentation & Micro-Segmentation: Isolate management networks for vSphere/ESXi hosts from general user and VM traffic. Implement micro-segmentation (e.g., with VMware NSX) to control east-west traffic between VMs, limiting lateral movement even if a VM is compromised.
- Enhanced Monitoring and Logging: Aggregate and analyze logs from ESXi hosts (via syslog) into your SIEM. Look for signs like the loading of unknown kernel modules, unexpected processes running on the hypervisor, or anomalous VSOCK socket activity. CISA provides valuable guidance on defending against APT actors.
8. Frequently Asked Questions (FAQ)
Q1: How can I check if my ESXi host has been targeted by this specific exploit?
A: Forensics require specialized tools. Start by checking your ESXi host for:
- Unknown Processes: Use commands like
ps -con the ESXi shell to look for unfamiliar processes, especially any listening on unusual ports. - VSOCK Connections: Investigate any active VSOCK connections. The backdoor used port 10000.
- File System Anomalies: Look for unexpected files in temporary directories or new, unsigned kernel modules. Review Huntress's blog and threat reports for specific Indicators of Compromise (IoCs).
Consider engaging a professional incident response team if you suspect a compromise.
Q2: I've applied the VMware patches. Am I completely safe now?
A: Applying the patches for CVE-2025-22224, -22225, and -22226 closes the specific technical door used in this exploit. However, you are not "completely safe." Other hypervisor vulnerabilities may exist. Safety comes from a layered security posture: ongoing patching, network segmentation, strong credential hygiene, and dedicated monitoring. Patching is the most critical single action, but it's just one layer of defense.
Q3: What's the big deal about VSOCK communication?
A: VSOCK is a communication channel between the host and guest that doesn't use the traditional TCP/IP network stack. It's like a private, internal phone line that bypasses the company's main switchboard (the physical network). Standard network-based intrusion detection systems (IDS) and firewalls cannot see this traffic because it never hits a physical network interface card (NIC). This makes VSOCK an ideal stealth channel for advanced backdoors, as detection requires inspecting activity on the hypervisor itself.
Q4: Are other hypervisors (like Hyper-V or KVM) vulnerable to similar attacks?
A: The concept of VM escape is a universal threat to all virtualization platforms. While the specific code vulnerabilities (CVEs) discussed here are unique to VMware products, other hypervisors have had their own critical escape vulnerabilities in the past. The defense principles remain the same across platforms: diligent patching, minimal attack surface (hardening), principle of least privilege for management, and dedicated monitoring of the virtualization layer. No platform is inherently immune.
9. Key Takeaways & Call to Action
The discovery of this VMware ESXi VM escape exploit toolkit is a watershed moment. It demonstrates that advanced, state-sponsored actors possess and are willing to use capabilities that fundamentally undermine the security model of global cloud infrastructure.
Key Takeaways:
- Virtualization Isolation is Not Impervious: Treat "air-gapped" or isolated VMs with healthy suspicion. A determined adversary with the right exploit can break out.
- Speed of Patching is a Survival Skill: The timeline from patch release to active, sophisticated exploitation can be zero days. Your patching cadence for hypervisors must be measured in hours and days, not weeks or months.
- Defense Must Extend to the Hypervisor Layer: Your security strategy needs a dedicated pillar for protecting the virtualization infrastructure itself, with appropriate tools and logging.
- Stealth is the New Normal: Advanced adversaries are increasingly using memory-only malware and non-standard communication channels like VSOCK to evade detection. Your monitoring must adapt.
Your Action Plan Starts Now
Don't let this be just another article you read. Take these three concrete steps today:
- Audit & Patch: Immediately verify the patch level of every ESXi, vCenter, Workstation, and Fusion system in your environment against VMware's security advisories. Prioritize the March 2025 patches (VMSA-2025-0004).
- Review Architecture: Examine your network segmentation. Is your vSphere management network truly isolated? Do you have the ability to monitor and control east-west traffic between VMs?
- Enable Advanced Monitoring: Ensure logs from all hypervisors are flowing to your central SIEM. Work with your security team to develop alerts for hypervisor-level anomalies, such as new process execution on ESXi hosts.
The battle for security has moved to a new layer. Secure your foundation, or risk losing everything built upon it.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































