Black Axe Takedown
Inside the Massive Black Axe Syndicate Bust Explained Simply
A Deep Dive into the Techniques, Global Impact, and Cybersecurity Lessons from a Landmark Bust
Table of Contents
- Executive Summary: The Fall of a Syndicate
- Who Are the Black Axe? A Cybercrime Profile
- Operation Jackal 2025: The Global Takedown
- The MITRE ATT&CK Playbook of Black Axe
- Step-by-Step: Anatomy of a Black Axe Campaign
- Common Mistakes & Best Practices for Defense
- Red Team vs. Blue Team: Offensive Tactics vs. Defensive Strategies
- Key Takeaways for Cybersecurity Professionals
- Frequently Asked Questions (FAQ)
- Your Next Step: From Awareness to Action
In a landmark strike against organized cybercrime, a recent global operation led by Europol resulted in the arrest of 34 members of the notorious Black Axe syndicate. This takedown isn't just a news headline; it's a masterclass in modern cybercriminal operations and international law enforcement collaboration. For cybersecurity beginners and professionals alike, understanding the techniques used by groups like Black Axe is crucial for building effective defenses. This analysis breaks down the attack vectors, maps them to the MITRE ATT&CK framework, and provides actionable insights to bolster your security posture.
Executive Summary: The Fall of a Syndicate
On January 20, 2025, Europol, in coordination with law enforcement from 21 countries, executed a meticulously planned operation codenamed "Jackal 2025." The target was the inner circle of the Black Axe confraternity, a group that had evolved from a Nigerian campus cult into a sophisticated transnational cybercrime empire. The operation culminated in 34 arrests, the seizure of over €2 million in assets, and the dismantling of a significant portion of their digital infrastructure.
This takedown highlights a critical shift: cybercriminal organizations now operate with corporate-like structures, leveraging social engineering, financial fraud, and money laundering on an industrial scale. For defenders, the operation provides a rare, detailed look into the threat actor's playbook.
Who Are the Black Axe? A Cybercrime Profile
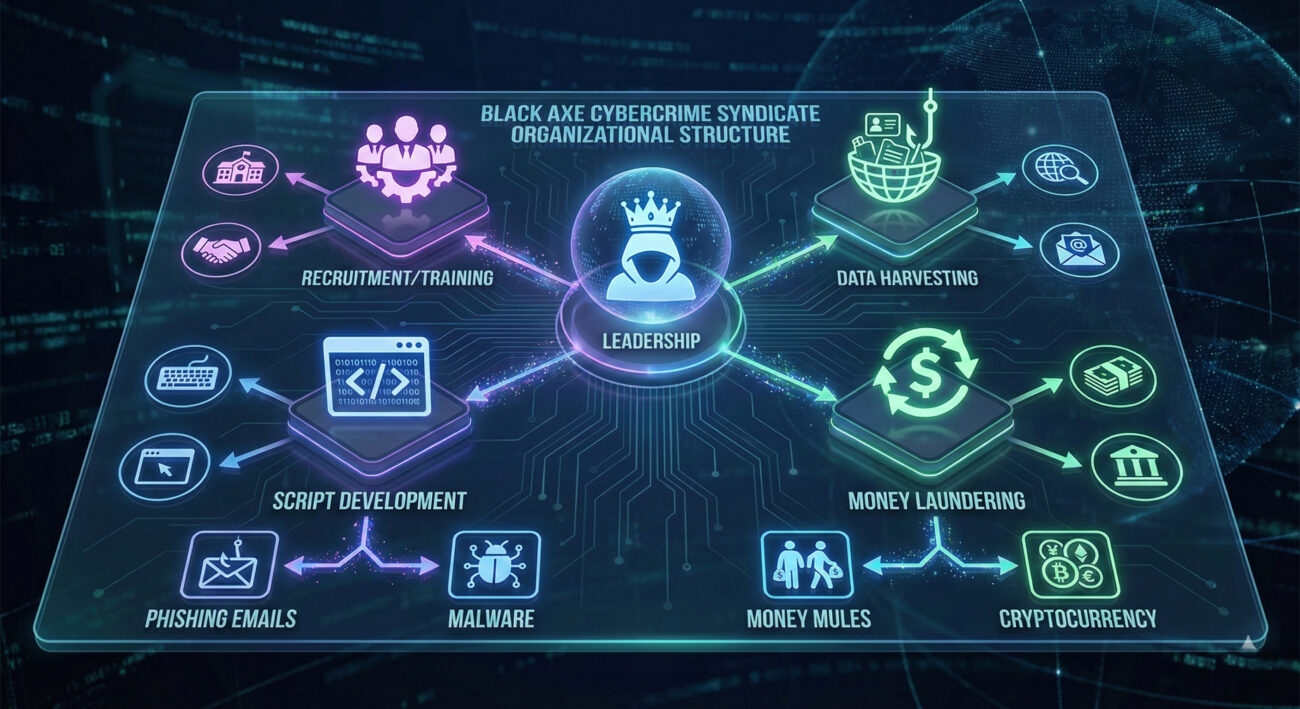
The Black Axe (also known as the "Neo-Black Movement of Africa") originated in the 1970s but pivoted to cyber-enabled crime in the early 2000s. They are not a loose group of hackers but a highly organized syndicate with defined roles:
- Recruiters & Trainers: Source and train individuals in social engineering and basic hacking.
- Data Harvesters: Specialize in obtaining personal identifiable information (PII) through phishing, data breaches, and buying from dark web markets.
- Script Developers: Create and manage the malware and tools used in campaigns.
- Money Launderers (Cashiers): Operate complex networks of "money mules" and cryptocurrency tumblers to clean illicit funds.
Their primary attack vectors center on high-volume, high-return scams like Business Email Compromise (BEC), romance scams (pig butchering), and large-scale phishing campaigns.
Operation Jackal 2025: The Global Takedown
The success of Operation Jackal was due to unprecedented international collaboration. Authorities didn't just target low-level operatives; they followed the money and data trail to mid-level managers and financiers.
- Scope: 21 countries involved, including the USA, UK, Canada, South Africa, and multiple EU nations.
- Actions Taken: 34 arrests, 58 locations searched, €2+ million in cash and assets seized, 400+ bank accounts frozen.
- Digital Evidence: Analysis of seized servers and devices revealed thousands of potential victims and the group's complete attack infrastructure.
This operation demonstrates a modern defense strategy: combining traditional policing with cyber forensic expertise to dismantle the entire criminal enterprise, not just its digital tools.
The MITRE ATT&CK Playbook of Black Axe
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques. Mapping the Black Axe takedown to this framework helps security teams understand and defend against similar threats.
| MITRE ATT&CK Tactic | Technique (ID) | How Black Axe Used It |
|---|---|---|
| Reconnaissance | Gather Victim Identity Info (T1589) | Scraped LinkedIn and social media for employee profiles to target in BEC attacks. |
| Initial Access | Phishing (T1566) | Mass phishing campaigns with malicious attachments (disguised as invoices, resumes) to deploy malware. |
| Execution | User Execution (T1204) | Relied on victims opening attachments or clicking links, often using psychological triggers like urgency or fear. |
| Persistence | Scheduled Task (T1053) | Used macros in documents to create scheduled tasks that would reinfect systems or maintain access. |
| Command & Control (C2) | Application Layer Protocol (T1071) | Used HTTPS and DNS tunnels to communicate with infected machines, blending traffic with normal web activity. |
| Exfiltration | Exfiltration Over C2 Channel (T1041) | Stolen credentials and financial data were sent back to attacker-controlled servers via the established C2 channel. |
| Impact | Financial Theft (T1657) | The ultimate goal: diverting funds via fraudulent wire transfers, gift card scams, and cryptocurrency theft. |
Understanding this attack chain is the first step in building defenses at each stage, a concept known as defense-in-depth.
Step-by-Step: Anatomy of a Black Axe Business Email Compromise (BEC) Campaign
Let's walk through a typical attack, highlighting the technical and social components.
Step 1: Reconnaissance & Target Selection
The group identifies a mid-sized company. Using open-source intelligence (OSINT), they compile a list of executives (CEO, CFO) and accounting staff from LinkedIn and the company website. They note email format (e.g., [email protected]).
Step 2: Initial Compromise & Persistence
They send a phishing email to an accountant, impersonating a trusted vendor with a "past due invoice" attachment. The attachment is a weaponized Microsoft Word document containing a malicious macro.
Dim cmd As String
cmd = "powershell -WindowStyle Hidden -EncodedCommand [MALICIOUS_BASE64_PAYLOAD]"
Shell(cmd, 0)
End Sub
If the user enables content, the macro executes a PowerShell command that downloads a remote access trojan (RAT) from a hacker-controlled server, establishing a foothold.
Step 3: Lateral Movement & Credential Harvesting
The RAT allows the attacker to move laterally within the network. They use keyloggers or dump credential stores (like the Windows LSASS memory) to steal login credentials for email and financial systems.
Step 4: The Fraudulent Transfer & Exfiltration
Using the stolen credentials, the hacker logs into the CFO's email account. They study email threads, then impersonate the CFO to send an urgent, legitimate-looking email to the accounting department, authorizing a large wire transfer to a fraudulent account controlled by a money mule. Funds are immediately transferred and laundered.
Common Mistakes & Best Practices for Defense
Common Mistakes (The Attackers' Entry Points)
- Lack of User Training: Employees clicking on links or enabling macros without verification.
- Weak Email Security: No filtering for impersonation (spoofing) or advanced phishing attempts.
- Poor Password Hygiene & No MFA: Reused passwords and lack of Multi-Factor Authentication on critical accounts make credential theft devastating.
- Unrestricted Macros: Allowing macros from the internet to run in Office documents.
- No Network Segmentation: Allowing a compromised user account full access to financial systems.
Best Practices (Building Your Defense)
- Implement Multi-Factor Authentication (MFA) Everywhere: Especially for email, VPN, and financial portals. This is the single most effective defense against credential theft.
- Conduct Regular, Realistic Security Awareness Training: Use simulated phishing campaigns to educate users.
- Deploy Advanced Email Security: Use solutions with impersonation protection, URL rewriting, and attachment sandboxing.
- Harden Endpoints: Disable Office macros from the internet, use application allowlisting, and run endpoint detection and response (EDR) software.
- Segment Your Network: Ensure accounting/finance systems are on a separate network segment with stricter access controls.
- Implement a Secure Financial Transaction Protocol: Require out-of-band verification (e.g., a phone call) for any payment or change to vendor details.
Red Team vs. Blue Team: Offensive Tactics vs. Defensive Strategies
This section contrasts the attacker's mindset (Red Team) with the defender's (Blue Team) in the context of a Black Axe-style attack.
Red Team (Attacker) View
Objective: Infiltrate, establish persistence, steal money.
- Focus on the Human: The easiest weak point is human psychology. Craft convincing lures.
- Evade Detection: Use living-off-the-land techniques (PowerShell, legitimate admin tools) to avoid triggering antivirus.
- Persistence is Key: Ensure access remains even if the initial entry point is closed.
- Follow the Process: Mimic legitimate business workflows (like invoice payments) to avoid raising alarms.
Blue Team (Defender) View
Objective: Prevent, detect, respond, and recover.
- Assume Breach: Operate under the assumption that a phishing email will eventually succeed.
- Monitor for Anomalies: Look for unusual logins (time, location), spikes in PowerShell usage, or abnormal outbound data transfers.
- Implement Zero Trust: "Never trust, always verify." Strict access controls and continuous authentication.
- Have an Incident Response Plan: Know exactly who to call and what to do when a breach is detected to minimize damage.
Key Takeaways for Cybersecurity Professionals
- Cybercrime is Organized Business: Groups like Black Axe are run like corporations, with specialization and scalability. Defenses must be equally professional.
- The Kill Chain is Your Defense Map: Use frameworks like MITRE ATT&CK to identify and shore up weak points at every stage of a potential attack.
- Technology + People + Process: No single silver bullet exists. Effective security combines technical controls (MFA, EDR), trained people, and solid processes (incident response).
- Collaboration is Force Multiplier: Just as law enforcement agencies collaborated for this takedown, sharing threat intelligence within your industry is crucial.
- Focus on Impact: Prioritize defenses that protect your organization's crown jewels, financial assets, intellectual property, and customer data.
Frequently Asked Questions (FAQ)
Q: As a small business, am I a target for groups like Black Axe?
A: Absolutely. Small and medium-sized businesses are often targeted precisely because they may have fewer security resources than large enterprises. The attack is automated and scalable; you don't need to be a specific target to get caught in their net.
Q: What's the #1 thing I should do right now to protect my organization?
A: Enable Multi-Factor Authentication (MFA) on all business-critical accounts, especially email, cloud services, and banking. This single step would have thwarted most of Black Axe's successful BEC scams, even if they stole the password.
Q: Where can I learn more about the MITRE ATT&CK framework?
A: The official MITRE ATT&CK website is the best resource. Visit https://attack.mitre.org/. For practical learning, platforms like TryHackMe and Cybrary offer hands-on courses that incorporate the framework.
Q: How can I stay updated on major cybercrime takedowns and threats?
A: Follow reputable sources. Besides The Hacker News, consider following advisories from CISA US-CERT, UK NCSC, and threat intelligence blogs from companies like Mandiant and CrowdStrike.
Your Next Step: From Awareness to Action
The story of the Black Axe takedown is more than a victory for law enforcement; it's a roadmap for your own cybersecurity journey. Don't let awareness be the end goal.
Action Plan for This Week:
- Audit Your MFA: Check every critical business account. If MFA is optional, enable it today.
- Review Macro Settings: Work with your IT team to disable macros from the internet in Microsoft Office via Group Policy or endpoint management.
- Schedule a Training: Book a 30-minute security awareness session for your team focusing on identifying BEC and phishing attempts.
- Bookmark MITRE ATT&CK: Start exploring one technique per week to understand how attackers operate and how to defend against it.
Cybersecurity is a continuous process. By learning from the tactics of groups like Black Axe, you empower yourself and your organization to build a strong, resilient defense.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































