Fake Booking Emails Redirect Hotel Staff to Fake BSoD Pages Delivering DCRat

In the ever-evolving landscape of cyber threats, a new, highly targeted phishing campaign has emerged, masquerading as legitimate hotel booking confirmations. This attack doesn’t just try to steal your login credentials, it’s a multi-stage breach designed to drain your wallet and compromise your identity. For cybersecurity beginners and professionals alike, understanding the mechanics of this hotel booking phishing scam is crucial for building effective defenses.
What is Identity Dark Matter?
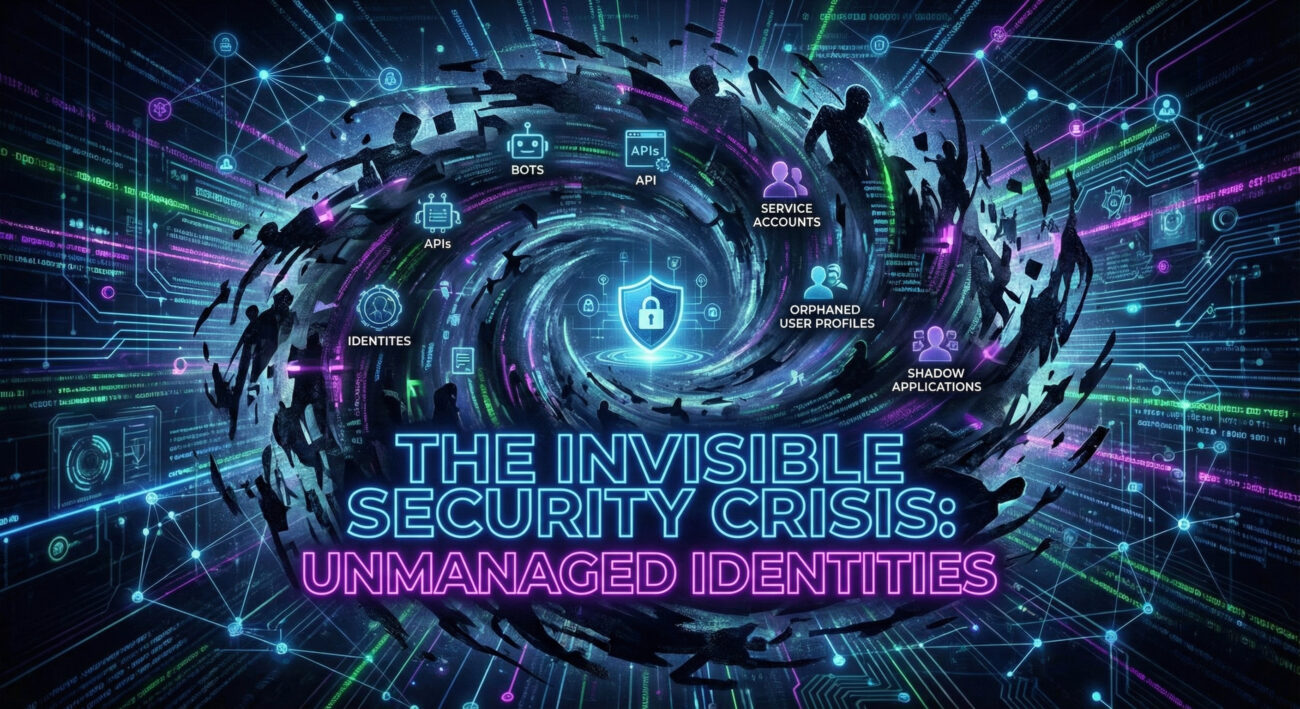
In the vast digital universe of your organization, a silent, invisible threat is expanding, Identity Dark Matter. Much like the cosmological dark matter that makes up most of the universe’s mass yet remains undetectable by telescopes, this cybersecurity phenomenon refers to the sprawling collection of unmanaged, unmonitored, and often forgotten digital identities. These include dormant service accounts, orphaned credentials, stale user profiles, and undocumented API keys that exist outside the purview of your Identity and Access Management (IAM) systems.
VS Code Forks Recommend Missing Extensions, Creating Supply Chain Risk in Open VSX
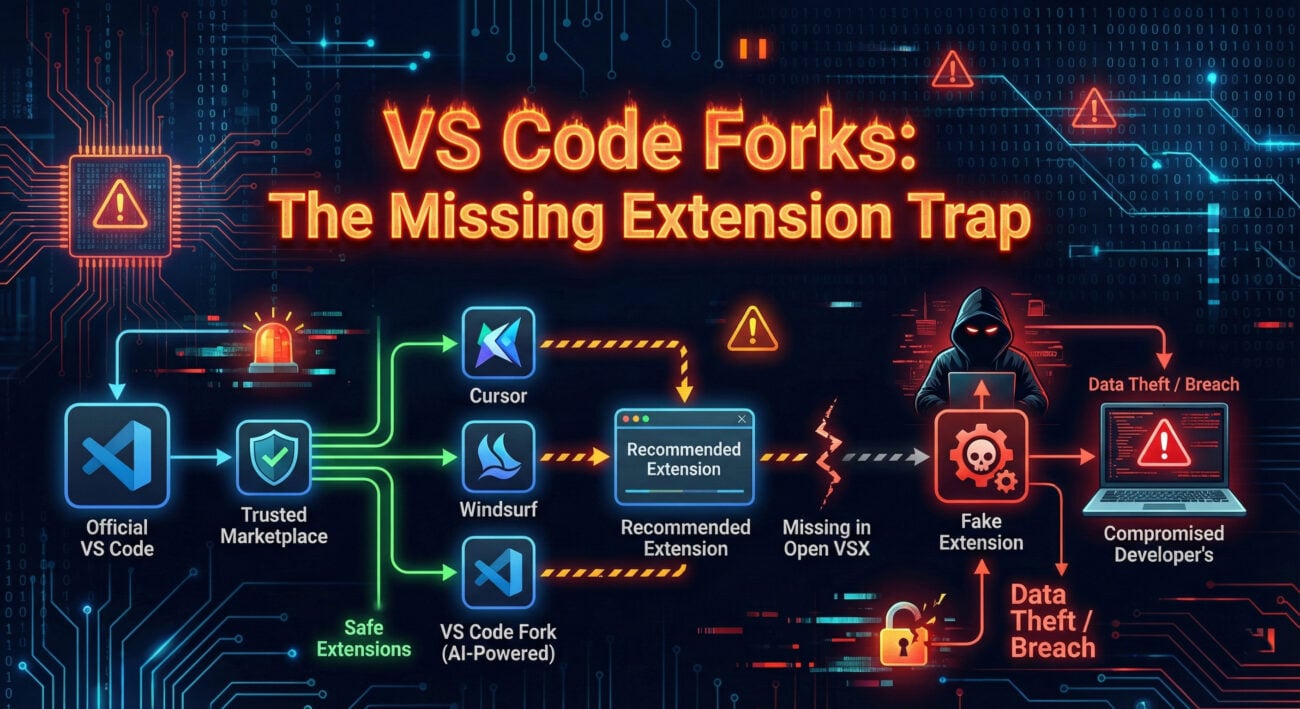
Your Visual Studio Code editor, the very tool you use to build secure applications, has become a prime target for sophisticated cyber attacks. A critical vulnerability in the VS Code extension security ecosystem allows malicious actors to distribute weaponized extensions through forked repositories, bypassing conventional security checks. This isn’t just theoretical, thousands of developers have already been exposed to this supply chain attack vector.
The core issue lies in how VS Code’s extension recommendation system can sometimes suggest forked versions of popular extensions. These forked extensions appear legitimate but contain hidden malware designed to steal credentials, exfiltrate source code, or establish persistent backdoors in development environments. Understanding this threat is crucial for every developer, from beginners to seasoned professionals, because your code editor has become the new attack surface.
New n8n Vulnerability (9.9 CVSS) Lets Authenticated Users Execute System Commands
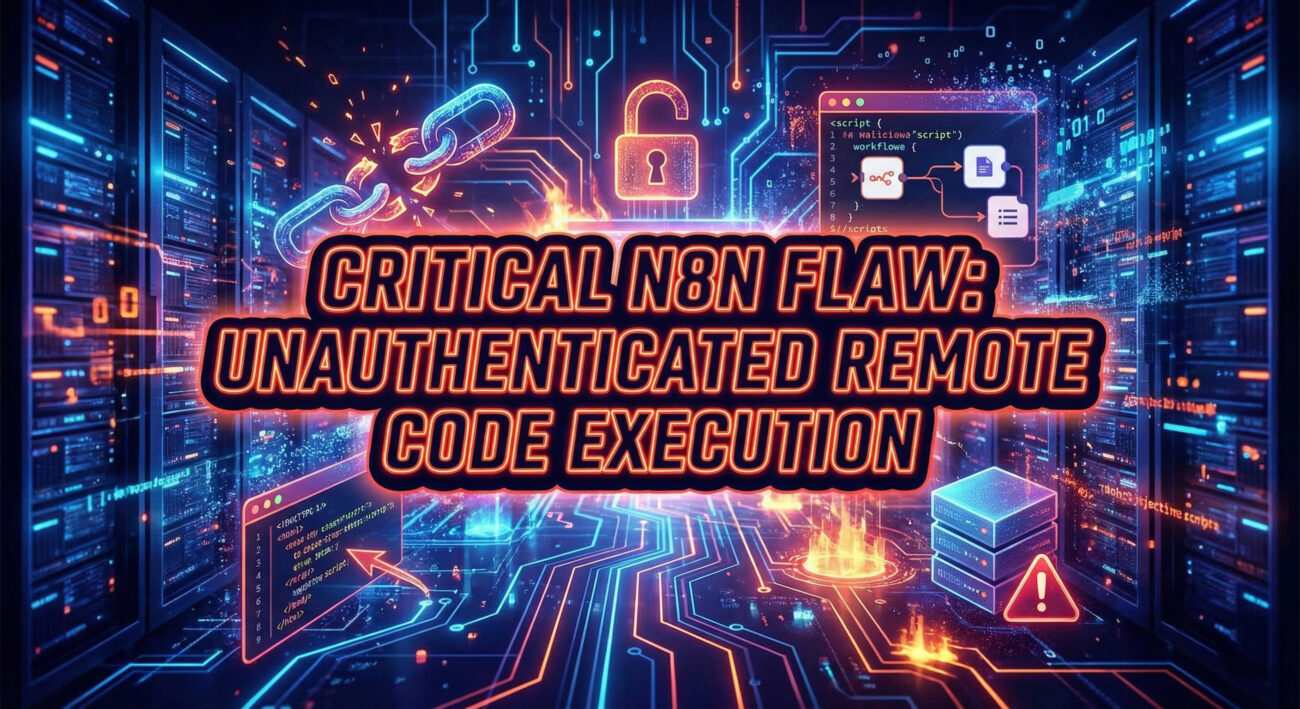
In the world of workflow automation, a critical security flaw can transform a productivity engine into a gateway for attackers. The recent discovery of CVE-2025-68668, a n8n vulnerability with a staggering CVSS score of 9.9, serves as a stark reminder of this reality. This flaw, affecting versions 1.0.0 through 1.x, allows any authenticated user with workflow edit permissions to escape the Python sandbox and execute arbitrary system commands on the host server.
Critical AdonisJS Bodyparser Flaw (CVSS 9.2) Enables Arbitrary File Write on Servers
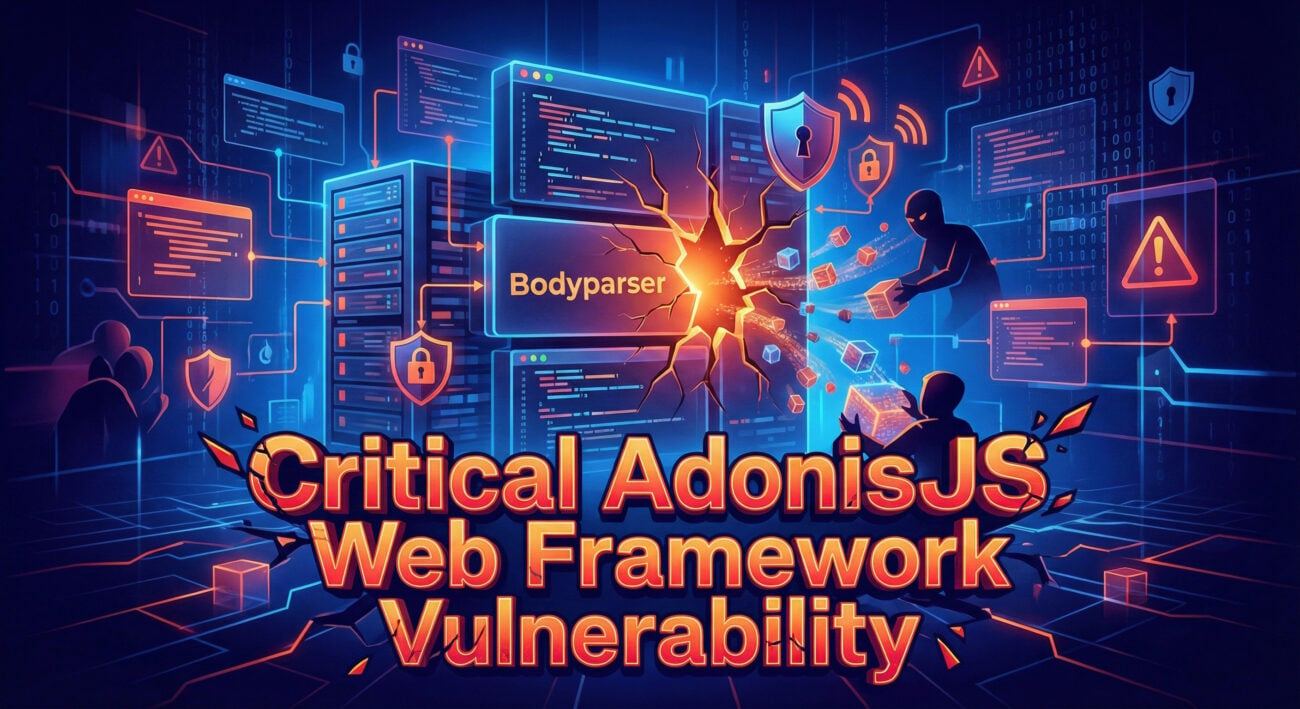
A critical security flaw designated as CVE-2025-2009 (CVSS Score: 9.8) has been discovered in the BodyParser middleware of the AdonisJS Node.js framework. This vulnerability allows attackers to perform prototype pollution through specially crafted HTTP requests, which can be chained to achieve Remote Code Execution (RCE) on vulnerable servers. This comprehensive guide breaks down the technical exploit mechanics and provides actionable defense strategies.
Russia-Aligned Hackers Abuse Viber to Target Ukrainian Military and Government

In January 2026, cybersecurity researchers uncovered a sophisticated attack campaign where the Russia-aligned threat actor UAC-0184 (Hive0156) successfully breached Ukrainian military and government systems. Their primary weapon wasn’t a novel malware strain, but the clever abuse of a trusted communication platform: Viber. This Viber messaging attack represents a significant shift in cyber-espionage tactics, moving beyond email to exploit the inherent trust in personal and professional messaging apps.
Kimwolf Android Botnet Infects Over 2 Million Devices via Exposed ADB and Proxy Networks
In early 2026, the cybersecurity community was alerted to one of the most pervasive mobile threats in recent memory: the Kimwolf Android botnet. This sophisticated malware has infected over two million Android devices, transforming them into weapons for Distributed Denial-of-Service (DDoS) attacks, credential stuffing, and a lucrative residential proxy service. Unlike typical malware that relies on user interaction, Kimwolf exploits a technical misconfiguration, the exposed Android Debug Bridge (ADB) interface, often found on non-standard Android devices like smart TVs and set-top boxes.
Bitfinex Hack Convict Ilya Lichtenstein Released Early Under U.S. First Step Act

The 2016 Bitfinex hack remains one of the most instructive breaches in cryptocurrency history. While the recent early release of convict Ilya Lichtenstein under the First Step Act brings the story back into the news, for cybersecurity professionals, the real headline is the timeless security lessons it teaches. This analysis moves beyond the headlines to dissect the technical attack vectors, the procedural failures, and extracts a clear, actionable defense framework you can apply today. Understanding these Bitfinex hack lessons is crucial for anyone responsible for safeguarding digital assets.
New VVS Stealer Malware Targets Discord Accounts via Obfuscated Python Code

In the ever-evolving landscape of cyber threats, a new and particularly insidious malware named VVS Stealer has emerged, setting its sights on one of the world’s most popular communication platforms: Discord. This isn’t just another piece of nuisance software; it’s a sophisticated information-hacker’s tool designed to vacuum up your digital life, from passwords and authentication tokens to precious cryptocurrency wallets. For cybersecurity professionals, students, and beginners alike, understanding this threat is the first critical step in building an effective defense.
Transparent Tribe Deploys New RAT Campaigns on Indian Government and Academia

In the ever-evolving landscape of cyber threats, few actors are as persistent and regionally focused as Transparent Tribe (APT36). Their latest campaign unveils a sophisticated new Android Remote Access Trojan (RAT), marking a significant escalation in mobile-targeted espionage. This guide breaks down this complex attack into understandable concepts, providing a clear roadmap for beginners in cybersecurity to comprehend, detect, and defend against such malware.


















































