APT28 Weaponizes Microsoft Office CVE-2026-21509: A Deep Dive into Operation Neusploit
🔍 Executive Summary
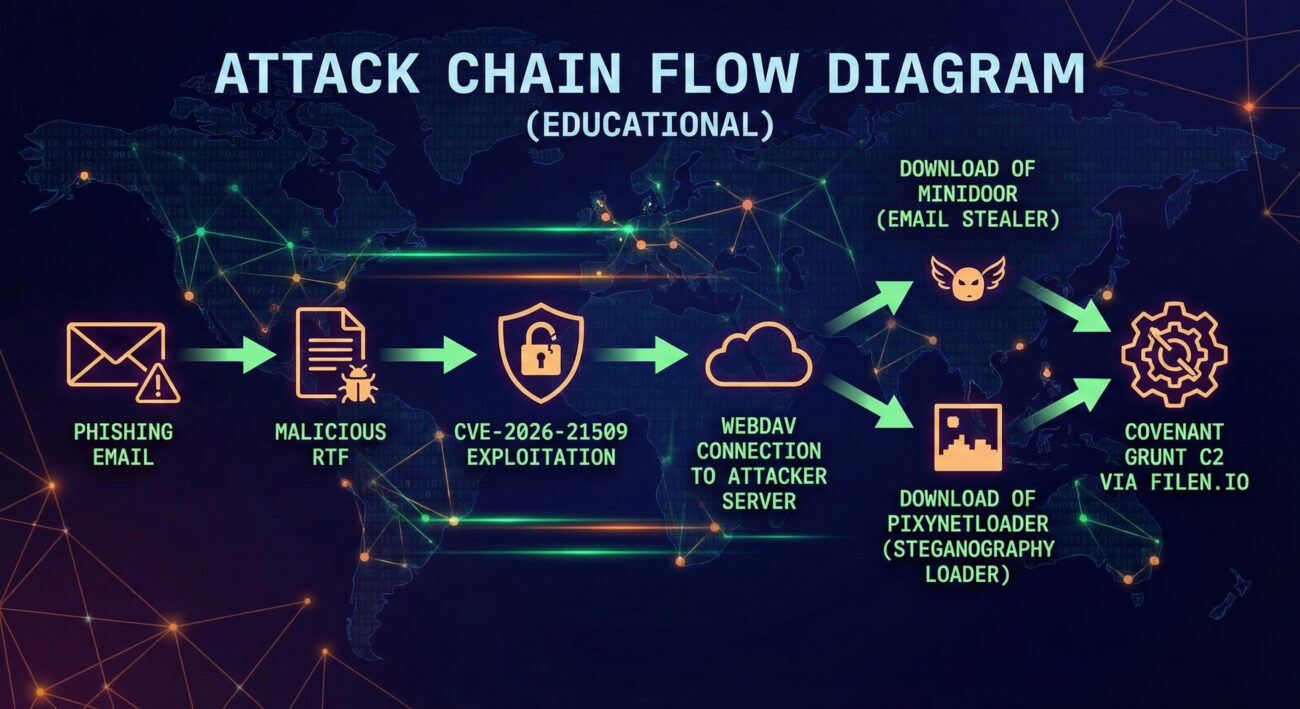
In late January 2026, the Russia-linked threat group APT28 (also known as Fancy Bear, UAC-0001) began exploiting a Microsoft Office zero-day vulnerability (CVE-2026-21509) in highly targeted espionage operations. Dubbed “Operation Neusploit” by Zscaler ThreatLabz, the campaign focuses on government and military entities in Ukraine, Slovakia, Romania, and later expanded to Poland, Turkey, and the UAE. The attackers use weaponized RTF documents that exploit CVE-2026-21509 to deliver two distinct malware families: MiniDoor (an email stealer) and PixyNetLoader (which deploys the COVENANT Grunt implant). This post breaks down the entire attack chain, maps it to MITRE ATT&CK techniques, and provides actionable steps for defenders.
🌍 Real-World Scenario: How the Attack Unfolds
APT28 crafted phishing emails with geopolitical themes, such as transnational weapons smuggling, military training programs, and meteorological emergencies, to lure victims. The emails contained malicious RTF files that, when opened in vulnerable versions of Microsoft Office, automatically triggered CVE-2026-21509 without any user interaction (no macros required).
To evade detection, the threat actors employed server-side evasion: the malicious payload was only served if the request originated from a targeted geographic region (Ukraine, Slovakia, Romania) and contained the correct HTTP User-Agent header. This ensured sandboxes and security researchers outside the target zone received benign content.
According to CERT-UA, more than 60 email addresses within central executive authorities of Ukraine were targeted. Metadata from one lure document showed it was created just one day after Microsoft’s public disclosure, highlighting how rapidly APT28 weaponizes new vulnerabilities.
⚙️ Technical Deep Dive: Step-by-Step Attack Chain
CVE-2026-21509 is a security feature bypass in Microsoft Office (CVSS 7.8). An attacker can send a specially crafted Office file that bypasses protected view or other security mechanisms, allowing code execution. Below is the step-by-step infection process observed by Zscaler, Trellix, and CERT-UA.
Step 1: Spear-Phishing with Malicious RTF
Victims receive an email with a weaponized RTF attachment. The document contains geopolitical lures in localized languages (Romanian, Slovak, Ukrainian, English). When opened, the RTF exploits CVE-2026-21509, triggering a WebDAV connection to an attacker-controlled server.
Step 2: Server-Side Filtering & Payload Delivery
The attacker's server checks the incoming request's User-Agent and IP geolocation. Only if it matches expected targets, the server responds with a malicious DLL (either MiniDoor or PixyNetLoader). Otherwise, it returns a decoy or nothing.
Step 3: Two Parallel Infection Paths
Path A – MiniDoor: A C++ DLL that steals emails from Outlook folders (Inbox, Junk, Drafts) and exfiltrates them to two hardcoded attacker email addresses: ahmeclaw2002@outlook[.]com and ahmeclaw@proton[.]me. MiniDoor is a stripped-down version of NotDoor (aka GONEPOSTAL).
Path B – PixyNetLoader: A more complex loader that extracts two embedded components: a shellcode loader (EhStoreShell.dll) and a PNG image (SplashScreen.png) containing hidden shellcode via steganography. The loader only activates if the parent process is explorer.exe and the machine is not an analysis environment.
Step 4: COVENANT Grunt Deployment
The shellcode from the PNG loads a .NET assembly, a Grunt implant associated with the open-source COVENANT C2 framework. The implant establishes persistence via COM hijacking and communicates with command-and-control servers hosted on legitimate cloud storage (filen[.]io) to blend in with normal traffic. In some cases, a custom backdoor called BEARDSHELL is also deployed.
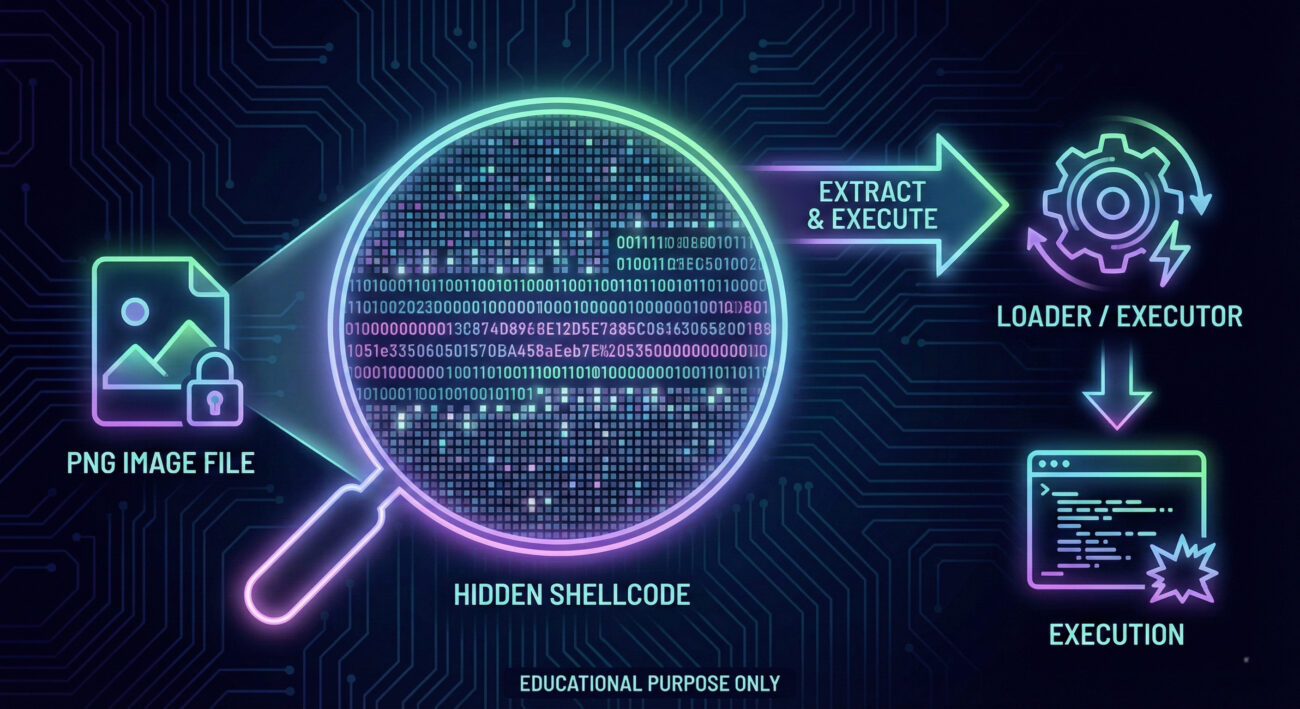
This multi-stage approach, combined with encrypted payloads and in-memory execution, minimizes forensic artifacts and evades traditional signature-based detection.
📊 MITRE ATT&CK Mapping
Understanding the adversary's behavior through the MITRE framework helps defenders build better detections. Here are the key tactics and techniques used in this campaign:
| Tactic | Technique ID | Technique Name | Context |
|---|---|---|---|
| Initial Access | T1566.001 | Spearphishing Attachment | Malicious RTF files delivered via email. |
| Execution | T1204.002 | Malicious File | User opens the RTF, triggering exploitation. |
| Defense Evasion | T1027 | Obfuscated Files or Information | Steganography in PNG, XOR string encryption. |
| Defense Evasion | T1546.015 | Event Triggered Execution: COM Hijacking | Persistence via COM object hijacking. |
| Credential Access | T1114 | Email Collection | MiniDoor steals emails from Outlook. |
| Command and Control | T1071.001 | Web Protocols | C2 over HTTPS using filen.io cloud storage. |
| Exfiltration | T1048 | Exfiltration Over Alternative Protocol | Stolen emails sent to attacker-controlled email addresses. |
For a complete overview of APT28, visit the MITRE ATT&CK group page for APT28.
🔴 Red Team vs 🔵 Blue Team Perspectives
🔴 Red Team (Adversary) View
- Weaponize zero-days quickly, APT28 exploited CVE-2026-21509 within 24-72 hours of disclosure.
- Evade sandboxes with server-side geofencing and User-Agent checks.
- Use living-off-the-land techniques like COM hijacking and cloud storage (filen.io) to avoid detection.
- Target high-value individuals in government and military with tailored lures.
🔵 Blue Team (Defender) View
- Patch aggressively, prioritize Microsoft Office updates, especially CVE-2026-21509.
- Monitor WebDAV connections to untrusted external IPs.
- Inspect email attachments for RTF files with embedded OLE objects.
- Enable AMSI and attack surface reduction rules to block script-based payloads.
🛡️ Defensive Measures & Best Practices
Common Mistakes (Avoid These)
- Delaying patches, assuming zero-days won't be used against you.
- Relying solely on signature-based AV, attackers use steganography and in-memory execution.
- Ignoring cloud storage traffic, filen.io traffic may be whitelisted but can be malicious.
✅ Best Practices
- Apply the February 2026 Microsoft security updates immediately (addresses CVE-2026-21509).
- Block WebDAV outbound to unknown destinations unless explicitly needed.
- Enable enhanced logging for process creation (Event ID 4688) and PowerShell.
- Use application control to prevent unauthorized DLLs from loading.
- Educate users about targeted phishing with geopolitical themes.
For more detailed hardening guidance, see Microsoft's official CVE-2026-21509 advisory and the Trellix deep-dive on BEARDSHELL.
❓ Frequently Asked Questions
Is CVE-2026-21509 being exploited in the wild?
Yes. Multiple security firms (Zscaler, Trellix, CERT-UA) have confirmed active exploitation by APT28 targeting Eastern European and NATO-aligned countries.
Do I need to do anything if I have automatic updates enabled?
Automatic updates should deploy the patch, but verify that your Office installation is up-to-date. Also consider the additional hardening steps above.
What is COM hijacking and how can I detect it?
Attackers modify Registry keys (e.g., HKCU\Software\Classes\CLSID) to execute malicious code when a legitimate application loads a COM object. Monitor Registry changes and use Sysmon Event ID 13 for Registry value modifications.
How can I detect steganography in images?
Detection is difficult, but you can monitor for unusual processes (like explorer.exe) that suddenly load image files and then make network connections. Endpoint detection and response (EDR) tools can flag such anomalies.
🎯 Key Takeaways
- APT28 continues to demonstrate rapid weaponization of Microsoft Office vulnerabilities.
- The attack chain is multi-layered: from RTF exploitation to steganography and COM hijacking.
- Patch management, application control, and behavior monitoring are critical defenses.
- Threat actors use legitimate cloud services (filen.io) to blend in with normal traffic.
- Understanding MITRE ATT&CK helps build better detection and response playbooks.
📢 Call to Action
Now that you understand the inner workings of this sophisticated APT28 campaign, take action:
- Check your Microsoft Office version and ensure it is patched for CVE-2026-21509.
- Review your email gateway logs for suspicious RTF attachments sent in January-February 2026.
- Share this post with your security team and conduct a threat-hunting exercise using the MITRE techniques listed above.
- Subscribe to our newsletter for the latest cybersecurity education content.
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































