Ransomware Leader Hunted Internationally via EU, INTERPOL Alerts
Key Leader Arrest Sparks Security Insights Explained Simply
In a significant blow to one of the most aggressive ransomware groups, authorities recently apprehended a key leader of the Black Basta cybercrime syndicate. This development offers a rare glimpse into the operational structure of these digital extortion rings and provides critical lessons for defenders. This analysis breaks down the Black Basta ransomware operation, maps its tactics to the MITRE ATT&CK framework, and provides actionable guidance for cybersecurity professionals and beginners alike to understand and counter this pervasive threat.
Table of Contents
- Executive Summary: The Fall of a Ransomware Kingpin
- What is Black Basta Ransomware?
- The Attack Chain: MITRE ATT&CK Techniques in Action
- Real-World Scenario: Anatomy of a Black Basta Breach
- Red Team vs. Blue Team: Attacker vs. Defender Mindset
- Common Mistakes & Best Practices for Defense
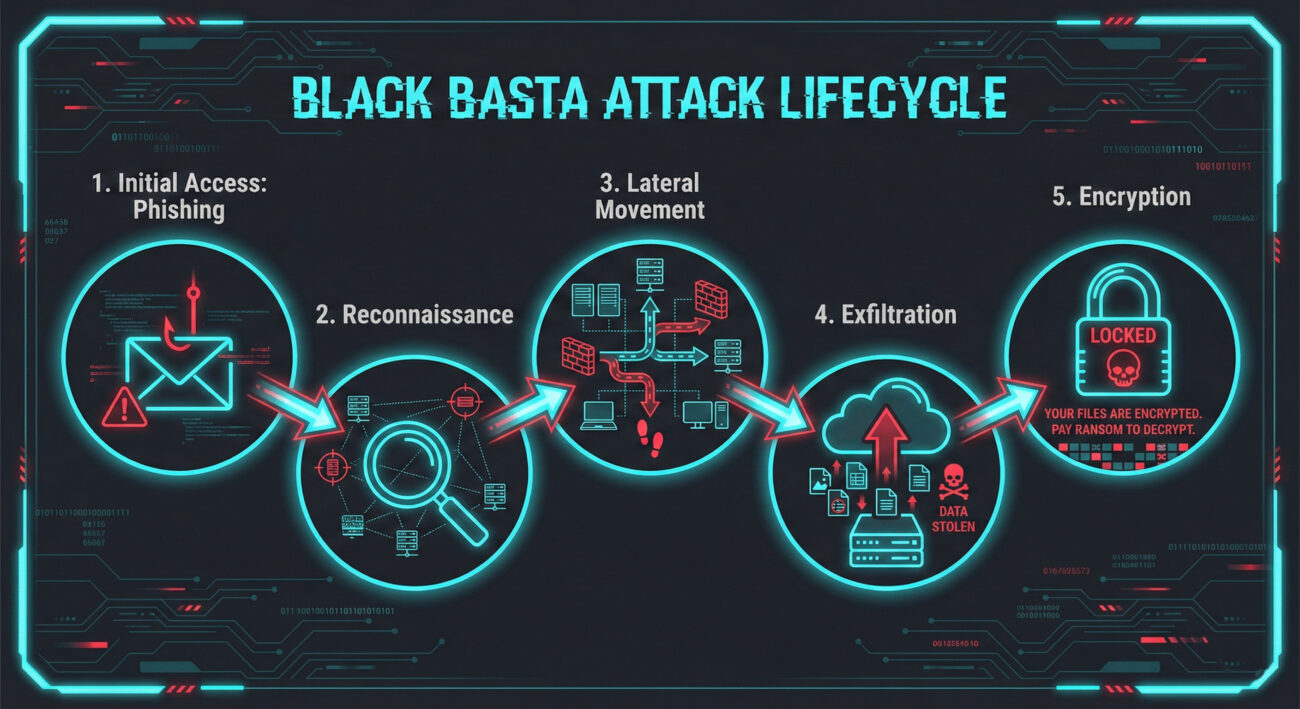
- Visual Breakdown: The Black Basta Attack Lifecycle
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Fortify Your Defenses
Executive Summary: The Fall of a Ransomware Kingpin
The arrest represents a major victory for international law enforcement, disrupting a group responsible for extorting hundreds of millions from global enterprises. Black Basta operates as a Ransomware-as-a-Service (RaaS) model, where developers create the malware and "affiliates" carry out the attacks, sharing profits. This arrest targeted a high-level figure involved in recruiting affiliates and laundering cryptocurrency payments, highlighting the business-like structure of modern cybercrime.
For cybersecurity teams, this event underscores the importance of understanding not just the malware's code, but the human and procedural elements behind the threat. Defense must evolve beyond technical controls to include intelligence gathering, robust identity management, and preparation for the "double extortion" tactic, stealing data before encrypting it.
What is Black Basta Ransomware?
Emerging in early 2022, Black Basta quickly established itself as a top-tier ransomware threat. It is written in C++ and primarily targets Windows systems, though a Linux variant also exists for VMware ESXi servers. The group is notorious for its "double extortion" model:
- Data Theft: Exfiltrate sensitive data from the victim's network.
- Encryption: Deploy ransomware to encrypt files, crippling operations.
- Extortion: Demand separate payments for the decryption key and a promise not to leak the stolen data.
Their public-facing "shame site" lists victims who refuse to pay, increasing pressure. The group's efficiency and aggression have been linked to members from the now-defunct Conti and REvil groups, suggesting a high level of sophistication.
The Attack Chain: MITRE ATT&CK Techniques in Action
Understanding Black Basta's methods through the MITRE ATT&CK framework is crucial for building effective defenses. Here are their core tactics and techniques:
| MITRE ATT&CK Tactic | Specific Technique (ID) | How Black Basta Uses It |
|---|---|---|
| Initial Access | Phishing (T1566) Valid Accounts (T1078) |
Uses sophisticated spear-phishing emails with malicious QakBot attachments or exploits known vulnerabilities in public-facing applications (like VPNs) to gain a foothold. Often purchases stolen corporate credentials from initial access brokers. |
| Execution | Command and Scripting Interpreter (T1059) User Execution (T1204) |
Initial payloads (e.g., QakBot) execute PowerShell or CMD commands to download the main ransomware binary. Users are tricked into enabling macros or running disguised installers. |
| Persistence & Lateral Movement | Exploitation of Remote Services (T1210) Pass the Hash (T1550.002) |
Uses tools like Cobalt Strike and Mimikatz to steal credentials and move laterally across the network. Creates new local/domain admin accounts to maintain access. |
| Defense Evasion | Impair Defenses (T1562) File and Directory Permissions Modification (T1222) |
Disables Windows Defender, antivirus software, and deletes volume shadow copies (vssadmin.exe delete shadows /all /quiet) to prevent file recovery. Uses living-off-the-land binaries (LoLBins) to blend in. |
| Impact | Data Encrypted for Impact (T1486) Data Destruction (T1485) |
Deploys the final ransomware payload, encrypting files with a strong algorithm and appending the .basta extension. Exfiltrates data prior to encryption for double extortion. |
Real-World Scenario: Anatomy of a Black Basta Breach
Let's walk through a typical attack sequence, based on incident reports from cybersecurity firms like CISA and SentinelOne.
Step 1: Initial Compromise via Phishing
An employee in the finance department receives a tailored email pretending to be a vendor invoice. The attachment is a weaponized Excel document. When opened, it prompts the user to "Enable Content," executing a macro that drops the QakBot malware.
Step 2: Establishing Foothold and Reconnaissance
QakBot establishes communication with its command-and-control (C2) server. It then injects itself into running processes, harvests email threads for further phishing, and begins basic reconnaissance of the network, looking for domain controllers and file servers.
Step 3: Lateral Movement and Privilege Escalation
Using stolen credentials and exploits like CVE-2022-30190 (Follina), the attackers move laterally. They deploy Cobalt Strike beacons and use Mimikatz to dump LSASS memory, obtaining admin credentials.
Step 4: Data Exfiltration and Preparation
The attackers identify and exfiltrate sensitive data (financial records, PII, intellectual property) to cloud storage using tools like Rclone or MegaSync. Concurrently, they disable security software and delete backups.
Step 5: Ransomware Deployment and Extortion
The final Black Basta payload is deployed across the network, often via Group Policy. Files are encrypted. A ransom note (README.txt) appears on every desktop, directing the victim to a Tor negotiation site where they are threatened with public data leakage if the ransom isn't paid.
Red Team vs. Blue Team: Attacker vs. Defender Mindset
Red Team (Threat Actor View)
Goals: Maximize financial gain, maintain operational stealth, and achieve total network control.
- Initial Access: Prefer low-effort, high-yield methods like purchased credentials or widespread phishing.
- Tooling: Use legitimate admin tools (PsExec, RDP) and commercial pen-testing frameworks (Cobalt Strike) to avoid detection.
- Critical Action: Disable defenses and delete backups before deploying ransomware to ensure payment is the only recovery option.
- Pressure Point: Leverage stolen data as a secondary, often more powerful, lever than encryption alone.
Blue Team (Defender View)
Goals: Detect intrusion early, contain lateral movement, protect critical assets, and ensure recoverability.
- Initial Access Defense: Implement strong phishing filters, enforce Multi-Factor Authentication (MFA) everywhere, and patch public-facing apps promptly.
- Detection: Monitor for unusual use of administrative tools (e.g., PsExec from a user's workstation), abnormal network flows to cloud storage, and attempts to disable security services.
- Critical Action: Maintain immutable, off-site backups that are regularly tested for restoration.
- Incident Response: Have a practiced plan that includes communication, legal, and decision-making protocols for a ransomware event.
Common Mistakes & Best Practices for Defense
Common Mistakes That Enable Attackers
- Lack of Multi-Factor Authentication (MFA): Single-factor passwords are trivial for attackers to compromise via phishing or credential stuffing.
- Overprovisioned User Permissions: Standard users with local admin rights or excessive network access allow easy lateral movement.
- Unpatched and Outdated Software: Failure to apply security patches for known vulnerabilities provides an open door.
- Insufficient Network Segmentation: A flat network allows ransomware to spread from an initial endpoint to critical servers unimpeded.
- Untested Backups: Assuming backups work without regular restoration tests is a recipe for disaster during an actual incident.
Best Practices for a Resilient Defense
- Enforce Phishing-Resistant MFA: Use hardware security keys or authenticator apps, especially for all remote access and administrative accounts.
- Implement the Principle of Least Privilege (PoLP): Regularly audit user permissions and remove local admin rights. Use just-in-time administrative access.
- Prioritize Patch Management: Automate the patching process for operating systems and all applications, prioritizing critical vulnerabilities.
- Segment Your Network: Create network zones (e.g., user, server, sensitive data) and control traffic between them with firewalls.
- Adopt a 3-2-1 Backup Strategy: Keep 3 copies of data, on 2 different media, with 1 copy stored off-site and offline/immutable. Test restores quarterly.
- Enable Robust Logging and Monitoring: Send logs to a centralized SIEM. Create alerts for suspicious activities like mass file encryption or vssadmin deletion commands.
- Conduct Regular Security Awareness Training: Teach employees to recognize and report phishing attempts and suspicious behavior.
Frequently Asked Questions (FAQ)
Q: Should my organization pay the ransom if hit by Black Basta?
A: Law enforcement and cybersecurity agencies universally advise against paying. Payment funds future criminal activity and does not guarantee data recovery or that data won't be leaked later. The only guaranteed recovery path is from secure, offline backups.
Q: How is Black Basta related to other ransomware groups?
A: Evidence suggests Black Basta evolved from members of the Conti and REvil cartels. It shares similar code, tactics, and infrastructure, representing a "rebranding" or splinter group, a common practice to evade law enforcement focus after a major takedown.
Q: As a beginner, what's the single most important thing I can do to protect against ransomware?
A: Implement and enforce Multi-Factor Authentication (MFA) on all accounts, especially email and remote access. This simple step blocks the vast majority of credential-based attacks that lead to ransomware.
Q: Are there any free decryptors for Black Basta?
A: Currently, there is no publicly available, reliable decryptor for recent versions of Black Basta. This reinforces the need for prevention and backups. Stay updated via resources like the No More Ransom project.
Key Takeaways
- Arrests Disrupt But Don't Eliminate: The arrest of a key leader is a victory, but the RaaS model ensures the threat persists. Continuous vigilance is required.
- Defense is Multi-Layered: No single tool stops ransomware. Combine MFA, least privilege, patching, segmentation, and backups.
- Assume Breach, Focus on Detection & Response: Modern defense assumes attackers will get in. The goal is to detect their movement quickly and contain the incident before the ransomware is deployed.
- Human Element is Critical: Both as the weakest link (phishing) and the strongest defense (trained staff). Invest in security awareness.
- Prepare for the Inevitable: Have a tested incident response and business continuity plan. Know who to call (legal, forensics, PR) and what decisions need to be made before a crisis hits.
Call to Action: Fortify Your Defenses Today
The Black Basta ransomware saga is a stark reminder of the evolving cyber threat landscape. Don't wait for an attack to test your resilience. Take these steps this week:
- Audit MFA Coverage: Ensure it's enabled on all VPN, email, and critical business applications.
- Test Your Backups: Pick a critical server or dataset and perform a full restoration drill.
- Review Your Incident Response Plan: If you don't have one, draft a basic "first 24 hours" checklist.
For further learning, explore these essential resources:
- CISA's Stop Ransomware Guide - Comprehensive U.S. government resource.
- MITRE ATT&CK® Framework - The knowledge base of adversary tactics.
- NIST Cybersecurity Framework - A proven risk management framework.
Share this knowledge. Forward this article to your colleagues and start a conversation about improving your organization's cyber posture. Defense is a team sport.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































