Claude AI Cybersecurity Assistant
A Game-Changer for Threat Analysis Explained Simply
The cybersecurity landscape is undergoing a seismic shift. The volume and sophistication of attacks are overwhelming human analysts. Enter Anthropic's Claude AI, a specialized secure assistant designed not to replace cybersecurity professionals, but to radically augment their capabilities. This guide dives deep into how this AI cybersecurity assistant works, its connection to frameworks like MITRE ATT&CK, and how both red teams and blue teams can leverage it.
Table of Contents
- Executive Summary: The AI-Augmented Defender
- How It Works: Inside the AI Cybersecurity Assistant
- The MITRE ATT&CK Connection: Automating Threat Intelligence
- Real-World Scenarios & Use Cases
- Red Team vs. Blue Team: A Dual Perspective
- Implementation Framework: Integrating AI into Your SOC
- Common Mistakes & Best Practices
- Visual Breakdown: The AI-Assisted Analysis Workflow
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: The Future is Assisted
Executive Summary: The AI-Augmented Defender
Anthropic's launch of Claude as a specialized AI cybersecurity assistant marks a pivotal move from general-purpose chatbots to domain-specific, secure AI partners. Unlike tools that can hallucinate or produce risky code, this assistant is constrained and trained to prioritize security context, accuracy, and safety. Its core function is to act as a force multiplier in Security Operations Centers (SOCs), sifting through petabytes of logs, linking isolated events to known adversary behaviors in the MITRE ATT&CK framework, and drafting clear, actionable reports, all at machine speed.
How It Works: Inside the AI Cybersecurity Assistant
This isn't magic; it's applied machine learning with a security-first constitution. The assistant is fine-tuned on a massive corpus of cybersecurity data: threat reports, malware analyses, CVE descriptions, and, critically, the entire MITRE ATT&CK knowledge base.
The Technical Perspective: From Prompt to Actionable Insight
When an analyst provides a prompt, like a suspicious PowerShell command or a snippet of a phishing email, the assistant performs a multi-step reasoning process:
Step 1: Contextual Ingestion & Deconstruction
The AI parses the input, identifying key entities: file paths, registry keys, IP addresses, URLs, code syntax, and natural language descriptions of activity.
Step 2: Pattern Matching Against Known TTPs
It cross-references these entities against its internal model of adversary Tactics, Techniques, and Procedures (TTPs). For example, a command to disable Windows Defender maps directly to MITRE ATT&CK T1562.001: Impair Defenses – Disable or Modify Tools.
Step 3: Hypothesis Generation & Evidence Linking
The AI doesn't just name a technique; it explains the "why." It might say, "This technique (T1562.001) is commonly used by ransomware actors like LockBit during the Execution phase to operate without detection before file encryption."
Step 4: Actionable Output Generation
Finally, it produces structured output: the mapped MITRE technique, confidence level, recommended investigative queries (e.g., Sigma or Splunk rules), and hardening steps.
This process turns a single indicator into a narrative of the potential attack, saving hours of manual research.
The MITRE ATT&CK Connection: Automating Threat Intelligence
The MITRE ATT&CK framework is the common language of cybersecurity. A key superpower of this AI cybersecurity assistant is its ability to automate the mapping of observed activity to this framework.
Practical Example: Decoding a Phishing Campaign
Imagine a user reports a sophisticated phishing email that bypassed filters. An analyst can feed the email body, headers, and attached file hash to the assistant.
- Assistant Input (Analyst Prompt): "Analyze this email: 'Urgent: Invoice Overdue' with a link to hxxps://malicious-download[.]com/invoice.zip. The zip contains a file 'Invoice.exe' with SHA-256 hash abc123...".
- Assistant Output & MITRE Mapping:
- Tactic: Initial Access. Technique: T1566.001: Phishing – Spearphishing Attachment.
- Tactic: Execution. Technique: T1204.002: User Execution – Malicious File (if the user runs the .exe).
- Linked Intelligence: "Hash abc123 is associated with the IcedID banking trojan, which often leads to ransomware deployment or credential theft."
- Recommended Action: "Block the domain, search for all instances of the file hash, and deploy a mail rule to quarantine emails with this subject pattern."
This instant, contextualized mapping accelerates threat hunting and incident response dramatically.
Real-World Scenarios & Use Cases
The assistant shines across the security workflow. Here’s how it translates to daily tasks:
- Incident Triage: Junior analysts can describe an alert in plain English. The assistant suggests the top 3 most likely TTPs and immediate containment steps.
- Malware Analysis Support: It can explain obfuscated code snippets, suggest what a piece of malware might be attempting (e.g., persistence via scheduled task), and generate YARA rules.
- Report & Playbook Authoring: It drafts sections of incident reports, executive summaries, and detailed secure playbooks based on the techniques identified.
- Security Awareness Training: It generates realistic phishing email examples or quiz questions based on current TTPs for employee training.
Red Team vs. Blue Team: A Dual Perspective
The AI cybersecurity assistant is a dual-use tool. Its value depends entirely on who holds the reins.
The Red Team / Threat Actor View
Adversaries could theoretically use similar AI to:
- Automate Vulnerability Research: Scan code or audit reports to find weak points faster.
- Generate Evasive Malware: Iterate on payload code to bypass signature-based detection.
- Craft Hyper-Targeted Phishing Lures: Use AI to generate convincing, personalized phishing emails (a significant risk).
- Map Attack Paths: Simulate attack chains using the MITRE ATT&CK framework to find the path of least resistance in a target network.
Important Note: Anthropic's Claude is built with safety "guardrails" to refuse generating explicitly malicious content, but open-source or maliciously fine-tuned models may not have such constraints.
The Blue Team / Defender View
Defenders leverage the assistant to:
- Democratize Expertise: Level up junior analysts by providing expert-level context instantly.
- Accelerate Mean Time to Respond (MTTR): Automate the initial, time-consuming correlation and research phase of an incident.
- Proactive Threat Hunting: Query the assistant with hypotheses ("How might an actor exfiltrate data without triggering our DLP?") to build new detection rules.
- Strengthen Controls: Get tailored recommendations for hardening systems against specific, identified TTPs.
The key defender advantage is scale and speed, turning individual analysts into high-output threat research teams.
Implementation Framework: Integrating AI into Your SOC
Adopting an AI cybersecurity assistant requires strategy, not just a subscription.
| Phase | Key Actions | Success Metrics |
|---|---|---|
| 1. Assessment & Scope | Identify pain points: slow triage, alert fatigue, knowledge gaps. Define clear use cases (e.g., "assist Tier 1 with alert enrichment"). | Clear definition of 2-3 pilot use cases. |
| 2. Pilot & Integration | Run a controlled pilot with a small analyst team. Integrate outputs into ticketing (e.g., Jira, ServiceNow) and SIEM workflows. | Reduction in time spent per initial alert analysis; user satisfaction scores. |
| 3. Training & Refinement | Train analysts on effective prompt engineering (e.g., being specific, providing context). Refine the AI's use based on feedback. | Improved quality and actionability of AI-generated reports. |
| 4. Scale & Evolve | Expand access. Use AI to help build new detection logic and automate routine report generation for compliance. | Increased SOC capacity (alerts handled per analyst); decreased MTTR. |
Common Mistakes & Best Practices
Common Mistakes to Avoid
- Over-Reliance: Treating AI output as absolute truth without human validation. It's an assistant, not an oracle.
- Poor Prompting: Vague prompts ("analyze this") yield vague, useless results.
- Ignoring Data Privacy: Feeding sensitive, uncleared incident data into a public AI model, risking a data breach.
- Skill Erosion: Letting analysts' fundamental investigation skills atrophy because "the AI does it."
Best Practices to Adopt
- Human-in-the-Loop (HITL): Always maintain a senior analyst's review and approval of AI-generated conclusions.
- Context is King: Provide detailed, structured prompts: "Given this [log snippet], what TTP from the Execution tactic is most likely, and what SIEM query would find similar activity?"
- Use On-Prem/Private Instances: For sensitive data, use vendor offerings that guarantee data isolation or on-prem deployments.
- Continuous Training: Use the AI as a training tool to explain complex TTPs to junior staff, strengthening the team's core knowledge.
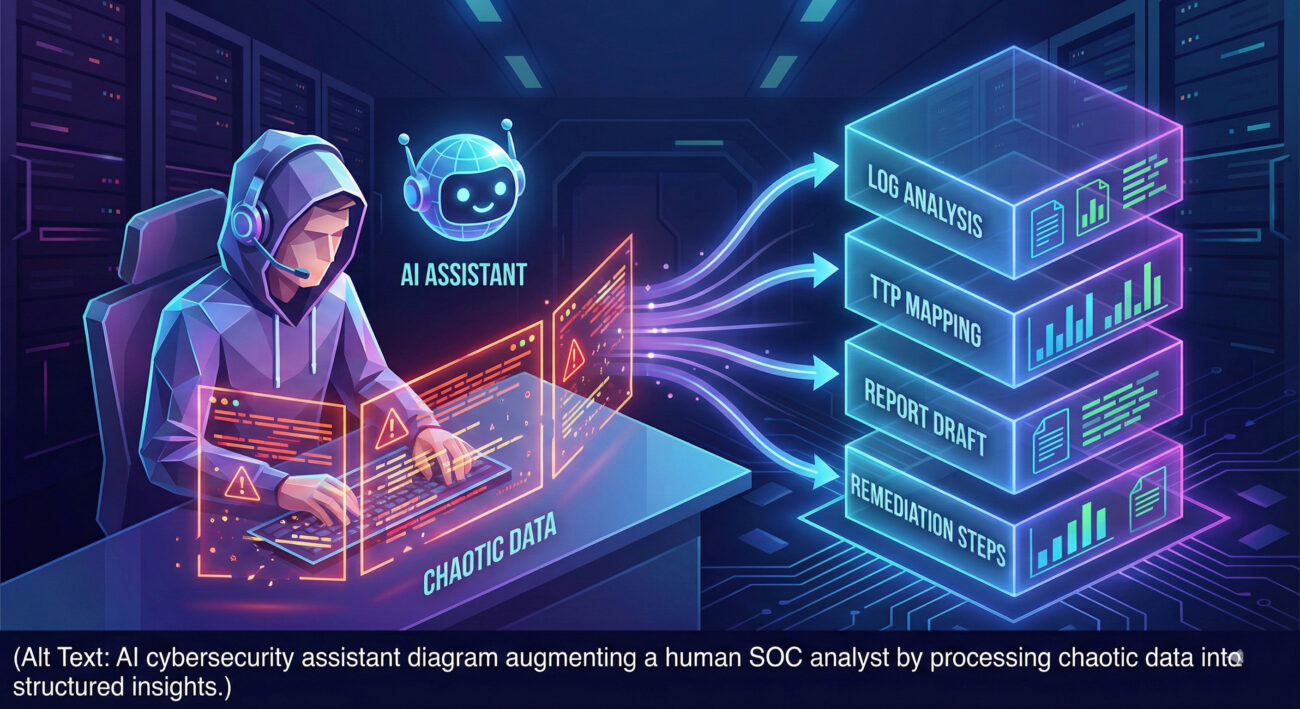
Visual Breakdown: The AI-Assisted Analysis Workflow

Frequently Asked Questions (FAQ)
Q: Is this AI cybersecurity assistant going to replace human analysts?
A: Absolutely not. It's designed to augment and elevate them. It automates the tedious research and correlation, freeing analysts to do what they do best: strategic thinking, complex investigation, and making critical decisions. The future is human-machine teaming.
Q: How accurate and reliable is the MITRE ATT&CK mapping?
A: It's highly accurate for well-documented TTPs but should be treated as a hypothesis. The assistant provides confidence levels and evidence. The analyst must confirm the mapping aligns with all observed data. It's a starting point, not the final verdict.
Q: What about data privacy? Is our incident data safe?
A: This is crucial. When evaluating an AI assistant, you must choose a deployment model that fits your risk tolerance. Opt for enterprise versions that guarantee data is not used for training and is encrypted in transit and at rest. Never feed highly sensitive data into a public, free chatbot.
Q: As a beginner, how do I start using such a tool effectively?
A: Start with low-risk tasks. Use it to explain security concepts you don't understand. Ask it to summarize long threat reports. Practice by giving it snippets from public breach disclosures and see how it maps them. Focus on learning to craft better prompts, it's a skill in itself.
Key Takeaways
- The AI cybersecurity assistant like Anthropic's Claude is a transformative force multiplier, automating threat intelligence correlation and MITRE ATT&CK mapping.
- Its core value lies in accelerating detection, investigation, and response, drastically reducing MTTR and alleviating analyst burnout.
- It is a dual-use technology: threat actors may use similar AI, making adoption by defenders not just an advantage but a necessity.
- Successful implementation requires a Human-in-the-Loop model, careful data privacy controls, and investment in analyst training on prompt engineering.
- This technology marks the beginning of a new era of augmented cybersecurity, where human expertise is amplified by machine speed and scale.
Call to Action: The Future is Assisted
The evolution from manual analysis to AI-assisted operations is no longer speculative; it's here. To stay ahead of sophisticated adversaries, cybersecurity teams must explore and integrate these tools thoughtfully.
Your next steps:
- Educate Your Team: Share this article and discuss the potential use cases within your organization.
- Experiment Responsibly: Start a pilot with a dedicated tool like Anthropic's Claude for Cybersecurity or explore integrations in platforms like CrowdStrike Falcon or Microsoft Security Copilot.
- Invest in Skills: Encourage your analysts to develop prompt engineering and AI oversight skills. Resources like the MITRE ATT&CK website and SANS Institute blogs are excellent for deepening foundational knowledge.
The goal isn't to create a SOC run by machines, but to build an unbeatable team where human intuition, creativity, and experience are supercharged by an AI cybersecurity assistant. Start building that future today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































