When the Cloud Fails: Protecting Identity Systems from Widespread Outages
- 1. Executive Summary: The Hidden Ripple
- 2. Real-World Scenario: When Booking Systems Go Dark
- 3. Anatomy of Identity Dependency
- 4. MITRE ATT&CK Mapping
- 5. Step-by-Step Resilience Assessment
- 6. Common Mistakes & Best Practices
- 7. Red Team vs Blue Team View
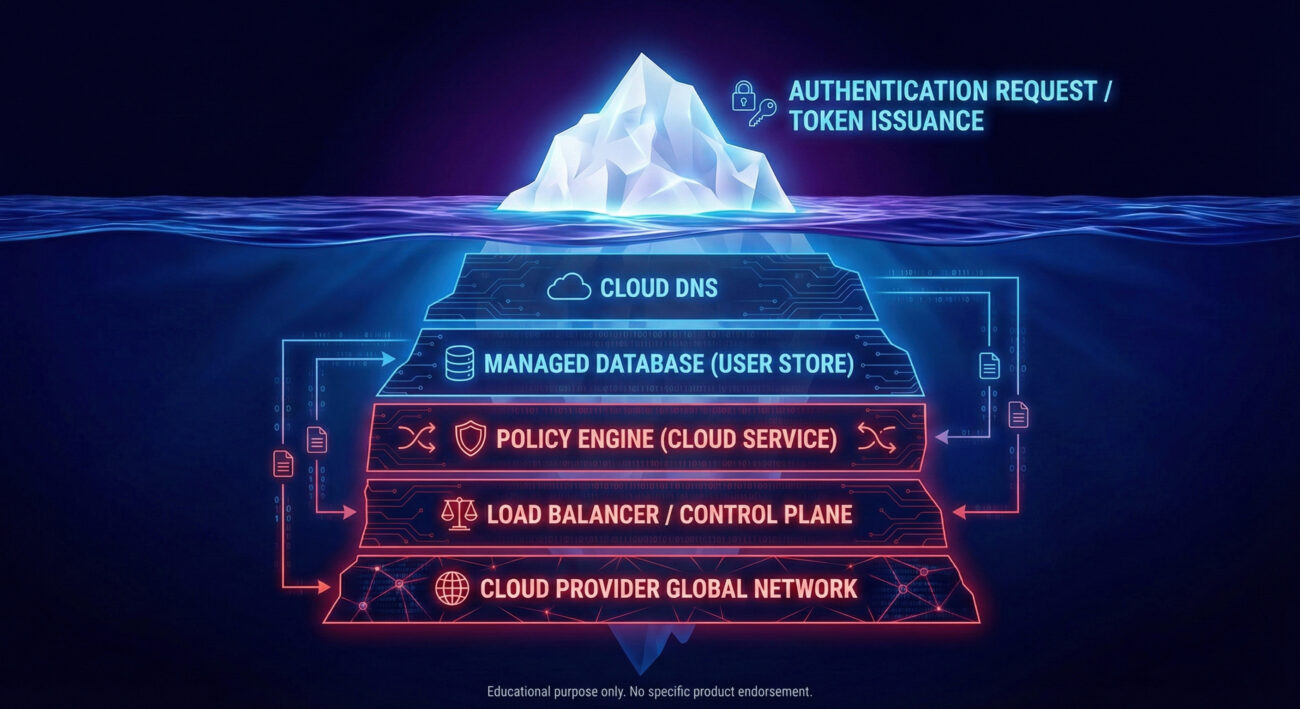
- 8. Visual: Dependency Chain
- 9. Designing for Resilience
- 10. FAQ
- 11. Key Takeaways
🚨 Executive Summary: The Hidden Ripple
When a major cloud provider like AWS, Azure, or Cloudflare suffers an outage, the internet doesn’t just slow down, it fractures. While consumers see a pizza order fail, businesses face a complete identity crisis. Authentication and authorization, the gatekeepers of every system, rely on a fragile chain of cloud dependencies: databases, DNS, control planes, and policy engines. If any link breaks, access collapses.
This article explores the cloud outage identity resilience challenge: why traditional high‑availability fails, how to map dependencies, and practical steps to keep identity systems alive when the cloud goes dark. We’ll also connect these risks to MITRE ATT&CK tactics, so you can think like both attacker and defender.
✈️ Real-World Scenario: When Booking Systems Go Dark
Imagine an airline’s booking platform, a complex mesh of microservices, APIs, and identity checks. During a recent cloud outage, the provider’s managed database for user profiles became unreachable. The identity provider (IdP) itself was still running, but it couldn’t fetch user attributes or session data. Result: every login attempt failed. Passengers couldn’t check in, pilots couldn’t access flight plans, and revenue evaporated.
This isn’t hypothetical. In 2025–2026, multiple high‑profile cloud incidents have shown that identity is the single point of failure. Even with multi‑region failover, if the control plane or a global DNS service goes down, every region tumbles.

🔗 Anatomy of Identity Dependency
Modern identity architectures are deeply woven into cloud infrastructure. Even if your OIDC or SAML provider is “up,” these backend components can break authentication:
- Datastores: User directories, profile attributes, and group memberships (e.g., Azure AD Directory, Amazon Cognito).
- Policy/Authorization data: Dynamic rules (e.g., OPA, AWS Cedar) that decide if a request is allowed.
- Load balancers & control planes: The brain that orchestrates identity traffic.
- DNS: Translates IdP endpoints into IPs, if DNS fails, everything stops.
A single authentication event triggers a cascade: resolve user → fetch attributes → evaluate policies → issue token → validate token at API. Every hop depends on the underlying cloud fabric. When that fabric fails, so does identity.
🎯 MITRE ATT&CK Mapping: Outages as Attack Vectors
Understanding these dependencies helps defenders anticipate how adversaries might exploit availability gaps. Below is a mapping to relevant MITRE ATT&CK tactics and techniques:
| Tactic | Technique ID | Name | Relevance to Cloud Outage |
|---|---|---|---|
| Impact | T1499 | Endpoint Denial of Service | Attackers may trigger resource exhaustion in identity databases, mimicking an outage. |
| Impact | T1498 | Network Denial of Service | DNS or control plane flooding can block identity lookups. |
| Defense Evasion | T1578 | Modify Cloud Compute Infrastructure | Adversaries could alter identity policies or disable redundancy during an outage window. |
| Credential Access | T1556 | Modify Authentication Process | If identity systems are down, attackers might try to bypass authentication altogether. |
While a natural outage isn’t an attack, the effect is identical: denial of access. Resilience planning must account for both accidental and malicious disruptions.
📋 Step-by-Step: Assess Your Identity Resilience
Use this practical guide to evaluate your exposure to cloud‑outage‑induced identity failure.
Step 1: Map Identity Dependencies
Document every external service your identity system touches: cloud provider services (DNS, databases, load balancers), third‑party APIs, and internal microservices. Include both runtime and configuration dependencies.
Step 2: Identify Shared Failure Domains
Look for dependencies that share a single cloud provider, region, or control plane. For example, if your primary and backup IdP both use the same cloud DNS, a DNS outage takes down both.
Step 3: Test “Degraded Mode” Scenarios
Simulate outages of each dependency. Can users still authenticate using cached tokens or attributes? Does authorization fall back to local policies? Measure the blast radius.
Step 4: Implement Graceful Degradation
Design fallback mechanisms: cache user sessions, precompute authorization decisions for critical APIs, and allow read‑only access when identity writes fail. Define what “limited access” means for your business.
Step 5: Multi‑Cloud / Hybrid Contingency
For truly critical identity functions, consider a secondary provider or on‑premises lightweight directory that can operate independently during a major cloud outage. Test failover regularly.
⚠️ Common Mistakes & Best Practices
❌ Mistakes (Red flags)
- Assuming regional failover protects against control‑plane outages.
- Ignoring DNS as a single point of failure for identity endpoints.
- Storing all session data exclusively in a cloud memory store (like ElastiCache) without a fallback.
- Treating identity as a “black box” – not mapping dependencies.
✅ Best Practices (Green)
- Implement caching of user attributes and authorization policies with TTLs.
- Use multiple DNS providers and monitor resolution from different vantage points.
- Design for offline access tokens (e.g., longer‑lived JWTs for critical APIs).
- Conduct chaos engineering experiments that disable identity dependencies.
⚔️ Red Team vs Blue Team: Exploiting & Defending Identity Outages
🔴 Red Team (Adversary) Mindset
- Identify cloud dependencies that, if knocked offline, would block authentication.
- Target shared services (e.g., cloud DNS, control plane) with DDoS or resource exhaustion.
- During an actual cloud outage, attempt to phish users who are desperate to regain access.
- Exploit degraded modes: if caching is enabled, try to poison cache entries.
🔵 Blue Team (Defender) Response
- Monitor cloud provider health dashboards and set alerts for identity‑related services.
- Maintain an emergency “break‑glass” authentication path that uses minimal dependencies.
- Regularly test offline authorization lists and cached attributes.
- Ensure incident response playbooks include “identity unavailable” scenarios.
🧩 Visual Breakdown: The Identity Dependency Iceberg
🏗️ Designing for Resilience: Beyond High Availability
Traditional HA (active‑passive regions) is not enough when the failure is global. Consider these architectural patterns:
- Multi‑cloud identity: Run a secondary IdP on a different cloud provider, with data replication (or a common LDAP backend).
- On‑premises fallback: For extreme scenarios, maintain a lightweight directory service that can authenticate critical users even if the internet is cut.
- Token‑based offline access: Issue short‑lived access tokens that contain enough claims to authorize API calls without contacting the IdP on every request.
- Graceful degradation policies: Define which applications can work in “read‑only” mode when identity writes fail. For example, allow viewing tickets but not purchasing new ones.
These strategies ensure that when the cloud outage hits, your identity systems degrade instead of collapse.
❓ Frequently Asked Questions
Q: Can't we just rely on cloud provider's SLA for identity?
A: SLAs cover uptime of their service, but not the myriad dependencies your identity flow has. An outage in a “different” service (like DNS) can still break authentication. Resilience is your responsibility.
Q: Is multi‑cloud the only answer?
A: Not the only, but it's a strong pattern. You can also use a hybrid model with an on‑premises directory replica. The key is to avoid a single shared failure domain.
Q: How often should we test identity outage scenarios?
A: At least twice a year, and after any major change to your identity infrastructure. Use game days to simulate a cloud DNS or control plane failure.
Q: What's the first step to improve cloud outage identity resilience?
A: Map your dependencies. You can't fix what you don't know. Start with the step‑by‑step guide above.
🔑 Key Takeaways
- Cloud outages cause identity failures even when the IdP itself is running, due to hidden dependencies.
- Traditional HA fails when the shared cloud control plane or global DNS goes down.
- Map your identity dependencies to identify single points of failure.
- Design for degraded operation: caching, offline tokens, and fallback authentication paths.
- Use the MITRE ATT&CK framework to understand how adversaries might exploit availability gaps.
- Regularly test outage scenarios with both red and blue team exercises.
🔒 Ready to harden your identity resilience?
Start with our free dependency‑mapping template and join the Cyber Pulse Academy newsletter for weekly deep dives into identity security and cloud architecture.
👉 Explore more at The Hacker News for real‑time updates, or check MITRE ATT&CK® and AWS Well‑Architected for official guidance.
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































