Credential Harvesting Attack Exposed
How APT28 Targets Global Infrastructure Explained Simply
How APT28's Sophisticated Phishing Campaigns Target Global Energy and Policy Infrastructure
Table of Contents
- Executive Summary: The APT28 Campaign
- How the Credential Harvesting Attack Works
- Mapping to MITRE ATT&CK: The Hacker's Playbook
- A Real-World Attack Scenario: Step-by-Step
- Red Team vs. Blue Team Perspective
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The APT28 Credential Harvesting Campaign
In early 2026, cybersecurity researchers uncovered a sophisticated credential harvesting attack campaign orchestrated by the Russian state-sponsored group APT28, also known as BlueDelta or Fancy Bear. This group, linked to the GRU, has systematically targeted individuals within a Turkish energy and nuclear research agency, a European think tank, and organizations in North Macedonia and Uzbekistan.
The core of this attack involves highly convincing fake login pages that mimic legitimate services like Microsoft Outlook, Google, and Sophos VPN. The campaign's sophistication lies not just in its appearance, but in its post-theft behavior: after stealing credentials, victims are seamlessly redirected to the real service, leaving them unaware of the breach. This analysis will break down this pervasive credential harvesting attack vector, providing a clear understanding for professionals and beginners alike.

How the Credential Harvesting Attack Works: A Technical Breakdown
Understanding the mechanics of this credential harvesting attack is crucial for defense. APT28's method is a multi-stage process designed for maximum deception and minimal detection.
Stage 1: The Bait - Spearphishing with Legitimate Lures
The attack begins with a targeted spearphishing email. Unlike generic spam, these emails contain contextually relevant lures. For example, APT28 used a real PDF publication from the Gulf Research Center about the Iran-Israel war and a climate policy briefing from think tank ECCO. The email contains a shortened URL link.
Stage 2: The Deceptive Redirect & Fake Page
Clicking the link starts a fast-paced redirect chain designed to disorient the victim:
- The victim is first taken to a page on a service like Webhook[.]site that briefly displays the legitimate decoy PDF (for about 2 seconds).
- An instant, automatic redirect then sends the victim to a second Webhook[.]site page hosting a perfect replica of a Microsoft OWA, Google, or Sophos VPN login portal.
The fake page is often hosted on free or disposable infrastructure like InfinityFree, Byet Internet Services, or ngrok. This allows the attackers to quickly set up and tear down malicious pages, making them hard to track.
Stage 3: The Silent Theft & Clean Exit
This is the cleverest part of the attack. The fake page contains hidden JavaScript code that performs two critical actions simultaneously when the victim submits their username and password:
- Credential Exfiltration: The stolen credentials are immediately sent (POST request) to a Webhook endpoint controlled by the hackers.
- Seamless Redirection: The user's browser is instantly redirected to the genuine, legitimate login page for the service they thought they were accessing (e.g., the real Outlook Web App).
From the user's perspective, they simply entered their password and successfully logged in, noticing nothing amiss. This "clean exit" is what makes this credential harvesting attack particularly dangerous and effective.
Mapping to MITRE ATT&CK: The Hacker's Playbook
Frameworks like MITRE ATT&CK help us categorize adversary behavior. The APT28 credential harvesting attack is a textbook example of several techniques working in concert.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How APT28 Applied It |
|---|---|---|
| Initial Access | T1566.002 - Phishing: Spearphishing Link | Sending targeted emails with shortened links to regional and professional lures (energy reports, policy briefs). |
| Credential Access | T1589.001 - Credential Access: Credential Harvesting | Deploying fake OWA, Google, and Sophos VPN login pages to steal usernames and passwords. |
| Collection | T1534 - Internal Spearphishing | Using stolen credentials from one victim to spearphish others within the same organization for lateral movement. |
| Defense Evasion | T1071.001 - Application Layer Protocol: Web Protocols | Using legitimate-looking web services (Webhook.site, InfinityFree) to host malicious content and blend in with normal traffic. |
| Resource Development | T1583.001 - Acquire Infrastructure: Domains | Registering and leveraging free hosting services and dynamic DNS providers for disposable attack infrastructure. |
By understanding this mapped attack sequence, defenders can build more effective detection rules. For instance, monitoring for rapid redirects between unrelated free-hosting domains and legitimate corporate login pages could be a key indicator.
A Real-World Attack Scenario: Step-by-Step
Let's walk through a specific instance from the September 2025 campaign to see how a credential harvesting attack unfolds in real-time from the victim's viewpoint.
Step 1: The Targeted Email Arrives
Ahmet, an analyst at a Turkish energy research institute, receives an email from a seemingly trusted sender. The subject references a recent, relevant industry report on Mediterranean energy policy. The body text is professional and urges him to "review the attached briefing." The "attachment" is actually a shortened link (e.g., bit.ly/xxxx).
Step 2: The Bait is Taken
Curious, Ahmet clicks the link. His browser opens a tab showing a genuine-looking PDF document hosted on Webhook[.]site. He sees it's a real ECCO climate briefing. After just two seconds, the page automatically refreshes.
Step 3: The Trap is Set
The new page looks exactly like his organization's Microsoft Outlook Web Access (OWA) login portal. The URL in the address bar shows "https://secure-login-infinityfree[.]net/owa/" – which looks plausible but is actually a malicious page hosted on free infrastructure. A message states, "Your session has expired. Please re-authenticate."
Step 4: Credentials are Stolen
Ahmet enters his corporate email and password and hits "Sign In." Hidden JavaScript code instantly sends his credentials to an APT28-controlled Webhook endpoint. Simultaneously, his browser is redirected to "https://outlook.office.com" – the real Microsoft login page.
Step 5: The Illusion of Normalcy
Ahmet may be prompted to log in again on the legitimate page (as his credentials weren't actually submitted there). He does so and gains access to his real mailbox. He assumes the first prompt was just a glitch or pre-login screen. He is completely unaware his credentials are now in the hands of APT28 hackers.
Red Team vs. Blue Team Perspective
Red Team (APT28 / Attacker) View
- Objective: Gain initial access to target organizations via valid credentials for espionage.
- Advantages: Uses low-cost, disposable infrastructure that's hard to blacklist. The "clean redirect" greatly reduces victim suspicion and help desk reports.
- Tactics: Heavy reliance on open-source intelligence (OSINT) to craft believable lures for specific sectors (energy, policy). Abuses trust in brand-name services (Microsoft, Google).
- Challenges: Requires continual development of new phishing pages and infrastructure as old ones are discovered. Effectiveness depends entirely on the victim's failure to inspect URLs or use multi-factor authentication (MFA).
Blue Team (Defender) View
- Objective: Detect and prevent credential theft, and contain breach impact.
- Detection Opportunities: Network logs showing connections to known free hosting IPs (InfinityFree, Byet) followed immediately by connections to legitimate cloud services. Email filters flagging shortened URLs in targeted emails.
- Defensive Tactics: Enforcing MFA universally is the single most effective mitigation. Implementing secure email gateways that rewrite or inspect shortened links. User training focused on URL inspection and reporting of re-authentication prompts.
- Key Challenge: Balancing security with usability. The attack exploits normal user behavior (entering passwords on familiar-looking pages). Defenders must build systems that are resilient to this without overburdening users.
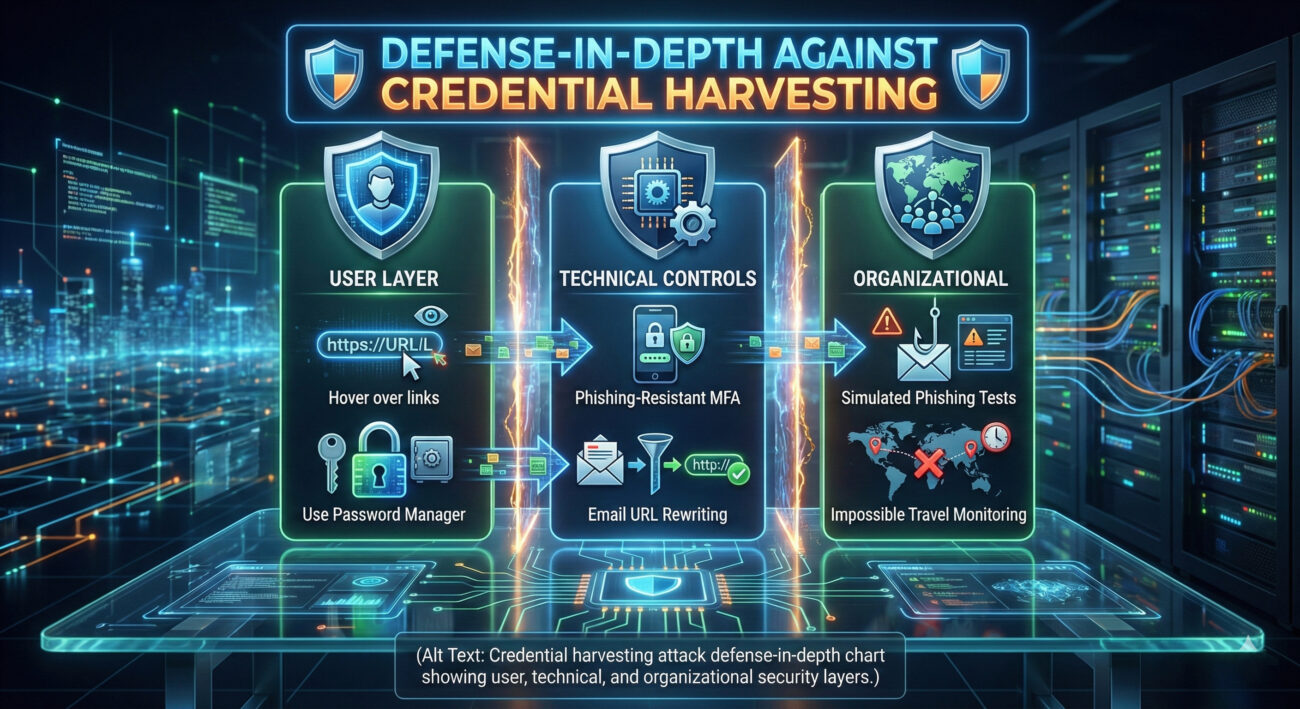
Common Mistakes & Best Practices for Defense
Learning from both victim mistakes and defender successes is key to building resilience against a credential harvesting attack.
❌ Common Mistakes That Enable Attacks
- Clicking Without Hovering: Not hovering over links to preview the actual destination URL before clicking.
- Password Reuse: Using the same password across corporate, personal, and third-party services, amplifying the impact of a single theft.
- Assuming Internal Emails are Safe: APT28 often uses initially stolen credentials to send follow-up phishing emails from compromised internal accounts, which bypasses external email filters.
- Lack of Reporting Culture: Users who experience a "weird login glitch" often don't report it to IT, missing a critical early detection signal.
✅ Best Practices to Stop Credential Theft
- Enforce Phishing-Resistant MFA: Implement Multi-Factor Authentication using FIDO2 security keys or authenticator apps. This makes a stolen password useless on its own. (The #1 most effective defense)
- Implement a Password Manager: Encourage/require the use of password managers. They auto-fill credentials only on the correct, saved domains, preventing entry into fake lookalike sites.
- Deploy Advanced Email Security: Use tools that scan and safely rewrite embedded URLs, perform time-of-click analysis, and flag emails with suspicious sender/reply-to address mismatches.
- Continuous Security Awareness Training: Move beyond annual quizzes to regular, simulated phishing tests and micro-learning modules that teach users to identify sophisticated lures and redirection tricks.
- Monitor for "Impossible Travel" & New Logins: Use Identity Threat Detection and Response (ITDR) tools to flag logins from new devices/locations shortly after the user accessed a suspicious free-hosting domain.
Frequently Asked Questions (FAQ)
Q: Why is this type of credential harvesting attack so effective?
A: Its effectiveness stems from three factors: highly believable targeting (spearphishing), flawless technical execution (perfect clone pages), and the clever psychological trick of the seamless redirect. The victim's confirmation bias ("I got to my real inbox, so all is well") overrides any initial suspicion.
Q: I'm just an individual user, not a big company. Should I be worried?
A: Absolutely. While APT28 targets organizations, the same attack techniques are used by countless cybercriminals against individuals for banking fraud, identity theft, and personal data breaches. The personal best practices listed above (password manager, MFA on personal accounts) are just as critical.
Q: Can a traditional antivirus or firewall stop this attack?
A: Often, no. The malicious page is just HTML/JavaScript hosted on a legitimate, benign web service. No malware is downloaded to the victim's computer, so file-based antivirus is ineffective. Network firewalls see the victim connecting to a standard web service (like InfinityFree) and then to Microsoft, both allowed. This is why behavioral detection (monitoring the sequence of events) and user education are paramount.
Q: Where can I learn more about the MITRE ATT&CK framework mentioned?
A: The official MITRE ATT&CK® website is the definitive source. For practical guidance on defense, the CISA Cybersecurity Best Practices site is an excellent public resource. To understand APT28's historical activities, refer to advisories from the UK's NCSC or the FBI's Cyber Division.
Key Takeaways & Call to Action
The APT28 credential harvesting attack campaign is a stark reminder that even simple techniques, when executed with precision and psychological insight, can threaten critical infrastructure. It exploits the inherent trust we place in familiar login screens and the hurried nature of modern work.
Your Action Plan
- For Everyone: Enable Multi-Factor Authentication (MFA) on every account that offers it, starting with email and financial services. Consider a password manager.
- For Security Professionals: Audit your organization's MFA implementation. Is it phishing-resistant? Review network and email logs for patterns of access to free web hosting services followed by cloud application logins.
- For Leaders & Decision-Makers: Invest in security awareness training that goes beyond compliance. Fund the adoption of modern, integrated secure email gateways and identity protection tools.
- Stay Informed: The threat landscape evolves daily. Follow trusted sources like the The Hacker News for the latest updates on attack vectors.
Cybersecurity is a shared responsibility. By understanding the mechanics of a credential harvesting attack, from its initial spearphishing lure to its silent data exfiltration, we empower ourselves to build stronger defenses, cultivate vigilant habits, and significantly raise the cost for adversaries like APT28.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































