Credentials (T1589.001)
Ultimate Guide to Gather Victim Identity Information - Credentials: Attack & Defense
Gather Victim Identity Information: Credentials is the foundational reconnaissance step where adversaries sleuth for usernames, passwords, API keys, and other authentication secrets before an attack even begins. This guide turns the official MITRE data into an actionable playbook for both red and blue teams.
ATT&CK ID T1589.001
Tactics Reconnaissance
Platforms PRE
Difficulty 🟢 Beginner
Prevalence High
Table of Contents
Understanding Gather Victim Identity Information: Credentials in Simple Terms
Imagine a thief casing a neighborhood not by checking for unlocked windows, but by sifting through recycling bins for bank statements, rummaging through public social media for pet names (common password hints), and even buying old employee directories from a shady source online. They aren't trying to break in yet, they're building a master key ring.
That's precisely what Gather Victim Identity Information: Credentials is in the cyber world. It's the passive, often legal, and alarmingly effective process of collecting the digital "keys" , usernames, email addresses, password hashes, exposed API tokens, or even just common password patterns , that will be used later to pick the lock during active intrusion attempts like Brute Force (T1110) or Valid Accounts (T1078).
The goal isn't immediate compromise, but to dramatically increase the odds of success when the real attack begins. This phase is critical because stolen or guessed credentials are the number one vector for major breaches.
Decoding the Jargon: Key Terms for Gather Victim Identity Information: Credentials
| Term | Simple Definition | Why It Matters |
|---|---|---|
| Credential Stuffing | Automatically trying username/password pairs from one breach on many other sites. | Exploits password reuse. A major risk for employees using work emails on personal, compromised accounts. |
| Password Hash | A scrambled, fixed-length representation of a password (e.g., the result of MD5, SHA-256, bcrypt). | Adversaries gather these from old breach dumps. If the hash is weak, it can be "cracked" back to the plaintext password. |
| OSINT (Open-Source Intelligence) | Information gathered from publicly available sources. | This is the primary method for this technique. Think GitHub commits, public code repos, LinkedIn, and data broker sites. |
| API Key / Token | A code used to identify and authenticate an application or user to a cloud service (AWS, GitHub, Slack). | Often accidentally exposed in public code. If gathered, it gives direct, authorized access to sensitive data and systems. |
| Data Broker / Aggregator | A company that collects, analyzes, and sells personal data from various public and private sources. | Adversaries may purchase bulk data containing email addresses, names, job titles, and sometimes inferred passwords or security Q&A. |
The Attacker's Playbook: Executing Gather Victim Identity Information: Credentials
Step-by-Step Breakdown
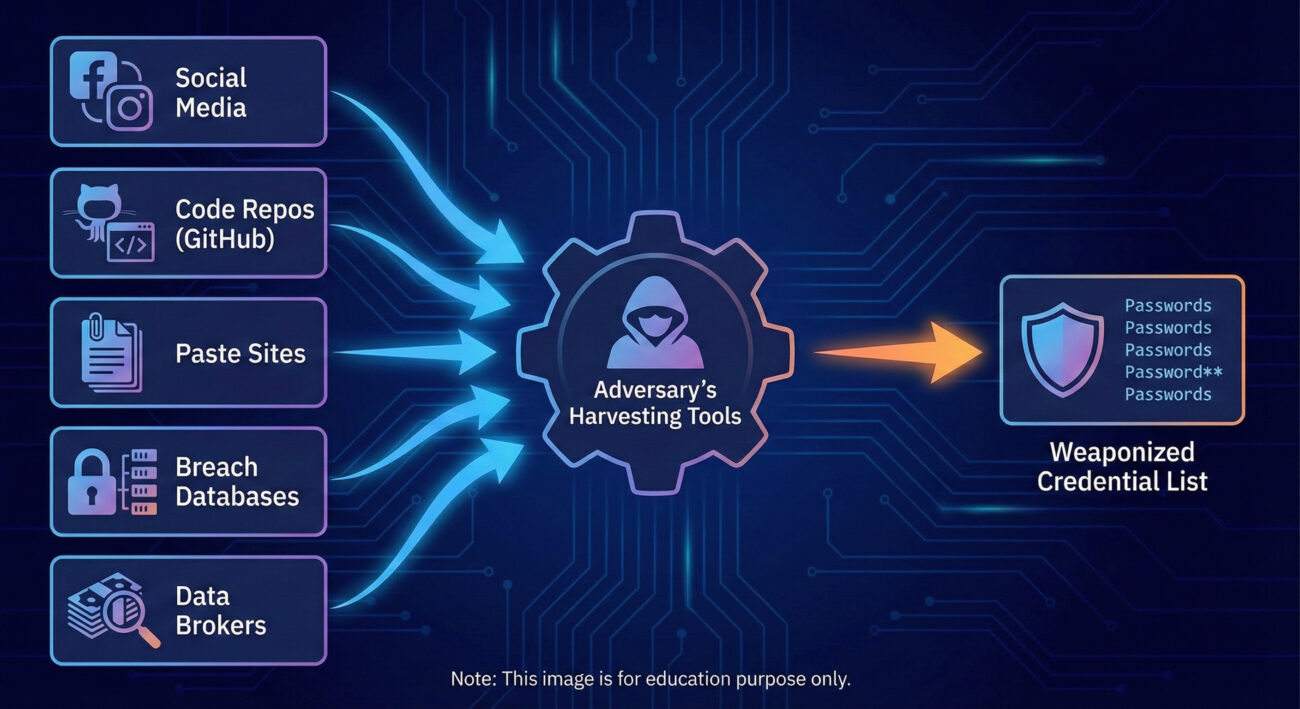
Adversaries follow a systematic, often automated process to maximize their haul of valuable credentials.
- Target Identification: The attacker defines their target organization or individual.
- Source Compilation: They identify relevant data sources: company GitHub, employee LinkedIn profiles, paste sites (like Pastebin), underground breach forums, and data broker lists.
- Automated Harvesting: Using tools (see below), they scrape, query, and download data from these sources, looking for patterns like "@targetcompany.com" or references to internal systems.
- Data Enrichment & Correlation: Gathered emails are checked against known breach databases (HaveIBeenPwned, DeHashed) to find associated passwords. Usernames are matched to potential naming conventions (first.last, flast, etc.).
- Weaponization: The compiled list of credentials (or hashes) is formatted for use in the next phase, such as a password spray list or a targeted phishing campaign.
Red Team Analogy & Mindset
Think of yourself as a private investigator working a case where you can't talk to anyone. Your entire case file must be built from public records, trash left on the curb, and unguarded public statements. Your success depends on patience, thoroughness, and connecting seemingly unrelated dots.
The mindset is one of opportunistic accumulation. You're not just looking for a single, perfect password. You're collecting hundreds of data points, emails, partial passwords, security questions (e.g., "What high school did you attend?" from LinkedIn), and password hashes, knowing that in aggregate, they will create multiple paths for initial access.
Tools & Command-Line Examples
- theHarvester: A classic OSINT tool for gathering emails, subdomains, and names.
- sherlock / maigret: Find usernames across hundreds of social media sites.
- GitRob / TruffleHog: Scan GitHub repositories for accidentally committed secrets (API keys, passwords).
- DeHashed / HaveIBeenPwned (HIPB) API: Programmatically check emails/passwords against known breaches.
Example Command (theHarvester):
theharvester -d "acmecorp.com" -b all -l 500 -f acme_report.html
# -d: Target domain
# -b all: Use all data sources (Google, LinkedIn, etc.)
# -l: Limit results
# -f: Output to HTML fileExample Python Script (Checking Breaches with HIPB API):
import requests
import hashlib
email = "[email protected]"
prefix = hashlib.sha1(email.encode()).hexdigest()[:5].upper()
url = f"https://api.pwnedpasswords.com/range/{prefix}"
response = requests.get(url)
# The response contains a list of hash suffixes that have been breached.
# An adversary would compare the full hash of a gathered password against this list.
print(f"Checking breach status for: {email}")Real-World Campaign Example: APT29 (Cozy Bear) and Cloud Credentials
The Russian-affiliated APT29 group is a master of patient, intelligence-driven reconnaissance. In campaigns targeting cloud environments, they have been observed extensively gathering victim identity information related to cloud services.
They scrape public repositories (like GitHub) for developers who may have accidentally left API keys, access tokens, or configuration files for services like AWS, Azure, or Google Cloud Platform in their code. These gathered credentials provide immediate, legitimate access to cloud resources, bypassing many perimeter defenses.
This activity is a critical precursor to their later tactics of Defense Evasion and Lateral Movement within cloud subscriptions.
Source: Mandiant Report on APT29 Attacks on Azure AD Identities
The Defender's Handbook: Stopping Gather Victim Identity Information: Credentials
Blue Team Analogy & Detection Philosophy
You are the homeowner trying to limit the information a thief can find in your trash. You shred documents, are mindful of what you post publicly, and periodically check if your personal info is for sale on sketchy websites. You can't stop all collection, but you can make it harder, noisier, and less valuable.
Detection at this stage is uniquely challenging because the activity often happens outside your network and uses legal methods. The defender's focus shifts from blocking to awareness and pre-emption. The goal is to discover what an adversary might have already learned about you and proactively invalidate those findings.
SOC Reality Check: What to Look For
You won't see a direct alert titled "Adversary Gathering Credentials." Instead, look for correlated anomalies:
- Unusual Volume: A sudden spike in failed logins for a wide range of user accounts (password spray) using credentials likely gathered from a breach.
- Impossible Travel or New Location: A user account successfully authenticating from a new country shortly after your company was mentioned in a targeted threat report.
- Probing from OSINT Hubs: Scans or web traffic originating from IPs associated with common OSINT tool hosting providers or data centers.
The noise here is immense. The key is to baseline normal authentication patterns and investigate deviations that align with a potential pre-attack reconnaissance phase.
Threat Hunter's Eye: Practical Query
This Sigma rule hunts for potential credential stuffing attacks by detecting multiple user accounts failing to authenticate from the same source IP in a short time window, a common next step after adversaries gather a list of valid usernames/emails.
title: Potential Credential Stuffing Attack
id: a7b3c8d2-1f4e-4a6c-b8d9-0e1f2a3b4c5d
status: experimental
description: Detects multiple failed logins for distinct usernames from a single source IP, indicative of credential stuffing.
author: Your SOC
date: 2023-10-26
logsource:
category: authentication
product: windows
service: security
detection:
selection:
EventID: 4625 # An account failed to log on
filter_local:
IpAddress|startswith: '192.168.' # Filter out internal IPs
IpAddress|startswith: '10.' # Filter out internal IPs
timeframe: 5m
condition: selection and not filter_local | count() by IpAddress > 10
# Alert if more than 10 distinct usernames fail from one external IP in 5 mins
fields:
- IpAddress
- TargetUserName
level: medium
tags:
- attack.credential_access
- attack.t1110 # Brute Force
- attack.t1589.001 # Credential Gathering (Precursor)Key Data Sources for Detection
- Authentication Logs (Windows Security Event ID 4625, VPN/Cloud IdP logs): The primary source for observing the use of gathered credentials.
- Web Proxy/Cloud Access Security Broker (CASB) Logs: Can show employees accessing known paste sites, breach databases, or OSINT tool sites from corporate IPs (could be insider threat or compromised host).
- Endpoint Detection & Response (EDR): Look for execution of OSINT tools (theHarvester, sherlock) or custom scripts on corporate assets.
- External Threat Intelligence Feeds: Services that alert you if your company's credentials or internal data appear in new breach dumps or on the dark web.
Building Resilience: Mitigation Strategies for Gather Victim Identity Information: Credentials
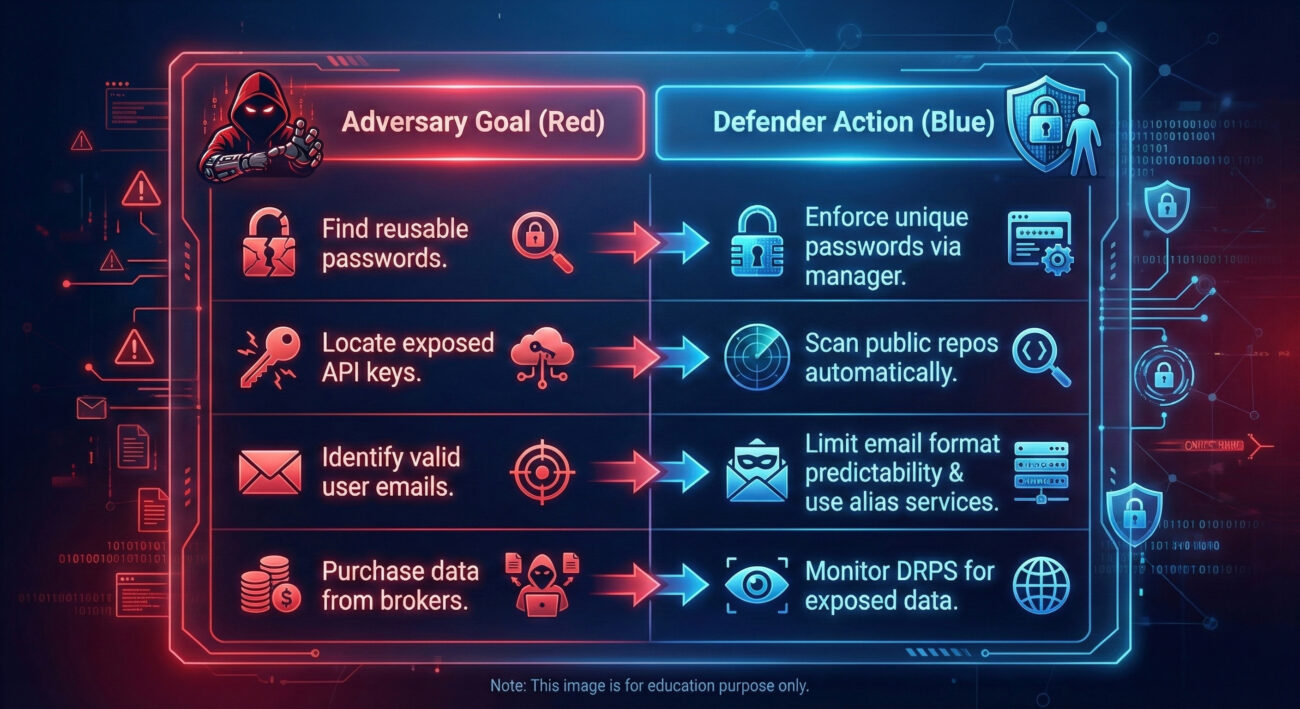
Actionable Mitigation Controls
- Enforce Strong, Unique Passwords & Password Managers: Mandate the use of password managers to eliminate password reuse across work and personal sites. This nullifies the value of credentials stolen from unrelated breaches.
- Implement Phishing-Resistant MFA Everywhere: Use FIDO2 security keys or certificate-based authentication. Even if a password is gathered, it's useless without the second factor.
- Conduct Proactive External Exposure Scans: Regularly use tools like TruffleHog on your own public GitHub orgs. Implement pre-commit hooks to scan for secrets in code. Consider services like GitHub's secret scanning.
- Security Awareness Training with a Twist: Don't just teach "don't click links." Train employees on operational security (OpSec): what not to post on social media, the dangers of reusing passwords, and how to report suspected doxxing or credential exposure.
- Subscribe to Digital Risk Protection Services (DRPS): These services continuously monitor the surface, deep, and dark web for your company's exposed data, credentials, and intellectual property, providing early warning.
Red vs. Blue: A Quick Comparison
Gather Victim Identity Information: Credentials Cheat Sheet
🔴 Red Flag
Employee email addresses appear in a new "combo list" (username:password dump) posted on a hacking forum. A surge in authentication attempts for non-existent users (probing for valid accounts) from diverse IPs.
🛡️ Blue's Best Move
Immediately enforce a password reset and review sign-in logs for affected accounts. Accelerate rollout of phishing-resistant MFA to the highest-risk groups.
🔍 Hunt Here
Authentication logs (Event ID 4625) filtered for failures on multiple distinct valid usernames from a single external IP within a 10-minute window. Cloud audit logs for GetUser or ListUsers API calls from new geolocations.
📚 Learn More
MITRE ATT&CK T1589.001
NIST Digital Identity Guidelines (SP 800-63B) - The gold standard for authentication.
Conclusion and Next Steps
Gather Victim Identity Information: Credentials (T1589.001) is the quiet, often invisible opening move in a modern cyber attack. By understanding the attacker's methods, scraping public data, mining breach dumps, and correlating information, defenders can shift from a reactive to a pre-emptive posture.
Your defense is not just about stronger walls, but about controlling the information landscape. Implement password managers, deploy phishing-resistant MFA, scan for your own exposed data, and hunt for the early-use patterns of gathered credentials.
Continue Your Learning:
- Internal Link: See how gathered credentials are used in the next phase with our guide on [Internal-Link: Credential Stuffing (T1110.004)].
- Internal Link: Understand how adversaries move after initial access with [Internal-Link: Lateral Movement Techniques].
- External Resource (DoFollow): The CISA Secure Our World campaign provides excellent foundational guidance for individuals and organizations, directly addressing password security and MFA.
- External Resource (DoFollow): Dive deeper into cloud credential security with the Microsoft Azure Identity Management Security Best Practices.
Stay vigilant, reduce your attack surface, and remember: the best time to defend against credential theft was yesterday. The second-best time is now.
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026


















































