Cybersecurity Predictions 2026
Separating Critical Threats from Overhyped Noise Explained Simply
Every year, the cybersecurity industry is flooded with dire predictions and sensational headlines. As we look toward 2026, separating the credible threats from the overhyped noise is more critical than ever for effective defense. This analysis cuts through the hype, focusing on the evolving tactics of adversaries, the practical implications for defenders, and the actionable steps you can take to build resilience. We'll map these future trends to real-world frameworks like MITRE ATT&CK to give you a concrete, technical understanding of what's coming.
Table of Contents
- Executive Summary: The Hype vs. Reality Matrix
- The AI & LLM Arms Race: Beyond the Hype
- Software Supply Chain Attacks: The New Normal
- MITRE ATT&CK Techniques to Watch in 2026
- Step-by-Step: Future-Proofing Your Security Posture
- Red Team vs. Blue Team: 2026 Perspectives
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Start Building Your 2026 Defense Today
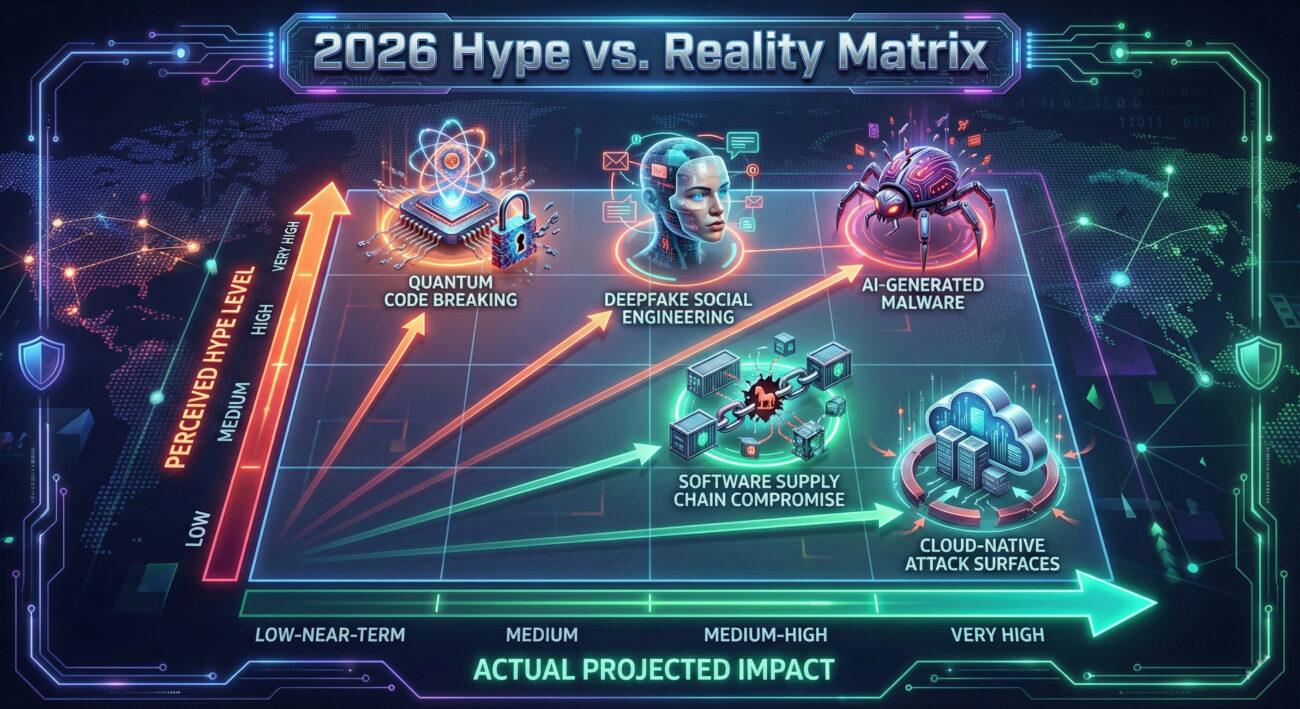
Executive Summary: The Hype vs. Reality Matrix
The landscape of cybersecurity predictions for 2026 is a mix of continued evolution and speculative leaps. While headlines scream about AI-powered cyber-doom and quantum apocalypses, the more pressing dangers are refinements of existing attack vectors. The core vulnerability remains: the human element and complex, interconnected digital ecosystems. This post will demystify the predictions, focusing on the practical defenses you need to prioritize.
The AI & LLM Arms Race: Beyond the Hype
The use of Artificial Intelligence (AI) and Large Language Models (LLMs) by both attackers and defenders is a guaranteed trend for 2026. The hype suggests fully autonomous hackers, but the reality is more nuanced: AI will act as a powerful force multiplier.
How AI-Powered Attacks Will Actually Work
Threat actors will use LLMs to dramatically scale and enhance social engineering. Imagine phishing campaigns with thousands of unique, grammatically perfect emails tailored by scraping your LinkedIn profile. Beyond emails, AI will generate convincing deepfake audio for CEO fraud (Business Email Compromise) or synthesize video for disinformation campaigns.
On the technical side, AI will be used to mutate malware code in real-time to evade signature-based detection (a technique related to Obfuscated Files or Information, T1027 in MITRE ATT&CK). It will also help attackers analyze vast amounts of stolen data to identify high-value targets for further exploitation more efficiently.
Software Supply Chain Attacks: The New Normal
Attacks like SolarWinds and Log4j demonstrated the catastrophic ripple effects of compromising a single piece of trusted software. In 2026, software supply chain attacks will become more frequent and sophisticated, moving from a headline-grabbing event to a persistent background threat.
The Attack Flow: A Technical Perspective
Here’s how a typical sophisticated supply chain compromise might occur:
Step 1: Initial Compromise (T1195.002)
The attacker gains access to a software vendor's development environment. This is often done via spear-phishing a developer (Initial Access) or exploiting a vulnerability in the vendor's public-facing systems.
Step 2: Code Poisoning & Obfuscation
The attacker subtly injects malicious code into a legitimate library or update. They use sophisticated obfuscation (T1027) to hide the malicious payload within normal-looking code, ensuring it passes initial code reviews.
Step 3: Trust & Distribution
The tainted software, signed with the vendor's legitimate digital certificate (Trusted Relationship, T1199), is distributed to thousands of victims through automatic update channels.
Step 4: Execution & Persistence
Once the update is installed, the malicious code executes (User Execution, T1204), often establishing a backdoor (Persistence) and moving laterally (Lateral Movement) within the victim's network.
MITRE ATT&CK Techniques to Watch in 2026
Mapping future threats to the MITRE ATT&CK framework provides a common language for understanding and defending against them. Here are key techniques expected to rise in prominence:
| MITRE ATT&CK Tactic | Technique (ID & Name) | 2026 Prediction & Context | Defensive Action |
|---|---|---|---|
| Initial Access | T1195.002 (Compromise Software Supply Chain) | Will be the primary vector for large-scale, espionage-focused campaigns. Targeting open-source repositories and CI/CD pipelines will increase. | Implement software bill of materials (SBOM) and strict code signing verification. |
| Execution | T1204.002 (Malicious File via User Execution) | AI-crafted lures will make file-based execution (docs, PDFs) more effective, bypassing user suspicion. | Enhanced user training on AI-generated lures and application allow-listing. |
| Defense Evasion | T1027 (Obfuscated Files or Information) | AI will automate the creation of polymorphic and metamorphic code, making static analysis nearly useless. | Shift to behavioral and heuristic detection (EDR/XDR) and network traffic analysis. |
| Credential Access | T1649 (Steal or Forge Authentication Certificates) | As certificates become more central to zero-trust models, attackers will increasingly target certificate authorities and steal machine identities. | Robust certificate lifecycle management and hardware security modules (HSMs). |
| Impact | T1486 (Data Encrypted for Impact) | Ransomware will evolve into more targeted "big game hunting" with triple extortion (data encryption, theft, and DDoS). | Immutable, air-gapped backups tested regularly and a practiced incident response plan. |
Step-by-Step: Future-Proofing Your Security Posture
Don't wait for 2026. Follow this actionable framework to build resilience against these evolving threats.
Step 1: Assume Breach & Adopt Zero Trust
Move from a perimeter-based model to "never trust, always verify." Implement strict access controls (like Multi-Factor Authentication (MFA) everywhere), micro-segmentation for your network, and continuous verification of user and device identity. The CISA Zero Trust Maturity Model is an excellent guide.
Step 2: Harden Your Software Supply Chain
- Generate and analyze an SBOM for all critical applications.
- Use trusted, vetted repositories and enforce version pinning.
- Scan all dependencies for known vulnerabilities using tools like OWASP Dependency-Check.
- Implement code signing and verify signatures before deployment.
Step 3: Shift to Behavioral Detection
Since signature-based AV will fail against AI-mutated malware, invest in Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) solutions. These tools monitor for anomalous behavior (e.g., a process trying to encrypt hundreds of files) rather than known bad code.
Step 4: Prepare for AI-Driven Social Engineering
Update your security awareness training. Run exercises using simulated AI-generated phishing content. Implement technical controls like email authentication (DMARC, DKIM, SPF) and advanced anti-phishing gateways that analyze language patterns.
Step 5: Test, Test, Test with Purple Teaming
Regularly test your defenses using purple teaming exercises, where your red (attack) and blue (defense) teams collaborate. Simulate the specific MITRE ATT&CK techniques highlighted for 2026 to find gaps in your detection and response playbooks.
Red Team vs. Blue Team: 2026 Perspectives
The evolving threat landscape changes the game for both attackers and defenders. Here’s how each side is preparing for 2026.
Red Team (Threat Actor) View
Primary Goal: Maximize impact and stealth while minimizing cost and effort.
- Weaponizing AI: Using LLMs to write convincing phishing lures, generate fake social media profiles for reconnaissance, and automate target analysis from data leaks.
- Exploiting Trust: Focusing less on brute force and more on compromising trusted third parties (suppliers, software vendors) to gain access to hardened primary targets.
- Living-off-the-Land (LOTL): Increasing use of legitimate admin tools (like PowerShell, PsExec) for execution and lateral movement to evade endpoint security that focuses on malicious binaries.
- Asymmetric Attacks: Targeting the less-secure personal devices of executives (mobile phones, home networks) as a backdoor into corporate resources in a work-from-anywhere world.
Blue Team (Defender) View
Primary Goal: Reduce mean time to detect (MTTD) and mean time to respond (MTTR) while building systemic resilience.
- Leveraging AI Defensively: Deploying AI-powered Security Orchestration, Automation, and Response (SOAR) to correlate alerts and automate containment of common attack patterns, freeing analysts for complex threats.
- Extended Visibility: Implementing XDR to get a unified view across endpoints, network, cloud, and email, crucial for spotting the subtle signs of a supply chain attack.
- Identity as the New Perimeter: Doubling down on strong identity governance, privileged access management (PAM), and universal MFA to mitigate credential-based attacks.
- Proactive Threat Hunting: Continuously searching for IOC/IoAs (Indicators of Compromise/Attack) related to emerging MITRE techniques, rather than waiting for alerts.
Common Mistakes & Best Practices
Avoid these pitfalls and embrace these proven strategies to navigate 2026 securely.
Common Mistakes to Avoid
- Ignoring the Software Supply Chain: Blindly trusting third-party code and updates without verification.
- Over-Reliance on Legacy AV: Assuming traditional antivirus is sufficient against fileless and AI-mutated malware.
- Static Security Training: Using the same phishing training examples year after year, failing to prepare for AI-generated content.
- Complexity Over Security: Implementing dozens of security tools that don't integrate, creating alert fatigue and visibility gaps.
- Neglecting Backup Integrity: Having backups but not testing restoration or leaving them connected to the main network, making them vulnerable to ransomware encryption.
Best Practices to Adopt
- Implement a Zero Trust Architecture: Start with network segmentation and strict access controls.
- Adopt EDR/XDR & SIEM: Invest in tools that provide behavioral detection and centralized log analysis.
- Enforce Strong Authentication: Mandate MFA everywhere possible and use phishing-resistant methods (FIDO2/WebAuthn) for high-privilege accounts.
- Run Regular Purple Team Exercises: Continuously test your defenses against the latest real-world attack techniques.
- Develop and Practice IR Plans: Have a clear, documented incident response plan and run tabletop exercises at least twice a year.
Frequently Asked Questions (FAQ)
Q: Is "AI hacking" the biggest threat for 2026?
A: Not exactly. AI is a powerful tool that enhances existing threats (like phishing and malware creation), but it's not an autonomous threat itself. The biggest danger is the human element being exploited by more convincing, AI-powered social engineering. Your defense should focus on training and technical controls for this hybrid threat.
Q: Should we be worried about quantum computing breaking encryption in 2026?
A: This is often overhyped for the near term. While quantum computing poses a long-term risk to current public-key encryption (like RSA), widespread, practical attacks are not expected by 2026. However, the transition to quantum-resistant cryptography is a multi-year process. The best practice now is to start inventorying where critical, long-term data is protected by current encryption and follow NIST's Post-Quantum Cryptography project for migration plans.
Q: As a small business, how can I possibly defend against these advanced threats?
A: Focus on the fundamentals, which stop the vast majority of attacks regardless of their sophistication:
- Enable Multi-Factor Authentication (MFA) on all accounts.
- Keep all software patched and updated automatically.
- Use a managed EDR service.
- Train employees on modern phishing tactics.
- Maintain verified, offline backups of critical data.
Many of these are low-cost or built into modern cloud services.
Key Takeaways
- Hype vs. Reality: Ignore the sci-fi scenarios. Focus on the evolution of software supply chain attacks, AI-augmented social engineering, and the exploitation of cloud and identity infrastructure.
- Framework is Key: Use the MITRE ATT&CK framework (techniques like T1195.002, T1027) to understand and plan defenses against these future threats in a structured way.
- Shift Left and Right: "Shift left" by securing your software supply chain with SBOMs and code signing. "Shift right" by investing in behavioral detection (EDR/XDR) and robust incident response capabilities.
- Identity is Paramount: In a perimeter-less world, strong authentication (MFA) and strict access controls are your most critical security layers.
- Preparation Beats Prediction: Instead of worrying about specific predictions, build a resilient, adaptable security program focused on visibility, automation, and continuous testing through purple teaming.
Call to Action: Start Building Your 2026 Defense Today
The cybersecurity predictions for 2026 aren't a distant future problem, they are trends already in motion. Begin your journey now:
Your First Week: Conduct a Gap Analysis
Map your current controls against the MITRE ATT&CK techniques listed in this article. Can you detect or prevent T1195.002 (Supply Chain Compromise) in your environment? If not, that's your starting point.
Continue Learning: Bookmark and regularly review resources from CISA's Secure Our World campaign, the OWASP Top Ten for application security, and the SANS Institute Blog for in-depth technical analysis.
Remember: Cybersecurity is a continuous process, not a destination. By understanding the real threats beyond the hype and taking systematic, actionable steps, you can confidently face the challenges of 2026 and beyond.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































