Digital Footprint Attack
How Your Online Traces Lead to Breaches Explained Simply
Table of Contents
- Executive Summary: The Invisible Attack Surface
- What is a Digital Footprint?
- The Anatomy of a Digital Footprint Attack
- Mapping to MITRE ATT&CK: The Attacker's Playbook
- Real-World Scenario: From LinkedIn to Ransomware
- Step-by-Step Guide: Auditing Your Digital Footprint
- Common Mistakes & Best Practices
- Red Team vs. Blue Team View
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action
Every click, every post, every account you create leaves a trace. This digital footprint is more than just a virtual shadow; it's a goldmine for cybercriminals. In what's known as a digital footprint attack, hackers systematically scour the internet for these traces to build a profile, identify vulnerabilities, and launch targeted attacks against individuals and organizations.
Executive Summary: The Invisible Attack Surface
A digital footprint attack is not a single tool or malware. It's a methodology that leverages open-source intelligence (OSINT) and reconnaissance to turn your public online presence into an attack vector. Before a single malicious line of code is written, threat actors are piecing together your digital life, your job title on LinkedIn, your tech stack mentions on GitHub, your email in a data breach, your location from a social media check-in. This compiled intelligence fuels highly effective phishing, credential stuffing, social engineering, and even physical security breaches.
What is a Digital Footprint? (And Why It's a Liability)
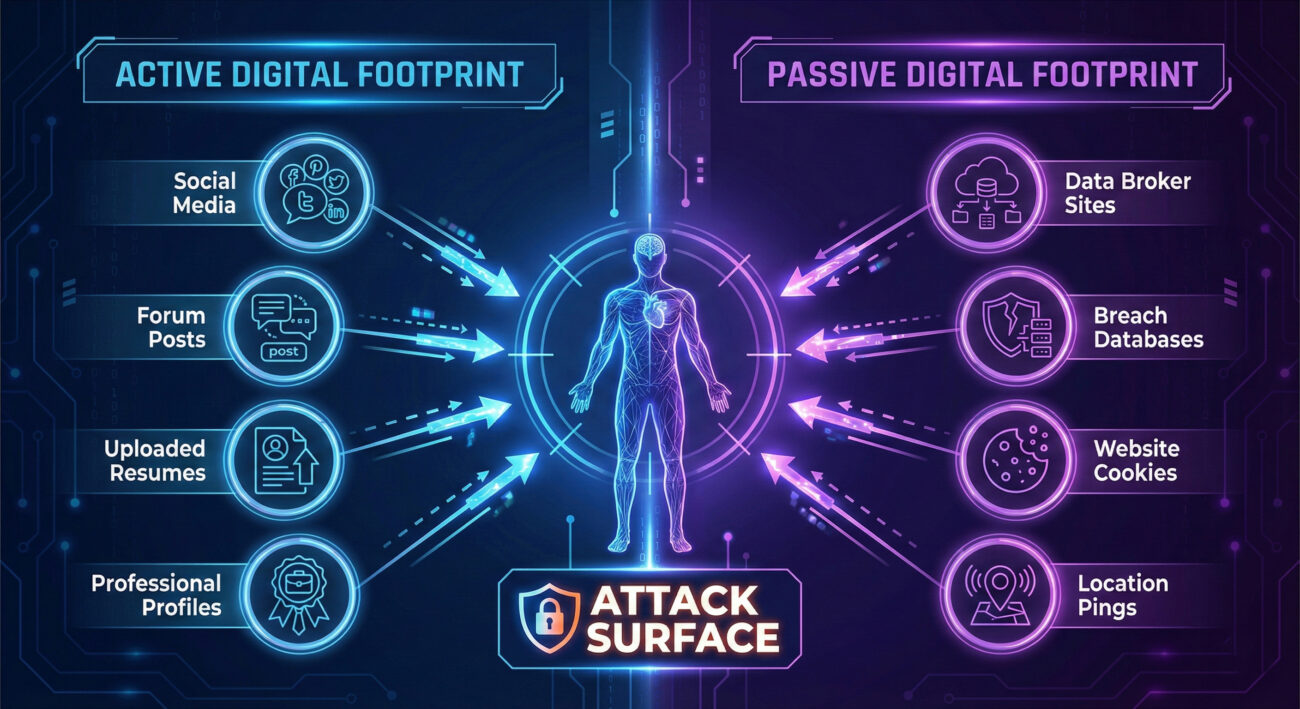
Your digital footprint consists of two main parts:
- Active Footprint: Data you intentionally share (social media posts, forum comments, professional profiles, uploaded documents).
- Passive Footprint: Data collected about you without your direct input (IP logs, website cookies, data broker profiles, breach databases).
For cybersecurity professionals, this includes: email addresses, employee directories, technical forum answers (revealing internal tools), metadata in uploaded documents, and even badges in conference photos.
The Anatomy of a Digital Footprint Attack: How It Works
Here's a technical breakdown of how a digital footprint attack progresses:
Phase 1: Reconnaissance (The Hunt)
The attacker uses automated OSINT tools and manual searches to gather data.
- Target Identification: Finding target email patterns (e.g., [email protected]) via company websites or LinkedIn.
- Data Aggregation: Using tools like theHarvester, Maltego, or simply searching on Google with advanced operators (e.g.,
site:pastebin.com "targetcompany"). - Password Dump Correlation: Checking email addresses against databases from past breaches (e.g., on Have I Been Pwned or underground forums).
Phase 2: Weaponization & Social Engineering
Collected data is used to craft believable attack vectors.
- Spear Phishing: An email references a recent project the target mentioned on Twitter or a real colleague's name found on the company page.
- Credential Stuffing: Reusing passwords found in breach dumps on corporate accounts (like VPN portals or email).
- Pretexting: Calling IT support, impersonating an employee using personal details (pet's name, hire anniversary) gleaned from social media to request a password reset.
Mapping to MITRE ATT&CK: The Attacker's Official Playbook
The digital footprint attack maps directly to several techniques in the MITRE ATT&CK framework, primarily under the Reconnaissance and Resource Development tactics.
| MITRE ATT&CK Tactic | Technique ID & Name | How It Relates to Digital Footprint Attacks |
|---|---|---|
| Reconnaissance | T1593.001 - Search Open Technical Databases | Scanning GitHub for code leaks, Shodan for exposed devices, or domain registration (WHOIS) data. |
| Reconnaissance | T1589.001 - Gather Victim Identity Information | Collecting employee names, email addresses, and phone numbers from LinkedIn, company websites, or press releases. |
| Reconnaissance | T1596.005 - Search Victim-Owned Websites | Analyzing a target company's career page to identify software/hardware in use (e.g., "looking for an AWS expert"). |
| Resource Development | T1586.001 - Compromise Accounts | Using credentials from past breaches to take over personal accounts that might grant access to work resources (e.g., same password reused). |
Understanding this framework is crucial for defenders to anticipate and monitor for these precursor activities.
Real-World Scenario: From a LinkedIn Post to a Ransomware Breach
Let's trace a fictional but highly plausible attack chain:
Step 1: The Recon
A threat actor finds a mid-level manager at "TechCorp" on LinkedIn. The manager's profile lists they're "Excited to lead the migration to CloudProviderX!" and congratulates a colleague on a promotion.
Step 2: The Weaponization
The attacker crafts a phishing email posing as "CloudProviderX Support," referencing the migration. The email is sent to the manager's work email (format: [email protected], found on the company's contact page).
Step 3: The Initial Access
The manager clicks the link, entering their corporate credentials on a convincing fake login page. The attacker now has valid credentials.
Step 4: Lateral Movement & Impact
Using these credentials, the attacker accesses the network, moves laterally, and eventually deploys ransomware. The initial entry point was entirely enabled by public digital footprint data.
Step-by-Step Guide: Auditing and Reducing Your Digital Footprint
Take proactive control. Follow this actionable guide:
Step 1: Self-Search Audit
Search for yourself (and your key employees) across multiple engines and platforms. Use incognito mode.
- Google: Search your name, email address, username, and "name + company".
- Specialized Sites: Check Have I Been Pwned for breach exposure. Use dehashed.com (requires account) for more detailed breach data.
- Image Search: Use Google Reverse Image Search on your profile pictures.
Step 2: Social Media & Profile Lockdown
- Review privacy settings on ALL platforms (LinkedIn, Facebook, Twitter, Instagram, GitHub).
- Remove or make private: birth date, address, family member names, exact job titles/descriptions if too revealing.
- Scrutinize past posts and photos for sensitive info.
Step 3: Implement Technical Safeguards
- Use a unique, strong password for every account, managed by a password manager.
- Enable Multi-Factor Authentication (MFA) everywhere, especially on email and financial accounts.
- Consider using email aliases or separate emails for shopping, social media, and professional use.
Common Mistakes & Best Practices
Common Mistakes (What Not To Do)
- Using the same password across personal and work accounts.
- Posting work-related details, travel plans, or tech stack info publicly on social media.
- Ignoring data breach notifications.
- Keeping old accounts active on sites you no longer use.
- Using personal email for work sign-ups and vice-versa, blending your footprints.
Best Practices (What To Do)
- Conduct a quarterly personal and organizational digital footprint audit.
- Use a Password Manager and enforce MFA universally.
- Educate employees on the risks of oversharing and spear phishing.
- Use professional aliases for online sign-ups to compartmentalize your footprint.
- Monitor domains and data for signs of corporate information leakage.
Red Team vs. Blue Team View
Red Team (Attack) Perspective
For a Red Teamer, a digital footprint is the starting point for every engagement. It's about efficiency: why brute force a door when you can find the key under the mat? Tools like Sherlock (for username hunting) and Recon-ng automate the collection. The goal is to build a "target package" with emails, potential passwords, social connections, and technical hints to craft a believable pretext for initial access.
Blue Team (Defense) Perspective
The Blue Team must think like the attacker. This involves proactive monitoring for corporate data leaks (e.g., code on paste sites, employee credentials in breach dumps). Security awareness training must cover digital footprint risks. Defenders can also run footprint audits on their own organization to find and remove unnecessary exposed information before the adversary does. Tools like Digital Footprint Lab or commercial OSINT platforms can be used defensively.
Frequently Asked Questions (FAQ)
Q: Can I completely erase my digital footprint?
A: Realistically, no. The goal isn't complete erasure (which is nearly impossible), but reduction and management. You can significantly shrink your attackable surface by removing unnecessary data and securing what remains.
Q: Is a digital footprint attack only a problem for executives?
A> Absolutely not. All employees are targets. An entry-level employee's credentials or system access can be the perfect foothold for a hacker to move laterally into a network.
Q: What's the single most important step I can take today?
A: Enable Multi-Factor Authentication (MFA) on your primary email account and password manager. This one action blocks the vast majority of automated credential-based attacks stemming from breached data.
Key Takeaways
- Your digital footprint is a primary attack vector, not just a privacy concern.
- Attackers follow the MITRE ATT&CK framework, using Reconnaissance (T1593, T1589) to fuel their attacks.
- The attack chain often starts with OSINT gathering long before any malware is deployed.
- Proactive, regular audits of your own and your organization's digital footprint are a critical defense measure.
- Password managers and MFA are non-negotiable tools to mitigate risks from exposed credentials.
Call to Action: Take Control Now
Don't be a low-hanging fruit. Spend the next 30 minutes on your digital hygiene.
- Search for your primary email on Have I Been Pwned.
- Enable MFA on your email and one other critical account (e.g., bank).
- Review the privacy settings on your most-used social media profile.
Your security starts with awareness. Share this guide with your team and start the conversation about digital footprint attacks today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































