VS Code Extensions Exploited by Evelyn Stealer for Data Theft
Evelyn Stealer Alert Explained Simply
The trusted tools in a developer's arsenal are becoming the latest attack vector. A sophisticated new malware campaign is weaponizing the Microsoft Visual Studio Code (VS Code) extension marketplace to deliver a powerful information stealer called Evelyn Stealer. This malware specifically targets software developers, a high-value target group with access to critical credentials, proprietary code, and organizational infrastructure. Understanding the mechanics of this attack is the first step in building effective defenses for your development environment.
Table of Contents
- Executive Summary: The Developer-Targeted Threat
- The Attack Flow: From Infected Extension to Data Exfiltration
- Technical Breakdown of Evelyn Stealer's Capabilities
- Mapping Evelyn Stealer to MITRE ATT&CK
- A Practical Defense Framework for Development Teams
- Red Team vs. Blue Team Perspective
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The Developer-Targeted Threat
The Evelyn Stealer campaign represents a dangerous evolution in cyber attacks, moving beyond phishing emails to compromise the very tools developers use daily. By uploading malicious extensions to the official VS Code marketplace, with names like "Theme for monkeytype" and "Codo AI", threat actors exploit the trust developers place in this ecosystem. Once installed, these extensions act as a trojan horse, initiating a multi-stage infection that results in comprehensive data theft from the victim's machine.
This malware is not just a simple credential scraper. It is a sophisticated tool designed to blend in, avoid detection, and persistently harvest a wide array of sensitive information, including browser cookies, cryptocurrency wallets, system credentials, and even desktop screenshots. Developers are targeted because compromising their workstations can provide a direct pipeline into an organization's source code, production servers, and cloud environments, making this a critical breach vector for enterprises.
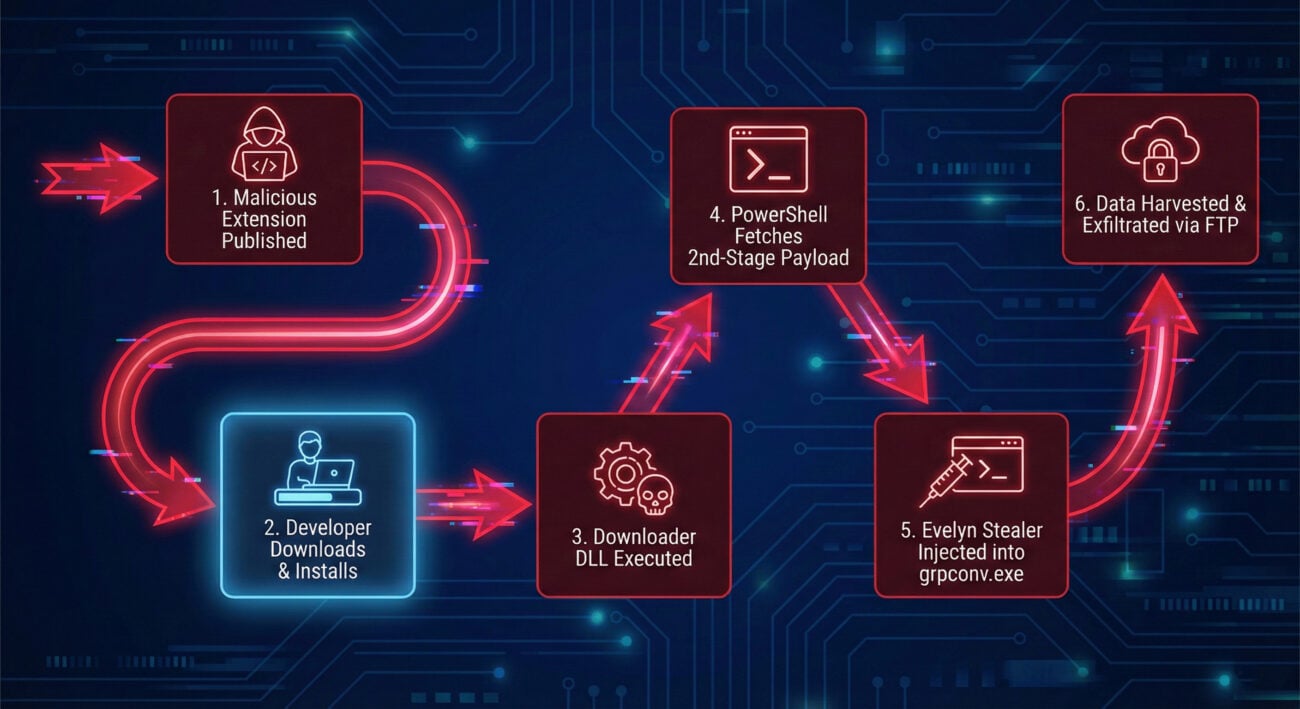
The Attack Flow: From Infected Extension to Data Exfiltration
Understanding the sequence of events is crucial for detection and prevention. The Evelyn Stealer infection follows a carefully orchestrated chain designed to evade initial security checks.
Step 1: Weaponizing Trust
Threat actors create seemingly useful or attractive VS Code extensions, like themes or AI assistants, and publish them to the official Visual Studio Code Marketplace. They rely on developers searching for tools and installing them without rigorous vetting.
Step 2: The Initial Compromise
Once the extension is installed and runs, it drops a malicious downloader DLL file (e.g., Lightshot.dll). This file is the first piece of the malware payload to touch the disk. Its primary job is to establish persistence and retrieve the next stage.
Step 3: Living off the Land
The downloader executes a hidden PowerShell command. This script uses legitimate system tools (Living off the Land Binaries or LOLBins) to fetch the second-stage payload, named runtime.exe, from a remote command-and-control (C2) server. Using PowerShell helps the activity blend in with normal admin tasks.
Step 4: Memory-Only Execution
The runtime.exe payload is designed to avoid writing the core stealer to disk. It decrypts the main Evelyn Stealer module and injects it directly into the memory space of a legitimate, trusted Windows process: grpconv.exe (the Group Policy Conversion Tool). This fileless execution technique makes traditional antivirus scans less effective.
Step 5: Stealthy Data Harvesting
With the stealer active in memory, it begins its collection routine. To ensure it can grab browser data without interference, it forcibly closes browsers and then re-launches them in a hidden, headless state using a series of command-line flags designed to disable security features and logging.
Step 6: Exfiltration
All harvested data, from credentials and cookies to wallet files and screenshots, is compressed into a ZIP archive. This archive is then sent out of the victim's network to the attacker's server via File Transfer Protocol (FTP), completing the breach.
Technical Breakdown of Evelyn Stealer's Capabilities
The power of Evelyn Stealer lies in its comprehensive and stealthy feature set. Below is a detailed table of its data harvesting capabilities and anti-analysis techniques.
| Category | Specific Target | Impact & Purpose |
|---|---|---|
| Credentials & Sessions | Cookies, Saved Logins from Chrome, Edge, Firefox; Session data from WhatsApp, Telegram | Allows attackers</span to hijack active sessions, bypassing passwords and multi-factor authentication (MFA) to access email, cloud accounts, and messaging apps. |
| Financial Data | Cryptocurrency wallet files (e.g., Exodus, Atomic, Electrum), Clipboard content | Direct financial theft. Monitoring the clipboard allows the malware to capture cryptocurrency addresses during transactions and replace them with the attacker's own. |
| System Intelligence | Installed apps, Running processes, Wi-Fi passwords, System information (hostname, OS) | Provides reconnaissance for further, targeted attacks within the network or for selling the information on cybercrime forums. |
| Anti-Analysis & Stealth | Virtual Machine (VM) detection, Mutex creation, Headless browser launch flags | Prevents execution in sandboxed analysis environments, avoids multiple instances causing crashes, and hides browser activity from the user during data theft. |
The Browser Trick: One of the most notable technical features is how Evelyn Stealer handles browsers. It terminates them, then relaunches them with flags like --headless=new, --no-sandbox, and --disable-logging. This allows it to programmatically access profile data (where cookies and passwords are stored) without triggering security warnings or leaving obvious traces in the user's visible session.
Mapping Evelyn Stealer to MITRE ATT&CK
Framing the attack within the MITRE ATT&CK framework gives defenders a standardized language to understand the adversary's tactics, techniques, and procedures (TTPs). This is essential for building effective detection rules.
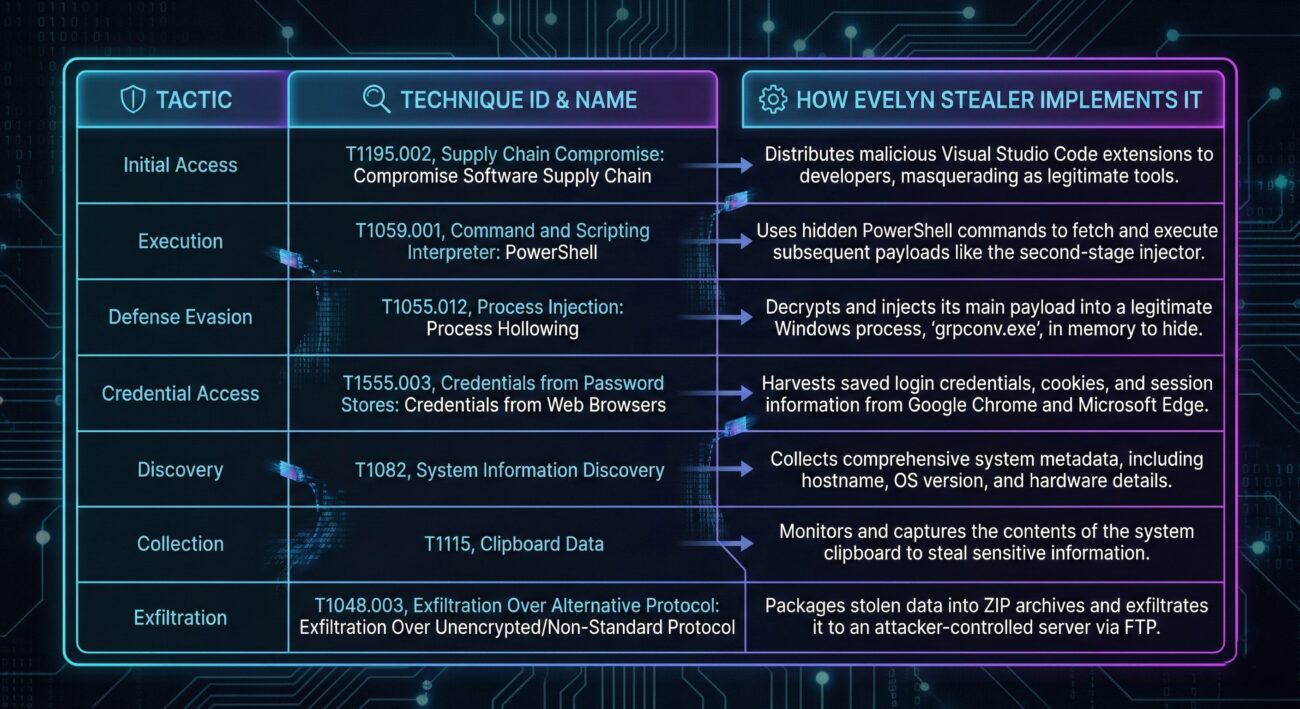
Here are the key MITRE ATT&CK techniques associated with the Evelyn Stealer campaign:
- Initial Access (TA0001):
- T1176: Supply Chain Compromise. The primary vector. The malicious VS Code extension represents a compromise of a trusted development tool supply chain.
- Execution (TA0002):
- T1059.001: Command and Scripting Interpreter: PowerShell. Used extensively to download and execute payloads silently.
- T1204.002: User Execution: Malicious File. The user is tricked into executing the malicious extension.
- Defense Evasion (TA0005):
- T1620: Reflective Code Loading. The stealer payload is decrypted and injected directly into the memory of
grpconv.exe. - T1497: Virtualization/Sandbox Evasion. Includes checks to detect virtual machine or analysis environments.
- T1562.001: Impair Defenses: Disable or Modify Tools. The browser flags (
--no-sandbox,--disable-logging) actively disable security features.
- T1620: Reflective Code Loading. The stealer payload is decrypted and injected directly into the memory of
- Collection (TA0009) & Exfiltration (TA0010):
- T1113: Screen Capture. Takes desktop screenshots.
- T1005: Data from Local System. Harvests files, credentials, and system information.
- T1041: Exfiltration Over C2 Channel. Uses FTP to send stolen data to a remote server.
A Practical Defense Framework for Development Teams
Protecting against threats like Evelyn Stealer requires a layered approach, combining policy, technology, and user awareness. Here are actionable steps for individuals and organizations.
Common Mistakes & Best Practices
Common Mistakes (The Don'ts)
- Blind Trust in Marketplaces: Assuming all extensions in an official store (like VS Code Marketplace) are safe without checking reviews, publisher credibility, or download counts.
- Running with Excessive Privileges: Using a local administrator account for daily development work, which allows malware like Evelyn Stealer to perform more damaging actions.
- No Network Segmentation: Having developer workstations on the same flat network as production servers or sensitive data stores, allowing lateral movement after an initial breach.
- Ignoring EDR/AV Alerts: Dismissing warnings about PowerShell scripts or unusual process injections (like into
grpconv.exe) as false positives.
Best Practices (The Do's)
- Implement a Vetting Policy: Establish a process where all third-party tools and extensions must be reviewed and approved by a security or lead engineer before use. Maintain an internal "allow list."
- Adopt the Principle of Least Privilege (PoLP): Developers should use standard user accounts. Use a separate, privileged access management (PAM) solution for tasks requiring admin rights.
- Deploy Advanced Endpoint Protection: Use Endpoint Detection and Response (EDR) tools that can detect suspicious behavior (e.g., memory injection, headless browser launches) rather than just file signatures.
- Segment Development Networks: Isolate developer environments from corporate and production networks. Use jump boxes or zero-trust network access (ZTNA) for accessing critical resources.
- Enforce Regular Updates and Patching: Keep VS Code, extensions, and the underlying OS updated to mitigate vulnerabilities that could be exploited in later stages of an attack.
Technical Controls Checklist
- Enable PowerShell Logging: Configure your endpoints to log all PowerShell activity (ScriptBlock Logging, Module Logging) and feed these logs to a SIEM for analysis. This can catch the initial download command.
- Configure Application Allowlisting: Use tools like AppLocker or Windows Defender Application Control to restrict which processes can run. You can block unexpected processes like
grpconv.exefrom performing network calls or spawning other processes. - Monitor for Unusual Outbound Connections: Set up network monitoring to alert on outbound FTP connections or connections to suspicious, newly registered domains like the C2 server used by Evelyn (
server09.mentality[.]cloud). - Use a Password Manager & Hardware Wallets: Encourage the use of dedicated password managers instead of browser-stored passwords. For cryptocurrency, use hardware wallets that do not expose private keys to the computer's file system.
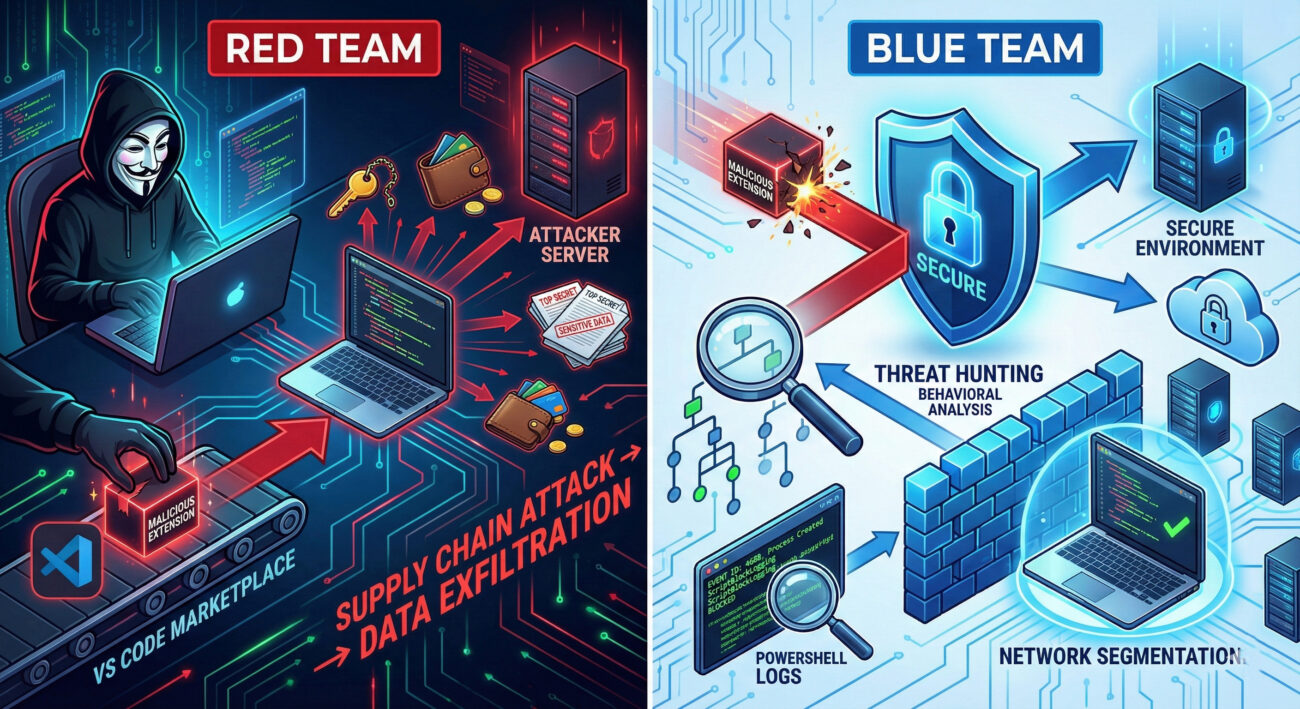
Red Team vs. Blue Team Perspective
Understanding both sides of the cyber battlefield sharpens defenses. Here’s how Red Teams (attackers) and Blue Teams (defenders) view the Evelyn Stealer campaign.
Red Team (Threat Actor) View
Objectives: Gain initial access to developer machines, establish persistence, exfiltrate credentials and source code, and potentially move laterally to high-value internal targets.
Why This Attack is Appealing:
- High Trust, Low Scrutiny: VS Code extensions are a soft target because they are often installed casually without security review.
- Access to Goldmines: Developer workstations are treasure troves of credentials (to GitHub, AWS, Azure), proprietary code, and internal documentation.
- Effective OPSEC: Using fileless injection and legitimate processes (
grpconv.exe) provides excellent operational security against traditional AV. - Multiple Exploitation Paths: Stolen data can be used for direct financial gain (crypto), sold on dark web forums, or leveraged in a larger, targeted attack against the organization.
Blue Team (Defender) View
Objectives: Prevent initial infection, detect anomalous behavior early, contain the breach, eradicate the threat, and learn to improve defenses.
Key Detection & Response Opportunities:
- Extension Telemetry: Monitor for the installation of extensions from unknown publishers or with very low install counts. VS Code itself provides telemetry that can be logged.
- Process Injection Alerts: EDR tools should be tuned to flag the injection of code into system binaries like
grpconv.exe, which is not its normal behavior. - PowerShell Anomalies: Detect PowerShell instances launched by VS Code or other unusual parent processes that are downloading and executing code from the internet.
- Headless Browser Execution: Create security rules to alert on browser processes launched with a long string of disabling flags (
--no-sandbox,--headless), especially if they are not initiated by user interaction.
Frequently Asked Questions (FAQ)
1. How can I check if I have installed a malicious VS Code extension?
Go to the Extensions view in VS Code (Ctrl+Shift+X). Review the list for any extensions you don't recognize, especially from publishers you don't trust. Look for the specific malicious ones named in reports: "Theme for monkeytype", "Codo AI", or any from the publisher "BigBlack". Immediately uninstall any suspicious extensions. You can also check the official VS Code security guide for more tips.
2. Is the official VS Code Marketplace not safe?
While Microsoft has security checks, they are not foolproof. The marketplace operates on a scale that makes perfect screening impossible. It is a curated repository, not a guaranteed safe space. The responsibility ultimately falls on users and organizations to vet extensions before installation, similar to mobile app stores. Always check the publisher, reviews, download count, and the extension's source code repository if available.
3. What makes developers such high-value targets for attacks like Evelyn Stealer?
Developers hold the "keys to the kingdom." Their machines often contain:
- Access Tokens & Keys: SSH keys, API tokens for cloud services (AWS, GitHub, Docker), and database credentials that are frequently stored locally for convenience.
- Proprietary Source Code: Intellectual property that can be stolen for espionage or to find vulnerabilities in the company's products.
- Network Position: Developer workstations are usually well-connected inside corporate networks, making them perfect jump-off points for attackers to move laterally to more sensitive systems like build servers, code repositories, or production environments.
4. Can traditional antivirus software detect Evelyn Stealer?
Signature-based antivirus may eventually detect known variants of the downloader DLL or payload files. However, due to its use of fileless techniques (injecting into grpconv.exe), polymorphic code (changing its decryption routine), and legitimate system tools (PowerShell), it can easily evade traditional AV. Behavior-based detection (provided by EDR/XDR platforms) that looks for the sequence of events, extension installs DLL, DLL calls PowerShell, PowerShell injects into system binary, is far more effective. Resources like the MITRE ATT&CK Framework help defenders understand these behaviors.
Key Takeaways & Call to Action
The Evelyn Stealer campaign is a wake-up call for the entire software development industry. It demonstrates that threat actors are strategically shifting their focus to the tools and personnel at the heart of digital innovation. Trust in software supply chains can no longer be implicit; it must be earned and verified.
Summary of Critical Points:
- Vector: The attack abuses the trust in the VS Code extension ecosystem, a software supply chain vulnerability.
- Technique: It employs advanced, stealthy methods like fileless memory injection and headless browser manipulation to avoid detection.
- Target: Developers are targeted for their high-value access to credentials, code, and internal networks.
- Defense: Protection requires a mix of policy (extension vetting, least privilege), technology (EDR, PowerShell logging), and awareness.
Your Action Plan:
- Audit Now: Immediately review the extensions installed on your and your team's development machines. Remove anything unnecessary or from unverified publishers.
- Implement Controls: Advocate for and implement the technical controls discussed, starting with PowerShell logging and network segmentation for dev environments.
- Educate Your Team: Share this knowledge. Make security a part of your team's culture. The OWASP Top Ten is a great starting point for broader application security principles.
- Stay Informed: Follow trusted cybersecurity research sources to stay updated on new threats targeting developers.
The landscape of threats is constantly evolving, but with informed vigilance and proactive defenses, development teams can secure their environments and continue to innovate safely.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































