Gather Victim Identity Information (T1589)
Ultimate Guide to Gather Victim Identity Information: Attack & Defense
Gather Victim Identity Information is the foundational reconnaissance step where adversaries collect data like names, emails, job titles, and affiliations to enable and tailor their attacks.
ATT&CK ID T1589
Tactics Reconnaissance
Platforms PRE
Difficulty 🟢 Beginner
Prevalence High
Table of Contents
- Understanding Gather Victim Identity Information in Simple Terms
- Decoding the Jargon: Key Terms for Gather Victim Identity Information
- The Attacker's Playbook: Executing Gather Victim Identity Information
- The Defender's Handbook: Stopping Gather Victim Identity Information
- Building Resilience: Mitigation Strategies for Gather Victim Identity Information
- Gather Victim Identity Information Cheat Sheet
- Conclusion and Next Steps
Understanding Gather Victim Identity Information in Simple Terms
Imagine a thief planning to rob a house. They don't just pick a random door. First, they might watch the neighborhood, check which homes have expensive cars, look for mail with names on it, or see when people leave for work. Gather Victim Identity Information is the digital version of this "neighborhood watch."
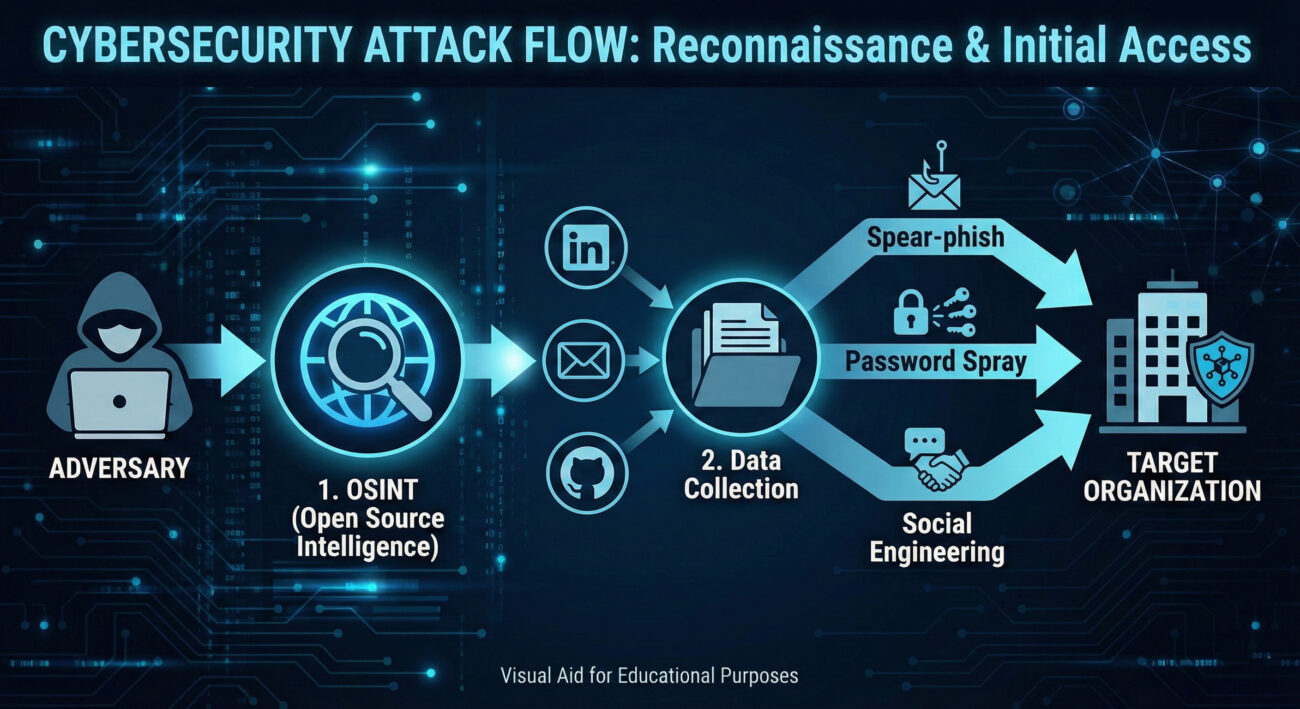
Before launching any spear-phishing email or password-spraying attack, adversaries need to know who they are targeting. This technique is all about collecting the digital "name tags" and "daily routines" of potential victims, names, email addresses, social media profiles, job roles, and professional connections. This information makes subsequent attacks dramatically more effective and convincing.
Decoding the Jargon: Key Terms for Gather Victim Identity Information
| Term | Simple Definition |
|---|---|
| OSINT (Open-Source Intelligence) | The practice of collecting information from publicly available sources. Think of it as using Google, social media, and public records to build a profile. |
| Reconnaissance (Recon) | The overall phase of gathering information before an attack. T1589 is a key part of this phase. |
| PII (Personally Identifiable Information) | Any data that can identify a specific individual (e.g., name, email, phone number, employee ID). This is the primary hacker's target in this technique. |
| Credential Stuffing | An attack enabled by this recon, where stolen usernames/passwords are tried on other sites. Knowing a person's email is the first step. |
| Spear-phishing | A highly targeted phishing attack. Effective spear-phishing is impossible without first gathering victim identity information like job title and colleagues' names. |
The Attacker's Playbook: Executing Gather Victim Identity Information
Step-by-Step Breakdown
This isn't a single action but a methodical process:
- Define the Target: Is it a specific company? A government agency? A particular department (like Finance or R&D)? The scope dictates the sources.
- Cast the Net (Passive Collection): Use search engines, social media (LinkedIn, Twitter, Facebook), professional forums (GitHub, Stack Overflow), company websites ("Our Team" pages), news articles, and public data breaches. Tools automate scraping this data.
- Enrich and Connect: Cross-reference found data. An email from a breach list can be linked to a LinkedIn profile, revealing job title, colleagues, and projects.
- Identify Attack Vectors: Based on the findings, choose the next step. Finding developer emails might lead to targeting their code repositories. Finding IT admin info might lead to phishing for network credentials.
Red Team Analogy & Mindset
Think of yourself as a private investigator hired to test a company's human firewall. Your job isn't to break in yet, but to build a comprehensive dossier on key individuals. The more details you have, the more believable your pretext will be. You're not looking for a zero-day exploit here; you're looking for the human element, names, relationships, habits, and digital footprints that can be leveraged.
Tools & Command-Line Examples
Attackers use a mix of manual sleuthing and automated OSINT tools.
- theHarvester: A classic tool for gathering emails, subdomains, and employee names.
- LinkedIn/Social Media Scrapers: Various tools (often shut down due to ToS violations) automate profile scraping to build org charts.
- Hunter.io & Phonebook.cz: Public services to find email addresses associated with a domain.
Example theHarvester Command:
theharvester -d "example.com" -b google,linkedin
# -d: Target domain
# -b: Data sources (Google search, LinkedIn)
# Output will list discovered emails and hosts.
Manual OSINT Example (LinkedIn Search): An attacker searches for "System Administrator at Example Corp," reviews the profile for skills, endorsements, and connections to other employees, then uses that info to craft a phishing email about a fake "IT Security Certificate" from a colleague they found.
Real-World Campaign Example
The Lazarus Group (APT38), a North Korean state-sponsored actor, is known for extensive reconnaissance. Before their infamous SWIFT network attacks and cryptocurrency heists, they spent considerable time gathering victim identity information on employees at financial institutions and crypto exchanges.
They used fake LinkedIn profiles posing as recruiters or tech professionals to connect with and gather intelligence on their targets, learning about roles, projects, and trust relationships to enable highly effective social engineering. This reconnaissance phase was critical to the success of their multi-million dollar attacks.
Reference: CISA Advisory on Lazarus Group (AA22-279A)
The Defender's Handbook: Stopping Gather Victim Identity Information
Blue Team Analogy & Detection Philosophy
You are the security manager of a secure corporate headquarters. You can't stop people from looking at your building from the public street (passive OSINT). However, you can:
- Control how much information is visible through the windows (public data).
- Train employees not to share internal schedules with strangers (awareness).
- Monitor for suspicious individuals taking excessive notes or pictures of employee badges (anomalous data gathering).
SOC Reality Check: What to Look For
Direct detection of passive OSINT is nearly impossible, it looks like normal web traffic. Your focus shifts to correlated indicators and post-reconnaissance activity.
- Alert Noise: You won't get a "Victim Info Gathered" alert. You'll see spikes in failed logins (password sprays) or the first successful phishing click, which are the *results* of this recon.
- Indirect Signals: Anomalous amounts of traffic to your corporate "About Us" or "Team" pages from a single IP or geographic location not associated with normal business. Multiple LinkedIn profile views from suspicious accounts reported by employees.
Threat Hunter's Eye: Practical Query
Hunt for early signs of targeted attacks by looking for reconnaissance patterns against your public web assets. The following KQL (Azure Sentinel/Microsoft Defender) query looks for a single external IP making requests to many different employee-oriented pages, which could indicate scraping.
// KQL Query: Hunting for Potential Web Scraping of Employee Info let timeframe = 24h; let targetPaths = dynamic(["/about", "/team", "/leadership", "/careers", "/contact", "/staff", "/people"]); Weblogs | where TimeGenerated >= ago(timeframe) | where ClientIP startswith "10." or ClientIP startswith "192.168." or ClientIP startswith "172." // Filter out internal IPs | where CsUriStem has_any (targetPaths) // Look for requests to pages likely containing PII | summarize DistinctPagesAccessed = dcount(CsUriStem), UserAgents = make_set(CsUserAgent), FirstSeen = min(TimeGenerated), LastSeen = max(TimeGenerated) by ClientIP, CsHost | where DistinctPagesAccessed >= 5 // Tune this threshold based on your site's normal traffic | project-rename Suspicious_IP = ClientIP, Target_Host = CsHost | order by DistinctPagesAccessed desc // This identifies external IPs accessing an unusual number of 'employee info' type pages, potentially mapping your organization.
Key Data Sources for Detection
- Web Server Logs: The primary source. Look for crawling patterns on specific directories.
- Network Proxies & Firewalls: Can show bulk requests from single sources to public-facing websites.
- Endpoint Detection & Response (EDR): Not for the passive recon, but for the next active step (e.g., a downloaded spear-phishing email).
- Identity & Authentication Logs: After recon, password sprays occur. These logs are where you'll see the first active attack attempts.
Building Resilience: Mitigation Strategies for Gather Victim Identity Information
Actionable Mitigation Controls
Since you can't block Google, mitigation is about hardening your public footprint and preparing for the inevitable follow-on attacks.
- Awareness & Training: Regularly train employees on oversharing PII on social media and professional networks. Teach them to identify suspicious connection requests and reporting procedures.
- Information Minimization: Audit your public-facing websites. Does the "Our Team" page need full names, direct email addresses, and precise job titles? Consider using role-based emails (security@) and more generic titles.
- Account Hardening: Implement strong password policies and MFA (Multi-Factor Authentication) universally. This directly counters credential-based attacks that follow recon.
- Digital Footprint Monitoring: Use services or conduct regular audits to see what information about your company and employees is available on paste sites, code repositories, and data breach databases.
Red vs. Blue: A Quick Comparison
| Attacker's Goal (Red Team) | Defender's Action (Blue Team) |
|---|---|
| Build a comprehensive target list of employees and their roles. | Minimize publicly available employee PII; use role-based contacts. |
| Discover corporate email naming conventions (e.g., [email protected]). | Implement MFA to make guessed/breached emails useless without the second factor. |
| Understand organizational structure for social engineering. | Conduct regular, realistic social engineering drills and awareness training. |
| Find old passwords in breach dumps to enable credential stuffing. | Enforce password filters to block previously breached passwords and monitor for authentication anomalies. |
Gather Victim Identity Information Cheat Sheet
Red Flag
Employees reporting a surge in connection requests from unknown "recruiters" or "industry peers" on LinkedIn, especially those asking detailed questions about projects or tools.
Blue's Best Move
Mandate MFA on ALL external-facing services (email, VPN, cloud apps) and conduct a quarterly "self-OSINT" audit to see what your company's public footprint looks like.
Hunt Here
In web server logs for scraping patterns and in authentication logs for the resulting password spray attacks that use the gathered email lists.
Conclusion and Next Steps
Gather Victim Identity Information (T1589) is the quiet, often undetectable first move in a long-chain cyber attack. While you cannot prevent it outright, understanding its methodology is crucial for building a proactive defense. By minimizing your public attack surface, hardening identity systems, and training your human layer, you can significantly raise the cost and complexity for the adversary, potentially causing their campaign to fail at this earliest stage.
Your Action Plan:
- Conduct a Self-OSINT Exercise: Spend 30 minutes trying to find employee names, emails, and org structure for your own company online. You'll be surprised at what you find.
- Review MFA Coverage: Is it enabled on every possible user account, especially for cloud email?
- Practice Related Techniques: Study the techniques that follow T1589, such as Phishing for Initial Access and Credential Stuffing Attacks.
Further Reading from Authoritative Sources:
Gather Victim Identity Information
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026
- No Comments


















































