GlobalProtect DoS Vulnerability
GlobalProtect VPN Flaw Exposes Networks to DoS Attacks Explained Simply
Table of Contents
- Executive Summary: The Urgent Patch Alert
- Vulnerability Breakdown: Anatomy of CVE-2024-0020
- Attack Mechanism: How the DoS Exploit Works
- MITRE ATT&CK Mapping: Classifying the Threat
- Real-World Scenario: Potential Attack Impact
- Red Team vs. Blue Team Perspective
- Step-by-Step Mitigation Guide
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call-to-Action: Your Security Checklist
In January 2026, Palo Alto Networks urgently patched a critical denial-of-service (DoS) vulnerability in its GlobalProtect VPN, tracked as CVE-2024-0020. This flaw highlights the constant need for vigilance in perimeter security. Understanding this GlobalProtect VPN DoS vulnerability is crucial for cybersecurity professionals, students, and beginners alike to protect their organizational gateways.
Executive Summary: The Urgent Patch Alert
CVE-2024-0020 is a critical severity (CVSS score pending) vulnerability affecting Palo Alto Networks' GlobalProtect VPN, a cornerstone of remote access security for countless enterprises. An unauthenticated attacker could send specially crafted network packets to a vulnerable GlobalProtect gateway, causing it to crash and become unresponsive. This creates a complete denial-of-service condition, blocking all remote access for employees and potentially disrupting business operations.
The patch was released as part of Palo Alto's standard security advisories. The vulnerability impacts specific versions of PAN-OS (the operating system for Palo Alto firewalls) when the GlobalProtect gateway feature is enabled. Immediate action is required to assess your exposure and apply the necessary updates.
Vulnerability Breakdown: Anatomy of CVE-2024-0020
At its core, CVE-2024-0020 is a classic resource exhaustion vulnerability. It resides in the component of the GlobalProtect service that parses incoming connection requests. By sending a flood of malformed packets designed to trigger a specific, unhandled condition, an attacker can cause the service to consume 100% of available CPU or memory resources.
Think of it like a receptionist (the GlobalProtect service) who follows a complex script. An attacker shouts a confusing, nonsensical question in a loop. The receptionist, having no protocol for this, gets stuck trying to process it, ignoring all other legitimate visitors. The system's stability crumbles under the weight of these malicious requests.
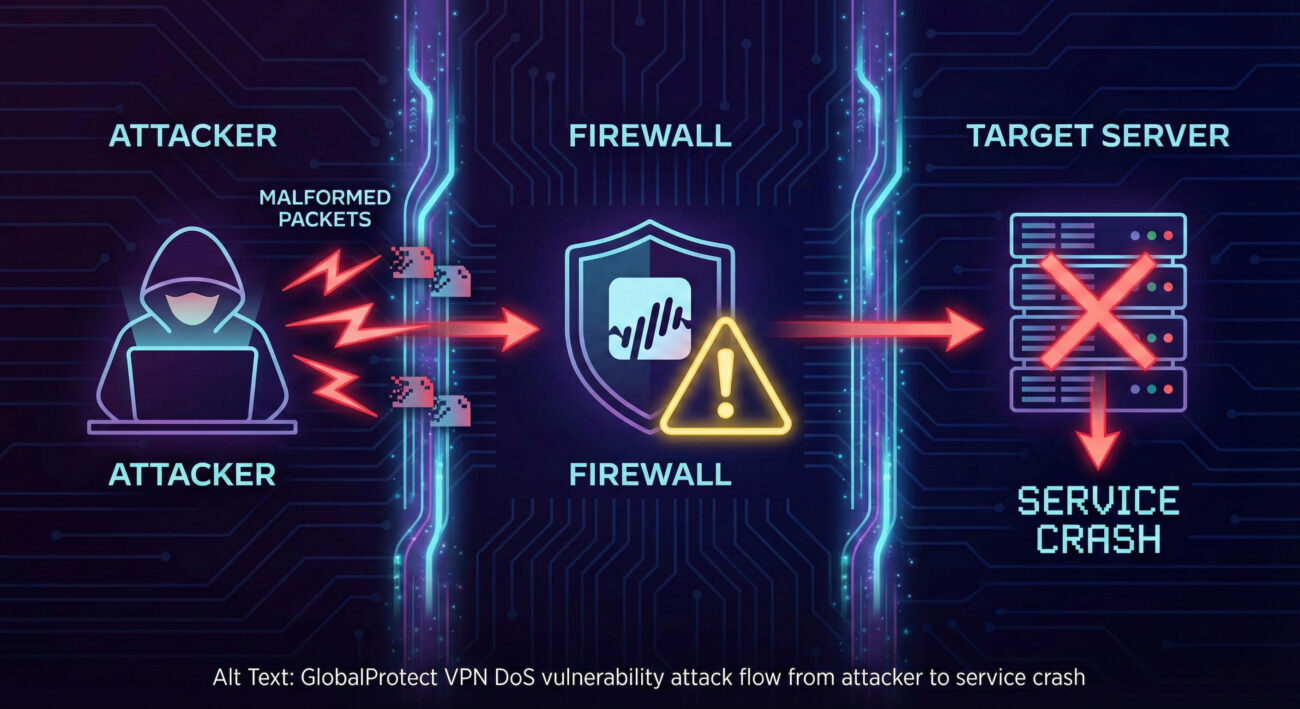
Attack Mechanism: How the DoS Exploit Works (Technical Perspective)
For those seeking a deeper technical understanding, here's how the exploit likely functions. The vulnerability is in the packet processing logic. The attacker doesn't need to authenticate; they simply need network reachability to the GlobalProtect service port (typically UDP 4501 for IPSec).
Step-by-Step Attack Flow:
Step 1: Reconnaissance
The attacker scans the target network to identify Palo Alto firewalls with the GlobalProtect portal/gateway exposed to the internet.
Step 2: Crafting the Malicious Payload
Using publicly disclosed details or reverse engineering, the attacker crafts network packets that violate the expected protocol. This could involve invalid headers, unexpected sequences, or oversized payloads designed to trigger a parsing error.
Step 3: Launching the Attack
The attacker sends a sustained stream of these malformed packets to the target IP on port 4501. A single packet might not cause the crash, but a flood of them overwhelms the service thread.
Step 4: Service Degradation and Crash
The GlobalProtect service enters an error-handling loop or attempts to allocate memory for each invalid packet, exhausting system resources (CPU/RAM). Legitimate user connections are queued or dropped, leading to a full DoS.
MITRE ATT&CK Mapping: Classifying the Threat
Mapping this vulnerability to the MITRE ATT&CK framework helps defenders understand its place in the adversary's playbook and plan detection strategies.
| MITRE ATT&CK Tactic | MITRE ATT&CK Technique | Description & Relevance to CVE-2024-0020 |
|---|---|---|
| Impact | T1499: Endpoint Denial of Service | This is the primary tactic. The attack aims to deny availability of the GlobalProtect VPN service, impacting business operations. |
| Impact | T1498: Network Denial of Service | The attack targets a network service (GlobalProtect), flooding it to exhaust resources. |
| Initial Access | T1190: Exploit Public-Facing Application | The attacker exploits the vulnerable, internet-facing GlobalProtect service to gain initial "access" in the form of causing a crash. |
Understanding this mapping allows Blue Teams to focus monitoring on network traffic spikes to VPN endpoints and system resource alerts on their firewalls.
Real-World Scenario: Potential Attack Impact
Imagine a mid-sized financial firm, "SecureBank Inc.," with 500 employees working remotely. Their Palo Alto firewall with GlobalProtect is the only remote access solution.
- Day 1, 9:00 AM: A competitor or hacktivist group discovers SecureBank's vulnerable VPN gateway.
- Day 1, 9:05 AM: They launch the CVE-2024-0020 exploit. The firewall's CPU spikes to 100%.
- Day 1, 9:10 AM: Remote employees start getting connection timeouts. The IT help desk is flooded with calls.
- Day 1, 9:30 AM: All remote access is dead. Trading, customer support, and internal operations are severely disrupted.
- Day 1, 10:00 AM+: IT struggles to diagnose the issue. They may need to physically access or hard-reboot the firewall, causing extended downtime and significant financial/reputational loss.
Red Team vs. Blue Team View
Red Team (Attacker) Perspective
- Objective: Disrupt operations, cause chaos, or serve as a smokescreen for a different attack.
- Tooling: Simple Python/Scapy scripts to generate malformed IPSec packets. Low sophistication required.
- Advantage: No authentication needed. High impact with minimal effort. Ideal for hacktivists.
- Risk: High-volume packet floods are easily detectable by network monitoring tools.
Blue Team (Defender) Perspective
- Objective: Maintain service availability, detect anomalous traffic, and patch swiftly.
- Detection: Monitor for spikes in UDP 4501 traffic, firewall CPU alerts, and failed VPN connection logs.
- Mitigation: Immediate application of the vendor patch. Implement rate-limiting on the VPN interface as a temporary workaround.
- Strategy: Defense-in-depth. Don't rely solely on the VPN firewall; have secondary access methods for admins.
Step-by-Step Mitigation Guide
Follow this actionable guide to protect your organization from the GlobalProtect VPN DoS vulnerability.
Step 1: Identify Affected Systems
Log into your Palo Alto Panorama or individual firewalls. Check the PAN-OS version and confirm if GlobalProtect Gateway is configured. Refer to the official Palo Alto Security Advisory for the exact vulnerable versions.
Step 2: Apply the Patch
Download and install the fixed version of PAN-OS as recommended by Palo Alto. Always test updates in a staging environment first. Schedule a maintenance window for production deployment.
Step 3: Implement Compensating Controls (If Patching is Delayed)
If you cannot patch immediately:
- Restrict Access: Use firewall rules to limit source IPs that can connect to the GlobalProtect gateway to known, trusted networks (e.g., corporate IP ranges).
- Rate Limiting: Configure DoS protection policies on the firewall to limit connections per second to the VPN service.
- Monitoring: Enhance logging and set aggressive alerts for resource utilization on the firewall.
Step 4: Verify and Monitor
After patching, verify the GlobalProtect service is functioning. Continue to monitor traffic and system health logs for any anomalous patterns that might indicate an attack attempt.
Common Mistakes & Best Practices
Common Mistakes (What to Avoid)
- Ignoring Patch Tuesday: Letting security advisories pile up without review.
- Exposing VPN to 0.0.0.0/0: Having no IP-based restrictions on the public-facing VPN interface.
- No Staging Environment: Applying major PAN-OS updates directly to production firewalls.
- Single Point of Failure: Relying on one firewall/VPN for all remote access without a backup plan.
- Weak Monitoring: Not alerting on firewall CPU spikes or anomalous UDP traffic volumes.
Best Practices (What to Do)
- Proactive Patching: Establish a formal, regular patch management cycle for all security appliances.
- Principle of Least Privilege (Network): Restrict VPN access by source IP where possible.
- Defense in Depth: Implement multi-factor authentication (MFA) and consider a backup VPN solution.
- Robust Monitoring: Use SIEM tools to correlate firewall logs, netflow data, and performance metrics.
- Regular Vulnerability Scans: Use tools like Nessus or Qualys to scan your external perimeter for known vulnerabilities.
Frequently Asked Questions (FAQ)
Q1: Is this vulnerability being actively exploited in the wild?
At the time of the advisory, Palo Alto Networks stated there were no known exploits. However, once a patch is released, attackers reverse-engineer it to create exploits. It is critical to assume active exploitation will begin soon and patch urgently.
Q2: I'm not using GlobalProtect. Am I still vulnerable?
No. The vulnerability only exists if the GlobalProtect gateway (portal) feature is enabled and configured on your Palo Alto firewall. You can verify this in the network interface configuration.
Q3: What's the difference between DoS and a data breach here?
This is a pure Denial-of-Service (DoS) flaw. It crashes the service but does not allow the attacker to steal data, infiltrate the network, or execute code. The impact is availability, not confidentiality or integrity.
Q4: Where can I learn more about Palo Alto security?
Bookmark the official Palo Alto Networks Security Advisories page. For broader cybersecurity education, resources like SANS Blog and NIST Guidelines are invaluable.
Key Takeaways
- CVE-2024-0020 is a critical DoS vulnerability in Palo Alto GlobalProtect VPN that can shut down remote access.
- The attack is low-complexity, requires no authentication, and has high impact on availability.
- It maps to MITRE ATT&CK tactics Impact (T1499) and Initial Access (T1190).
- Immediate patching is the primary mitigation. Compensating controls include source IP restriction and rate limiting.
- This flaw underscores the non-negotiable importance of a consistent, tested patch management process for all perimeter security devices.
Call-to-Action: Your Security Checklist
Don't be the next headline. Use this checklist to secure your network today:
- ✅ Inventory: List all your Palo Alto firewalls and their PAN-OS versions.
- ✅ Assess: Check the advisory to see which ones are vulnerable and have GlobalProtect enabled.
- ✅ Plan: Schedule patches for your staging environment immediately, then for production.
- ✅ Harden: Implement IP allow-lists for your VPN gateway as a standard practice.
- ✅ Monitor: Configure alerts for firewall resource exhaustion and VPN connection failures.
For continuous learning, subscribe to vendor advisories and follow trusted cybersecurity news sources like The Hacker News or Krebs on Security.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































