IP Addresses (T1590.005)
Ultimate Guide to Gather Victim Network Information - IP Addresses: Attack & Defense
Gather Victim IP Addresses involves collecting the public IP addresses associated with a target organization to map their external network presence, identify potential entry points, and plan subsequent attacks.
ATT&CK ID T1590.005
Tactics Reconnaissance
Platforms PRE
Difficulty 🟢 Easy
Prevalence High
Table of Contents
- Understanding Gather Victim IP Addresses in Simple Terms
- Decoding the Jargon: Key Terms for Gather Victim IP Addresses
- The Attacker's Playbook: Executing Gather Victim IP Addresses
- The Defender's Handbook: Stopping Gather Victim IP Addresses
- Building Resilience: Mitigation Strategies for Gather Victim IP Addresses
- Gather Victim IP Addresses Cheat Sheet
- Conclusion and Next Steps
Understanding Gather Victim IP Addresses in Simple Terms
Imagine you're planning a heist on a secure corporate building. Before you even think about picking a lock, you'd spend days observing. You'd note the guard patrol schedules, the delivery truck routes, which doors are used by employees, and where the security cameras are blind spots. This is passive, legal observation from a distance.
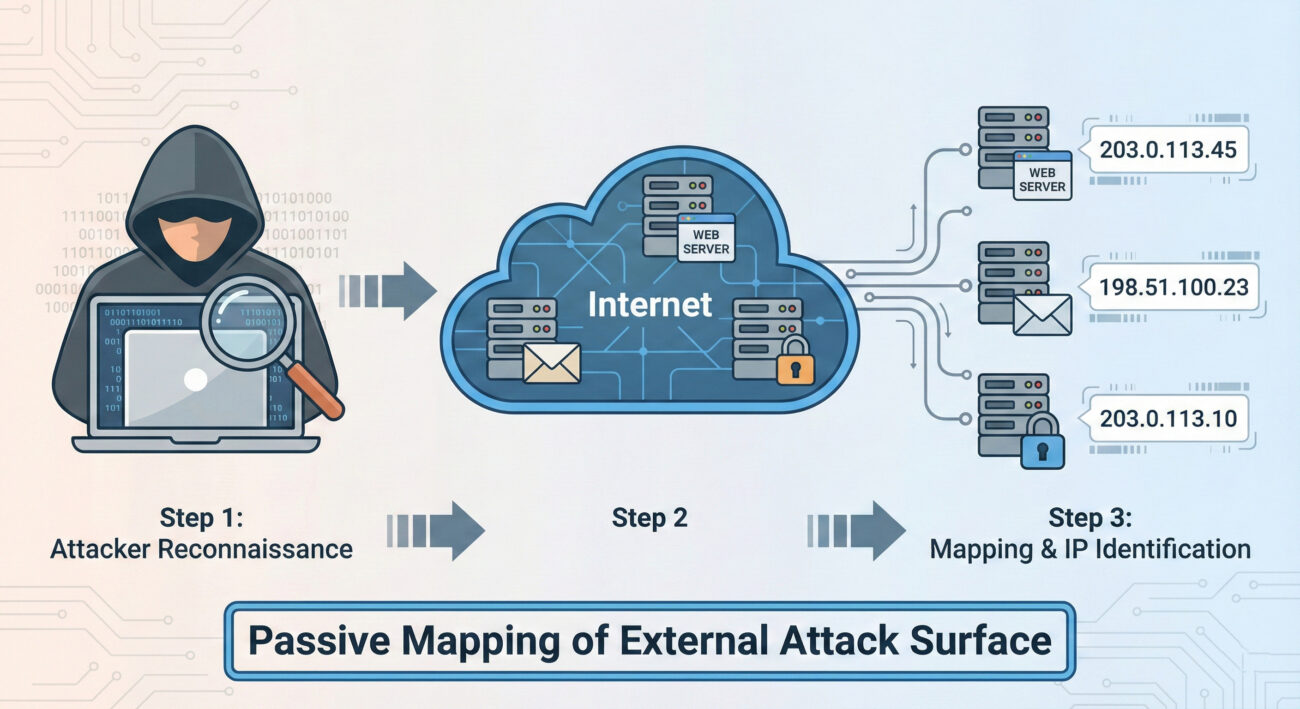
Gather Victim IP Addresses is the digital equivalent of this initial surveillance. Before any malware is sent or any exploit is attempted, an attacker needs to map out your organization's digital "building." They need to find all the public-facing doors and windows, your web servers, email servers, VPN gateways, and any other internet-connected assets, each identified by its unique IP address. This step is foundational, cheap, and often goes completely unnoticed by the target.
Decoding the Jargon: Key Terms for Gather Victim IP Addresses
| Term | Simple Definition | Why It Matters Here |
|---|---|---|
| IP Address (Internet Protocol Address) | A unique numerical label assigned to every device connected to a network (like the internet). It's the digital equivalent of a street address. | This is the primary data point the adversary is collecting. It's the identifier for your organization's online assets. |
| Passive Reconnaissance | Gathering information without directly interacting with the target's systems. Think: reading public records, not knocking on the door. | Gather Victim IP Addresses is almost exclusively passive. It uses publicly available data, making it hard to detect and completely legal. |
| Autonomous System Number (ASN) | A unique number assigned to a large network or ISP (like a "neighborhood" on the internet). Blocks of IP addresses belong to specific ASNs. | Attackers can query an organization's ASN to find ALL IP ranges registered to them, massively speeding up the discovery process. |
| BGP (Border Gateway Protocol) | The "postal system" of the internet that determines how data packets are routed between large networks. | Public BGP routing tables are a goldmine for discovering which IP ranges are announced (owned) by a specific organization. |
| Attack Surface | The total sum of all possible points (like IPs, domains, apps) where an unauthorized user can try to enter your digital environment. | Each discovered public IP address represents a potential entry point, thus expanding the known attack surface. |
The Attacker's Playbook: Executing Gather Victim IP Addresses
Step-by-Step Breakdown
A systematic attacker doesn't just guess IPs. They follow a logical, layered process to build a comprehensive map.
- Start with the Obvious: Use the organization's known website domain. Simple DNS lookups (like `nslookup` or `dig`) reveal the primary web server IPs.
- Find the Network "Neighborhood" (ASN): Use tools like
whoisor online databases to find the ASN(s) registered to the target company or their ISP. - Enumerate the IP Range: Query public BGP databases (e.g., BGPView, Hurricane Electric BGP Toolkit) to list ALL IP address blocks associated with the discovered ASN. This often reveals forgotten or shadow IT infrastructure.
- Expand via Passive DNS: Services like SecurityTrails or VirusTotal Passive DNS show historical and current DNS records, linking more domains and subdomains to the discovered IPs, which may lead to discovering more IPs.
- Scan & Fingerprint: With a target list of IPs, perform light, non-intrusive scans (e.g., TCP SYN to port 443) to verify which IPs are live and what service might be running, without triggering aggressive alarms.
Red Team Analogy & Mindset
Think like a real estate developer scouting a city block. You don't just look at the building you're interested in. You pull all the public property records (ASN/BGP), you note every structure on the block (IP range), you see which ones have lights on at night (live hosts), and you observe traffic patterns to and from each building (passive DNS). Your goal isn't to break in yet, it's to create the most accurate map possible so you can plan the most effective entry point later. Every piece of data is a potential vulnerability: an old, unmaintained building (legacy server) is a more attractive target than a new, secure skyscraper (modern, patched web server).
Tools & Command-Line Examples
- AMass / Subfinder: Passive enumeration tools that aggregate data from dozens of public sources to find subdomains and their associated IPs.
- Shodan / Censys: Search engines for internet-connected devices. An attacker can search by organization name, ASN, or netblock to find devices, open ports, and service banners.
- BGP Tools (bgp.he.net): Web-based interfaces to query which IP prefixes are announced by an ASN.
Command-Line Snippet (Example - Passive Discovery):
# Step 1: Get ASN for target company (using whois)
whois -h whois.radb.net ' -i origin ACME-CORP' | grep -E "route:|route6:"
# Step 2: Use the ASN (e.g., AS12345) to get all IP ranges via a BGP tool (curl example)
curl -s "https://api.bgpview.io/asn/12345/prefixes" | jq '.data.ipv4_prefixes[].prefix'
# Step 3: Passive subdomain enumeration linked to IPs (using amass)
amass enum -passive -d acme-corp.com -o subdomains.txt
Real-World Campaign Example
The APT29 (Cozy Bear, associated with Russian intelligence) is a master of extensive reconnaissance. In campaigns targeting government and think-tank networks, their initial activity heavily involves gathering victim IP addresses and network information. They use this data to identify targets for later spear-phishing campaigns and to tailor their malware infrastructure to blend in with the victim's environment.
Source: For detailed analysis, see the joint advisory from CISA and partners: "Advanced Persistent Threat Compromise of Government Agencies, Critical Infrastructure, and Private Sector Organizations" which details APT29's reconnaissance tradecraft.
The Defender's Handbook: Stopping Gather Victim IP Addresses
Blue Team Analogy & Detection Philosophy
You can't stop someone from looking at your public property records. The defense isn't about preventing the reconnaissance; it's about managing your attack surface. Think like a security-conscious property manager. Your job is to ensure that every public-facing door (IP address) is documented, necessary, and as secure as possible. You regularly audit your property portfolio (IP inventory) to find and decommission forgotten sheds in the back (unused public IPs). You assume the adversary has your map, so you focus on fortifying the doors they'll find.
SOC Reality Check: What to Look For
Direct detection of passive IP gathering is nearly impossible, no logs are generated on your end. The blue team's focus shifts to the next steps and managing exposure.
- Noise vs. Signal: You won't get an alert titled "Attacker Looked Up Your IP." The signal comes later: an increase in scanning activity from new sources against your IP ranges, or targeted phishing using the discovered infrastructure details.
- Actionable Intelligence: Correlate external threat intelligence feeds that might report your organization's IPs being queried in malware C2 infrastructure or discussed on underground forums.
Threat Hunter's Eye: Practical Query
While you can't see the IP lookup, you can hunt for the initial active probing that almost always follows. Here is a Sigma rule to detect scanning activity that maps to the Gather Victim IP Addresses and subsequent discovery phase.
# Sigma Rule: Reconnaissance - Mass Port Scan from Single Source
# Maps to ATT&CK: T1590.005 (Gather Victim IP Addresses) -> T1595 (Active Scanning)
# This rule looks for a single source IP hitting many different destination IPs on a common port (like 443) in a short time.
title: Mass Port Scan from Single Source
id: 7a8b9c0d-1e2f-4a3b-5c6d-7e8f9a0b1c2d
status: experimental
description: Detects a potential reconnaissance scan where one source connects to many distinct internal IPs on a specific port.
references:
- https://attack.mitre.org/techniques/T1590/005/
author: Blue Team Field Manual
date: 2024-05-17
logsource:
category: firewall
product: paloalto
detection:
selection:
action: allow
dst_port: 443
timeframe: 5m
condition: selection | count(dst_ip) by src_ip > 50
falsepositives:
- Legitimate security scanners
- CDN or cloud service traffic
level: low
Key Data Sources for Detection
- Firewall/Network Perimeter Logs: To detect the active scanning that follows IP gathering.
- DNS Query Logs: While passive DNS lookups can't be seen, monitoring for unusual internal DNS queries to your own domains might indicate an insider or compromised asset performing reconnaissance.
- External Threat Intelligence Feeds: Services that alert you if your company's IPs or ASN appear in suspicious contexts.
- Asset & Inventory Management Systems: Your authoritative source of truth for what public IPs you should have.
Building Resilience: Mitigation Strategies for Gather Victim IP Addresses
Actionable Mitigation Controls
Convert MITRE's general guidance into concrete actions your team can take.
- M1053: Data Minimization
- Action: Conduct quarterly attack surface discovery audits. Use tools like Shodan or Censys on your own organization. Compare the results with your CMDB. Decommission any public-facing asset (IP, server, service) that is unauthorized or no longer needed.
- M1056: Pre-compromise
- Action: Implement a rigorous change control process for public IP space. No new public IPs can be provisioned (in cloud or on-prem) without a ticket that auto-updates the central asset inventory.
- M1056: Vulnerability Scanning (Proactive Defense)
- Action: Run credentialed, non-intrusive vulnerability scans against your known public IP range weekly. Patch critical findings within SLA. This assumes the attacker has your map and is looking for the same vulnerabilities.
Red vs. Blue: A Quick Comparison
| Attacker Goal (Red Team) | Defender Action (Blue Team) |
|---|---|
| Find all public IPs belonging to the target. | Maintain a complete and accurate inventory of authorized public IPs. |
| Identify forgotten, unpatched servers in the IP range. | Perform regular attack surface audits to find and secure or decommission unknown assets. |
| Use IP info to tailor phishing lures or identify VPN endpoints. | Implement strong MFA on all external access points and conduct user awareness training. |
| Map the network to plan the next attack phase (Initial Access). | Assume the map is known; focus on hardening and monitoring all public-facing assets. |
Gather Victim IP Addresses Cheat Sheet
Red Flag
Your organization's IP ranges appearing in uncategorized or malicious threat intelligence reports. Sudden spikes in scanning traffic from diverse sources against your IP space, especially on common service ports (22, 443, 3389).
Blue's Best Move
Conduct a monthly "Google yourself" exercise. Use Shodan, Censys, and whois on your own company name and ASN. Any asset you find that isn't in your CMDB is a risk and must be addressed immediately. Encrypt and update relentlessly.
Hunt Here
Firewall logs for sources connecting to a high number (>50) of your internal IPs on the same port within a short timeframe (5-10 minutes). This is the active verification scan that follows passive IP gathering.
Learn More
• Official MITRE Page: T1590.005 - Gather Victim IP Addresses
• External Deep Dive: SANS Blog: Attack Surface Mapping Before the Attack
Conclusion and Next Steps
Gather Victim IP Addresses (T1590.005) is the quiet, foundational step of a modern cyber attack. You cannot stop it, but you can render it far less useful to the adversary. The defender's power lies in rigorous attack surface management, comprehensive asset inventory, and the assumption that your public IP map is already in the hands of threat actors.
Your Action Plan:
- Audit: This week, spend 30 minutes using a public tool like Shodan.io to search for your organization. Document any surprises.
- Inventory: Ensure your CMDB or asset management system is the single source of truth for public IPs.
- Hunt: Implement the Sigma rule or a similar query in your SIEM to baseline and then monitor for mass scanning patterns.
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026
- No Comments


















































