Beware: LastPass Alerts Users to Fake Maintenance Scams After Master Passwords
40 Powerful Lessons from the LastPass Phishing Attacks Explained Simply
A new, highly targeted wave of phishing attacks has security teams on high alert. In January 2026, LastPass issued a critical warning to its user base about a sophisticated campaign specifically designed to steal the one credential that protects all others: the master password. This isn't just another spam email; it's a calculated attack that preys on trust and urgency to compromise the very core of your digital security. Understanding this threat is essential for anyone, from cybersecurity beginners to seasoned professionals.
Table of Contents
- Executive Summary: Anatomy of a Targeted Phishing Campaign
- How the Attack Worked: A Step-by-Step Breakdown
- The Hacker's Playbook: MITRE ATT&CK Techniques at Work
- Red Team vs. Blue Team: Perspectives on the Attack
- Common Mistakes & Best Practices for Defense
- Implementation Framework: Building Your Defense
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: Anatomy of a Targeted Phishing Campaign
This series of phishing attacks represents a significant escalation in credential harvesting. Attackers sent convincing emails impersonating LastPass, claiming that urgent "infrastructure updates" or "maintenance" required users to create a local backup of their vaults within 24 hours. The goal was singular: to lure victims to a fake login page and harvest their master passwords. Giving up this password is the digital equivalent of handing a thief the master key to your entire house, not just the front door.
LastPass confirmed it would never ask for a user's master password. The campaign, starting around January 19, 2026, used subject lines like "LastPass Infrastructure Update: Secure Your Vault Now" to create a powerful sense of urgency. The emails directed users through a series of redirects, ultimately landing on a deceptive domain ("mail-lastpass[.]com") designed to look legitimate.

How the Attack Worked: A Step-by-Step Breakdown
Understanding the mechanics of these phishing attacks is the first step in building immunity against them. The attackers followed a refined, multi-stage process designed to bypass both technical filters and human skepticism.
Step 1: The Bait - Crafting the Urgent Email
The attack began with emails sent from seemingly official but fake addresses like [email protected]. The content leveraged powerful psychological triggers: authority (impersonating LastPass), urgency ("action required in 24 hours"), and fear (potential loss of data). By framing the request as a "backup" for the user's own protection, they masked their malicious intent.
Step 2: The Hook - The Multi-Layered Redirect
To evade simple link scanners, the emails contained links to intermediary domains, such as a benign-looking Amazon S3 bucket URL. This URL would then automatically redirect the victim to the final phishing domain. This layer of obfuscation makes the initial email appear less suspicious to automated security tools.
Step 3: The Net - The Deceptive Landing Page
Users landed on "mail-lastpass[.]com" – a domain chosen for its visual similarity to the real LastPass login pages. The site was likely a near-perfect clone, complete with logos, branding, and familiar layout, prompting the user to enter their email and, crucially, their master password.
Step 4: The Catch - Credential Harvesting & Pivoting
Once submitted, the credentials were sent directly to the attackers. With the master password in hand, they could potentially access the victim's entire vault if other security layers like two-factor authentication (2FA) were not enabled. This single credential becomes a gateway for further attacks, including identity theft and corporate network infiltration.
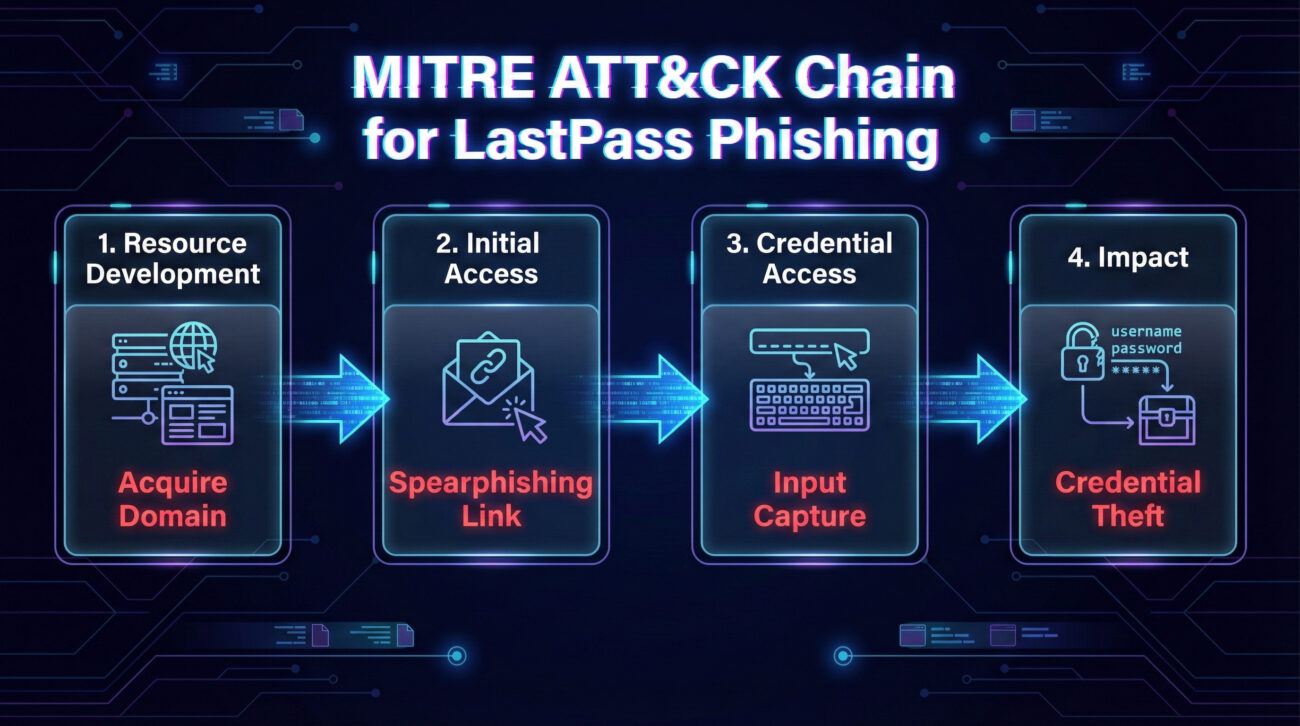
The Hacker's Playbook: MITRE ATT&CK Techniques at Work
This campaign can be mapped precisely to the MITRE ATT&CK® framework, a globally recognized knowledge base of adversary tactics. Mapping the phishing attacks this way helps defenders speak a common language and prepare systematic defenses.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It Was Used in This Attack |
|---|---|---|
| Initial Access | T1566: Phishing | The primary method to gain initial foothold. Spearphishing emails with malicious links were sent to a broad set of LastPass users. |
| Credential Access | T1589.001: Credentials from Password Stores | The ultimate objective. By stealing the master password, attackers aimed to harvest all credentials stored within the password manager vault. |
| Resource Development | T1583.001: Domains | Attackers registered deceptive domains (mail-lastpass[.]com) to host their phishing infrastructure and lend an air of legitimacy. |
| Defense Evasion | T1204.002: User Execution - Malicious Link | Relied on the user clicking the link in the email, requiring human interaction to bypass technical controls. |
Red Team vs. Blue Team: Perspectives on the Attack
Viewing an incident through both the attacker's (Red Team) and defender's (Blue Team) lenses provides complete strategic understanding. Here’s how each side would approach these phishing attacks.
The Red Team (Attackers') View
- Objective: Harvest high-value master passwords at scale.
- Targeting: Broad but focused on users of a specific, trusted service (LastPass). No need for complex reconnaissance when the target list is self-identifying.
- Exploitation: Exploit the immutable trust relationship between a user and their password manager. The service is so critical that users are more likely to comply with urgent requests.
- Infrastructure: Use disposable, widely-available infrastructure (like cloud storage buckets) for redirects. This makes takedowns less effective, as demonstrated when attackers shifted to new URLs within days.
- Success Metric: Number of credentials captured, especially those not protected by multi-factor authentication (MFA).
The Blue Team (Defenders') View
- Detection: Monitor for suspicious email patterns: sender addresses with odd subdomains (@lastpass.server8), keywords like "urgent backup," and links that redirect through unusual domains.
- Prevention: Implement and enforce DMARC, DKIM, and SPF email authentication protocols to make domain spoofing harder. Use endpoint/web security tools to block known phishing domains.
- User Education: This is the critical layer. Train users on the cardinal rule: "Your password manager will NEVER ask for your master password." Use this real-world example in security awareness training.
- Response: Have a clear process for users to report phishing emails. Work with takedown services to disable malicious domains swiftly, even knowing attackers may re-establish.
- Defense-in-Depth: Advocate for and enforce the use of MFA on all password manager accounts. This renders a stolen master password far less useful.
Common Mistakes & Best Practices for Defense
Even security-conscious individuals can fall victim to sophisticated phishing attacks. Here’s what to avoid and what to embrace.
Common Mistakes to Avoid
- Assuming legitimacy based on branding: Just because an email has correct logos and colors does not make it real. Attackers copy these effortlessly.
- Blindly clicking links in unsolicited emails: Hovering over a link to see the true destination (which will show in your browser's status bar) is a basic but vital habit.
- Complying with artificial urgency: Legitimate companies rarely demand immediate action on a 24-hour clock, especially for critical actions like backing up a password vault.
- Reusing your master password anywhere else: This password must be absolutely unique. If it's breached in another, unrelated incident, your vault is immediately compromised.
- Disabling multi-factor authentication (MFA): Treating MFA as an optional inconvenience is the biggest gift you can give a hacker.
Best Practices to Implement
- Adopt a "Zero-Trust" mindset with emails: Always verify. If in doubt, navigate to the service's website directly by typing the URL yourself, not by clicking a link.
- Use a password manager's built-in features: Many, like LastPass, have a "Trusted Devices" feature or browser extension that auto-fills credentials. If the extension doesn't auto-fill on a site, it's a huge red flag that you're on a phishing page.
- Enable the strongest available MFA: Use an authenticator app (like Google Authenticator or Authy) or a hardware security key (like a YubiKey) instead of SMS-based codes, which can be intercepted.
- Report suspicious emails: Use your email client's "Report Phish" button. This trains corporate filters and helps protect your colleagues.
- Bookmark the official login pages for critical services like your password manager, bank, and email. Always use the bookmark to access them.
Implementation Framework: Building Your Defense
For IT administrators and security leaders, here is a practical framework to protect your organization from similar phishing attacks targeting password managers.
Phase 1: Policy & Education (Week 1-2)
Establish a Clear Policy: Formally state that the company will never ask for credentials via email. Mandate the use of the corporate-approved password manager and enforce MFA on it.
Launch Targeted Training: Conduct a 15-minute training session using this LastPass case study as the primary example. Simulate a similar phishing email to test user awareness.
Phase 2: Technical Controls (Week 3-4)
Secure Email Gateways: Configure filters to flag or quarantine emails with suspicious characteristics: sender domain mismatches, urgent financial/password-related language, and links to newly registered domains.
Web Filtering: Deploy DNS or proxy-based web security that blocks access to known phishing domains and categories. Integrate threat intelligence feeds for real-time blocking.
Phase 3: Monitoring & Response (Ongoing)
Enable Advanced Monitoring: Use tools like a SIEM (Security Information and Event Management) to correlate login failures, MFA bypass attempts, and traffic to suspicious domains.
Create an Incident Response Playbook: Have a dedicated procedure for "Suspected Credential Phishing." This should include steps for credential reset, user re-education, and infrastructure takedown requests.
Frequently Asked Questions (FAQ)
Q1: I clicked the link but didn't enter my password. Am I safe?
A: Most likely, yes. The primary risk comes from entering and submitting your credentials. However, sophisticated attacks can sometimes exploit browser vulnerabilities just by visiting a page (a "drive-by download"). It's best to run a full antivirus scan, clear your browser cache, and remain vigilant for any unusual activity on your accounts.
Q2: How can I tell if a login page is real?
A: Check the URL in the address bar meticulously. The real LastPass login page is on a domain ending in "lastpass.com" (like "https://lastpass.com"). The phishing page used "mail-lastpass[.]com" – a subtle but critical difference. Also, a password manager browser extension that fails to auto-fill on a page where it normally does is a major warning sign.
Q3: What should I do if I accidentally gave away my master password?
A: Act immediately. Log in to your password manager from a trusted device using any saved session or by following the official "Forgot Password" process (which will require your account recovery options). Change your master password and your primary email account password. Review your vault for any unauthorized activity and enable or update your MFA settings.
Q4: Are other password managers vulnerable to similar attacks?
A: Absolutely. Any service that stores high-value credentials is a prime target for phishing attacks. The principles in this article apply universally: be suspicious of unsolicited, urgent requests; never share your master password; and always use MFA. You can read about general password security best practices from the U.S. Cybersecurity & Infrastructure Security Agency (CISA).
Key Takeaways & Call to Action
Key Takeaways
- The master password for your password manager is the ultimate key to your digital life. Guard it with your life.
- Legitimate companies like LastPass will never email you asking for this password. Any such request is a phishing attack.
- Attackers weaponize urgency and fear to bypass your rational judgment. Slow down and verify.
- Multi-factor authentication (MFA) is the most effective single layer of defense that can neutralize a stolen password.
- Security is a shared responsibility. Staying informed about active threats, like this one, is a critical part of your own defense.
Call to Action: Your cybersecurity posture is only as strong as your habits.
- Verify Your MFA: Go to your password manager account settings right now and ensure a robust form of MFA is enabled.
- Bookmark Official Sites: Create bookmarks for your critical services to avoid accidental navigation to fake sites.
- Share Knowledge: Forward this article or discuss its key points with your team, family, or friends. Awareness is collective defense.
- Stay Updated: Follow trusted security resources like Krebs on Security or The Hacker News to stay ahead of evolving threats.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































