Malicious Chrome Extension Threat
How Hackers Steal Crypto API Keys How to Stop Them
Imagine installing a simple tool to help with your crypto trading, only to find it’s a digital pickpocket that silently empties your wallet. This is the reality of a sophisticated attack recently uncovered by cybersecurity researchers. A malicious Chrome extension, masquerading as a helpful trading automator for the MEXC exchange, was caught programmatically stealing users' API keys with full withdrawal permissions. This incident is a masterclass in supply-chain attack vectors and highlights critical flaws in how we trust browser ecosystems. For cybersecurity professionals and crypto enthusiasts alike, understanding this threat is the first step in building effective defenses.
Table of Contents
Executive Summary: The API Key Heist
In early 2026, a malicious Chrome extension named "MEXC API Automator" was identified on the official Chrome Web Store. Its purported function was to help users automate trading on the MEXC cryptocurrency exchange by simplifying API key generation. In reality, it was a highly targeted credential-stealing tool.
The extension operated with surgical precision. Once installed, it lay dormant until a user visited MEXC’s specific API management page. It then activated, hijacking the user’s authenticated browser session to create a new API key with withdrawal permissions enabled, a critical detail it actively hid from the user’s view. The newly minted API key and secret were instantly exfiltrated to a threat actor-controlled Telegram bot. This gave the attacker persistent, long-lived access to the victim’s exchange account, independent of the user’s password or 2FA, enabling them to drain funds at their leisure.
Technical Breakdown: How the Malicious Chrome Extension Works
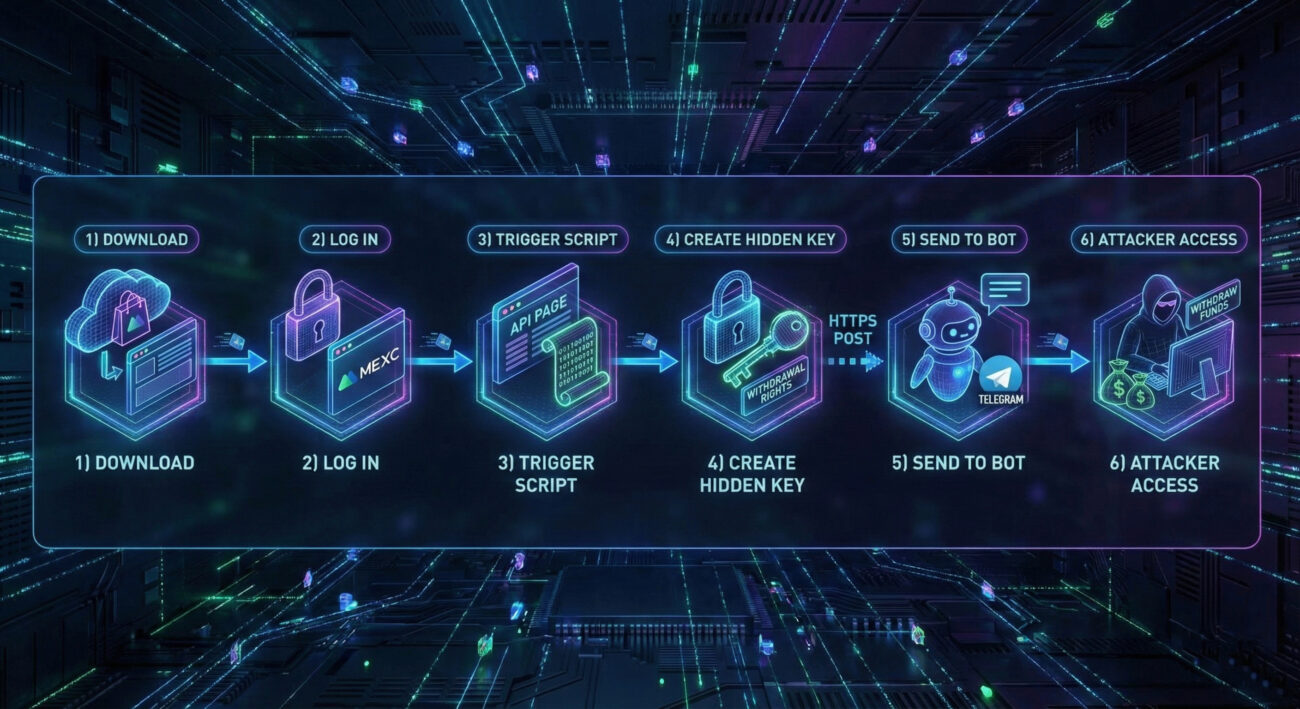
This attack is a clever blend of social engineering and technical exploitation. Let's dissect the step-by-step malware functionality.
Step 1: Deployment & Initial Infection
The threat actor publishes the "MEXC API Automator" extension on the official Chrome Web Store. This is a critical trust exploit, users assume the store is vetted. The extension description promises legitimate utility: automating API key creation for trading bots.
Step 2: Triggering the Payload
The extension's malicious code is packaged in a content script (e.g., script.js). It doesn't act immediately. It uses a condition check to wait for the perfect moment. The script constantly monitors the browser's active tab URL. The attack triggers only when the user navigates to the specific MEXC API management page, detected by the URL fragment /user/openapi. This ensures the user is already logged in, providing an active, authenticated session to hijack.
Step 3: Session Hijacking & Silent Key Generation
Once on the target page, the script injects itself into the page context. It then programmatically interacts with the MEXC web interface, mimicking a human user. Using JavaScript, it:
- Clicks the "Create New API Key" button.
- Programmatically checks the "Enable Withdrawal" permission checkbox.
- Executes a critical UI manipulation: It modifies the page's Document Object Model (DOM) to hide or uncheck the withdrawal permission visually, while the backend setting remains enabled. This is the heart of the deception.
- Clicks "Confirm" to generate the key.
Step 4: Data Exfiltration
As soon as the new API "Access Key" and "Secret Key" are displayed on the page, the script scrapes these values. It then sends them via a secure HTTPS POST request to a hardcoded command-and-control (C2) endpoint: a Telegram Bot API URL. Telegram provides the attackers with an anonymous, resilient, and easily accessible data collection point.
Step 5: Persistent Attacker Access
The user remains completely unaware. Even if they uninstall the extension moments later, the damage is done. The attacker now possesses a valid API key with withdrawal rights. This key acts as a long-lived backdoor, allowing the attacker to log into the victim's exchange account programmatically, bypassing all password and 2FA protections, to withdraw funds at any time until the key is manually revoked by the user.
This attack chain demonstrates a terrifying efficiency: it bypasses most traditional security controls (passwords, 2FA) by abusing the legitimate API system and the user's existing trust in their browser session.
Mapping to MITRE ATT&CK: The Adversary's Playbook
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques. This malicious Chrome extension campaign employs a clear sequence of techniques, providing a perfect case study.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It's Used in This Attack |
|---|---|---|
| Initial Access | T1472: Supply Chain Compromise | The attacker compromises the software supply chain by publishing a malicious extension on the trusted Chrome Web Store, a primary distribution point. |
| Execution | T1204.002: User Execution - Malicious File | The user is socially engineered to execute the threat by manually installing the malicious browser extension, believing it to be a legitimate tool. |
| Persistence | T1136: Create Account T1552.001: Unsecured Credentials - Credentials In Files |
Creation of a new, attacker-controlled API key establishes persistence. The stolen keys (credentials) are stored remotely by the attacker for long-term use. |
| Defense Evasion | T1552.008: Unsecured Credentials - API Keys T1564.001: Hide Artifacts - Hidden Window |
Stealing API keys bypasses standard authentication. The script hides the enabled withdrawal permission in the UI, concealing its malicious activity from the victim. |
| Credential Access | T1539: Steal Web Session Cookie T1555.003: Credentials from Password Stores |
By operating within an authenticated browser session, the script effectively hijacks the session. It then steals the newly generated API keys, which are credentials for programmatic access. |
| Exfiltration | T1041: Exfiltration Over C2 Channel | The stolen API keys are transmitted out of the victim's environment over an encrypted HTTPS channel to a Telegram Bot (the C2 server). |
| Impact | T1537: Transfer Funds | The ultimate goal and impact: using the stolen API keys to fraudulently transfer cryptocurrency out of the victim's exchange wallet. |
Understanding this ATT&CK mapping is crucial for defenders. It shifts the view from a single incident to a replicable pattern of behavior that can be hunted for and defended against systematically.
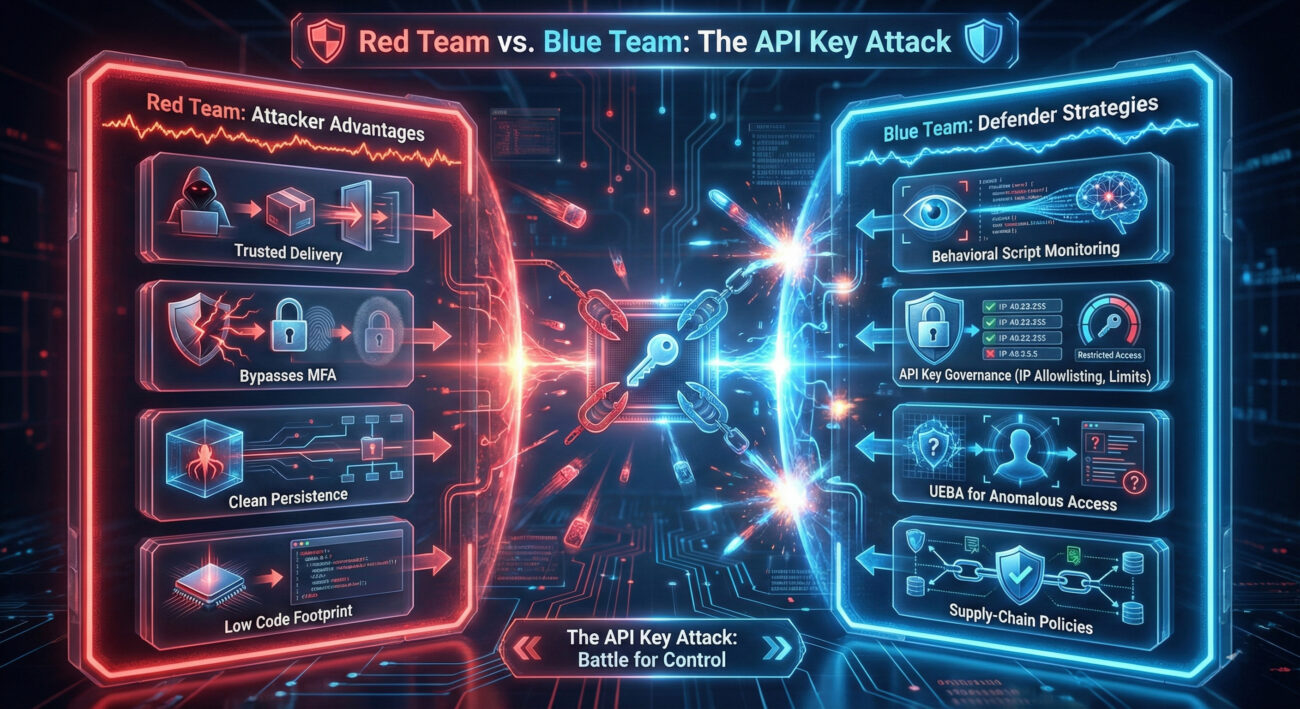
Red Team vs. Blue Team Perspective
The Red Team (Attacker) View
Objective: Steal cryptocurrency with low detection risk.
Why This Vector is Elegant:
- High Trust, Low Scrutiny: The Chrome Web Store provides a trusted delivery mechanism. Users and basic security tools often lower their guard for store-approved extensions.
- Bypasses Core Defenses: It completely circumvents password managers and multi-factor authentication (MFA) by targeting API keys generated after login.
- Clean Persistence: Access is tied to a revocable but often overlooked API key, not persistent malware on the OS. The attack remains effective even after the initial vector (the extension) is removed.
- Easy Obfuscation: The malicious code is minimal and triggers only on a specific site, making static analysis less likely to flag it as broadly malicious.
Future Evolution: Red teams predict future variants will target multiple exchanges, use heavier code obfuscation, and request broader browser permissions (like reading all site data) to maximize impact.
The Blue Team (Defender) View
Challenge: Defending against an attack that exploits trusted platforms and user behavior.
Key Detection & Prevention Points:
- Behavioral Monitoring: Detecting anomalous browser extensions that inject scripts into sensitive financial pages. Tools can monitor for DOM manipulation on specific URLs.
- API Key Governance: Implementing strict controls on exchange platforms: mandatory IP allowlisting for API keys, daily withdrawal limits, and alerting on the creation of new keys with high privileges.
- User & Entity Behavior Analytics (UEBA): Flagging instances where an API key is used from a geographical location or IP address radically different from the user's typical browser login.
- Supply-Chain Verification: Creating internal policies to vet and approve browser extensions before use in business or high-value personal contexts, treating the Web Store as an untrusted source.
Core Principle: The defense must shift from just securing the login to securing the entire post-authentication session and the credentials (API keys) generated within it.
A Practical Defense Framework: From Awareness to Action
Knowledge without action is insufficient. Here is a layered defense framework to protect yourself and your organization from similar supply-chain attacks targeting credentials.
Layer 1: Prevent Installation (The Human Firewall)
- Extreme Vetting of Extensions: Treat every browser extension as potentially malicious. Before installing, research the developer, read reviews critically, check the number of users (very low counts are a red flag), and scrutinize the permissions it requests. Ask: "Does this need to read and change data on *all websites*?"
- Use Official Sources, But Verify: While official stores are safer, they are not safe. Prefer extensions developed by well-known, reputable companies or open-source projects with active communities.
- Implement a Deny-List Policy: In organizational settings, use browser management tools (like Chrome Browser Cloud Management) to block the installation of extensions not on an approved list.
Layer 2: Limit Impact (The Technical Controls)
- Principle of Least Privilege for API Keys: When creating API keys on ANY exchange (MEXC, Binance, Coinbase, etc.), never enable withdrawal permissions unless absolutely necessary for your trading bot. For most automated trading, "Trade" permission is sufficient. This single step would have neutered this entire attack.
- Enable IP Allowlisting: Most exchanges offer the option to restrict API key usage to specific IP addresses. If your trading bot runs from a known server IP, configure this. It renders a stolen key useless from the attacker's location.
- Set Strict Withdrawal Limits: If withdrawal must be enabled, use the exchange's settings to impose a daily maximum withdrawal amount (in both currency and frequency). This turns a catastrophic drain into a limited, potentially detectable incident.
Layer 3: Detect & Respond (The Safety Net)
- Audit API Keys Regularly: Make it a weekly or monthly habit to review all active API keys in your exchange accounts. Immediately revoke any that are unknown, unused, or overly permissive.
- Monitor for Unfamiliar Activity: Enable all notification alerts offered by your exchange: logins from new devices, new API key creation, withdrawals, and large trades. Real-time alerts are your best early warning system.
- Use a Dedicated Environment: Consider using a separate, clean browser profile or even a virtual machine solely for accessing high-value financial accounts and trading. This limits the exposure to potentially compromised extensions in your daily-use browser.
Common Mistakes & Best Practices
| Common Mistake (The Risk) | Best Practice (The Defense) | Why It Matters |
|---|---|---|
| Installing browser extensions without research, trusting the Web Store implicitly. | Vet every extension. Check developer, reviews, permissions, and update history. Use browser settings to limit extensions to specific sites. | Prevents the initial infection vector. You are the most important firewall. |
| Creating API keys with "Withdrawal" permission enabled by default "just in case." | Apply the Principle of Least Privilege (PoLP). Only enable the specific permissions your bot needs (e.g., "Read" and "Trade"). | This is the single most effective technical control. A key without withdrawal rights cannot drain your wallet. |
| Never reviewing or cleaning up old, active API keys. | Schedule quarterly audits of all connected apps and API keys across all financial services. Revoke what you don't use. | Reduces your attack surface and cleans up potential lingering backdoors you've forgotten. |
| Using the same browser for daily browsing (with many extensions) and high-value financial activities. | Segment your activities. Use a dedicated, clean browser or a "Guest" profile for logging into exchanges and banks. | Contains the blast radius of a compromised extension. Malware in your main profile can't touch your financial session. |
| Relying solely on passwords and 2FA, assuming they fully protect your account. | Understand that API keys are powerful passwords. Secure them with the same rigor: IP restrictions, usage limits, and active monitoring. | Shifts security mindset to post-login credential management, which is where modern attacks are increasingly focused. |
Frequently Asked Questions (FAQ)
1. I've installed a suspicious extension. Just uninstalling it keeps me safe, right?
Wrong. This is the most dangerous misconception. Uninstalling the extension removes the threat actor's tool from your browser, but it does not revoke the API keys it may have already stolen. If those keys were created with withdrawal rights, the attacker still has access. You must immediately log into your exchange account, navigate to the API management section, and revoke all recently created or unfamiliar API keys.
2. Can antivirus or endpoint protection software detect this?
Traditional antivirus may struggle because the extension is a legitimate Chrome component from a trusted source. However, modern Endpoint Detection and Response (EDR) solutions could detect the malicious behavior, such as a browser process making anomalous network connections (to a Telegram API) or performing unusual DOM manipulation on a specific financial website. Behavioral detection is key here.
3. Are other browsers (Firefox, Edge, Safari) vulnerable to similar attacks?
Absolutely. While this specific incident targeted Chrome, the attack vector is universal. Firefox Add-ons, Microsoft Edge Extensions, and Safari Extensions galleries are all potential distribution points for similar malicious code. The same defensive principles apply across all browsers.
4. What's the role of the exchange (MEXC) in preventing this?
Exchanges can implement several protective measures:
- API Key Security Features: Making IP allowlisting and withdrawal limits mandatory or default options.
- Enhanced UI Protections: Implementing CAPTCHAs or additional confirmation steps for creating high-privilege API keys.
- User Education: Prominently warning users about the risks of third-party tools and browser extensions.
- Monitoring: Detecting and alerting on patterns like rapid API key creation followed by access from a different geographic region.
Key Takeaways & Call to Action
The "MEXC API Automator" incident is not an isolated event; it's a template for future attacks. It exploits the convergence of trust (in app stores), necessity (of API keys), and oversight (in post-authentication security).
Your Action Plan Starts Now:
- Audit Your Browser: Review your installed extensions today. Remove anything unfamiliar, unused, or from an unverified developer.
- Lock Down Your API Keys: Log into every crypto exchange and financial platform you use. Review every active API key. Revoke the unused ones. For the essential ones, disable withdrawal rights and enable IP allowlisting if possible.
- Enable Every Alert: Turn on all available notification alerts (email, SMS, authenticator app) for your financial accounts.
- Adopt a Security Mindset: Understand that in the modern threat landscape, security extends far beyond your password. Your browser extensions, session cookies, and API keys are all high-value targets that need active management.
For further reading on secure browsing and API security, consult these excellent external resources:
- OWASP Top Ten - The standard awareness document for web application security.
- MITRE ATT&CK® Framework - The comprehensive knowledge base of adversary tactics used in this analysis.
- CISA: Secure Our World - Foundational cybersecurity advice from the U.S. Cybersecurity & Infrastructure Security Agency.
- Krebs on Security - In-depth investigative cybersecurity journalism by Brian Krebs.
- UK NCSC: Phishing and Scams - Guidance on recognizing and avoiding social engineering attacks.
Stay vigilant, practice defense in depth, and remember: in cybersecurity, your habits are either your strongest shield or your weakest link.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































