Privilege Escalation
The Attacker's Critical Power Grab & How to Stop It
Privilege Escalation (TA0004)
The Attacker's Critical Power Grab & How to Stop It
Privilege Escalation is the art and science of turning a foothold of limited access into the keys to the kingdom. In plain English, it's when an attacker who has gotten "in the door" finds a way to grab more power, more permissions, and more control than they were originally supposed to have.
Why it matters: This tactic is the critical pivot point between a minor security incident and a catastrophic breach. Success here lets an attacker move from reading a single user's emails to stealing the entire customer database, deploying ransomware across the network, or sabotaging critical infrastructure. If defenders fail to detect and stop Privilege Escalation, the battle is often lost.
Table of Contents
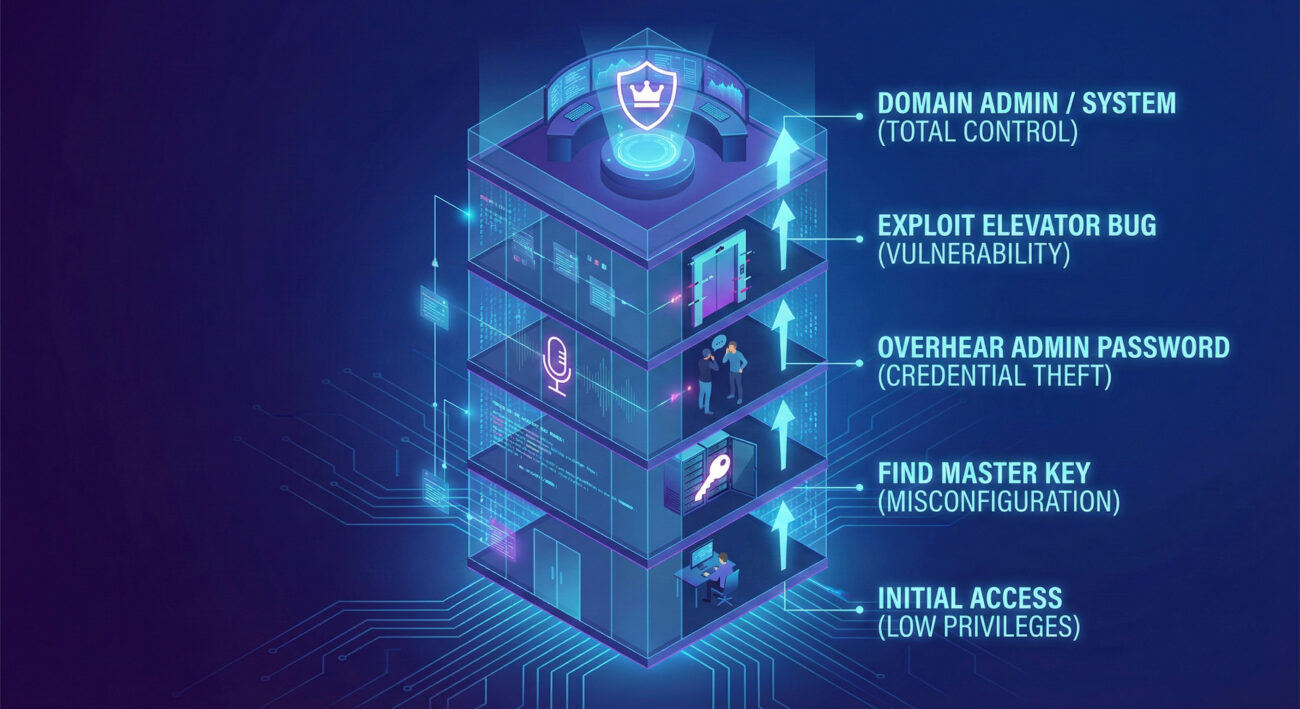
The Core Analogy: From Janitor to CEO
Imagine a sprawling corporate headquarters. An attacker doesn't start in the boardroom; they might slip in disguised as a delivery person or sneak in through an unlocked service entrance (Initial Access). They're now in the building, but they only have access to the mailroom or a hallway. They're a "low-privilege user."
Privilege Escalation is the process of that intruder finding ways to gain ever-higher levels of access. They might:
- Pick the lock on a manager's office to find a building master keycard left in a desk drawer (Exploiting Misconfigured Permissions).
- Eavesdrop on an IT admin's conversation in the cafeteria to learn the password to the server room (Credential Dumping/Theft).
- Find a set of elevator maintenance instructions that, if followed in a specific way, force the elevator to go straight to the penthouse executive floor (Exploiting a Software Vulnerability).
Their goal isn't just to be in the building it's to reach the server room, the CFO's office, or the boardroom where the real power resides. Every step up the privilege ladder unlocks new areas, sensitive information, and the ability to cause far greater damage.
Vocabulary Decoder Ring
Before we dive deeper, let's decode the essential jargon.
- Principle of Least Privilege (PoLP): The security best practice that users and systems should only have the minimum level of access needed to perform their function. Why it matters here: A perfect PoLP environment makes Privilege Escalation extremely difficult, acting as a fundamental barrier.
- Access Token: A digital key held by a Windows process that identifies the user, their groups, and their privileges. Why it matters here: Attackers often steal or manipulate these tokens to impersonate higher-privilege users without needing their password.
- Local Administrator: A user account with full control over a single computer or endpoint. Why it matters here: This is a common first major target for escalation, as it allows attackers to disable security software and dig for domain credentials.
- Domain Admin: A user account with full control over all computers and users in a Windows Active Directory domain. Why it matters here: This is often the "crown jewel" target of privilege escalation, granting control over the entire network.
- SYSTEM/NT AUTHORITY\SYSTEM: The highest privilege level on a Windows machine, even above local administrators. Why it matters here: Gaining SYSTEM privileges is a key objective for executing stealthy, powerful attacks on a compromised host.
The Attacker's Playbook (Red Team View)
The Intruder's Mindset: Finding the Master Keys
In our building analogy, the attacker is methodical and opportunistic. Their goal is clear: find the fastest, stealthiest path upward. The feeling is one of calculated progression each new privilege level is a victory that opens new avenues. They're looking for lax policies (keys left in drawers), trusted but vulnerable systems (the elevator with a bug), and careless users (the talking admin).
Common Techniques of Privilege Escalation
- T1548 - Abuse Elevation Control Mechanism: Exploiting built-in OS features like sudo (Linux) or User Account Control (Windows) to run code with higher privileges.
- T1555 - Credentials from Password Stores: Dumping saved passwords from browsers, email clients, or dedicated password managers.
- T1068 - Exploitation for Privilege Escalation: Leveraging a software bug (vulnerability) in the OS or an application to break out of a confined context.
- T1134 - Access Token Manipulation: Stealing or duplicating the access token of a higher-privilege process to impersonate it.
- T1078 - Valid Accounts: Using found or phished credentials for accounts that already have higher privileges (the simplest, most common form).
The Toolbox
Attackers have a suite of powerful tools: Mimikatz (the legendary credential dumper), PowerSploit/PowerUp (PowerShell scripts to find misconfigurations), and WinPEAS/LinPEAS (automated scripts that scour systems for escalation paths).
Command-Line Glimpse: Seeing is Believing
PS C:\> Invoke-AllChecks
# Checking for services with weak permissions that can be modified
ServiceName : VulnerableService
Path : "C:\Program Files\OldApp\service.exe"
ModifiablePath : @{ModifiablePath="C:\Program Files\OldApp"; IdentityReference="BUILTIN\Users"}
StartName : LocalSystem
# An attacker can replace service.exe with their malicious binary.
# When the service restarts, it runs as LOCAL SYSTEM (highest privilege).
PS C:\> sc stop VulnerableService
PS C:\> copy C:\Temp\malware.exe "C:\Program Files\OldApp\service.exe" /Y
PS C:\> sc start VulnerableService
The Defender's Handbook (Blue Team View)
The Security Guard's Perspective: Spotting the Imposter
You're monitoring the building's security cameras and access logs. You're not looking for a person in a black hoodie; you're looking for abnormal behavior. Why is the janitor's keycard being used at 3 AM to enter the server wing? Why did a standard user account just attempt to query the list of all domain admins? Your job is to connect these anomalous dots before the intruder reaches their final target.
SOC Reality Check: What You'll Actually See
In your SIEM, Privilege Escalation looks like a series of suspicious events:
- Windows Event ID 4688: A process spawned from an unexpected parent. "Parent Process: lsass.exe | Child Process: cmd.exe" - This screams credential dumping via Mimikatz.
- Windows Event ID 4672: A special privilege assigned to a new logon. Seeing "SeDebugPrivilege" or "SeTcbPrivilege" granted to a user who isn't an admin is a massive red flag.
- Sysmon Event ID 10 (Process Access): Process 'mimikatz.exe' opened a handle to process 'lsass.exe' with access rights 0x1FFFFF. This is the digital equivalent of seeing someone pickpocket the security chief.
Threat Hunter’s Eye: A Proactive Hypothesis
Hunt Query Idea: "Find all instances where a user account successfully authenticates from a host, and within a short time window (e.g., 5 minutes), that same host generates authentication attempts (like Kerberos ticket requests) for significantly higher-privilege accounts (e.g., Domain Admins)." This pattern suggests credential theft followed by recon or lateral movement using those stolen credentials.
Defensive Tools & Categories
Endpoint Detection and Response (EDR) platforms are essential for tracing process lineage and detecting token manipulation. Privileged Access Management (PAM) solutions tightly control and audit the use of admin accounts. A well-tuned SIEM with curated rules is your correlation engine.
Blue Team Command / Detection Logic
# Sigma Rule for detecting potential Access Token Manipulation (T1134)
title: Process Access to LSASS with Suspicious Rights
status: experimental
logsource:
category: process_access
product: windows
detection:
selection:
TargetImage|endswith: '\lsass.exe'
GrantedAccess|contains:
- '0x1FFFFF' # PROCESS_ALL_ACCESS
- '0x1410' # PROCESS_VM_READ | PROCESS_QUERY_INFORMATION
filter:
SourceImage|endswith:
- '\taskmgr.exe'
- '\procexp.exe'
- '\vmtoolsd.exe'
condition: selection and not filter
falsepositives:
- Legitimate administration tools not excluded in filter
level: high
Real-World Example: From Headlines to Logs
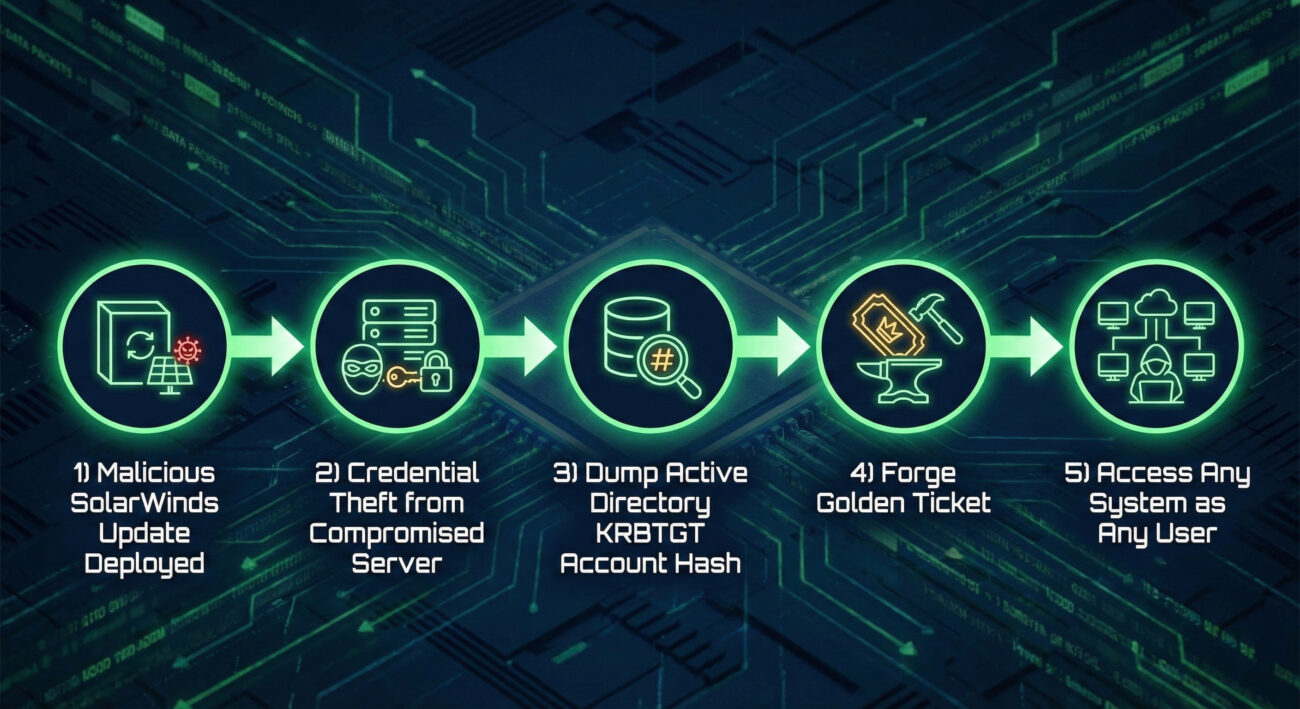
The SolarWinds SUNBURST Attack
The 2020 SolarWinds compromise is a masterclass in a patient, sophisticated attack chain. After gaining initial access via a trojanized software update, the threat group (often called Nobelium or UNC2452) needed to move and escalate.
Explicit Connection: In the SolarWinds attack, the threat actors used Privilege Escalation when they stole and forged Kerberos authentication tickets (a technique called "Golden Ticket" attack). This allowed them to impersonate any user in the Active Directory domain, including highly privileged accounts, giving them unrestricted access to critical systems and enabling the massive, stealthy data exfiltration that followed.
Mapping the MITRE ATT&CK Landscape for Privilege Escalation
Below is a high-level map of the primary Privilege Escalation techniques. Remember, each of these contains numerous sub-techniques
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1548 | Abuse Elevation Control Mechanism | Exploit mechanisms like sudo or UAC to execute code at a higher privilege level. |
| T1555 | Credentials from Password Stores | Extract credentials from stored locations like keychains, vaults, or configuration files. |
| T1068 | Exploitation for Privilege Escalation | Use a software vulnerability to escape a sandbox or gain higher privileges on a system. |
| T1134 | Access Token Manipulation | Make a process run under a different user's token to assume their identity and privileges. |
| T1078 | Valid Accounts | Use existing accounts with higher privileges, obtained through phishing, leaks, or purchase. |
| T1547 | Boot or Logon Autostart Execution | Configure malicious code to run at system start or user logon, often with high privileges. |
| T1484 | Domain Policy Modification | Modify domain-wide policies (like Group Policy) to weaken security and aid further escalation. |
Key Takeaways & Immediate Actions
For Everyone:
- Privilege Escalation is the bridge from a minor intrusion to a major breach. Stopping it breaks the attacker's kill chain.
- It exploits the gap between the access an attacker has and the access they want, often through misconfigurations, stolen credentials, or software bugs.
For Leadership:
- Business Risk: Unchecked privilege escalation enables total network compromise, leading to data theft, ransomware deployment, operational shutdown, and massive financial/reputational damage.
For Defenders & IT Admins:
- Action 1: Enforce the Principle of Least Privilege (PoLP). Audit local administrator rights and domain group memberships. No user should be a local admin without a documented, business-critical need.
- Action 2: Protect Credentials. Implement Credential Guard (Windows), use LSA Protection, and mandate Multi-Factor Authentication (MFA) for all privileged accounts.
- Action 3: Enable and Centralize Key Logs. Ensure Event IDs 4688 (process creation), 4689 (process end), 4672 (special privileges), and Sysmon Event ID 10 (process access) are collected in your SIEM. Hunt for parent-child process anomalies.
Further Learning & References
Continue your journey with these essential resources:
- The Official MITRE ATT&CK Page for Privilege Escalation - The definitive source for techniques, sub-techniques, and mitigations. Bookmark this.
- PayloadsAllTheThings - Windows Privilege Escalation - An incredibly detailed, community-maintained guide to techniques and tools (great for red team learning and blue team awareness).
- CISA: Secure by Design - Guidance on building systems that inherently limit privilege escalation opportunities through better architecture and defaults.
- Microsoft: Securing Privileged Access - In-depth documentation on securing Active Directory and privileged accounts from real-world attacks.
- On this blog: Understanding Privilege Escalation naturally leads to the next step: Lateral Movement (TA0008). Once attackers have higher privileges on one host, they use them to move sideways through your network.
- Cyber Pulse Academy
- February 6, 2026
- No Comments
Accelerate Cyber Pulse Academy
Join us in revolutionizing cybersecurity education.Your contribution directly funds:
Every contribution moves us closer to our goal: making world-class cybersecurity education accessible to ALL.
Choose the amount of donation by yourself.


















































