Reconnaissance
The Attacker's Critical First Step & How to Stop It
Reconnaissance (TA0043)
The Attacker's Critical First Step & How to Stop It
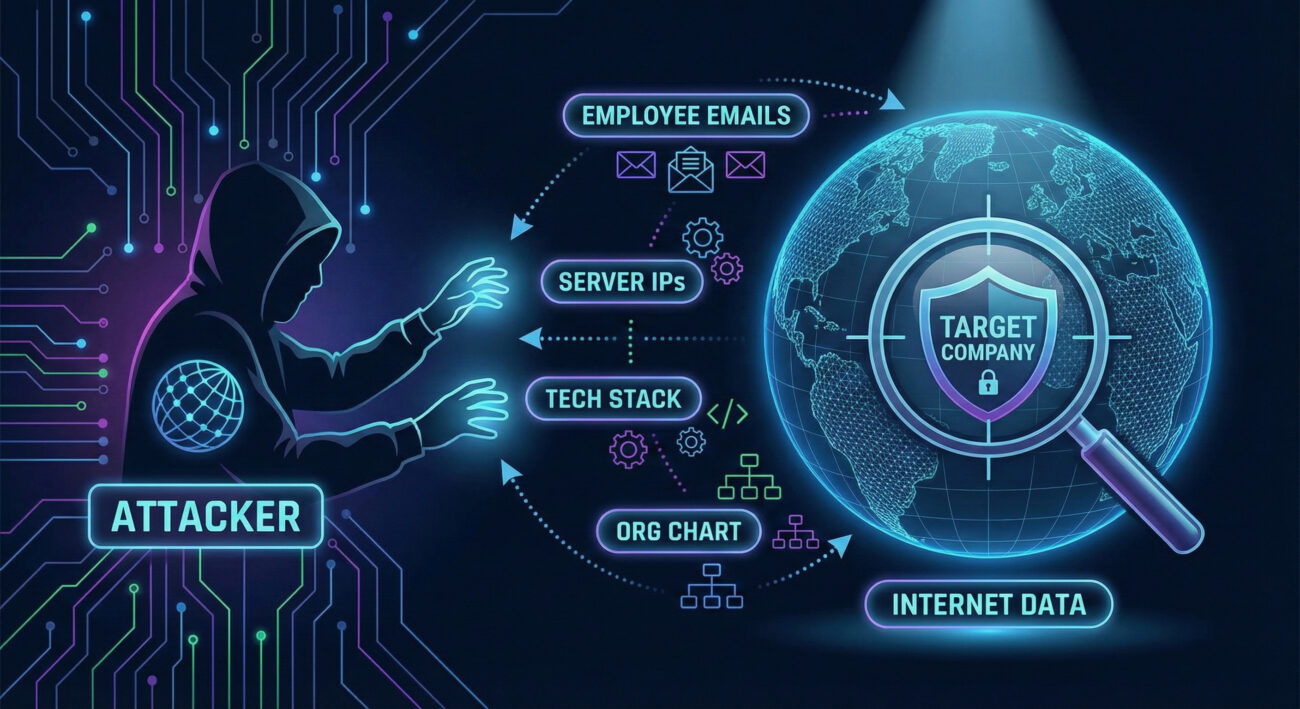
Reconnaissance is the systematic information gathering that every cyber attacker performs before launching an assault. Think of it as the attacker's homework, and skipping it is like planning a heist without ever seeing the building blueprints.
This foundational phase determines the success or failure of everything that follows. A skilled attacker who executes effective Reconnaissance understands your digital footprint, identifies your weakest points, and crafts a bespoke attack that bypasses generic defenses. For defenders, catching this phase is your golden opportunity to stop an attack before it truly begins, turning a potential breach into a mere failed attempt.
Table of Contents
The Core Analogy: Cat Burglars & Digital Footprints
Imagine a professional cat burglar targeting a luxury neighborhood. They don't just randomly pick a house and smash a window. First, they case the joint. They drive through the area at different times, noting which houses have no cars during the day (empty targets), which have visible alarm stickers (security vendors), and which have a gardener who leaves a side gate unlocked (third-party vulnerabilities).
They might sift through the target's trash ("dumpster diving" for discarded documents) to find names, bank info, or schedules. They could pose as a utility worker to get a closer look at locks and cameras ("phishing" for physical access). Every piece of data, the brand of the lock, the dog walker's schedule, the model of the security system, shapes their final, stealthy entry plan.
This is Reconnaissance. Your company's digital "neighborhood" is the public internet and your online presence. The "cat burglar" is the threat actor. The "trash" is your exposed data on code repositories, breached password databases, and outdated subdomains. The goal isn't to break in yet; it's to learn everything needed to break in successfully and silently.
Vocabulary Decoder Ring
- Attack Surface: The sum total of all possible points (hardware, software, cloud services, employees) where an unauthorized user can try to enter or extract data. Why it matters here: Reconnaissance is the process of mapping and understanding your attack surface better than you do.
- Open Source Intelligence (OSINT): Information gathered from publicly available sources. This isn't hacking; it's using Google, social media, business registries, and certificate databases. Why it matters here: 80% of an attacker's recon uses free, legal OSINT tools to find critical vulnerabilities.
- Passive Reconnaissance vs. Active Reconnaissance: Passive recon involves gathering data without directly interacting with the target's systems (e.g., viewing cached pages). Active recon involves interacting with the target (e.g., scanning ports), which is louder and more detectable. Why it matters here: Defenders can only realistically hope to detect active reconnaissance; passive recon happens invisibly.
- Domain Name System (DNS) Enumeration: The process of locating all DNS servers and records for a target domain to map subdomains and related infrastructure. Why it matters here: It's a primary recon technique to discover forgotten, unpatched, or misconfigured subdomains (like
test.example.comorlegacy.example.com).
The Attacker's Playbook (Red Team View)
Red Team Analogy: The Burglar's Notebook
From the attacker's view, Reconnaissance is about building a target dossier. Our cat burglar's goal is confidence and precision. The feeling is one of calculated patience. The methodology is systematic: start broad (the neighborhood), then narrow in (the specific house, its routines, its weaknesses). Every bit of information reduces risk and increases the likelihood of a clean, untraceable entry.
Common Reconnaissance Techniques
- T1595 - Active Scanning: Proactively probing the target's external network (e.g., port scanning, vulnerability scanning) to discover live hosts and services.
- T1589 - Gather Victim Identity Information: Collecting employee names, email addresses, job titles, and social media profiles to enable phishing and social engineering.
- T1590 - Gather Victim Network Information: Mapping the target's network boundaries, IP ranges, domain names, DNS records, and network topology.
- T1596 - Search Open Technical Databases: Querying public repositories like Shodan, Censys, or SSL certificate databases to find exposed assets and technologies.
- T1592 - Gather Victim Host Information: Determining details about the target's operating systems, software versions, and hardware to tailor exploits.
The Reconnaissance Toolbox
- Maltego: A powerful OSINT and data-linkage tool that visually maps relationships between people, companies, domains, and infrastructure.
- Shodan / Censys: Search engines for internet-connected devices. They allow attackers to find specific servers, webcams, or industrial control systems with known vulnerabilities.
- theHarvester: A simple but effective tool for gathering emails, subdomains, hosts, and employee names from public sources like search engines and PGP key servers.
Command-Line Glimpse
# Using nslookup for DNS enumeration (Passive/Active Recon)
nslookup
> set type=any
> server 8.8.8.8
# Using Google's DNS
> ls -d example.com
# Attempts a zone transfer (often restricted, but worth trying)
# Using theHarvester to gather OSINT
theHarvester -d "example.com" -b google,linkedin
# Simple port scan with netcat (Active Scanning)
for port in {80,443,22,3389}; do
nc -zv target-ip $port 2>&1 | grep succeeded
done
The Defender's Handbook (Blue Team View)
Blue Team Analogy: The Neighborhood Watch
From the defender's chair, you are the Neighborhood Watch coordinator. You can't stop the burglar from driving through the neighborhood (passive recon). But you can look for the unfamiliar car circling the block multiple times, the person taking photos of houses, or someone checking door handles. Your goal is to identify the suspicious pattern before the break-in occurs.
SOC Reality Check: What Recon Looks Like in Logs
- Firewall Logs: A single external IP making sequential connection attempts to ports 22 (SSH), 443 (HTTPS), 3389 (RDP), and 445 (SMB) across your entire public IP range. This is a classic port scan.
- Web Server Logs (Apache/Nginx): An unusual spike in requests to non-existent URLs, common vulnerability paths (e.g.,
/wp-admin/,/phpmyadmin/), or requests with tools like "sqlmap" or "nikto" in the User-Agent string. - DNS Query Logs: External IPs performing massive volumes of DNS queries for your subdomains (A, AAAA, MX, TXT records), especially using tools like
dnsreconorsublist3rpatterns.
Threat Hunter’s Eye: A Hunt Hypothesis
Hypothesis: "An adversary is performing targeted subdomain enumeration against our primary domain prior to a phishing campaign."
Hunt: Query DNS logs for sources generating an abnormally high volume of unique subdomain permutations (e.g., api-dev, mail-test, vpn-staging) within a short time window, especially from IPs associated with cloud/VPS providers (DigitalOcean, AWS, Linode) not used by your legitimate employees.
Defensive Tools & Categories
- Threat Intelligence Platforms (TIPs): Services like Recorded Future or AlienVault OTX that can alert you if your company's assets appear in underground forums or scanning databases.
- Security Information and Event Management (SIEM): The central brain for correlating recon activity from firewalls, DNS, web proxies, and endpoint logs.
- Attack Surface Management (ASM) Tools: Platforms like Cortex Xpanse or Rapid7 that continuously discover and assess your external-facing digital assets from an attacker's perspective.
Blue Team Command: Sigma Rule Snippet
title: Potential DNS Reconnaissance / Zone Transfer Attempt
description: Detects multiple AXFR or IXFR type DNS queries which are indicative of a DNS zone transfer attempt, a common reconnaissance technique.
logsource:
category: dns
detection:
selection:
query_type:
- 'AXFR'
- 'IXFR'
condition: selection
falsepositives:
- Legitimate network administration or DNS replication between trusted servers
level: medium
Real-World Example: From Headlines to Logs

Narrative: The 2020 SolarWinds SUNBURST compromise is a masterclass in sophisticated cyber operations. Before the infamous malicious update was deployed, the threat actors (believed to be APT29/Cozy Bear) conducted extensive, patient reconnaissance.
Explicit Connection: In the SolarWinds attack, the threat group used Reconnaissance when they systematically mapped SolarWinds' internal network, development environment, and update infrastructure after gaining an initial foothold. This allowed them to understand the build process, identify the perfect vehicle for their malware (the Orion platform's update mechanism), and craft an attack that remained undetected for months, ultimately compromising thousands of downstream customers.
Their recon was so thorough that they even identified and avoided certain high-security customer networks, demonstrating how recon informs not just the attack, but also the attacker's risk assessment.
Mapping the MITRE ATT&CK Reconnaissance Landscape
Below are the top-level Techniques for TA0043 - Reconnaissance. Remember, each of these contains numerous Sub-techniques that detail specific procedures. This table is your high-level map.
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1595 | Active Scanning | Probe victim's infrastructure via network scans to gather information about IPs, open ports, and services. |
| T1596 | Search Open Technical Databases | Use online resources (Shodan, Censys, SSL certs) to find victim assets and technical details. |
| T1590 | Gather Victim Network Information | Collect data about the victim's network (IP ranges, domain names, DNS) to understand their perimeter. |
| T1589 | Gather Victim Identity Information | Collect employee names, emails, and social profiles to enable targeted social engineering. |
| T1594 | Search Victim-Owned Websites | Analyze the victim's own public websites and posts for technical details and employee information. |
| T1592 | Gather Victim Host Information | Discover details about the victim's operating systems, software, and hardware to find vulnerabilities. |
Key Takeaways & Immediate Actions
For Everyone:
- Reconnaissance is not hacking; it's information gathering. It's the critical planning phase that makes subsequent hacking possible and effective.
- Your public digital footprint is far larger than you think. Assume attackers are constantly and passively collecting this data.
For Leadership:
- Business Risk: Unchecked reconnaissance enables highly targeted, difficult-to-detect attacks. Success here leads directly to devastating data breaches, ransomware deployment, and intellectual property theft, causing massive financial and reputational damage.
For Defenders:
- Action 1: Know Your External Attack Surface. Regularly use ASM tools or external pentest services to discover all internet-facing assets you own. You can't defend what you don't know exists.
- Action 2: Monitor for Active Reconnaissance. Ensure your SIEM ingests and correlates logs from firewalls, DNS servers, and web applications. Build alerts for port scanning patterns, aggressive subdomain enumeration, and web vulnerability scanner signatures.
- Action 3: Practice Good Cyber Hygiene Publicly. Implement strict policies for what developers can push to public code repositories (no secrets!). Train employees on social media oversharing. Regularly audit and retire old subdomains and SSL certificates.
Further Learning & References
- MITRE ATT&CK® Tactics: Reconnaissance (TA0043) - The official, authoritative source. Bookmark this page for the most up-to-date techniques and sub-techniques.
- CISA Alert (AA21-291A): APT29 Targeting COVID-19 Vaccine Development - A real-world case study showing detailed reconnaissance tradecraft used by a sophisticated state actor.
- SANS Blog: OSINT as a Super-Power for Defenders - Learn how to turn the attacker's primary tool (OSINT) into a powerful defensive capability.
- Next Tactic: Initial Access (TA0001) - Once reconnaissance is complete, attackers need a way in. Learn about the next critical phase in the MITRE ATT&CK framework.
- Cyber Pulse Academy
- February 5, 2026
- No Comments


















































