Credential Access
The Attacker's Critical Power Grab & How to Stop It
Credential Access (TA0006)
The Attacker's Critical Power Grab & How to Stop It
Table of Contents
- Introduction: The "So What?" Hook
- The Core Analogy: The Master Key Forger
- Vocabulary Decoder Ring
- The Attacker's Playbook (Red Team View)
- The Defender's Handbook (Blue Team View)
- Real-World Example: From Headlines to Logs
- Mapping the MITRE Landscape
- Key Takeaways & Immediate Actions
- Further Learning & References

Introduction: The "So What?" Hook
Credential Access is the attacker's art of stealing the digital keys, usernames, passwords, hashes, tokens, that unlock doors within your network. It’s not just about getting in; it’s about getting the keys to move freely, silently, and with authority once you're inside.
Why does this matter so much? Because in the cyber kill chain, initial access is often noisy and temporary. Credential Access is the pivot point that transforms a fragile foothold into a persistent, powerful position. Success here lets an attacker escalate privileges, move laterally to critical systems, and ultimately access the crown jewels, all while mimicking legitimate users, making detection incredibly difficult. If defenders fail at this stage, the entire network can become a playground for the adversary.
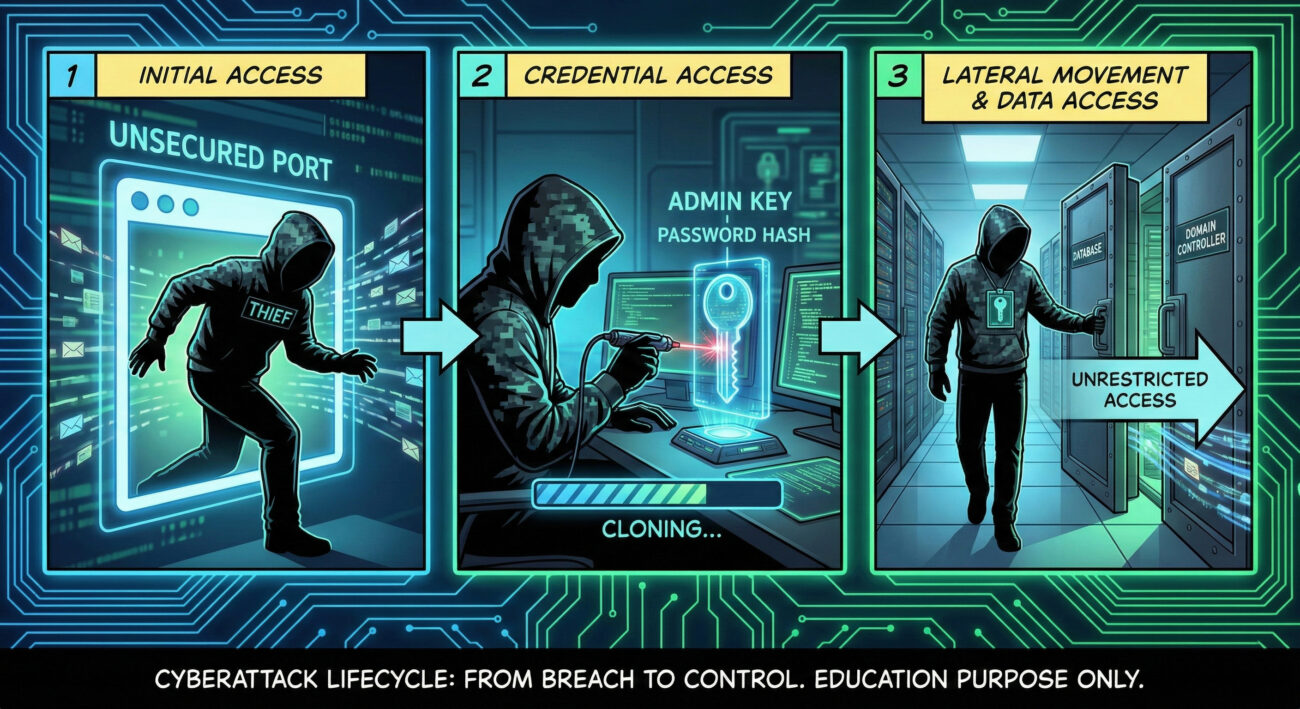
The Core Analogy: The Master Key Forger
Imagine your corporate network is a sprawling, high-security office building. Every door, from the server room to the CFO's office, requires a specific keycard.
An attacker using Credential Access isn't just picking the lock on the back door (Initial Access). They're the professional thief who, once inside the lobby, focuses entirely on stealing the master keyring from the security guard, duplicating keycards left on desks, or tricking employees into handing over their PINs.
With those credentials in hand, they're no longer a suspicious intruder hiding in the stairwell. They can now walk boldly through the halls, open any door they please, and look completely legitimate to every camera and security patrol. This is the devastating power of successful Credential Access.
Vocabulary Decoder Ring
- Credential Dumping: Extracting login information (like password hashes) from a system's memory or storage. Why it matters here: This is the primary method for stealing credentials from a compromised machine, often providing the keys to the rest of the network.
- Pass-the-Hash (PtH): An attack where an adversary uses a stolen password hash (not the plaintext password) to authenticate to a remote system. Why it matters here: It bypasses the need to crack the hash, allowing immediate lateral movement.
- Kerberos Ticket: A time-sensitive, encrypted network authentication ticket used in Windows Active Directory environments. Why it matters here: Stealing or forging these tickets (Golden/Silver Ticket attacks) grants attackers legitimate domain access.
- LSASS (Local Security Authority Subsystem Service): A Windows process that handles user authentication and stores credential data in memory. Why it matters here: It's the prime target for credential dumping tools like Mimikatz.
- MFA (Multi-Factor Authentication): A security system requiring two or more distinct forms of verification. Why it matters here: It's the most effective defensive control to mitigate many Credential Access techniques, especially phishing.
The Attacker's Playbook (Red Team View)
Red Team Analogy: The Master Forger at Work
From the attacker's view, the office building is full of opportunities. The goal isn't to break down every door, it's to become invisible. They feel for the "give" of an unlocked workstation (unpatched system), listen for the careless conversation where a password is shared (network sniffing), or craft a perfect fake ID badge request (phishing). Their methodology is patient, systematic theft of identity.
Common Techniques
- T1003: OS Credential Dumping: Stealing credentials stored in the OS, like from LSASS or the Security Account Manager (SAM) database.
- T1110: Brute Force: Systematically guessing passwords via trial and error.
- T1555: Credentials from Password Stores: Pulling saved passwords from browsers, email clients, or dedicated password managers.
- T1539: Steal Web Session Cookie: Hijacking active browser sessions to bypass login pages entirely.
- T1056: Input Capture: Using keyloggers or GUI input capture to record user keystrokes and mouse clicks.
Toolbox
- Mimikatz: The legendary tool for extracting plaintext passwords, hashes, and Kerberos tickets from Windows memory.
- Impacket: A Python toolkit with scripts like
secretsdump.pyfor remote credential dumping via protocols like SMB. - LaZagne: An application used to recover passwords stored locally on a system from numerous software.
Command-Line Glimpse
# Using Mimikatz to dump credentials from LSASS memory privilege::debug # Escalate to DEBUG privileges (often needed) sekurlsa::logonpasswords # Extract plaintext passwords and NTLM hashes from memory # Result: Shows user names, domains, and (if cached) plaintext passwords or NTLM hashes. # These hashes can be used for Pass-the-Hash attacks immediately.
The Defender's Handbook (Blue Team View)
Blue Team Analogy: The Vigilant Security Director
As defenders, we're the security team reviewing access logs and camera footage. We're not looking for smashed windows; we're looking for anomalies. Why is the janitor's keycard being used to enter the R&D lab at 2 AM? Why did one employee's login originate from two different countries within an hour? Our job is to spot the legitimate key being used in an illegitimate way.
SOC Reality Check: What You'll See in the Logs
- Windows Security Event ID 4688: A process (like
mimikatz.exeorrundll32.exe) with a parent process oflsass.exe- a huge red flag for credential dumping. - Excessive Logon Failures (Event ID 4625) followed by a Successful Logon (Event ID 4624) from the same source: Classic sign of a successful brute-force or password spray attack.
- Unexpected registry access to
HKLM\SAMorHKLM\SECURITYhives: Indicates attempts to dump the SAM database.
Threat Hunter’s Eye: A Sample Hypothesis
"Hunt for processes with the name lsass.exe that have more than one child process. The legitimate LSASS rarely spawns children. Any child process (especially unknown ones) is highly suspicious and indicative of code injection for dumping."
Defensive Tools & Categories
- Endpoint Detection and Response (EDR): Tools like CrowdStrike, Microsoft Defender for Endpoint to detect process injection into LSASS.
- Privileged Access Management (PAM): Solutions like CyberArk or BeyondTrust to vault and manage privileged credentials.
- SIEM with Custom Alerting: Aggregating logs and alerting on the specific event sequences mentioned above.
Blue Team Command / Rule
# Sigma rule to detect potential LSASS credential dumping via process creation
title: Potential LSASS Memory Dump
status: experimental
description: Detects a process creation event where the parent process is lsass.exe, which is highly unusual and indicative of credential dumping.
logsource:
category: process_creation
product: windows
detection:
selection:
ParentImage|endswith: '\lsass.exe'
condition: selection
falsepositives:
- Legitimate administrative or security tools (should be very rare, whitelist explicitly)
level: high
Real-World Example: From Headlines to Logs
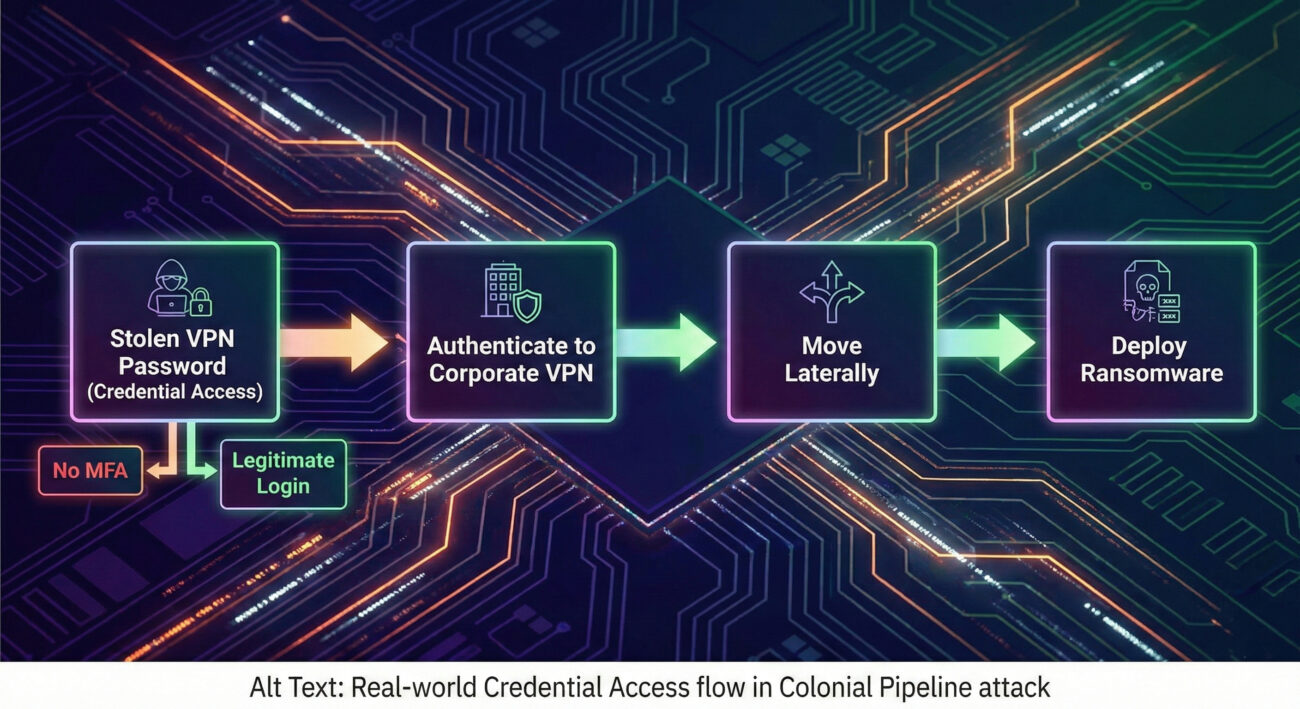
Narrative: The 2021 Colonial Pipeline ransomware attack, attributed to the DarkSide group, crippled a major US fuel pipeline. The initial access vector was a compromised virtual private network (VPN) account that did not have multi-factor authentication enabled.
Explicit Connection: In the Colonial Pipeline attack, the threat group DarkSide used Credential Access when they obtained a single VPN password, likely through a password leak or purchase on the dark web. This allowed them to authenticate directly to the corporate network as a legitimate user, bypassing perimeter defenses and immediately beginning their lateral movement to deploy ransomware.
Mapping the MITRE Landscape
Below are some of the primary Techniques within the Credential Access tactic (TA0006). Remember, each of these contains numerous sub-techniques, these are the high-level categories.
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1003 | OS Credential Dumping | Steal credentials stored by the operating system from memory or files. |
| T1110 | Brute Force | Guess credentials by systematic trial and error (password spraying, cracking). |
| T1555 | Credentials from Password Stores | Harvest credentials from third-party applications like browsers or email clients. |
| T1539 | Steal Web Session Cookie | Hijack active web sessions to bypass authentication mechanisms. |
| T1552 | Unsecured Credentials | Find credentials insecurely stored in files, code, configuration, etc. |
| T1056 | Input Capture | Intercept user input via keylogging or credential capture prompts. |
Key Takeaways & Immediate Actions
For Everyone:
- Credential Access is the pivot point where attackers go from being "in the network" to "owning the network." It turns a vulnerability into an identity crisis.
- Attackers aim to steal hashes and tickets just as much as plaintext passwords, these can be used without ever cracking them.
For Leadership:
- The business risk is total loss of trust and control. Compromised credentials enable data breaches, ransomware deployment, and intellectual property theft, often leading to regulatory fines and massive recovery costs.
For Defenders:
- Enable and enforce MFA everywhere, especially on VPNs, email, and critical cloud services. This single control breaks most credential-based attacks.
- Implement Credential Guard on Windows 10/11 Enterprise and Windows Server 2016+ to protect LSASS from credential dumping attacks.
- Monitor and alert on the specific event sequences outlined in this post (e.g., LSASS child processes, access to SAM/SECURITY hives, successful logons after many failures).
- Conduct regular password audits and phishing simulations to find and remediate weak credentials and user susceptibility.
Further Learning & References
- Official MITRE ATT&CK Page: Credential Access (TA0006) - The definitive source for techniques and sub-techniques. Start here.
- CISA Alert: Threat Actors Use Brute Force Attacks to Obtain Access to Remote Desktop Protocols - A real-world government analysis of credential-based attacks with mitigation steps.
- SpecterOps Blog: Attacking Kerberos - A deep technical dive into one of the most critical credential systems in Windows environments.
- Microsoft Security Blog: The Scale of Credential Phishing - Understand the modern scale of the problem from a major defender's perspective.
- Internal/Contextual: After achieving Credential Access, attackers almost always move to Privilege Escalation (to get administrator keys) and Lateral Movement (to use those keys on other systems).
- Cyber Pulse Academy
- February 6, 2026
- No Comments


















































