Network Security Appliances (T1590.006)
Ultimate Guide to Gather Victim Network Information - Network Security Appliances: Attack & Defense
Network Security Appliances involves identifying and fingerprinting security devices like firewalls, VPN gateways, and intrusion detection systems to map defensive perimeters and find potential weaknesses before launching an attack.
ATT&CK ID T1590.006
Tactics Reconnaissance
Platforms PRE
Difficulty 🟢 Low
Prevalence High
Table of Contents
- Understanding Network Security Appliances in Simple Terms
- Decoding the Jargon: Key Terms for Network Security Appliances
- The Attacker's Playbook: Executing Network Security Appliances
- The Defender's Handbook: Stopping Network Security Appliances
- Building Resilience: Mitigation Strategies for Network Security Appliances
- Network Security Appliances Cheat Sheet
- Conclusion and Next Steps
Understanding Network Security Appliances in Simple Terms
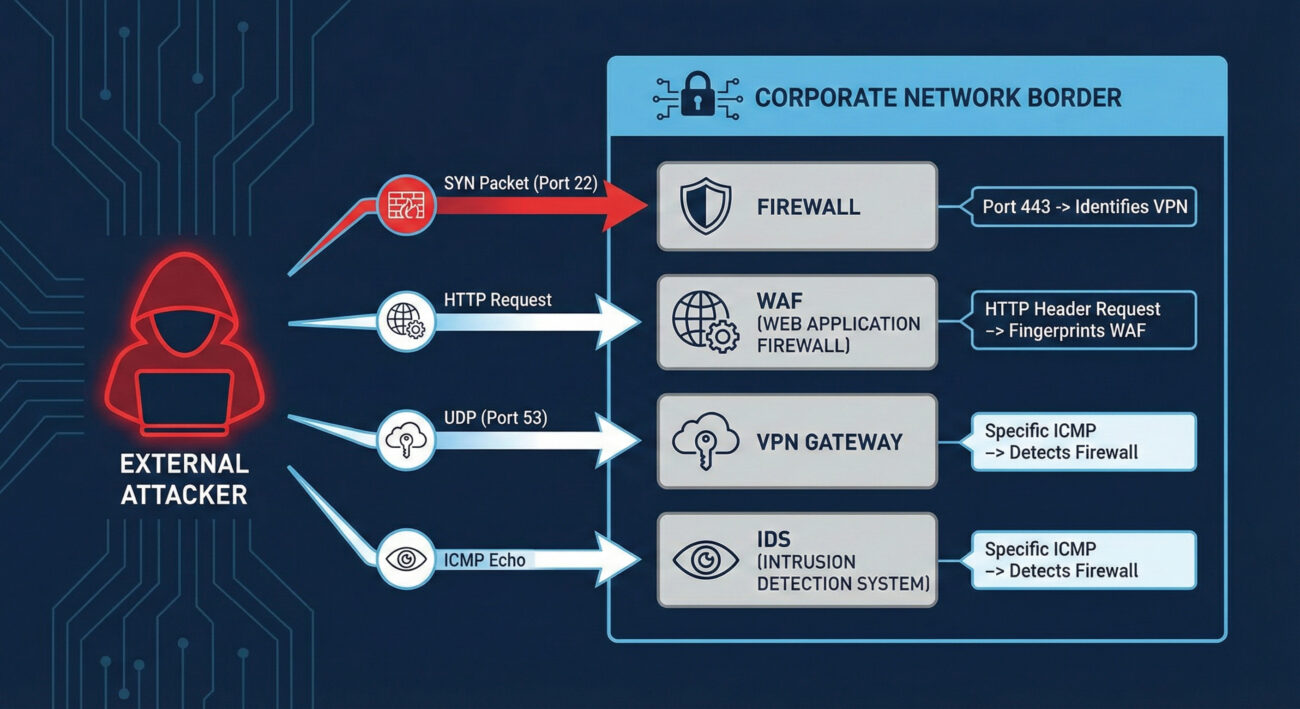
Imagine you're a burglar casing a neighborhood. You wouldn't just look at houses, you'd note which homes have alarm company signs, security cameras, guard dogs, or particularly strong doors. Network Security Appliances reconnaissance is the digital equivalent. Before launching an attack, adversaries scan your digital perimeter to identify what security devices you have deployed, firewalls, VPN gateways, web application firewalls (WAFs), and intrusion detection systems.
This isn't about breaking in yet; it's about understanding your defenses. By fingerprinting these appliances, attackers can determine make, model, version, and sometimes even configuration details. This intelligence is gold: it tells them what vulnerabilities might exist (based on known flaws for that version), what evasion techniques to use, and where the weakest link in your security chain might be located.
Decoding the Jargon: Key Terms for Network Security Appliances
| Term | Definition | Why It Matters |
|---|---|---|
| Banner Grabbing | Connecting to a network service (like SSH, HTTP, FTP) and recording the "banner" or identification string it sends back. | A primary method for fingerprinting appliances. A banner might reveal "Cisco ASA 9.16" or "Fortinet FortiGate". |
| Fingerprinting | The process of determining the type and version of a networked device or software based on its responses to crafted probes. | Allows attackers to map your security stack and research version-specific exploits or misconfigurations. |
| Attack Surface | The sum of all possible points (attack vectors) where an unauthorized user can try to enter or extract data from your environment. | Every exposed security appliance expands your attack surface. Knowing what's exposed is the first step to reducing it. |
| Next-Generation Firewall (NGFW) | A firewall that integrates additional capabilities like intrusion prevention, deep packet inspection, and application awareness. | A common target for reconnaissance. Identifying an NGFW model helps an attacker understand what deep inspection they need to evade. |
| VPN Concentrator/Gateway | A hardware device or software that creates secure remote access tunnels for many simultaneous users. | A high-value target. Fingerprinting can reveal vulnerabilities (e.g., CVE-2019-19781 in Citrix VPN) that provide a direct entry point. |
The Attacker's Playbook: Executing Network Security Appliances Reconnaissance
Step-by-Step Breakdown
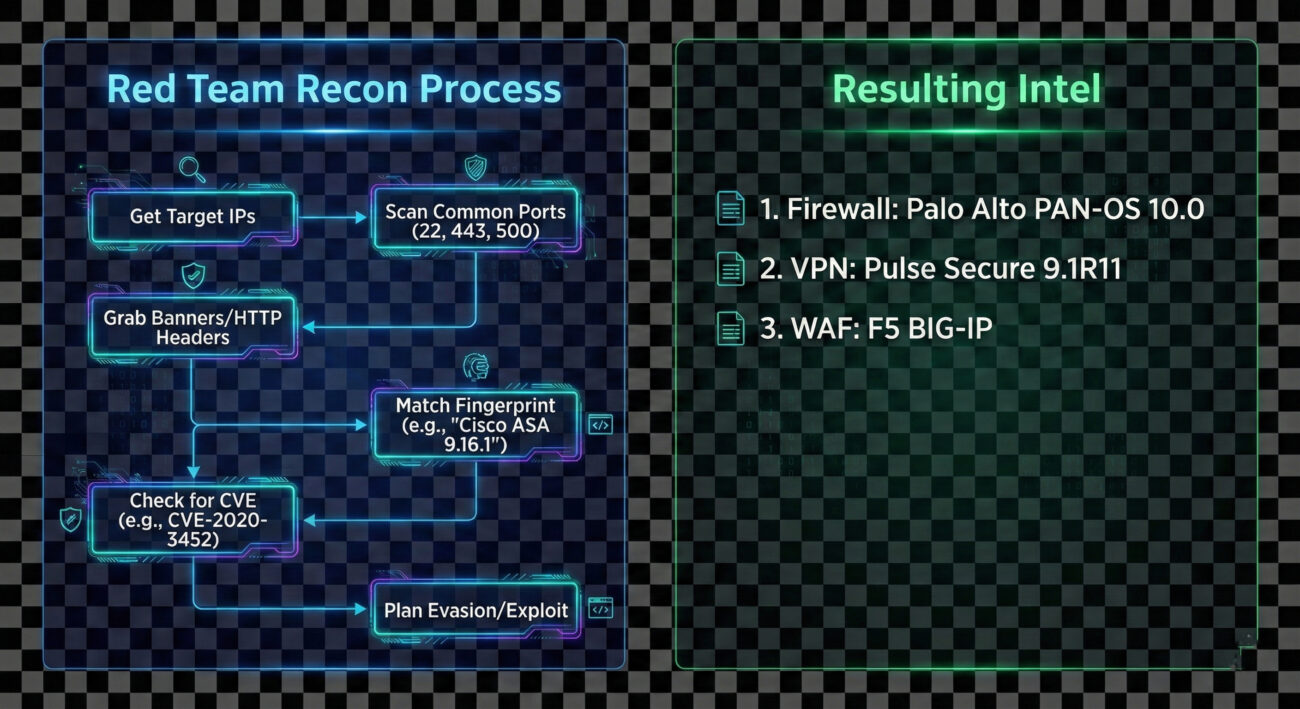
The process is methodical and often automated. An adversary begins with a broad net and progressively refines their focus.
- Initial Target Scope: The attacker identifies the target organization's IP ranges (from T1590.001 - IP Addresses) or domain names.
- Port Scanning & Service Discovery: They perform a port scan (using tools like Nmap or Masscan) against the target ranges, focusing on common security appliance ports:
- TCP/443 (HTTPS/SSL VPNs)
- TCP/22 (SSH management)
- TCP/80 (HTTP management interfaces)
- UDP/500 (IPSec VPN)
- TCP/4443-4445 (Common alternative management ports)
- Banner Grabbing & Protocol Interaction: For each open port, they attempt to connect and retrieve a banner or elicit a unique response. For web interfaces (port 443/80), they may fetch the default login page or examine HTTP headers for server identifiers.
- Fingerprint Analysis: Collected data is compared against databases of known device fingerprints (like those in Nmap's
nmap-service-probesfile) to identify the exact appliance and version. - Vulnerability Correlation: The identified versions are cross-referenced with public exploit databases (Exploit-DB, NVD) and vendor advisories to find unpatched vulnerabilities.
- Evasion Planning: Knowledge of the specific security stack informs the next steps. For example, knowing a specific WAF is in place might lead the attacker to craft payloads designed to bypass it.
Red Team Analogy & Mindset
Think of yourself as a penetration tester on a physical security assessment. You don't run at the main vault first. You walk the perimeter, take photos of locks, alarm sensors, and guard patrol patterns. You note the brand of the security cameras to see if they have known weaknesses. Your goal in this phase isn't theft, it's building a detailed blueprint of the defense system. The mindset is one of patience and curiosity: "What do they have protecting them, and what does that tell me about how to get in later?"
Tools & Command-Line Examples
This reconnaissance is heavily tool-driven. Here are the common ones:
- Nmap: The king of network discovery. Its vast scripting engine (
-sC) and service/version detection (-sV) are perfect for this. - Masscan: For incredibly fast scans of large IP ranges to find open ports.
- httprint, WAFW00F: Specialized tools for fingerprinting web servers and Web Application Firewalls based on response characteristics.
- Shodan, Censys: Search engines for Internet-connected devices. Attackers can often find exposed security appliances without scanning directly.
Example Nmap Commands:
# Basic service and version detection on common security appliance ports
nmap -sV -p 22,80,443,4443,8443,9000 203.0.113.0/24 -oA security_scan
# Aggressive banner grabbing with NSE scripts
nmap -sV --script=banner,http-title,ssh-auth-methods -p 22,443,8443 target.corporate.com
# Specific script to detect and fingerprint VPN services
nmap -sU -p 500,4500 --script=ike-version target_gateway.company.com# The comments above show how an attacker uses Nmap to probe for and fingerprint services on standard management and VPN ports.
Real-World Campaign Example
The Chinese state-sponsored group APT29 (Cozy Bear) is a master of meticulous reconnaissance. In campaigns leading up to the 2020 SolarWinds compromise, and in other operations, APT29 has been observed conducting extensive network security appliance mapping. They would scan for and fingerprint VPN appliances (like Pulse Secure and Fortinet) and firewalls to identify potential vulnerabilities or misconfigured devices that could provide initial access or be used as command-and-control (C2) infrastructure.
This reconnaissance was not a one-off event but a persistent, low-and-slow effort integrated into their broader intelligence-gathering mission. By understanding the target's security perimeter in detail, they could tailor their intrusion methods with high precision.
External Reference: Mandiant's detailed report on UNC2452 (related to SolarWinds) discusses the group's sophisticated tradecraft, including victim environment reconnaissance.
The Defender's Handbook: Stopping Network Security Appliances Reconnaissance
Blue Team Analogy & Detection Philosophy
You're the security manager for a high-security facility. Your job isn't to stop people from looking at the building, that's impossible. Your job is to notice when someone is taking an unusual amount of interest, photographing details, or testing door handles. For Network Security Appliances, the blue team philosophy is: "Assume you will be scanned. Detect the scan. Obscure the useful details." You shift from trying to prevent all reconnaissance (impossible) to making the reconnaissance data unreliable or raising alarms when it occurs.
SOC Reality Check: What to Look For
In your SIEM, you'll see noise. The key is separating benign internet background radiation from targeted reconnaissance.
- Alert Fatigue: Your perimeter IPS/IDS may fire alerts for "Web Application Fingerprint Attempt" or "SSL VPN Scan." Tune these to reduce false positives from legitimate security researchers or automated bots.
- Correlation is Key: A single connection to port 443 is normal. 500 sequential connections to ports 22, 80, 443, 8443 across your entire subnet from a single IP in 2 minutes is a scan.
- Source Context: Scans from known bulletproof hosting providers, cloud VPS regions with no business ties, or Tor exit nodes carry higher severity.
- Logging Gaps: The biggest challenge is often getting the right logs. Ensure your perimeter firewalls, VPN concentrators, and WAFs are sending their connection/audit logs to your central SIEM.
Threat Hunter's Eye: Practical Query
Here is a Splunk SPL query designed to hunt for horizontal scanning activity targeting common security appliance management ports. This looks for a single source IP hitting multiple distinct internal IPs on a specific set of ports within a short time window.
index=firewall OR index=vpn
dest_port IN (22, 80, 443, 4443, 8443, 9000, 500, 4500)
action="allowed" OR action="denied"
| bucket _time span=5m
| stats
values(dest_ip) as targeted_hosts,
values(dest_port) as ports_probed,
count as total_events
by src_ip, _time
| where mvcount(targeted_hosts) > 5
| where mvcount(ports_probed) >= 3
| table _time, src_ip, targeted_hosts, ports_probed, total_events
| sort - total_events# This query identifies potential scanners by looking for sources that have connected to more than 5 different internal hosts on at least 3 of the listed security appliance ports within a 5-minute window.
Key Data Sources for Detection
- Perimeter Firewall Logs: Connection attempts (allowed and denied) to management interfaces.
- VPN Gateway Logs: Authentication attempts (especially failed) and connection logs to the VPN service port.
- Network Intrusion Detection System (NIDS) Alerts: Alerts for scanning patterns or specific fingerprinting attempts.
- Web Server/Proxy Logs: For appliances with web management interfaces (common on port 443/8443). Look for GET requests to default paths like
/admin,/login, or specific vendor paths. - Asset Management Database: Knowing what you should have exposed helps identify unexpected devices responding to probes.
Building Resilience: Mitigation Strategies for Network Security Appliances
Actionable Mitigation Controls
Convert MITRE's high-level mitigations into concrete actions your team can implement this quarter.
- Network Segmentation: Place management interfaces for firewalls, VPNs, and other security appliances on a dedicated, isolated management network (out-of-band if possible). Never expose them directly to the internet.
- Banner/Header Obfuscation: Where supported, modify default banners and HTTP headers to remove or genericize vendor and version information. (Note: This is security through obscurity and should not be your only control).
- Aggressive Patch Management: Since reconnaissance aims to find vulnerable versions, a rigorous and fast patching cycle for all security appliances is your best defense. Prioritize patches for internet-facing devices.
- Access Control Lists (ACLs): If internet access is necessary, restrict source IPs to known, trusted ranges (e.g., your corporate IPs, approved partner IPs, or your managed security service provider).
- Regular External Attack Surface Scans: Use tools like CISA's Cyber Hygiene service or commercial solutions to scan your own external IPs. See what an attacker sees and remediate unexpected exposures.
Red vs. Blue: A Quick Comparison
| Attacker Goal (Red Team) | Defender Action (Blue Team) |
|---|---|
| Identify all exposed security appliances. | Minimize exposed appliances; use jump hosts/VPNs for management. |
| Fingerprint exact make, model, and version. | Obfuscate banners and keep software patched to negate the value of version data. |
| Find unpatched vulnerabilities in identified versions. | Implement a rigorous patch management program with SLAs for critical external devices. |
| Use intelligence to plan evasion and initial access. | Use detection queries to alert on reconnaissance activity, gaining early warning of impending attacks. |
Network Security Appliances Cheat Sheet
Red Flag
A single external IP making sequential TCP/SYN connections to ports 22, 80, 443, 8443 across multiple internal IPs within minutes. This is a classic horizontal scan for management interfaces.
Blue's Best Move
Take management interfaces offline. Use a VPN (itself non-publicly managed) to access a management network. If public access is unavoidable, enforce strict source IP whitelisting.
Hunt Here
Correlate logs from your perimeter firewall, VPN concentrator, and WAF. Look for the same source IP appearing across these logs in a short timeframe, probing different services.
Conclusion and Next Steps
Network Security Appliances reconnaissance (T1590.006) is a foundational step in the adversary lifecycle. While simple in execution, its value to an attacker is immense. As defenders, we cannot stop the internet from knocking at our door, but we can control what it sees, how we watch those knocks, and how quickly we fix the flaws it might discover.
Your action plan:
- Conduct an external scan of your own organization to see what security appliances are visible.
- Review and tighten access controls on any management interfaces that must remain accessible.
- Implement or tune the detection query provided in this guide within your SIEM to catch scanners.
- Validate your patch cycles for perimeter security devices, these should be among your fastest patched assets.
Continue Your Learning:
- Explore T1590.001: Gathering Victim IP Addresses, another key reconnaissance technique.
- Dive into T1595: Active Scanning, the parent category for this type of activity.
- Read the NIST SP 800-40r4: Guide to Enterprise Patch Management for a framework on securing all systems, including appliances.
- Watch the MITRE ATT&CK® Defender™ Defending against Reconnaissance webinar for broader defensive strategies.
Stay vigilant, measure your attack surface, and remember: the best time to detect an intrusion is before it happens, during the reconnaissance phase.
Network Security Appliances
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026
- No Comments


















































