Network Topology (T1590.004)
Ultimate Guide to Gather Victim Network Information - Network Topography: Attack & Defense
Network Topography is a critical reconnaissance technique where adversaries map your network structure to identify key assets, trust relationships, and potential attack paths before launching their main assault.
ATT&CK ID T1590.004
Tactics Reconnaissance
Platforms PRE (Preparation)
Difficulty 🟢 Easy
Prevalence High
📋 Table of Contents
- Understanding Network Topography in Simple Terms
- Decoding the Jargon: Key Terms for Network Topography
- The Attacker's Playbook: Executing Network Topography
- The Defender's Handbook: Stopping Network Topography
- Building Resilience: Mitigation Strategies for Network Topography
- Network Topography Cheat Sheet
- Conclusion and Next Steps
Understanding Network Topography in Simple Terms
Imagine you're a burglar planning to rob a museum. You wouldn't just walk in blind. First, you'd study blueprints, note guard patrol routes, identify alarm sensor locations, and find the back door behind the gift shop. Network Topography is the digital equivalent of this planning phase.
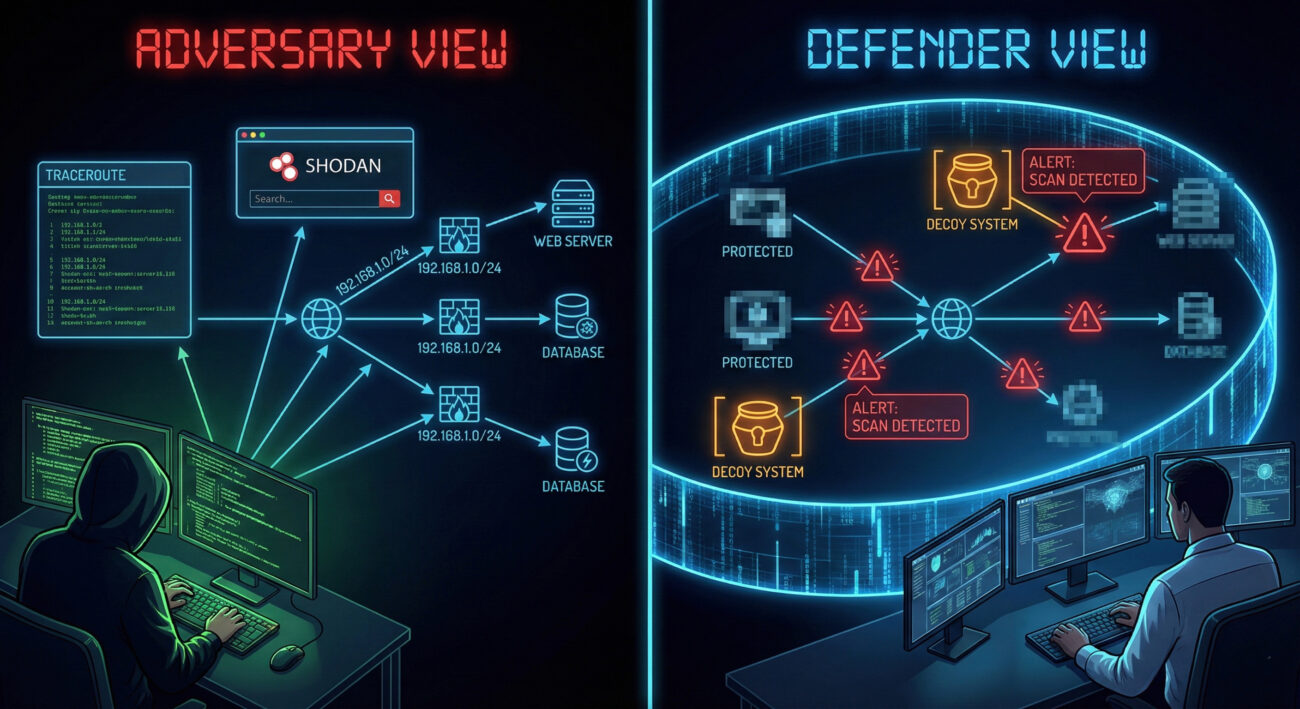
Adversaries, from script kiddies to advanced nation-state groups, start by drawing a map of your digital territory. They want to answer questions like: Where are the servers? How are network segments connected? What security devices (firewalls, IDS) are in place? Which systems talk to each other? This map becomes their attack playbook, allowing them to move stealthily and target the most valuable assets efficiently.
This technique is passive and often goes unnoticed because it uses information that is publicly available or gleaned from routine, allowed network traffic. The goal isn't to break in yet, it's to learn how to break in with the highest chance of success and the lowest risk of detection.
Decoding the Jargon: Key Terms for Network Topography
| Term | Simple Definition | Why It Matters |
|---|---|---|
| Network Mapping | The process of discovering and visualizing devices, their connections, and the structure of a network. | This is the core activity of T1590.004. Attackers use it to create their target blueprint. |
| Autonomous System (AS) | A large network or group of networks under a single organization's control, identified by a unique AS Number (ASN). | Attackers can identify all IP ranges belonging to your company, revealing your digital perimeter's true size. |
| Tracerouting | A technique to map the path network packets take from source to destination, revealing intermediate hops (routers). | It exposes internal network architecture, trust paths, and potential chokepoints or security devices. |
| Passive Reconnaissance | Gathering information without directly interacting with the target systems (e.g., searching public databases). | Makes Network Topography extremely stealthy and hard to attribute or detect. |
| BGP (Border Gateway Protocol) | The protocol that manages how packets are routed across the internet via ASNs. | BGP public records are a goldmine for attackers to map an organization's internet-facing infrastructure. |
The Attacker's Playbook: Executing Network Topography
Step-by-Step Breakdown
The process is methodical, often blending automated tools with manual analysis:
- Target Identification: The attacker starts with a company name. Using tools like WHOIS, they find registered domains (e.g., acme.com, dev.acme.com, vpn.acme.com).
- IP Range Enumeration: They query BGP databases (e.g., BGPView, Hurricane Electric BGP Toolkit) to find all IP address blocks (CIDR ranges) owned by the company's ASN.
- Live Host Discovery: Within those IP ranges, they perform ping sweeps or use masscan to identify which IPs are actually active and responding.
- Service & Port Mapping: For live hosts, they scan for open ports (nmap) to identify running services (web server on 443, database on 1433, RDP on 3389).
- Path Analysis: Using traceroute from multiple vantage points, they map network paths to key assets, identifying firewalls, load balancers, and network segments.
- Diagram Synthesis: All data is fed into tools like draw.io or Maltego to create a visual network map, highlighting critical assets, trust relationships, and potential entry points.
Red Team Analogy & Mindset
Think like a military cartographer before D-Day. Your job isn't to fight yet, but to create the most accurate possible map of the enemy's coastline, defenses, supply lines, and command centers. Every piece of information reduces uncertainty. The red team mindset here is one of patient, thorough observation. They rely on the fact that most organizations don't monitor for low-and-slow information gathering from disparate public sources.
Tools & Command-Line Examples
Attackers have a vast arsenal for this phase:
- Nmap: The Swiss Army knife.
nmap -sS -sV -O 192.168.1.0/24scans a subnet, discovering hosts, services, and OS. - Masscan: For blistering speed:
masscan 10.0.0.0/8 -p1-65535 --rate=10000. - Shodan/Censys: Search engines for internet-connected devices. Query:
org:"Acme Corp" port:22finds all their exposed SSH servers. - traceroute/tracert:
traceroute -I 10.10.10.5(Unix) ortracert 10.10.10.5(Windows) maps the route. - Maltego: Graphical tool for link analysis and data aggregation from OSINT.
Real-World Campaign Example
APT29 (Cozy Bear / The Dukes), associated with Russian intelligence, is notorious for extensive, patient reconnaissance. In campaigns targeting government and think-tank networks, they have been observed conducting detailed Network Topography mapping over weeks or months.
They use this intelligence to craft highly targeted spear-phishing emails and to identify the perfect initial access point, such as a vulnerable, internet-facing server in a less-secure network segment. Their success is built on this foundational understanding of the victim's digital landscape.
Further Reading: Mandiant's report on APT29 details their reconnaissance-heavy tradecraft.
The Defender's Handbook: Stopping Network Topography
Blue Team Analogy & Detection Philosophy
Your job is to be the counter-intelligence unit. You must assume that adversaries are constantly mapping you. The goal isn't to prevent all mapping (that's nearly impossible) but to distort their map, detect their cartographers, and hide your true treasures. Shift from thinking "we've been scanned" to "what did they learn, and how can we make that information useless or misleading?"
SOC Reality Check: What to Look For
Direct detection of passive reconnaissance (BGP lookups, Shodan scans) from your internal logs is impossible. Focus on detecting the active probing that usually follows or complements it:
- Port Scans: High volume of connection attempts to multiple ports across sequential IPs from a single source.
- Suspicious Traceroutes: ICMP Time Exceeded or UDP packets from external IPs traversing your border.
- DNS Recon: Bursts of AXFR requests, DNS zone transfers, or queries for non-existent hosts (NXDOMAIN storms).
- Noise vs. Signal: These activities blend with normal traffic. Correlation over time and geolocation of source IPs (e.g., traffic from a non-business country) is key.
Threat Hunter's Eye: Practical Query
Here is a Sigma rule to detect horizontal port scanning behavior, a common tactic used to validate network maps:
# Simple Sigma rule for detecting horizontal port scans
title: Horizontal Network Port Scan
id: 5a4215a7-58a5-4b2b-8c0a-9d3e1f7a2c6b
status: experimental
description: Detects a single source IP attempting to connect to multiple destination ports across multiple hosts in a short timeframe.
author: ATT&CK Field Guide
references:
- https://attack.mitre.org/techniques/T1590/004/
logsource:
category: firewall
product: windows
detection:
selection:
action: allowed # Focus on allowed traffic that evades simple blocks
timeframe: 5m
condition: selection | count(dst_ip) by src_ip > 50 and count(dst_port) by src_ip > 20
# Thresholds (50 unique hosts, 20 unique ports) are tunable
falsepositives:
- Legitimate network scanners
- Vulnerability assessment tools
level: mediumKey Data Sources for Detection
- Firewall/Network Device Logs: The primary source for connection attempts, denied probes, and traceroute packets.
- NetFlow/IPFIX Data: Essential for analyzing traffic patterns and identifying scanning behavior across broad IP ranges.
- DNS Server Logs: Critical for detecting reconnaissance through DNS enumeration and zone transfer attempts.
- IDS/IPS Alerts: Rules specifically tuned for scanning patterns (e.g., SURICATA ET SCAN rules).
- Endpoint Logs (EDR): While less common for external mapping, they can detect internal reconnaissance tools like Advanced IP Scanner if an attacker gains a foothold.
Building Resilience: Mitigation Strategies for Network Topography
Actionable Mitigation Controls
- Network Segmentation: Divide your network into isolated segments. A successful map of your DMZ should reveal nothing about your internal PCI or R&D networks. This limits the utility of any single map.
- Obscure Architecture: Use non-standard ports for critical services where feasible (though not security by obscurity). More importantly, ensure external DNS doesn't leak internal hostnames (split-horizon DNS).
- Rate Limiting & Egress Filtering: Configure border firewalls to rate-limit ICMP/UDP packets used in traceroutes and block outgoing packets with internal source IPs (anti-spoofing).
- Honeypots/Deception: Deploy fake systems with enticing names ("HR_DB_SERVER," "CEO_FILES") in your IP ranges. Any interaction with them is a high-fidelity alert for reconnaissance or attack.
- Vulnerability Management: Since mapping reveals services, ensure all internet-facing services are patched and unnecessary ones are disabled. Shrink your attack surface.
- Third-Party Monitoring: Regularly search for your own assets on Shodan/Censys. See what the attacker sees and take corrective action.
Red vs. Blue: A Quick Comparison
| Attacker Goal (Red) | Defender Action (Blue) |
|---|---|
| Map all IP ranges belonging to the target. | Consolidate and minimize public IP ranges where possible. Use IP reputation to block scanning IPs. |
| Identify all live hosts and services. | Implement strict egress filtering and deploy honeypots to detect probing. |
| Understand network paths and trust relationships. | Enforce network segmentation and encrypt internal traffic to obscure trust paths. |
| Remain stealthy and avoid detection. | Monitor for low-and-slow scanning patterns with NetFlow analytics and behavioral baselining. |
Network Topography Cheat Sheet
Red Flag
External IPs performing sequential connections to blocks of your IP space on multiple ports, especially if followed by traceroute patterns. A sudden spike in DNS queries for internal hostnames or NXDOMAIN responses.
Blue's Best Move
Implement Network Segmentation & Deception. Limit what can be learned from any single point of observation. Deploy high-interaction honeypots in your external IP ranges to generate high-fidelity alerts on contact.
Hunt Here
Firewall/NetFlow logs for "one-to-many" connections. DNS logs for anomalous query volumes or AXFR requests. Correlate events over longer time windows (hours/days) to catch slow, distributed reconnaissance.
Conclusion and Next Steps
Network Topography (T1590.004) is the quiet, patient foundation of nearly every successful cyber attack. By understanding the attacker's methodology, turning your public information into a tactical map, you can develop more effective defenses. The key is shifting from a reactive to a proactive and deceptive posture.
Your Action Plan:
- Conduct a self-assessment: Use Shodan and tools like nmap against your own external IP ranges. See what an attacker sees.
- Review detection capabilities: Can your SIEM/NDR detect the scanning patterns described? Test the Sigma rule provided.
- Plan one mitigation improvement: This could be implementing a simple honeypot or tightening egress filtering rules.
Continue Your ATT&CK Journey:
- Related-Technique-Name - Active Scanning (T1595): The logical next step after topography mapping.
- Related-Technique-Name - Gather Victim Network Information (T1590): The parent technique covering all network recon.
External Authority Links:
- NIST SP 800-160 Vol. 2: Developing Cyber-Resilient Systems - Guidance on engineering systems to withstand attacks, including those informed by reconnaissance.
- CISA Security Tip: Understanding Denial-of-Service Attacks - While about DoS, it includes relevant info on network architecture resilience.
Stay vigilant, think like your adversary, and build a network that's harder to map and even harder to breach.
Network Topology
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026
- No Comments


















































