Notepad++ Update Hijack: Critical Supply Chain Attack Exposed
📋 Executive Summary
In February 2026, the maintainer of Notepad++ disclosed a sophisticated supply chain attack where the official update mechanism was hijacked to deliver malware to selected users. This attack leveraged an infrastructure-level compromise at the hosting provider, not a vulnerability in Notepad++ code. The updater (WinGUp) was tricked into downloading malicious binaries due to weak integrity verification. Attributed to Violet Typhoon (APT31), the attack targeted East Asian telecom and financial sectors. This post dissects the attack from a beginner-friendly perspective, maps it to MITRE ATT&CK, and provides actionable defenses.
Focus keyword: This Notepad++ update hijack serves as a critical case study in software supply chain security.
🔍 Attack Breakdown & MITRE ATT&CK Mapping
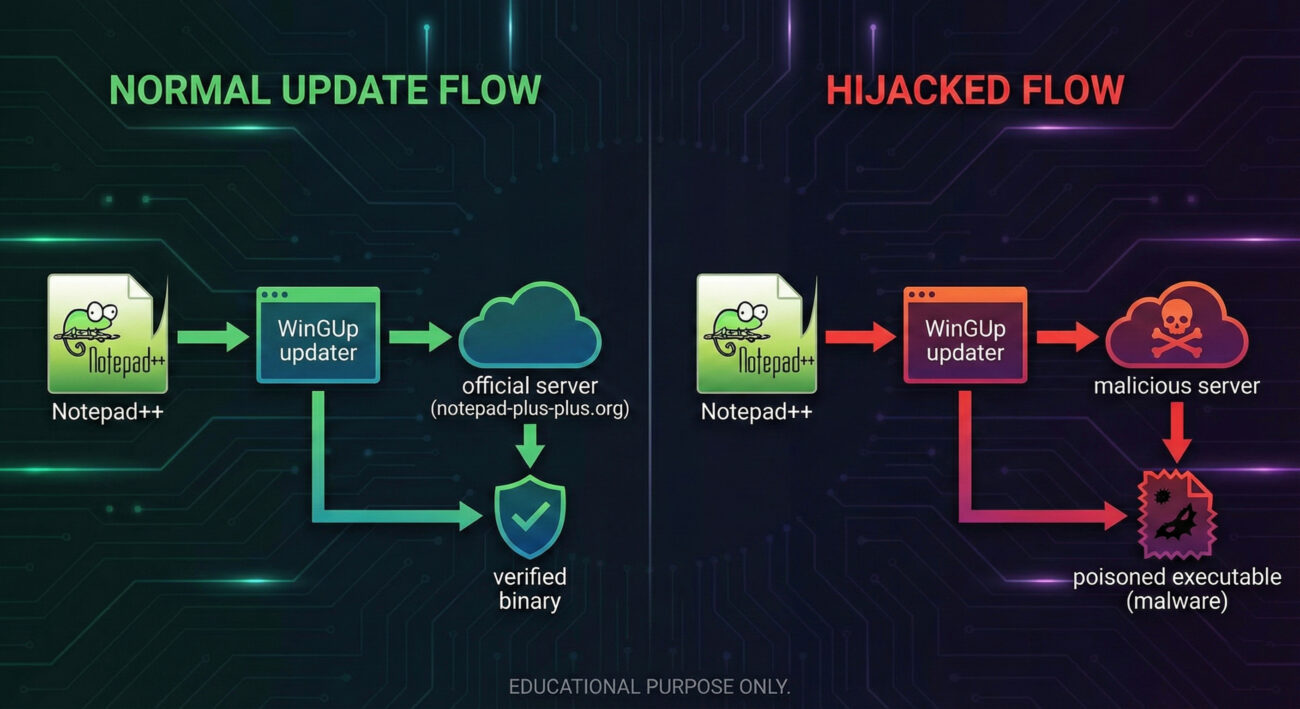
The attack exploited the trust relationship between the Notepad++ application and its update server. Here’s how it unfolded technically:
- Infrastructure compromise: Attackers gained access to the hosting provider’s systems, redirecting traffic from
notepad-plus-plus.orgto malicious servers. - Update mechanism flaw: WinGUp (the updater) did not properly validate the integrity and authenticity of downloaded updates, allowing a man-in-the-middle to substitute a legitimate binary with a poisoned one.
- Targeted delivery: Only specific users (based on IP or geolocation) were redirected, making detection difficult.
Below is the mapping to MITRE ATT&CK techniques (v14):
| Tactic | Technique ID | Technique Name | Context |
|---|---|---|---|
| Initial Access | T1195.001 | Supply Chain Compromise: Compromise Software Dependencies | Update mechanism hijacked at infrastructure level |
| Initial Access | T1190 | Exploit Public-Facing Application | Likely exploitation of hosting provider vulnerabilities |
| Command and Control | T1071.001 | Application Layer Protocol: Web Protocols | Malicious servers communicated via HTTPS to deliver payloads |
| Credential Access | T1557 | Adversary-in-the-Middle | Intercepted update traffic to inject malicious binaries |
🌍 Real-World Scenario: Who Was Targeted?
According to researcher Kevin Beaumont, the attack was highly targeted. The threat actor Violet Typhoon (APT31), a Chinese state-sponsored group, focused on:
- Telecommunications companies in East Asia (e.g., Taiwan, Japan, South Korea).
- Financial services institutions in the same region.
- Only traffic originating from specific IP ranges was redirected to malicious servers, making the attack nearly invisible to global users.
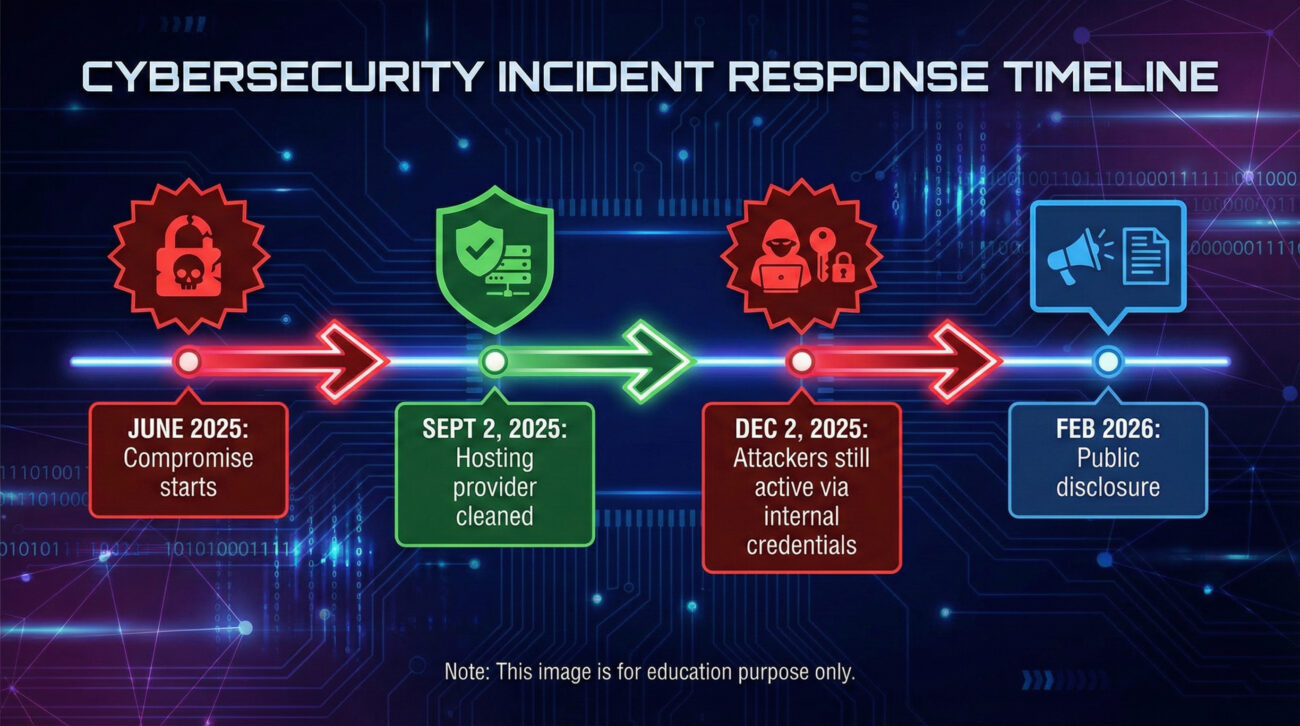
The compromise lasted from June 2025 until discovery in February 2026, even after the hosting provider was cleaned in September 2025, attackers maintained access to internal services until December 2025, allowing continued redirection.
🕵️ Step-by-Step Attack Flow
How did the Notepad++ update hijack actually work? Follow these steps:
Step 1: Infrastructure Compromise
Attackers breached the hosting provider serving notepad-plus-plus.org. They gained control over DNS settings or web server configurations to redirect update traffic.
Step 2: Traffic Redirection
When a Notepad++ user in a targeted region triggered an update check, the request was sent to a malicious server instead of the legitimate one. This was done by altering DNS responses or through a reverse proxy at the hosting level.
Step 3: Weak Integrity Check
WinGUp downloaded what it believed was an update. The updater only performed a simple hash check (likely MD5) which could be easily spoofed by the attacker. No digital signature verification was enforced.
Step 4: Malware Delivery
Users received a trojanized Notepad++ installer that installed backdoors, enabling persistence and lateral movement within target networks.
Step 5: Long-Term Access
Even after the hosting provider removed the attackers from the server in September 2025, they retained credentials to internal services until December, continuing to redirect traffic.
⚠️ Common Mistakes & Best Practices
What went wrong, and how can we defend against similar attacks?
Mistakes Made
- Weak update integrity checks – Only a simple hash, no code signing enforcement.
- Over-reliance on hosting provider – No monitoring for DNS/route hijacking.
- Delayed credential revocation – Attackers retained access for months after initial cleanup.
- No targeted user segmentation – All users treated equally, allowing targeted redirection to go unnoticed.
Best Practices to Implement
- Enforce code signing – Updates must be signed with a trusted certificate and verified before installation.
- Use HTTPS with certificate pinning – Prevents man-in-the-middle even if DNS is hijacked.
- Implement binary transparency logs – Similar to certificate transparency, log all update hashes.
- Regularly rotate credentials and audit provider security – Assume breach and limit blast radius.
- Monitor update traffic anomalies – Sudden redirects or download sources should trigger alerts.
🔴 Red Team vs 🔵 Blue Team Perspectives
🔴 Red Team (Attacker View)
- Objective: Hijack trusted update flow to deliver custom malware.
- TTPs: Compromise hosting provider, use AiTM, target specific sectors.
- Success factor: Weak integrity checks and lack of code signing.
- Persistence: Maintain internal access even after initial cleanup.
🔵 Blue Team (Defender View)
- Detection: Monitor for unexpected update sources, anomalous network connections from updater processes.
- Prevention: Implement certificate pinning, use signed updates, conduct regular third-party security audits.
- Response: Have an incident plan for supply chain compromises, revoke trust, force reinstall from known-good media.
- Hardening: Segment networks so that even if one endpoint is compromised, lateral movement is limited.
🛡️ Implementation Framework: Securing Update Mechanisms
Based on the Notepad++ update hijack, here’s a framework for developers and security teams to harden software update processes:
- Code Signing & Verification – Use strong signatures (RSA/SHA-256) and enforce verification before execution.
- Secure Channel with Pinning – HTTPS + public key pinning to prevent interception.
- Binary Transparency – Publish expected hashes of updates in a public log (e.g., Sigstore).
- Provider Security Audits – Regularly assess hosting providers’ security practices and SLAs.
- Fallback & Recovery – Have a manual update option and ability to revoke compromised versions.
- User Segmentation & Monitoring – Monitor for unusual update requests and consider gradual rollouts.
❓ Frequently Asked Questions
Q: Was Notepad++ itself vulnerable?
A: No. The attack occurred at the infrastructure level (hosting provider), not in Notepad++ code.
Q: How many users were affected?
A: The attack was highly targeted; only users in specific East Asian organizations (telecom/finance) were redirected.
Q: How can I check if I was affected?
A: Look for unexpected Notepad++ updates installed between June 2025 and February 2026. Verify hashes against official announcements. Use endpoint detection tools to scan for known APT31 indicators.
Q: What should developers learn from this?
A: Never trust the transport layer alone; implement defense-in-depth for updates: code signing, certificate pinning, and integrity validation.
✅ Key Takeaways
- The Notepad++ update hijack demonstrates that supply chain attacks can target update mechanisms without touching application code.
- Defense in depth is crucial: code signing, certificate pinning, and continuous monitoring would have prevented or detected this attack.
- Even after remediation, attackers retained access for months target="_blank" rel="noopener noreferrer" class="tactic-name">highlighting the need for complete credential revocation and provider reassessment.
- Targeted attacks can fly under the radar; global user bases may not notice small-scale redirections.
- MITRE ATT&CK provides a common language to understand and communicate such threats (T1195.001, T1557).
🔒 Secure Your Software Supply Chain Today
Don’t wait for the next update hijack. Audit your update mechanisms, implement code signing, and educate your team. For a deep dive into supply chain security, explore our free resources or book a consultation.
Download Supply Chain Security Checklist
Already using Notepad++? Verify your version and learn more from official Notepad++ site and the MITRE ATT&CK database.
📚 Further reading: Original Hacker News report | APT31 (Violet Typhoon) on MITRE | CISA supply chain guidance | Binary transparency explained | MitM attack defense
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































