NTLM Phase-Out: Microsoft's 3-Stage Plan to Move Windows to Kerberos
🔐 Executive Summary: The End of an Era for NTLM
After years of warnings, Microsoft has officially ignited the deprecation of NTLM (New Technology LAN Manager) with a concrete three-stage plan. This NTLM phase-out aims to replace the legacy protocol with Kerberos as the default authentication method in Windows. The move responds to decades of vulnerabilities, including pass-the-hash, relay attacks, and weak cryptography, that have made NTLM a favorite target for attackers. For cybersecurity professionals and IT teams, this transition is both a challenge and an opportunity to harden their identity infrastructure. This guide breaks down the plan, the risks, and exactly how to prepare.
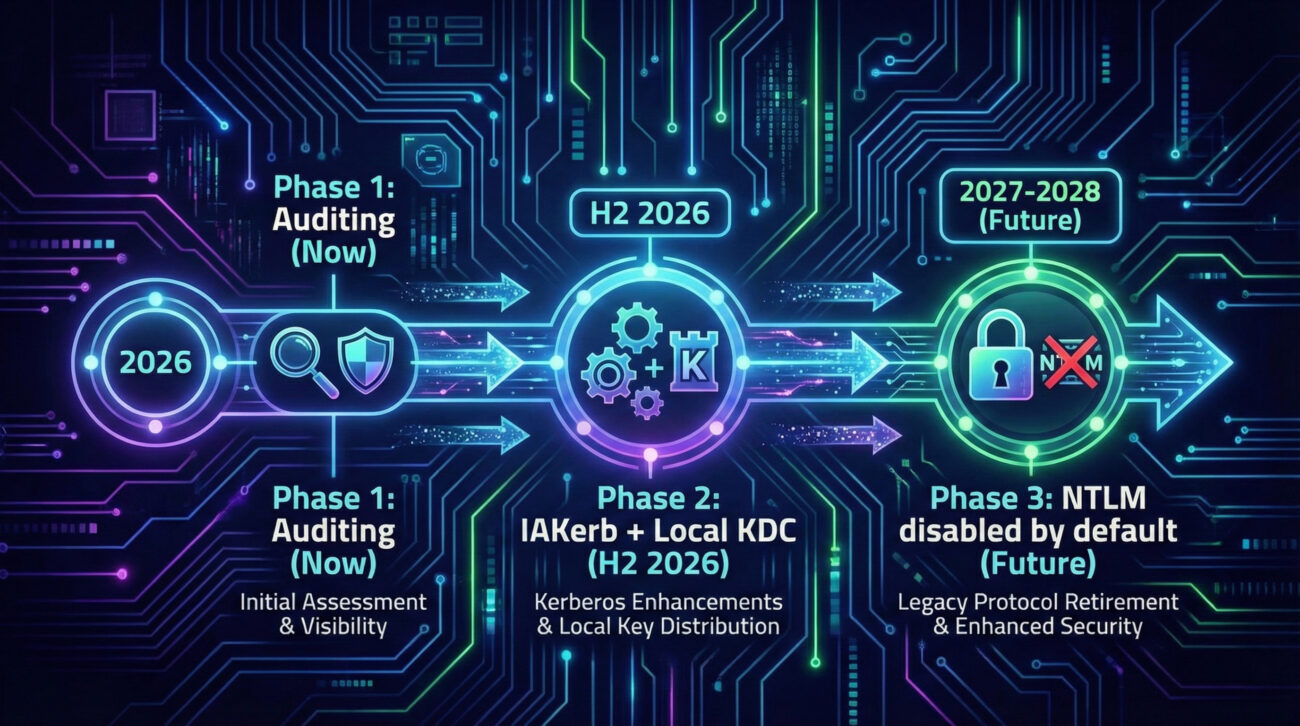
Whether you're a student, a system administrator, or a CISO, understanding the NTLM phase-out is essential. Microsoft's roadmap includes enhanced auditing now, new features like IAKerb and local KDC in late 2026, and finally disabling NTLM by default in future Windows releases. Let's dive deep into what this means for your environment.
📖 Table of Contents
- Executive Summary
- 1. NTLM & Associated MITRE ATT&CK Risks
- 2. Why Microsoft is Phasing Out NTLM
- 3. Microsoft's Three-Stage Plan (Detailed)
- 4. Step-by-Step Guide for Organizations
- 5. Common Mistakes & Best Practices
- 6. Red Team vs Blue Team View
- 7. Implementation Framework: NTLM vs Kerberos
- 8. FAQ
- 9. Key Takeaways
- 10. Call to Action
🛡️ Understanding NTLM and Its MITRE ATT&CK Techniques
NTLM is a challenge-response authentication protocol introduced by Microsoft in the early 1990s. It has long been considered insecure due to its use of weak cryptography (like LM/NTLM hashes) and vulnerability to multiple attack techniques documented in the MITRE ATT&CK framework.
Key techniques adversaries use against NTLM include:
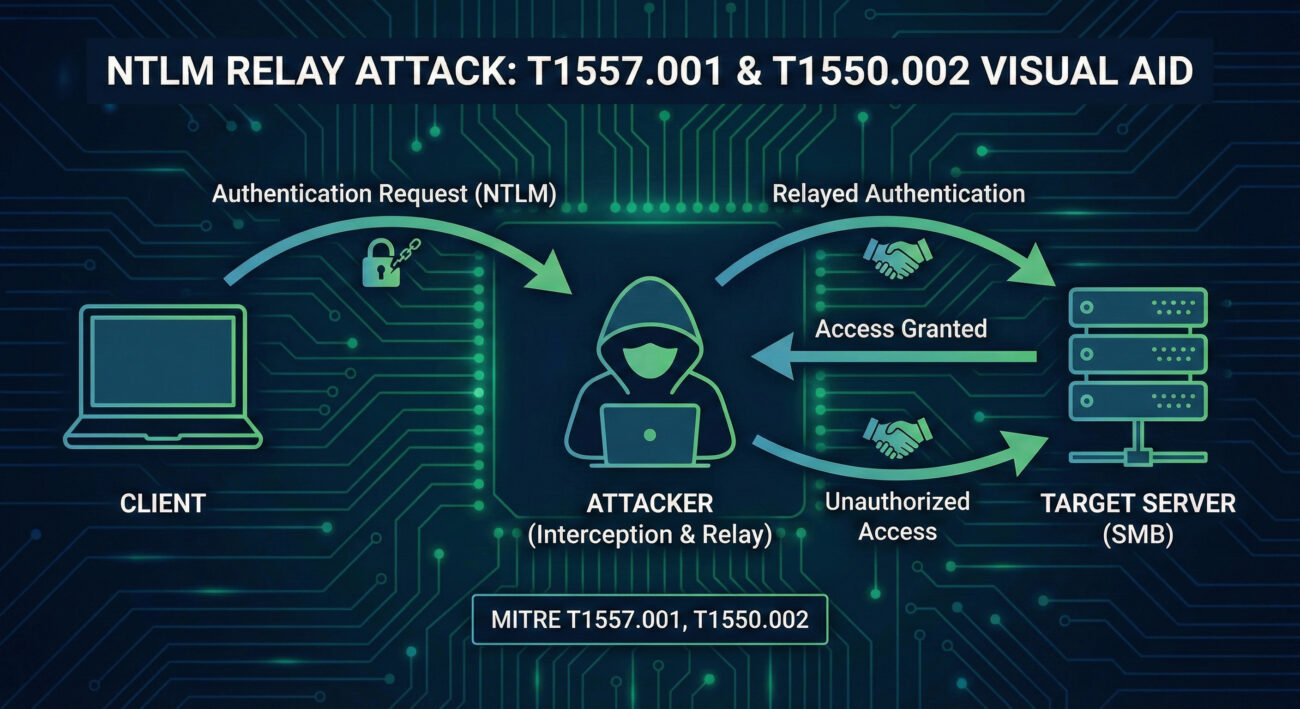
- Pass-the-Hash (T1550.002): Attackers capture NTLM hashes (from memory or LSASS) and use them to authenticate without needing the plaintext password.
- NTLM Relay (T1557.001): Adversaries position themselves between a client and server to relay NTLM authentication, gaining unauthorized access to resources like SMB shares or Exchange.
- Credential Dumping (T1003.002): Tools like Mimikatz extract NTLM hashes from LSASS memory, enabling lateral movement.
- Man-in-the-Middle (T1557): Combined with ARP spoofing or rogue APs, attackers can downgrade authentication to NTLMv1 or capture exchanges.
⚙️ Why Microsoft is Forcing the NTLM Phase-Out
As Mariam Gewida from Microsoft stated, "NTLM is susceptible to various attacks, including replay and man-in-the-middle attacks, due to its use of weak cryptography." Despite being formally deprecated in June 2024, NTLM remains widely used in enterprises due to legacy applications, network constraints, or simple inertia. This exposes organizations to credential theft and lateral movement.
The shift to Kerberos brings modern security features: mutual authentication, ticket-based access, support for MFA, and resistance to replay attacks. Microsoft's three-stage plan ensures a secure-by-default future while providing tools to ease migration.
📅 Microsoft's Three-Stage NTLM Phase-Out Plan
Stage 1: Visibility & Control (Available Now)
Enhanced NTLM auditing allows administrators to log and analyze exactly where NTLM is still used. This includes which applications, servers, or clients are requesting NTLM authentication. Without this visibility, migration is impossible.
Stage 2: Addressing Roadblocks (Expected H2 2026)
Microsoft will introduce two key technologies to eliminate common blockers:
- IAKerb – allows Kerberos to work across trust boundaries and non-domain joined scenarios.
- Local KDC – a lightweight Key Distribution Center for local accounts and scenarios where a domain controller isn't reachable.
- Core Windows components will be updated to prefer Kerberos automatically.
Stage 3: Disabling NTLM by Default (Future Windows Release)
The next version of Windows Server and its associated Windows client will ship with NTLM network authentication disabled. Organizations can re-enable it via Group Policy if absolutely necessary, but the default state is secure.
👣 Step-by-Step Guide to Prepare for the NTLM Phase-Out
Step 1: Enable Enhanced NTLM Auditing
Use Group Policy: Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Security Options → Network security: Restrict NTLM: Audit NTLM authentication in this domain. Collect logs from Domain Controllers and members.
Step 2: Map Dependencies
Analyze the logs to identify all applications, services, or devices that still use NTLM. Pay special attention to legacy servers, printers, scanners, and in-house apps.
Step 3: Test Kerberos in a Staging Environment
Create a test OU with GPOs that block NTLM (e.g., "Network security: Restrict NTLM: NTLM authentication in this domain" set to "Deny all"). Validate that critical apps still work via Kerberos.
Step 4: Upgrade or Remediate Incompatible Systems
For apps that break, work with vendors to enable Kerberos, or consider wrapping legacy apps with Kerberos-aware proxies. Microsoft's upcoming IAKerb and Local KDC (Phase 2) may help, but plan to remove NTLM entirely.
Step 5: Gradually Enforce Kerberos
Use "Deny all" audit modes first, then move to blocking. Leverage Group Policy to disable NTLM in pilot rings before full rollout.
✅❌ Common Mistakes & Best Practices During NTLM Phase-Out
🔴 Common Mistakes
- Assuming Kerberos works for all apps without testing.
- Ignoring NTLM usage in non-Windows devices (printers, IoT).
- Relying only on default auditing (not enabling detailed logging).
- Disabling NTLM before verifying IAKerb/local KDC readiness.
- Forgetting that service accounts might store NTLM hashes.
🟢 Best Practices
- Start auditing today – even if migration is far away.
- Inventory all service accounts and convert to Group Managed Service Accounts (gMSA).
- Enable Kerberos armoring (FAST) where possible.
- Use Windows Defender Firewall to block unnecessary SMB traffic that could relay NTLM.
- Plan for phased disablement using Group Policy rings.
🎭 Red Team vs Blue Team: NTLM Phase-Out Impact
🔴 Red Team (Attackers)
With NTLM still present, red teams leverage:
- Pass-the-Hash (T1550.002) – using tools like Mimikatz or Impacket.
- NTLM Relay (T1557.001) – via tools like ntlmrelayx to compromise servers.
- Coercion attacks (e.g., PrinterBug) to force a DC to authenticate back to an attacker.
Once NTLM is disabled, these attack paths become significantly harder, forcing attackers to target Kerberos (which requires more complex techniques like Kerberoasting or Golden Tickets).
🔵 Blue Team (Defenders)
Defenders can use the phase-out to:
- Enforce phishing-resistant MFA (Kerberos supports modern auth).
- Monitor for NTLM usage anomalies via Event ID 8001-8004 (NTLM auditing).
- Implement EPA (Extended Protection for Authentication) to harden existing apps.
- Use the three-stage plan as a justification to get budget for legacy app remediation.
⚖️ Comparison: NTLM vs Kerberos
| Feature | NTLM | Kerberos |
|---|---|---|
| Authentication type | Challenge-response (symmetric) | Ticket-based (asymmetric + symmetric) |
| Mutual authentication | No (server not authenticated to client) | Yes (both parties verify) |
| Resistance to replay | Weak (timestamps optional) | Strong (timestamps + session keys) |
| Pass-the-hash risk | High – hashes are sufficient | Low – requires ticket + session key |
| MFA support | Limited (NTLMv2 can leverage, but rarely used) | Native (with PKINIT, smart cards, Windows Hello) |
| Default in Windows | Legacy fallback | Domain-joined default |
❓ Frequently Asked Questions About the NTLM Phase-Out
A: Only if it hard-codes NTLM and cannot use Kerberos. Microsoft is providing IAKerb and local KDC to cover many legacy scenarios. You should test and plan to upgrade.
A: Phase 3 focuses on network NTLM. Local logons may still use NTLM until further notice, but the goal is to eventually move everything to Kerberos (including via Local KDC).
A: Enable the Group Policy setting "Network security: Restrict NTLM: Audit NTLM authentication in this domain" and review the logs on Domain Controllers. Microsoft also provides detailed guidance.
A: Yes, all versions of NTLM (including v2) are being phased out. NTLMv2 is more secure than v1 but still vulnerable to relay and pass-the-hash.
📌 Key Takeaways
- Microsoft's NTLM phase-out is real and accelerating: Phase 1 auditing is available now, Phase 2 mid-2026, Phase 3 (default disable) in a future Windows release.
- NTLM is associated with critical MITRE techniques like pass-the-hash (T1550.002) and relay (T1557.001), making its removal a major security win.
- Organizations must start auditing immediately to discover hidden NTLM dependencies.
- New technologies like IAKerb and local KDC will help bridge gaps for legacy apps.
- Red teams will lose a reliable attack vector; blue teams gain a more robust authentication foundation.
🚀 Start Your NTLM Phase-Out Journey Today
Don't wait until 2026. Begin with these three actions:
- 🔍 Enable NTLM auditing on your Domain Controllers.
- 📋 Create a dependency map of all NTLM-using devices and apps.
- 🧪 Test Kerberos-only policies in a lab.
For deeper dives, explore these resources:
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































